
DataSunrise Overview
DataSunrise Data and Database and AI Security Platform is an advanced software suite which protects sensitive information across corporate databases, cloud storage systems, and LLM communications. It employs ML and AI-integrated solutions for enhanced log analysis and user experience improvement. With an intuitive interface and easy deployment, DataSunrise helps organizations comply with comprehensive data security regulations while safeguarding their digital assets across multiple platforms.
DataSunrise firewall runs independently of any applications, does not require any software agents and doesn’t inflict any additional load on protected database. It is worth noting that DataSunrise does not store database passwords or any other sensitive info.
Since most data leaks originate from companies’ own employees, DataSunrise protects corporate data both from external data breaches and insider threats.
Deployment options
DataSunrise is compatible with 64-bit Windows and Linux operating systems. You can install it on the database server, on a separate server in the cloud, or on-premises.
DataSunrise offers flexible deployment options to suit various organizational needs. While multiple configurations are available, two primary setups stand out for their versatility and effectiveness.
Sniffer Mode
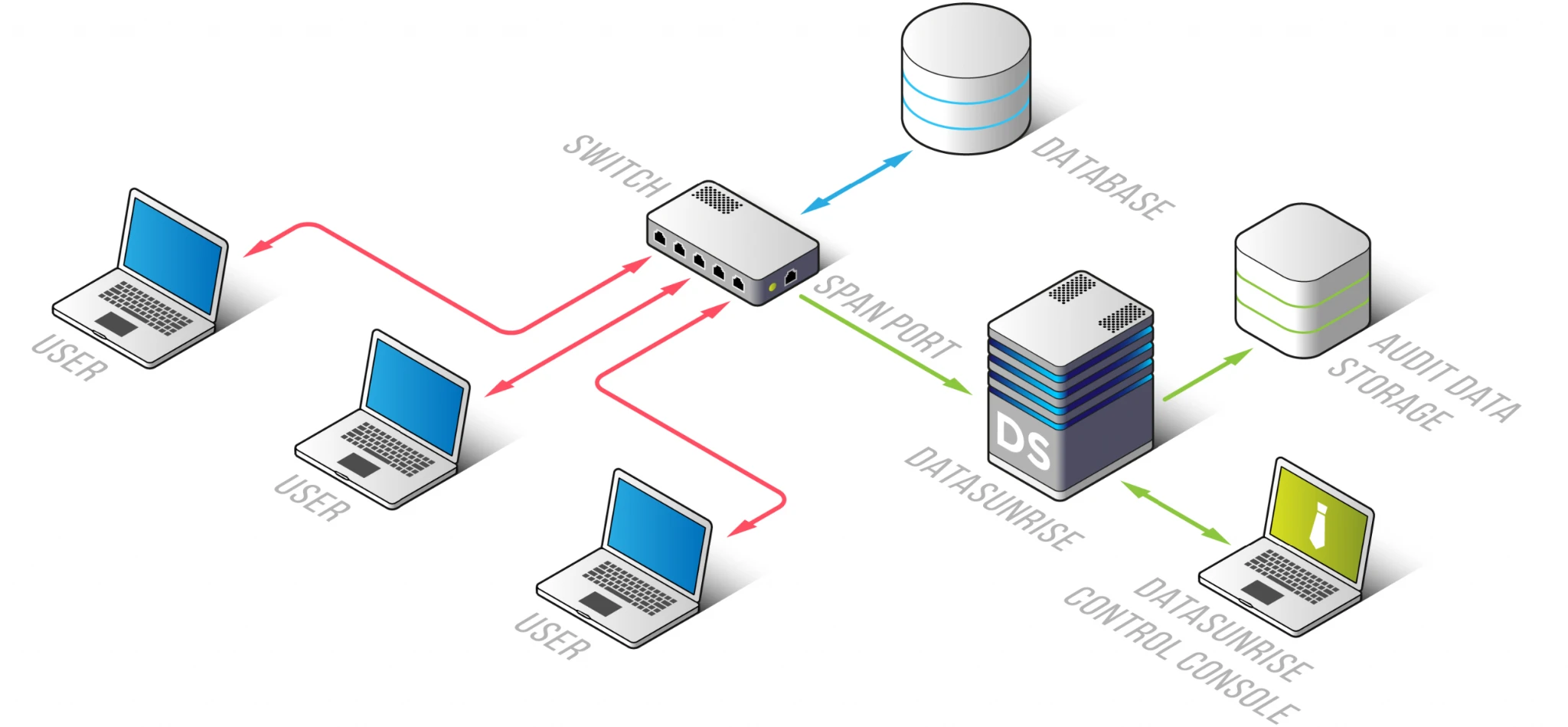
While running in this mode, DataSunrise acts as a traffic analyzer: it logs all database events. In this configuration, DataSunrise can not interfere database traffic, so it is able to perform only data auditing functions. Running DataSunrise in sniffer mode does not require any additional tweaking of databases or client applications.
