
Streamlining Data Access with Universal Access Control Systems

Introduction
Today, organizations must manage and secure large amounts of data stored in many databases in our data-focused world. As data breaches become more sophisticated and frequent, the need for robust security measures has never been more critical. Enter the universal access controller – a game-changing solution that revolutionizes how we approach database access control.
This article delves into the world of universal access controllers, exploring their significance in modern database management and security. We will see how these tools can help control access to various data sources. This will ensure compliance and protect sensitive information.
What is Database Access Control?
Before we dive into the concept of universal access control, let’s briefly touch on the fundamentals of database access control.
An access control system is a security tool. It controls who can access data in a database. It also determines what actions they can take with the data. It’s the first line of defense against unauthorized access, data breaches, and other security threats.
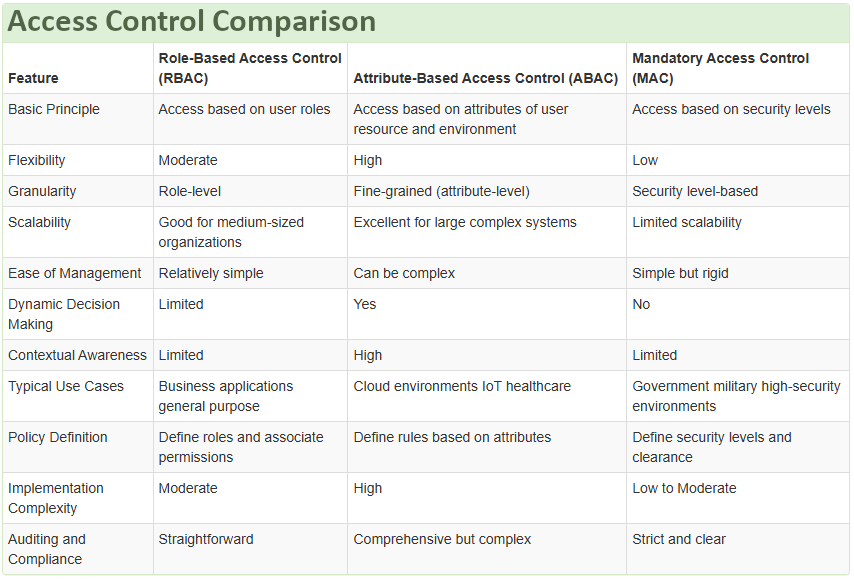
Traditional access control methods include:
- Role-Based Access Control (RBAC)
- Attribute-Based Access Control (ABAC)
- Mandatory Access Control (MAC)
These methods are effective, but they struggle with the complexities of modern data environments. This is especially true when working with multiple data sources.
Understanding Universal Access Control
Defining Universal Access Controller
A Universal Access Controller is an advanced security solution that provides centralized access control across multiple databases and data sources. It acts as a single point of control, allowing administrators to manage and enforce access policies consistently across diverse data environments.
Key features of a Universal Access Controller include:
- Centralized policy management
- Support for multiple database types
- Real-time monitoring and auditing
- Dynamic access control rules
- Data masking and encryption capabilities
All these features are implemented in DataSunrise software, which is one of the most widely used data access control solutions on the market. At DataSunrise, we focus on the simplicity of secure solutions while ensuring existing data safety. This approach offers two key advantages: First, the setup time for the most essential security tasks is minimal with DataSunrise. Second, DataSunrise can operate in four different modes, allowing you to choose the safest one for your needs.
The Need for Universal Access Control
As organizations adopt hybrid and multi-cloud environments, managing access control becomes increasingly complex. Universal Access Controllers address this challenge by providing a unified approach to data security.
Benefits of implementing a Universal Access Controller:
- Simplified administration
- Enhanced security posture
- Improved compliance management
- Reduced risk of data breaches
- Increased visibility into data access patterns
Implementing Universal Access Control
There are several ways to implement universal access control in your data environment. Let’s explore some common approaches:
1. Native Database Integration
This method involves configuring access control policies directly within each database system. While it leverages built-in security features, it can be challenging to maintain consistency across different database types.
2. Application-Level Implementation
In this approach, access control logic is built into the application layer. While it provides fine-grained control, it can lead to increased complexity and potential security gaps if not implemented properly.
3. Middleware Approach with Reverse Proxy
Middleware access control is gaining popularity due to its flexibility and effectiveness. It includes a reverse proxy for data access rules, masking, and auditing.
This type of access control is becoming more widely used. It is popular because it is flexible and effective. Let’s dive deeper into this method.
The Middleware Access Control: A Closer Look
The middleware approach to universal access control involves deploying a reverse proxy between clients and database servers. This proxy intercepts all database requests, applies access control rules, and forwards approved requests to the appropriate database.
