
Implementing ABAC in MySQL: A Step-by-Step Approach to Data Protection

Introduction
In today’s world, it is crucial to keep sensitive information in databases safe and secure. Attribute-Based Access Control (ABAC) has emerged as a powerful approach to enhance data security in MySQL. This article will explain the basics of ABAC in MySQL, including security features and examples to show how it works.
What is ABAC in MySQL?
ABAC is a model that controls access to resources based on attributes of users, data, and the environment. In MySQL, ABAC provides detailed control over database access. It considers factors such as user roles, data sensitivity, time of access, and location.
ABAC offers a flexible and dynamic approach to data security, enabling organizations to enforce granular access policies based on specific attributes.
Security Aspects of ABAC in MySQL
ABAC in MySQL addresses several critical security aspects:
- Granular Access Control: ABAC allows admins to control who can access specific data and when, based on different characteristics. This provides precise data access control.
- Attribute-Based Policies: ABAC policies use attributes to decide who can access information. These attributes include a person’s role, the sensitivity of the data, time restrictions, and other factors.
- Dynamic Authorization: ABAC allows for instant evaluation of access requests using current attribute values, making dynamic and context-aware access control decisions.
- Separation of Duties: ABAC enforces separation of duties by creating rules that prevent conflicting or unauthorized access based on user roles and responsibilities.
Implementing ABAC in MySQL
To implement ABAC in MySQL:
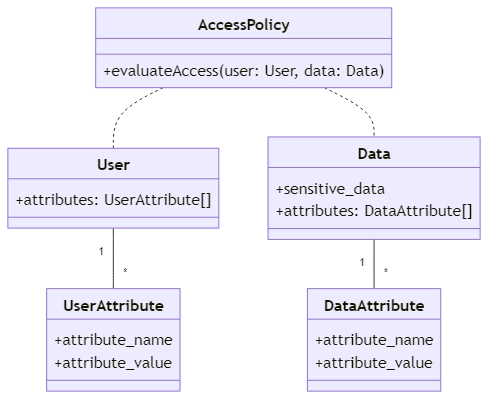
Define Attributes: Identify the relevant attributes for subjects, objects, and the environment. User attributes like role, department, and security clearance, and data attributes like sensitivity level and data owner.
Create Attribute Tables: Create tables in MySQL to store the attribute values for subjects and objects. For instance:
CREATE TABLE user_attributes ( user_id INT, attribute_name VARCHAR(50), attribute_value VARCHAR(100), PRIMARY KEY (user_id, attribute_name) ); CREATE TABLE data_attributes ( data_id INT, attribute_name VARCHAR(50), attribute_value VARCHAR(100), PRIMARY KEY (data_id, attribute_name) );
Define Access Policies: Create access policies based on the attributes. For example, to grant access to sensitive data only to users with a specific role and security clearance:
SELECT *
FROM sensitive_data
WHERE EXISTS (
SELECT 1
FROM user_attributes ua
WHERE ua.user_id = [current_user_id]
AND ua.attribute_name = 'role'
AND ua.attribute_value = 'manager'
) AND EXISTS (
SELECT 1
FROM user_attributes ua
WHERE ua.user_id = [current_user_id]
AND ua.attribute_name = 'security_clearance'
AND ua.attribute_value = 'top_secret'
);
Enforce Access Control: Implement the access policies in your application or database access layer to enforce ABAC. You can do this using SQL queries, stored procedures, or application-level code.
Example of ABAC in MySQL
Let’s consider an example where we have a database containing sensitive customer information. We want to ensure that only authorized users with the appropriate attributes can access specific data.
First, create the necessary tables:
CREATE TABLE customers ( customer_id INT PRIMARY KEY, name VARCHAR(100), email VARCHAR(100), sensitive_data VARCHAR(100) ); CREATE TABLE user_attributes ( user_id INT, attribute_name VARCHAR(50), attribute_value VARCHAR(100), PRIMARY KEY (user_id, attribute_name) );
Insert sample data:
INSERT INTO customers (customer_id, name, email, sensitive_data) VALUES (1, 'John Doe', '[email protected]', 'Confidential'), (2, 'Jane Smith', '[email protected]', 'Restricted'); INSERT INTO user_attributes (user_id, attribute_name, attribute_value) VALUES (1, 'role', 'manager'), (1, 'security_clearance', 'top_secret'), (2, 'role', 'employee'), (2, 'security_clearance', 'confidential');
To retrieve sensitive customer data based on user attributes:
SELECT c.customer_id, c.name, c.email, c.sensitive_data
FROM customers c
WHERE EXISTS (
SELECT 1
FROM user_attributes ua
WHERE ua.user_id = [current_user_id]
AND ua.attribute_name = 'role'
AND ua.attribute_value = 'manager'
) AND EXISTS (
SELECT 1
FROM user_attributes ua
WHERE ua.user_id = [current_user_id]
AND ua.attribute_name = 'security_clearance'
AND ua.attribute_value = 'top_secret'
);
Only managers with top-secret clearance can access sensitive customer data in this example. The query dynamically evaluates the user’s attributes to determine access rights.
Conclusion
Implementing ABAC in MySQL provides a robust and flexible approach to enhance data security. Organizations can protect sensitive information by using attributes and creating specific access rules for authorized users. ABAC offers granular control, dynamic authorization, and the ability to enforce separation of duties. Follow the steps in this article and think about security to successfully use ABAC in your MySQL database.
DataSunrise provides great tools for managing data, such as security, audit rules, masking, and compliance. DataSunrise’s solutions can greatly complement and enhance the implementation of ABAC in MySQL. For more information, you can visit the online demo session.