Proxy Mode
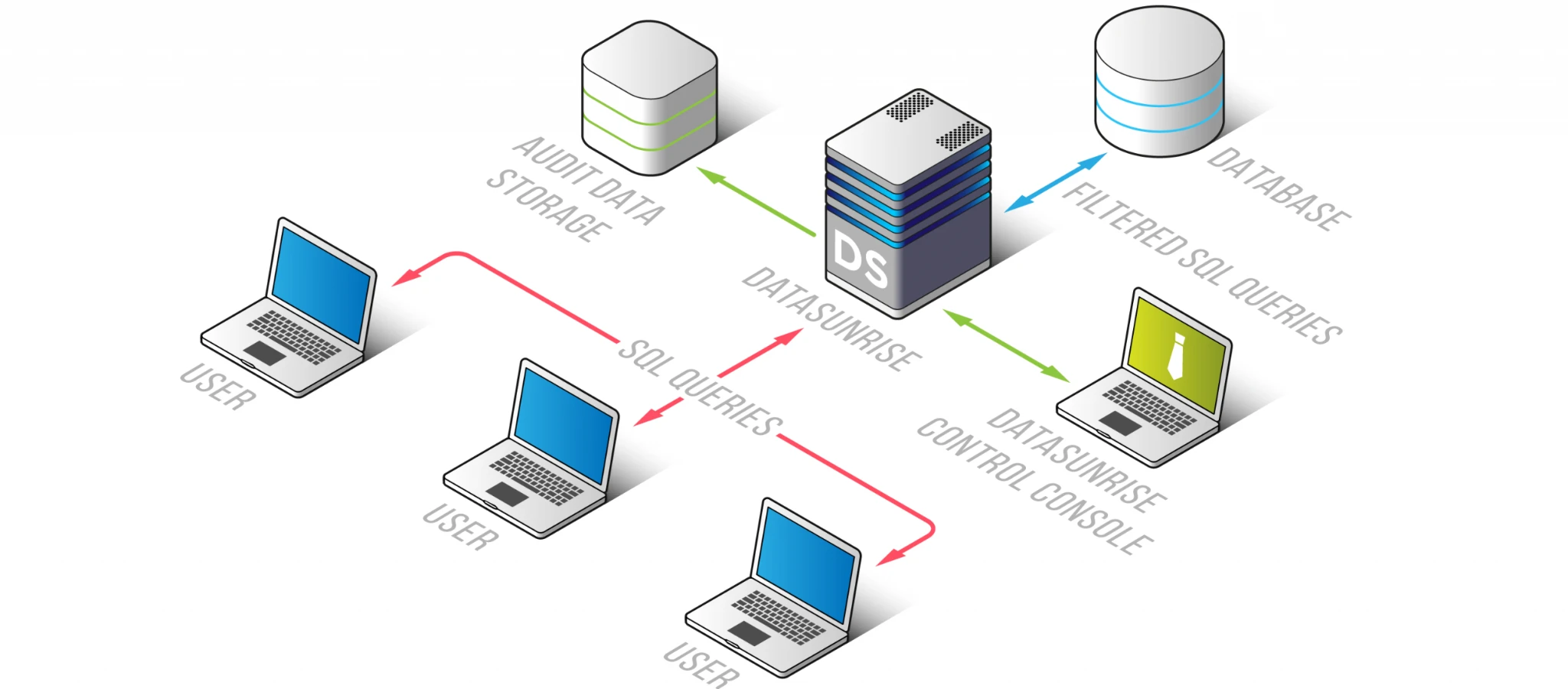
When deployed in this configuration, DataSunrise acts as a proxy server controlling incoming queries and database responses. Unlike Sniffer mode, Proxy mode enables DataSunrise to block or modify client queries if necessary. In Proxy mode, DataSunrise can perform all its functions; however, there may be restrictions depending on the database it protects or the nature of the storage. Besides that, the database response time is somewhat increased (not more than 5-10%) as compared with Sniffer mode.
