Audit Guide
Data auditing supports real-time database activity monitoring by recording detailed information about every executed query, including read, update, and delete operations. DataSunrise captures both user interactions and any changes to database configurations or system settings. This guide explains how to configure DataSunrise to audit all queries for a selected target database.
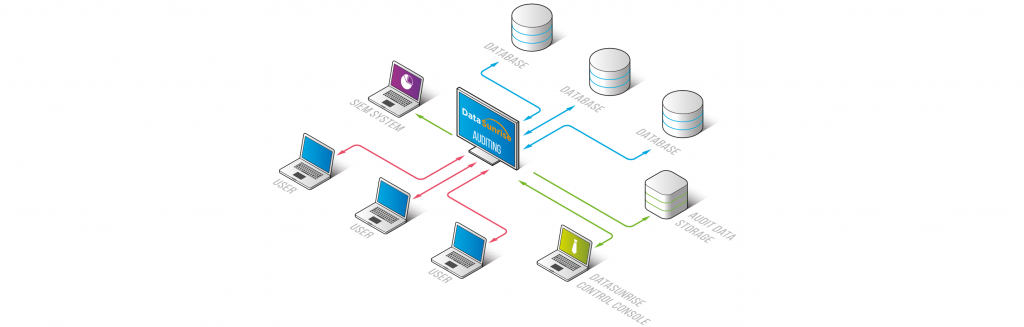
The audit logs are stored in the DataSunrise-integrated SQLite database or in an external database. Logged data helps to comply with requirements of regulatory standards such as SOX, HIPAA, PCI DSS, and other regulators and acts.
The Data Audit feature is available in both Sniffer and Proxy modes. Within the Data Audit section, you can create new audit rules or modify existing ones. These rules can be configured to monitor transactions for specific databases, as well as filter activity by database users, IP addresses, or client applications.
To enhance your understanding of data auditing, we highly recommend visiting our YouTube channel to watch our videos on this topic. These videos not only showcase our auditing solution but also familiarize you with alternative data auditing methods using native DBMS features.
Why Database Auditing Matters
Database auditing is critical for detecting unauthorized access, monitoring administrative actions, and keeping a reliable record of all operations involving sensitive data. This becomes especially important for organizations subject to regulations such as GDPR, SOX, HIPAA, and PCI DSS, where visibility into data access is not optional but required.
By applying granular auditing rules through platforms like DataSunrise, security teams can quickly identify suspicious activity, investigate incidents with greater accuracy, and generate audit records suitable for compliance checks. Without proper auditing in place, unauthorized actions or insider misuse can go unnoticed, leading to increased financial risk and reputational harm.
What is DataSunrise Data Audit?
DataSunrise Data Audit is a core feature of the platform that captures database activity in detail. It monitors user interactions continuously and records queries, data changes, and connection attempts in real time using proxy or sniffer deployment modes.
This level of monitoring allows organizations to enforce least-privilege principles, track privileged users, and satisfy auditing requirements defined by regulations such as HIPAA, SOX, and PCI DSS. Built-in filtering and alerting also enable the system to serve both as an incident investigation tool and a foundation for ongoing compliance.
Creating an Audit Rule
Let’s assume that you’ve already created the target database profile. Then to audit our test database, it is necessary to create and configure an Audit Rule. In this case, the sequence of actions is the following:
- Navigate to Audit → Rules. Then click Add Rule to create a new Audit Rule.
- Configure your Audit Rule to log all queries to the database (see notes below).
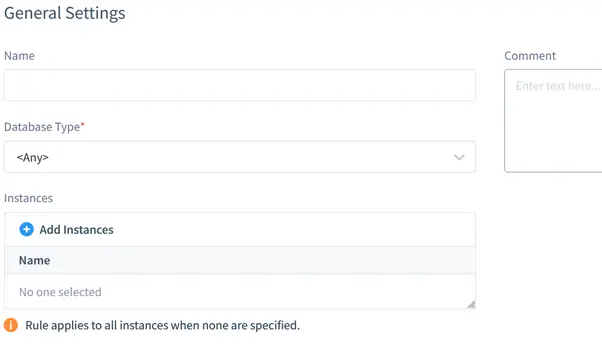
In the Main section subsection, the target database information is specified. It includes database type (PostgreSQL), database instance (as the target database entry is named in the Configurations) and the Rule’s logical name.
