
Vulnerability Assessment (VA)

What is Vulnerability Assessment?
Today, organizations deal with many cyber threats that can harm their systems and data security in the digital world. To stay safe, find and fix weaknesses before bad people can use them to harm you. This is where vulnerability assessment comes into play.
Vulnerability assessment is the process of systematically identifying, quantifying, and prioritizing the vulnerabilities in a system. Evaluating an organization’s IT infrastructure involves assessing networks, servers, applications, and databases to uncover weaknesses that attackers could exploit. By proactively identifying and addressing these vulnerabilities, organizations can significantly reduce their risk of falling victim to cyber attacks.
The Importance of Vulnerability Assessment
Regular vulnerability assessments are of utmost importance. Cyber attacks are becoming increasingly sophisticated, and attackers are constantly finding new ways to exploit vulnerabilities in systems and applications.
Organizations must actively search for and address vulnerabilities. If they do not, harmful attacks may target them. These attacks can result in data breaches, financial losses, and damage to their reputation.
Moreover, many industries are subject to regulatory requirements that mandate the implementation of robust security measures, including regular vulnerability assessments. The PCI DSS requires companies to conduct vulnerability scans every quarter. If you identify any issues, you must address them promptly.
Vulnerability Assessment: The Security Scanning Process
The vulnerability assessment process typically involves several key steps:
- Asset Discovery: First, identify all the assets in an organization’s IT system that require evaluation. This includes servers, workstations, network devices, applications, and databases.
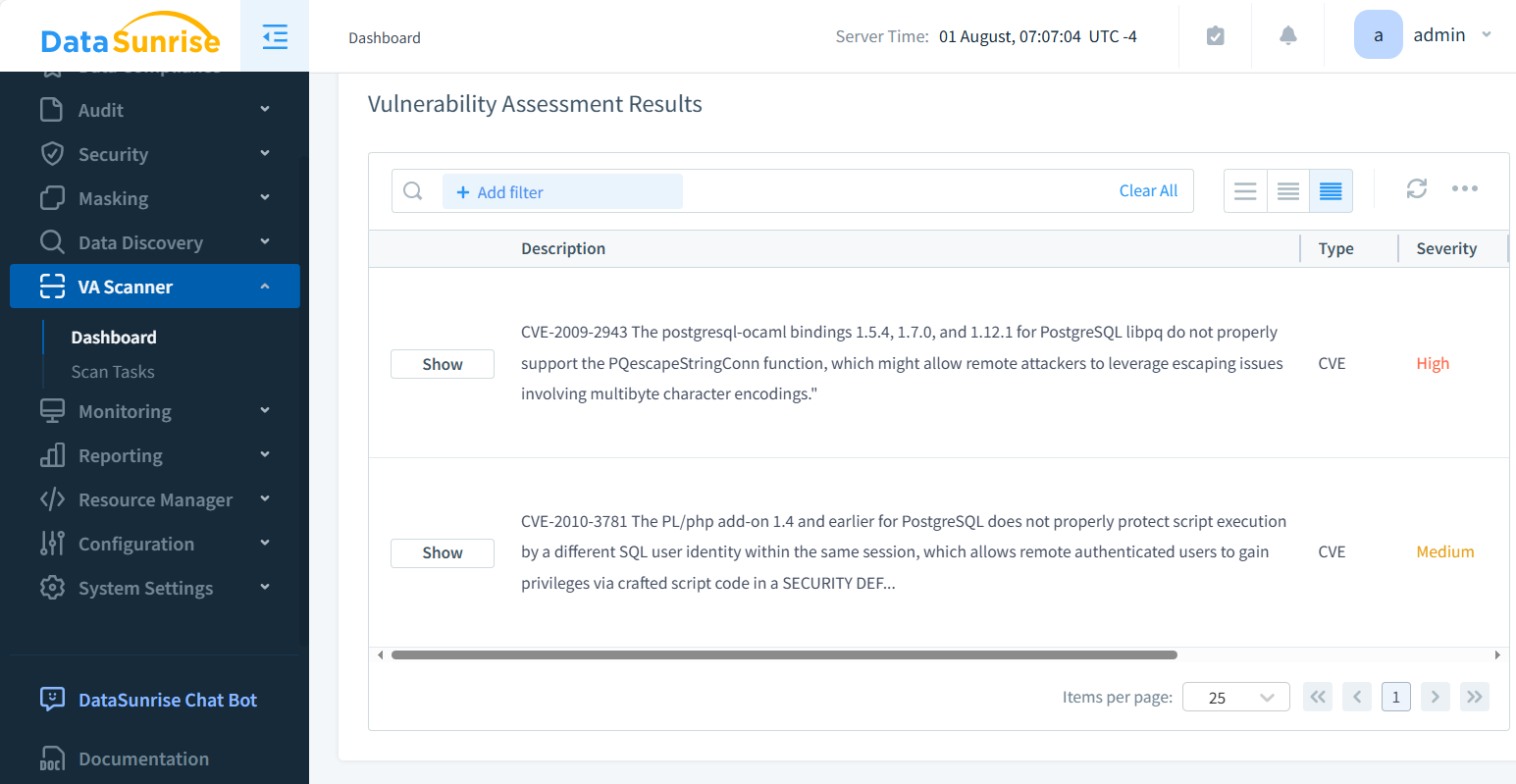
- Vulnerability Scanning: Automated vulnerability scanning tools scan the systems for known vulnerabilities after identifying the assets. These tools compare the system configurations against databases of known vulnerabilities and report any matches.