Data Audit
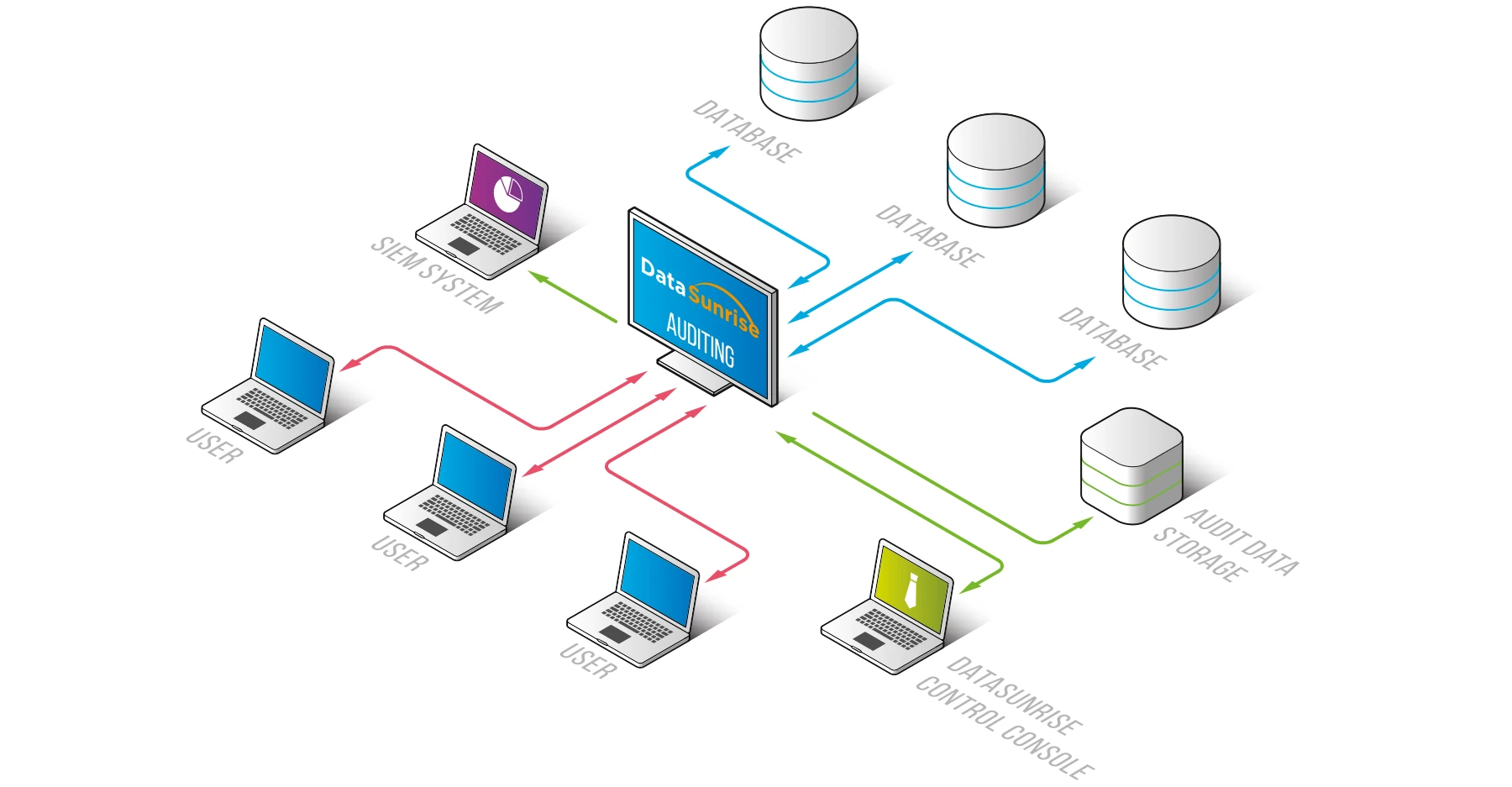
DataSunrise Data Audit component collects information on all user actions and modifications made to database contents. The audit is used mostly for data breach investigation and assessment of security system vulnerabilities. Continual data auditing helps to detect data breach preparations and initiate its prevention.