How It Works
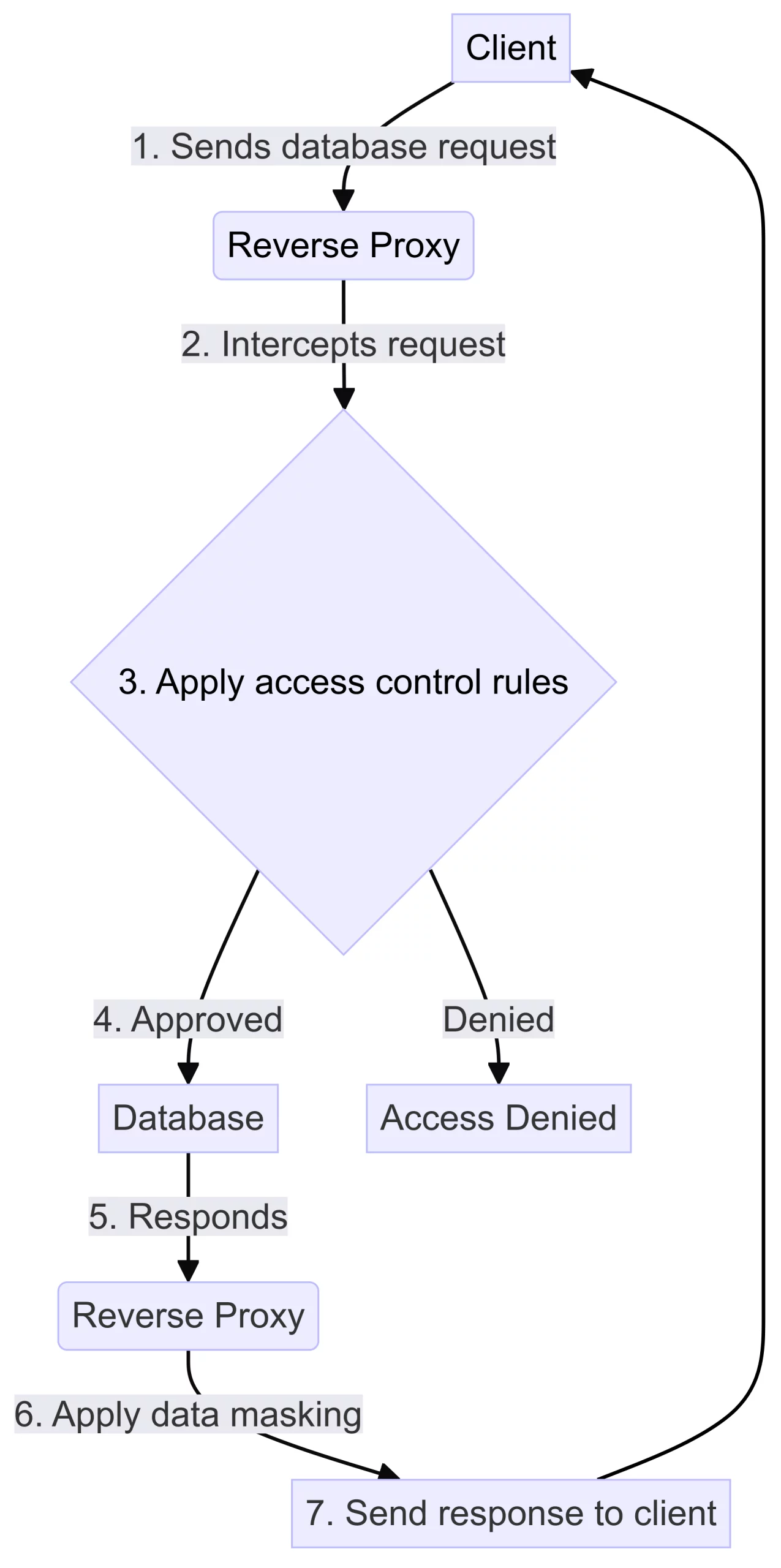
Key Components
- Reverse Proxy: Acts as an intermediary between clients and databases
- Policy Engine: Defines and enforces access control rules
- Auditing Module: Logs all database activities for compliance and security analysis
- Data Masking Engine: Applies data obfuscation techniques to protect sensitive information
Advantages of the Middleware Approach
- Centralized control: Manage access policies from a single point
- Database agnostic: Works with various database types and versions
- Non-intrusive: No changes required to existing databases or applications
- Real-time protection: Applies rules on-the-fly for dynamic access control
- Comprehensive auditing: Captures detailed logs for compliance and forensics
Best Practices for Universal Access Control
To maximize the effectiveness of your Universal Access Controller implementation, consider these best practices:
- Adopt a least privilege approach
- Regularly review and update access policies
- Implement strong authentication methods
- Use data classification to guide access control decisions
- Conduct regular audits and security assessments
- Provide ongoing training for administrators and users
Challenges and Considerations
While Universal Access Controllers offer significant benefits, there are some challenges to consider:
- Performance impact: Proxying requests may introduce latency
- Initial setup complexity: Configuring policies for diverse data sources can be time-consuming
- Keeping policies up-to-date: Regular reviews are necessary to maintain security
- Integration with existing systems: May require changes to network architecture
Future Trends in Universal Access Control
As technology evolves, we can expect to see advancements in Universal Access Control, including:
- AI-driven policy recommendations
- Enhanced integration with cloud services
- Improved support for IoT and edge computing scenarios
- More sophisticated data masking and encryption techniques
Conclusion
Universal Access Controllers represent a significant leap forward in database security and access management. Organizations can improve data access control, security, administration, and compliance with data protection laws by using a centralized system.
This system allows organizations to have better control over who can access data. It also helps in enhancing security measures. Additionally, it simplifies administrative tasks. Lastly, it ensures compliance with data protection laws.
The middleware approach offers a powerful and non-intrusive way to achieve universal access control. Organizations can control access, protect data, and track activity by monitoring database requests in real-time. You can do this without changing databases or applications.
As data systems become more complicated, Universal Access Controllers will be crucial for safeguarding valuable information and compliance.
DataSunrise offers user-friendly and flexible tools for database audit, masking, and compliance. To experience the power of universal access control firsthand, visit our website at DataSunrise.com for an online demo and discover how our solutions can enhance your database security across multiple data sources.
