
Impact of Remote Code Execution Attacks

What is Remote Code Execution (RCE)?
Remote Code Execution, often abbreviated as RCE, is a type of cyber attack that allows an attacker to execute arbitrary code on a target machine or in a target environment. This grants the attacker full control over the vulnerable application or system. RCE attacks are extremely dangerous, as they enable an adversary to perform any action that the compromised application or user has permissions for.
RCE vulnerabilities often arise due to insufficient input validation and sanitization in applications that process untrusted user input. If user-supplied input is not properly validated before being used in security-sensitive operations like database queries, file system operations, or system commands, an attacker may be able to inject and execute malicious code.
Impact of Remote Code Execution Attacks
The impact of a successful RCE attack can be severe, depending on the privileges of the exploited application. In the worst case, RCE can allow an attacker to completely take over the vulnerable system and access sensitive data, install malware, and use the compromised machine for further attacks. Some potential consequences of RCE include:
- Sensitive data theft: The attacker can access and exfiltrate sensitive information stored on the system or accessible to the application, like customer data, financial records, intellectual property, etc.
- Malware installation: RCE often allows installation of malware like ransomware, spyware, trojans, rootkits, and bots, enabling the attacker to maintain access and control even after the initial attack.
- Lateral movement: A compromised machine can be used as a beachhead to launch further attacks against other systems on the same network, allowing the attacker to move laterally and compromise additional assets.
- Reputation damage: RCE attacks resulting in data breaches or service disruptions can severely damage an organization’s reputation and lead to loss of customer trust.
Types of Remote Code Execution Attacks
RCE attacks can take various forms depending on the vulnerability being exploited. Some common types of RCE include:
SQL Injection
SQL injection is a type of RCE attack that targets applications that construct SQL queries based on user input without proper validation. An attacker crafts malicious input containing SQL code, which is then executed by the database. For example:
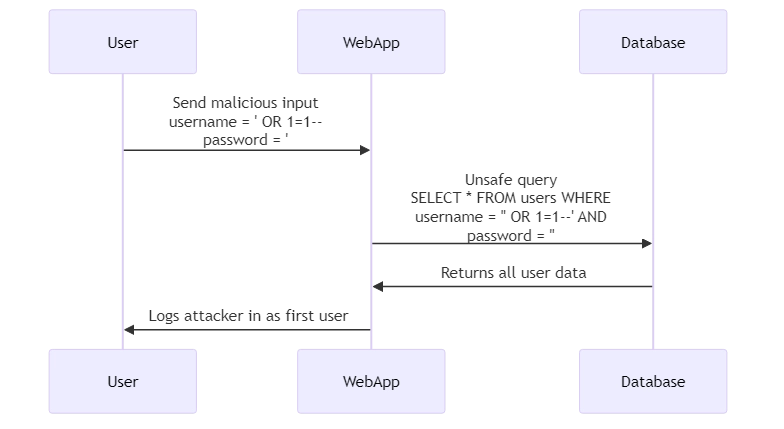
SELECT * FROM users WHERE username = '' OR 1=1--' AND password = '';
This input leads to the SQL query becoming:
SELECT * FROM users WHERE username = '' OR 1=1-- AND password = '';
The double dash (–) comments out the rest of the query, effectively removing the password check. The 1=1 condition is always true, so this logs the attacker in as the first user in the database.
To enable this attack, the application would have to construct the query by directly interpolating user input, like:
$query = "SELECT * FROM users WHERE username = '$_POST[username]' AND password = '$_POST[password]'";
To prevent SQL injection, user input should never be directly included in SQL queries. Instead, parameterized queries or prepared statements should be used.
Command Injection
Command injection RCE occurs when an application passes unsafe user input into a system shell. Attackers can inject shell commands which are then executed with the privileges of the vulnerable application. For instance, consider a web application that allows users to ping an address they provide:
system("ping -c 4 " . $_POST['address']);
An attacker could provide input like:
127.0.0.1 && cat /etc/passwd
This would result in the following command being executed:
ping -c 4 127.0.0.1 && cat /etc/passwd
After pinging localhost, the attacker’s injected command (cat /etc/passwd) would be executed, displaying sensitive system information.
To prevent command injection, application functionality requiring shell commands should be re-implemented in safer ways if possible. If shell commands are unavoidable, user input should be strictly validated against a whitelist of safe values.
Deserialization Attacks
Many programming languages allow serializing objects into strings which can be deserialized back into objects later. If an application deserializes user-controllable data without sufficient validation, an attacker may be able to manipulate the serialized string to inject malicious code that gets executed during deserialization.
For example, consider a Java application that deserializes user-provided session cookies:
Cookie sessionCookie = request.getCookies()[0]; byte[] serializedObject = Base64.getDecoder().decode(sessionCookie.getValue()); ObjectInputStream objectInputStream = new ObjectInputStream(new ByteArrayInputStream(serializedObject)); Object deserializedObject = objectInputStream.readObject();
An attacker could carefully craft a malicious serialized object that, when deserialized, executes arbitrary code through the readObject method, giving them RCE.
To prevent deserialization attacks, avoid deserializing untrusted data if possible. If deserialization is necessary, use language-specific safety features like the ValidatingObjectInputStream in Java. Deserialized objects should be treated as untrusted and validated thoroughly.
Summary and Conclusion
Remote Code Execution attacks allow attackers to execute arbitrary code on target systems, potentially giving them full control. RCE often results from improper handling of untrusted user input in applications. Key types of RCE include SQL injection, which targets unsafe database queries; command injection, which exploits improper shell command composition; and unsafe deserialization, which abuses serialization flaws to inject malicious code.
The impact of RCE can be severe, including sensitive data exposure, malware installation, lateral movement to other systems, and reputation damage. To protect against RCE, applications must validate and sanitize all untrusted input before using it in any sensitive operations. Specific prevention measures depend on the type of vulnerability but can include using parameterized queries, validating against strict whitelists, and avoiding unsafe deserialization.
For solutions to help secure your data and systems against RCE and other threats, consider DataSunrise’s user-friendly and flexible tools for database security, sensitive data discovery (including OCR to find sensitive data in images), and compliance. Contact our team to schedule an online demo and learn how DataSunrise can help protect your organization.