DataSunrise features self-learning algorithm integrated into the Data Audit component. Our data security solution uses these algorithms to learn typical database user behavior and create a White list of authorized SQL queries intended to be used by Data Security and Data Masking components. The firewall administrator can use dedicated Learning Rules set to manage self-learning process.
Data Security
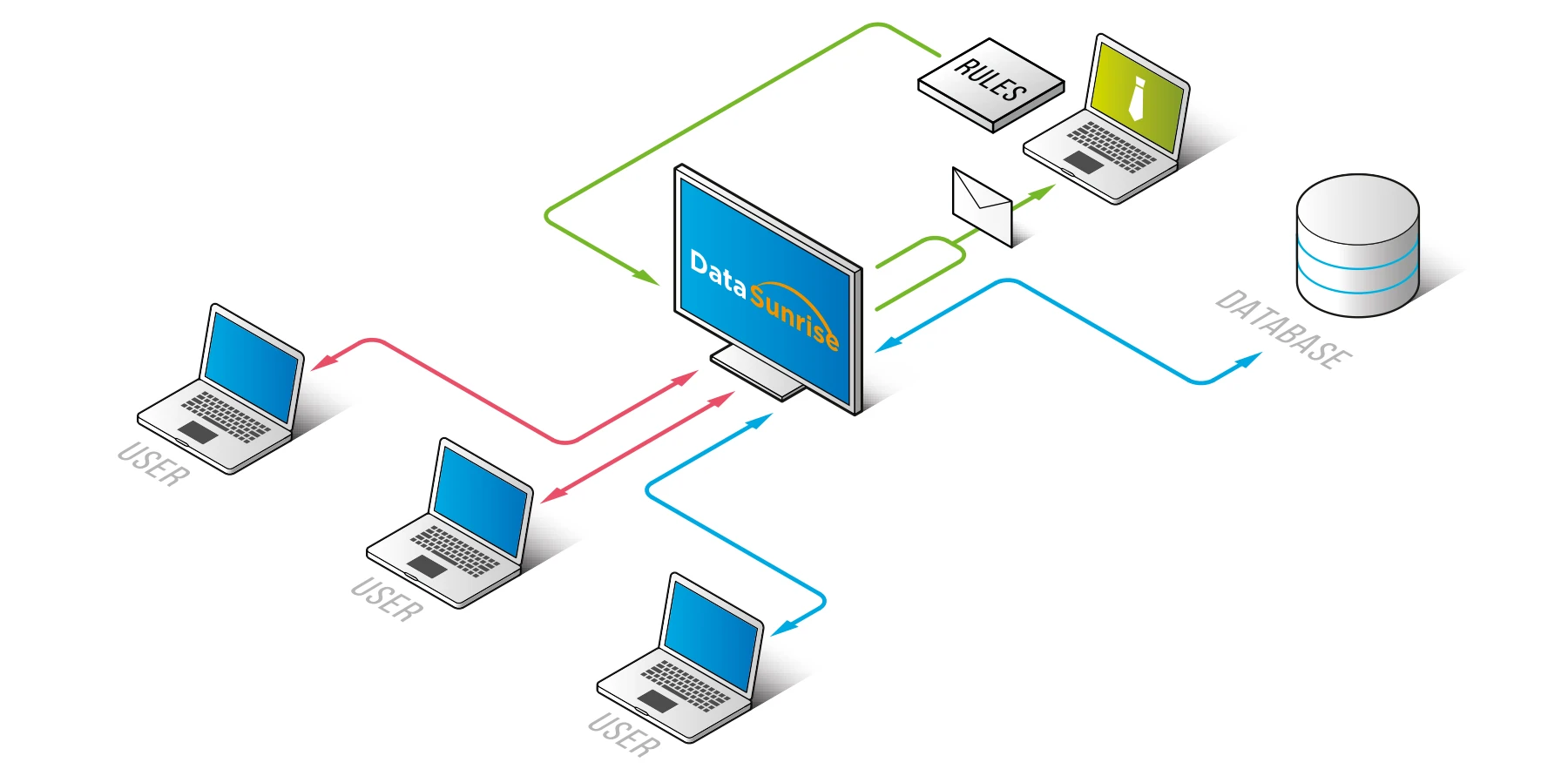