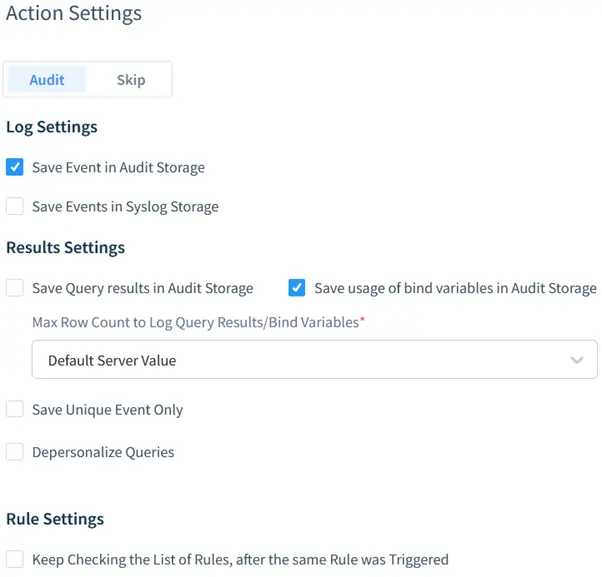
By default, the “Audit” action is selected. It means that DataSunrise will audit user queries when the rule is triggered. To log database responses (the output), the Log Data checkbox is checked.
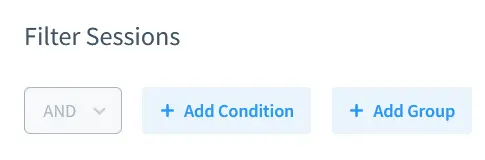
Since the current scenario requires all user queries to be audited, Filter Sessions are left as by default. Thus, any query to the database regardless of its source IP address will trigger the rule.
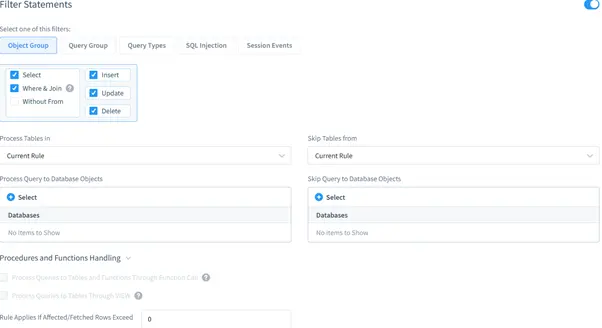
Filter Statements settings are as by default as well. Thus, DataSunrise will audit all queries directed to all database objects.
Viewing Database Audit Results
This stage includes demonstration of auditing results. The Audit Rule which was created at the previous stage is configured to be triggered by any incoming user query. Here’s what happens when DataSunrise receives a user query.
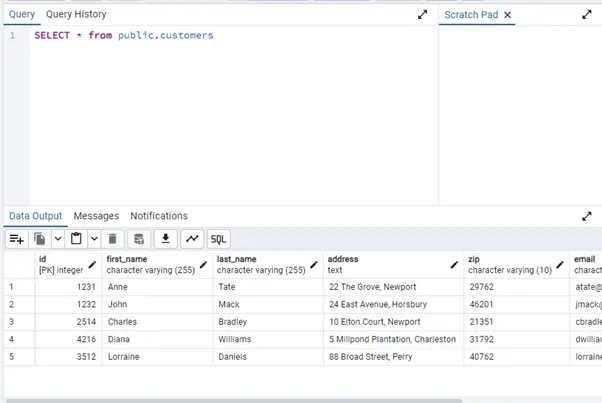
- Let’s send the following query via PGAdmin:
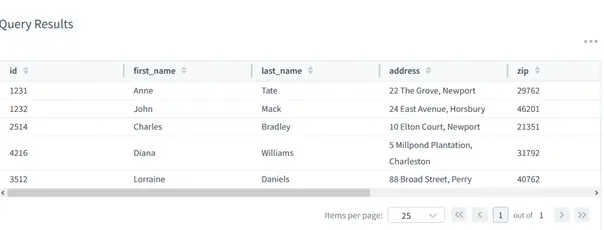
- The database outputs the table contents:
- Now let’s check the auditing results in the DataSunrise’s Web Console. Navigate to the Data Audit → Transactional Trails subsection.