- Manual Testing: While automated scanning tools are effective at identifying known vulnerabilities, they may miss certain types of vulnerabilities that require manual testing. This may include testing for logical flaws in applications or attempting to bypass security controls.
- Risk Assessment: After identifying the vulnerabilities, assess them for their potential impact and likelihood of exploitation. Organizations use this to decide which vulnerabilities to fix first based on how risky they are.
- Remediation: Finally, we need to address the identified vulnerabilities through a combination of patches, configuration changes, and other remediation measures. Verifying that the remediation measures have been effective through follow-up vulnerability scans is important.
Vulnerability Assessment Tools
Many tools can assess vulnerabilities, from free options to high-quality commercial products. Some of the most popular vulnerability assessment tools include:
- Nessus: Nessus is a widely-used commercial vulnerability scanner that can identify vulnerabilities across a wide range of operating systems, devices, and applications.
- OpenVAS: OpenVAS is an open-source vulnerability scanner that provides a comprehensive set of tests for identifying vulnerabilities in systems and applications.
- Metasploit: Metasploit is an open-source penetration testing framework that includes a vulnerability scanner as well as tools for exploiting identified vulnerabilities.
- Burp Suite: Burp Suite is a widely used platform for testing web application security. It includes a vulnerability scanner and tools for manual testing and exploitation.
Consider the size and complexity of your IT system when selecting a vulnerability assessment tool. Also, take into account the skills of your security team. Also, consider any compliance rules that you must follow.
Vulnerability Assessment and Web Application Firewalls (WAF)
While vulnerability assessments are an essential component of a comprehensive security strategy, they are not a silver bullet. One additional layer of defense that organizations can deploy is a Web Application Firewall (WAF).
A WAF is a security tool that checks and blocks web traffic to and from a web application. It uses rules to check incoming traffic for potential attacks. These attacks include SQL injection, cross-site scripting (XSS), and other common web application vulnerabilities.
Adding a WAF in front of a web app can help protect against attacks, even if the app has vulnerabilities. However, it is important to note that one should not rely solely on a WAF for securing a web application. Regular vulnerability assessments and remediation efforts are still necessary to address underlying vulnerabilities and ensure the overall security of the application.
Vulnerability Management Systems
While conducting vulnerability assessments is an important first step, it is only one component of a comprehensive vulnerability management program. To effectively manage vulnerabilities over time, organizations need to implement a vulnerability management system.
