
Two-Factor Authentication: an Extra Access Security
One more time about strengthening your database security or how you can intensify authorization to the restricted DBMS. Two-factor authentication (2FA) validates database users’ identities by two separate identifiers. Authentication to access the database is not performed until both identification methods input by the user are correct.
Generally speaking, access to any system may be protected by a combination of various identity verification methods. Along with login credentials, 2FA may be used and would include push notifications, a one-time password, voice call or SMS authentication, biometrics, etc. First, a user enters his username and a password and then has to prove his identity one more time by an additional confirmation method.
Extra Layer of Security. Is the Game Worth the Candle?
As everything with the “extra” prefix sounds complicated not to mention may seem so in action, additional measures are usually ignored to save effort. First, is it wise to disregard extra measures that are related to database security and meant to intensify it? Second, the complications work both ways. Attackers are attracted by easy targets. In simple words, 2FA serves as a disincentive for hackers to start trying to compromise your doubled authentication, and they’d rather go looking for victims with just one authentication layer.
Password-based access is the most common form of identification, a part of login process or the so-called single-factor authentication. However, even considering a strong password policy implemented, in light of numerous recently reported security breaches a password alone is usually rejected, as it can no longer provide adequate protection, as it is guessable, can be stolen or shared with wrong people, i.e. more susceptible to various hacking techniques, such as phishing, brute force, keystroke logging, etc. With 2FA, the risk of fraudulent access to your database is limited, as before obtaining access to the system users are properly authenticated by doubled verification method. So, obviously 2FA justifies the trouble and cost involved.
DataSunrise 2FA in Action
Most databases do not have 2FA solutions installed by default, and specific authentication plugins may be required to protect users’ access with 2FA. It may cause some inconveniences, as these plugins differ for various databases, and it takes time and effort to evaluate various similar solutions before making a choice, then install them and test. The 2FA feature in DataSunrise is universal and adjustable to all supported databases and requires no additional configuration of plugins or tools. To verify user’s permission to access a target database, DataSunrise incorporates two separate verification methods in its two-factor authentication solution. The basic login procedure is intensified by email-based authentication.
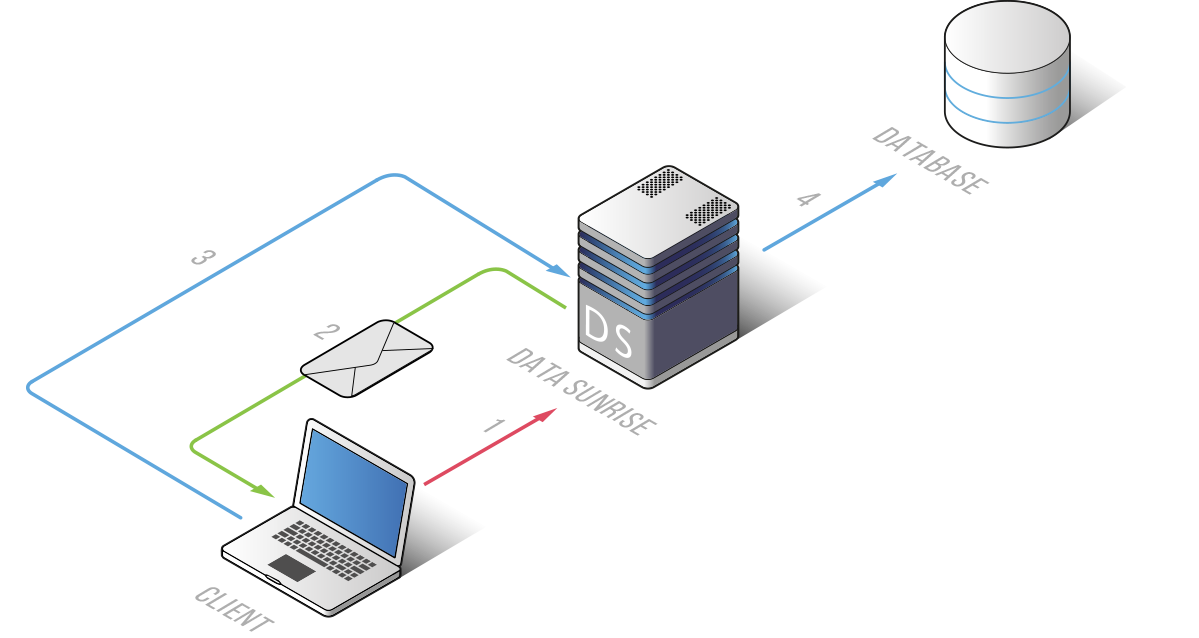
When a database user authenticates with credentials, he is notified of a confirmation link sent directly to his email. To send emails with confirmation links, configure an SMTP server at Configuration → Subscribers → Add Server and check the Send security emails from this server checkbox.
Depending on privileges and administrative roles you may disable 2FA for certain database users and allow them to log in using just a username and a password and assign 2FA to others with more critical roles. For this purpose, proceed to Configuration → Database Users, open the required user’s profile, check Enable Two-Factor Authentication and indicate an email to which DataSunrise will send a security letter with a confirmation link. The user has to open the link and log in again to complete the second identity confirmation step.
You may also activate 2FA in such a way that only users with email-based authentication can access you target database. To do so, open the target database profile and check Accept Only Two-Factor Authentication Users in the Advanced Settings.
Even if DataSunrise 2FA is optional, consider its deployment, as it significantly reduces the possibility of an unauthorized user to log in to your target database.
For more information about incorporation of two separate identifiers, refer to the DataSunrise Database Security Suite User Guide.