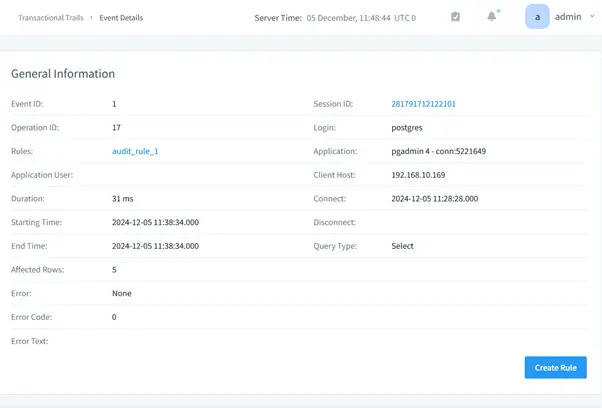
- To view detailed information about some event, click event’s ID. In a new tab, the event’s details will be displayed: code of the query, basic information, session information, database objects involved in the query and the query results.
SELECT * FROM public.customers;
Each event logs comprehensive metadata including IP addresses, application names, timestamps, and execution details.
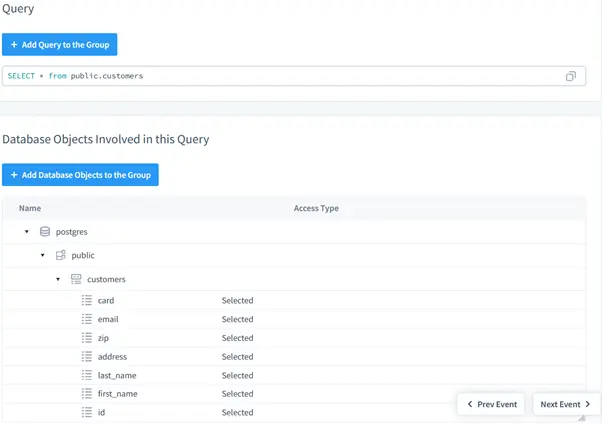
Scrolling down reveals additional event details, including the complete SQL query statement and database objects the query touches. The query accessed sensitive data fields including credit card numbers, email addresses, and ZIP codes.
Query results can be displayed, but enabling this feature significantly impacts audit database storage consumption.
Real-World Use Cases: Applying DataSunrise Data Audit
The DataSunrise Data Audit engine isn’t just a logging tool—it’s a compliance enabler and incident response ally. Here’s how organizations use it to meet regulatory and operational requirements in live environments:
| Use Case | How DataSunrise Helps |
|---|---|
| SOX Compliance | Tracks privileged user activity on financial systems and logs changes to critical configurations. Supports external audit reviews with detailed transaction histories. |
| HIPAA Monitoring | Audits all queries involving PHI, including read access to medical records. Captures session metadata for accountability and breach investigation. |
| PCI DSS Enforcement | Monitors credit card data access in real time and logs queries that touch PAN fields. Supports alerting on unauthorized access attempts. |
| Data Exfiltration Detection | Flags suspicious query volumes, DUMP statements, and unapproved exports—especially from new IPs or clients. |
| Insider Threat Visibility | Captures admin actions, schema modifications, and unusual object access—all correlated with user identities and timestamps. |
Because DataSunrise works at the proxy layer, it can enforce auditing even when the database’s native logging is disabled or bypassed. This makes it an essential part of modern data security and governance strategies.
Conclusion
Effective database auditing is essential for detecting suspicious behavior, meeting regulatory requirements, and maintaining accountability within modern data ecosystems. DataSunrise enables organizations to implement detailed, real-time monitoring of database queries and transactions without impacting performance or disrupting operations.
Capabilities such as role-based access control, proxy-level traffic analysis, and full session logging deliver clear insight into who accessed data, when the activity occurred, and through which connection. This creates a centralized audit trail that simplifies investigations, supports compliance with standards like SOX, HIPAA, and PCI DSS, and reduces the risk of unauthorized data access.
Whether monitoring a small number of sensitive tables or managing large-scale production systems, DataSunrise provides the scalability, visibility, and control needed to safeguard critical data and ensure ongoing compliance.