A vulnerability management system is a centralized platform that allows organizations to track and manage vulnerabilities across their entire IT infrastructure. It typically includes features such as:
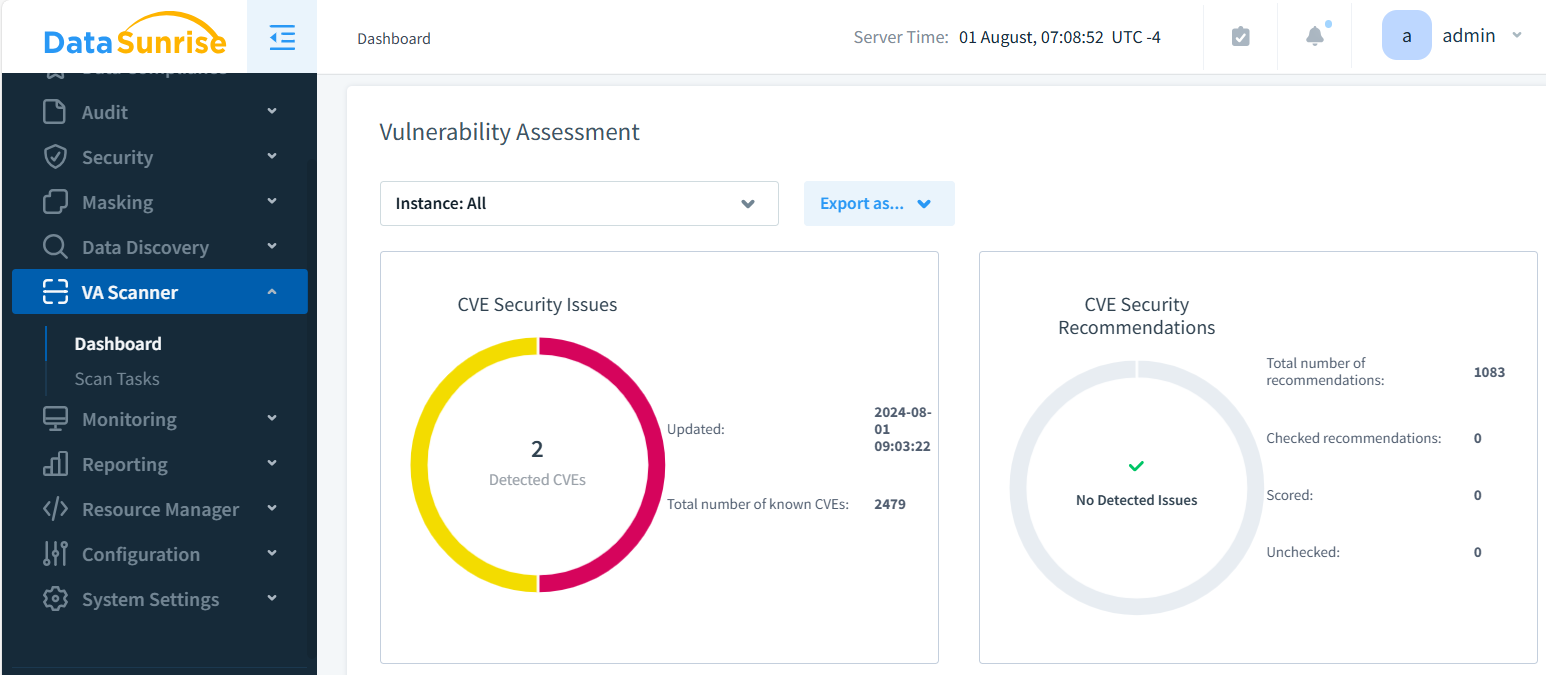
- Vulnerability Scanning: The ability to automatically scan systems and applications for vulnerabilities regularly.
- Vulnerability Prioritization: The ability to prioritize vulnerabilities based on their severity and potential impact on the organization.
- Remediation Tracking: Tracking progress to fix issues and ensuring prompt addressing of vulnerabilities.
- Reporting and Analytics: The ability to generate reports and dashboards that provide visibility into the organization’s overall vulnerability posture.
Organizations can ensure that they identify and address vulnerabilities in a consistent and effective manner over time by implementing a vulnerability management system.
Conclusion
In today’s digital landscape, vulnerability assessments are an essential component of any comprehensive security strategy. By proactively identifying and addressing vulnerabilities in systems and applications, organizations can significantly reduce their risk of falling victim to cyber attacks.
However, vulnerability assessments are just one piece of the puzzle. Organizations should have a strong vulnerability management program in place to protect their IT infrastructure. This program should include regular scans, prioritizing vulnerabilities, and promptly fixing any issues.
Additionally, organizations should consider deploying additional layers of defense, such as Web Application Firewalls, to provide an extra level of protection against potential attacks.
At DataSunrise, we offer user-friendly and flexible tools for database security, data discovery (including OCR), and compliance. Our solutions can help organizations identify and address vulnerabilities in their databases and ensure that they properly protect sensitive data. For more information, contact our team to book an online demo session.