Data Security component is the basic tool DataSunrise utilizes to counter various harmful actions: it prevents unauthorized access and defends the database from SQL injections.
The functionality is based on a system of security policies. First, the firewall administrator specifies which queries should be treated as malicious based on their source and SQL code. Then DataSunrise performs smart analysis of database traffic. If an incoming query violates existing security policies, it is blocked. Then DataSunrise informs the firewall administrator via Email.
Data Masking
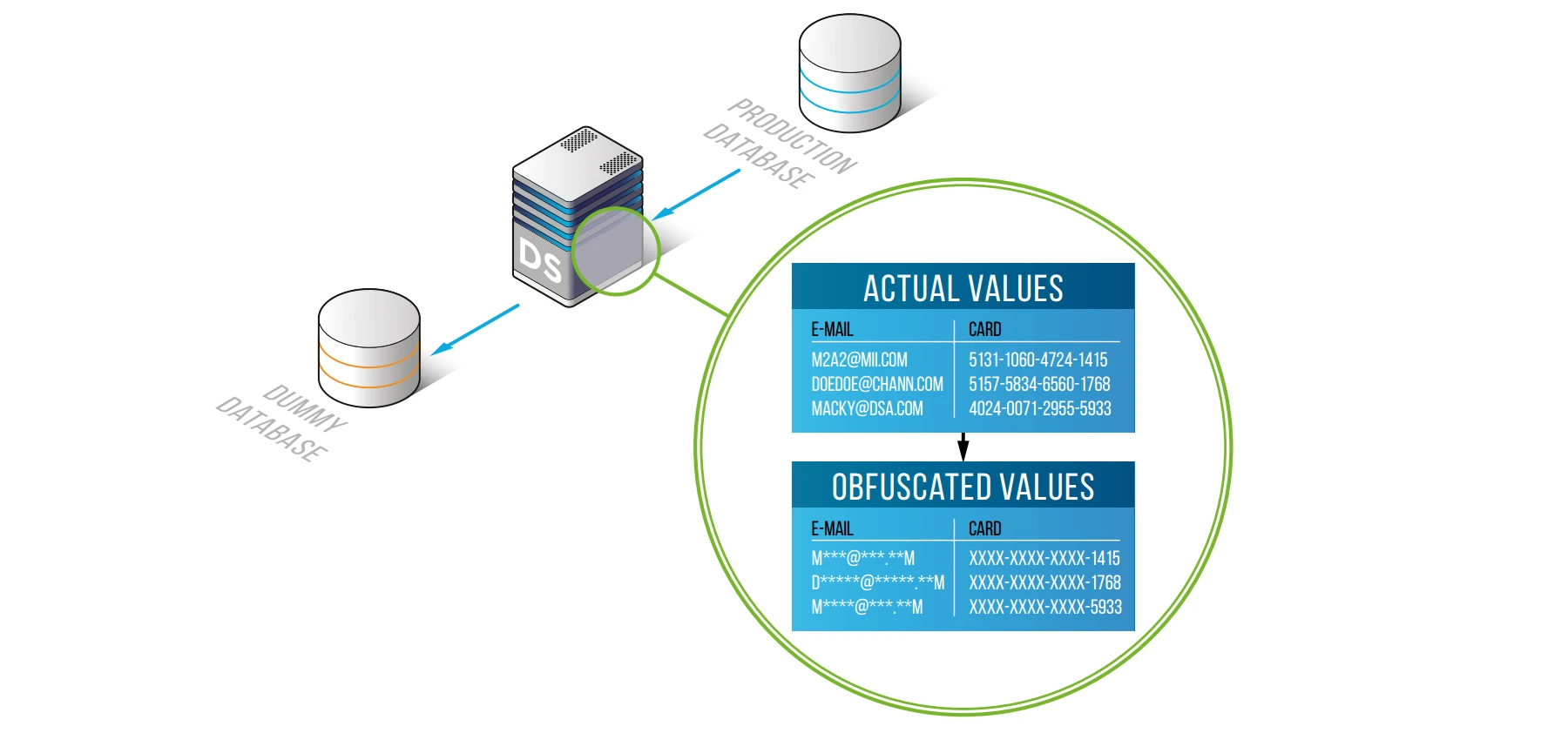
Static data masking tool enables you to create a copy of the database and change required content with fake values or random characters.
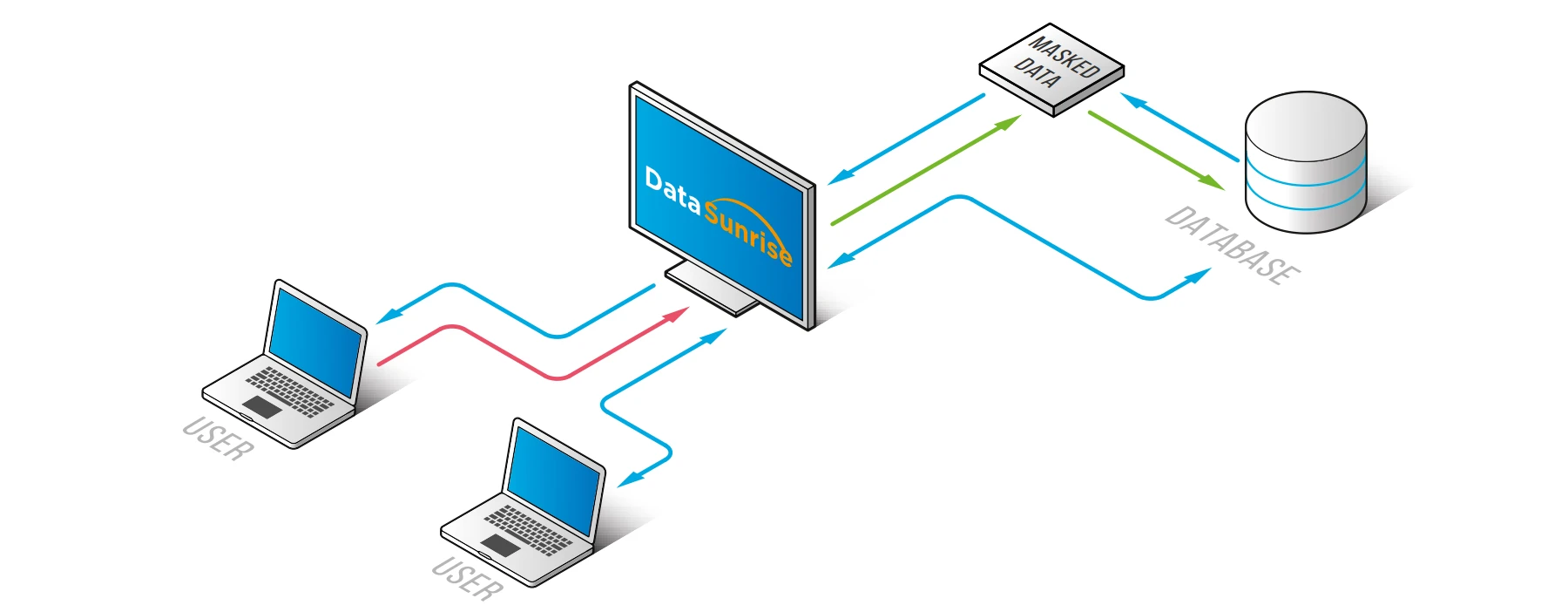
The firewall administrator can hide database contents from unauthorized users by replacing the actual database output with fake values. Our solution obfuscates the data before it reaches the user, helping to prevent potential data leaks.
In most cases, data masking not only protects data from hacker actions but also helps with data sharing situations when intentional data transfer to a third party occurs (for testing, reporting, etc.).
Sensitive Data Discovery
Confidential and regulated data requires special care but first, you need to find where it is. Sensitive Data Discovery feature detects columns containing various types of sensitive data and creates security, audit or masking rule for these columns. Search is performed by detecting matches of pre-defined regular expression patterns for various types of data:
- PII (driver’s license number, social security number, passport number, criminal history credit history)
- PCI data (credit card numbers, personal identification numbers (PINS), bank account numbers, magnetic stripe data, security codes)
- ePHI (health status and history, health insurance account information, medical treatment history, diagnoses, Medicare and Medicaid data)
Events and Statistics Reports
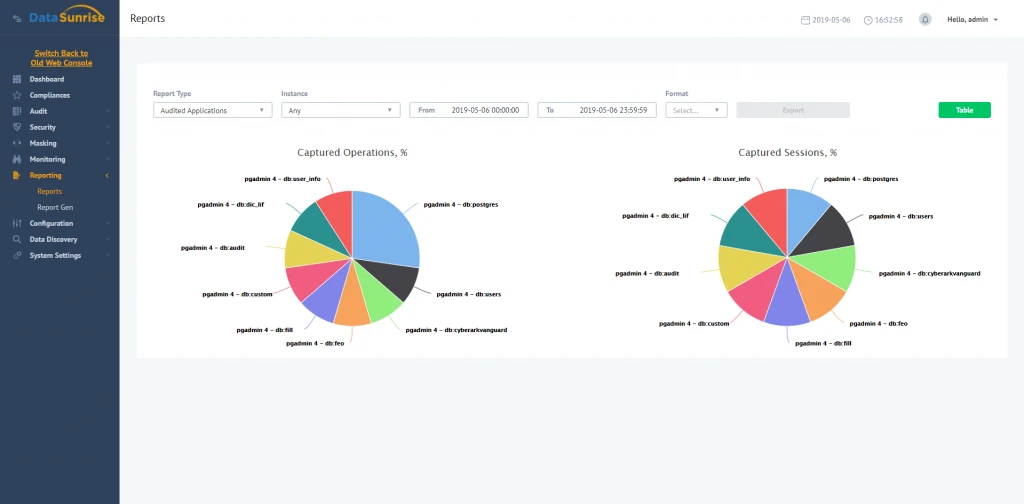
Web Console features Event Monitor section dedicated to provide the administrator with full details on system events, intercepted queries, and the firewall actions. To make this info easy to understand, the Event Monitor visualizes it as a table or a chart.
Additionally DataSunrise features an advanced reporting tool named Report Generator. This feature enables you to create custom reports on required events and save them as a PDF or CSV file.
DataSunrise supports all major databases and data warehouses. You are welcome to download a free trial if would like to install on your premises. In case you are a cloud user and run your database on Amazon AWS or Microsoft Azure you can get it from AWS market place or Azure market place.
