
What is Database Audit?
Most data breaches don’t start with complex attacks. They usually stem from everyday lapses—accounts that stay active too long, contractors with more access than they need, or sensitive data shared without proper safeguards. Each of these actions leaves a trace. Data auditing collects and structures these traces into logs that show what happened, who did it, when it occurred, and under what conditions. This gives security and compliance teams clear, evidence-based visibility instead of relying on assumptions.
With advanced analytics and automated alerts, auditing shifts from a reactive task to a proactive control. Teams can spot suspicious behavior sooner, apply least-privilege principles more effectively, and confirm that data usage aligns with internal policies and regulatory requirements. Solutions like User Behavior Analysis (UBA) enhance this by detecting unusual user activity patterns in real time.
- Identifying brute-force attacks and port scanning activities
- Preventing organization-wide malware and virus spread
- Discovering unauthorized software on workstation networks
- Countering internet-based fraud and phishing schemes
- Analyzing operational system failures and outages
- Detecting software vulnerabilities and performance issues
- Finding security gaps in data storage and access controls
Example: An employee retains outdated access rights and downloads sensitive HR data after transferring to another department. Without audit logging, this activity may go undetected for an extended period. With DataSunrise, the action would generate an immediate alert and be recorded with complete session details for further investigation.
Traditional security strategies tend to focus on external threats. In reality, internal risks from employees or contractors often remain unnoticed. Sensitive data can leak through messaging apps, cloud storage synchronization, or social platforms—channels that bypass standard DLP controls. In many situations, users expose data unintentionally by exporting reports to personal devices, syncing database backups to consumer cloud services, or sharing screenshots that contain confidential information. These actions are subtle and typically fall outside the visibility of perimeter-based defenses.
Conventional DLP tools are designed to track file transfers and email activity. However, the most critical data resides in databases, which operate over protocols these tools cannot interpret. As a result, risky behavior such as unauthorized queries, misuse of privileges, or large-scale data extraction via SQL often goes undetected. This gap highlights the need for database-focused security with full audit coverage. Dedicated monitoring solutions capture query-level activity, link actions to user identities, and identify abnormal access patterns—delivering a level of visibility that generic DLP systems simply cannot provide.
Key Takeaways: Database Auditing
- Database auditing extends DLP coverage by analyzing SQL activity and user behavior directly at the data layer.
- Focus audit logs on your most critical schemas to reduce overhead and improve threat visibility.
- Forward structured audit trails to your SIEM for better correlation and real-time threat detection.
- Use DataSunrise Database Audit to enforce consistent policies across Oracle, PostgreSQL, SQL Server, and cloud databases.
Building Database Audit Foundations
PostgreSQL Trigger: Establishing Basic Logging
Development teams can implement basic database logging with PostgreSQL triggers. This approach captures INSERT, UPDATE, and DELETE operations. It provides a practical foundation for comprehensive audit workflows:
-- PostgreSQL: Comprehensive audit trail for data operations
CREATE TABLE audit_log (
id SERIAL PRIMARY KEY,
operation TEXT NOT NULL,
user_name TEXT NOT NULL,
table_name TEXT NOT NULL,
old_row JSONB,
new_row JSONB,
executed_at TIMESTAMP DEFAULT current_timestamp,
session_id TEXT,
client_ip INET
);
CREATE OR REPLACE FUNCTION audit_trigger_fn()
RETURNS TRIGGER AS $$
BEGIN
INSERT INTO audit_log(operation, user_name, table_name, old_row, new_row, session_id, client_ip)
VALUES (
TG_OP,
session_user,
TG_TABLE_NAME,
CASE WHEN TG_OP = 'DELETE' THEN row_to_json(OLD) ELSE NULL END,
CASE WHEN TG_OP = 'INSERT' THEN row_to_json(NEW) ELSE row_to_json(NEW) END,
current_setting('application_name', true),
inet_client_addr()
);
IF TG_OP = 'DELETE' THEN
RETURN OLD;
ELSE
RETURN NEW;
END IF;
END;
$$ LANGUAGE plpgsql SECURITY DEFINER;
-- Apply trigger to sensitive tables
CREATE TRIGGER audit_trigger
AFTER INSERT OR UPDATE OR DELETE ON employees
FOR EACH ROW EXECUTE FUNCTION audit_trigger_fn();
This script works well for development environments or smaller deployments. For enterprise-scale compliance and advanced controls, organizations use specialized platforms like DataSunrise.
Heads-up Full-fidelity logging on a 5 TB OLTP cluster can add ≈30 % I/O and 150 GB/day of storage. Scope audits to high-risk schemas or budget accordingly.
Database Auditing — TL;DR, Checklist, Fixes
TL;DR (60 seconds)
- Enable native audit (
pgAudit/ SQL Server Audit / MySQL Audit). - Normalize events: actor, role, object, action, status, sensitivity.
- Tag PII/PHI/PCI at ingestion; alert on off-hours reads & bulk SELECT.
- Ship to SIEM; correlate with Activity Monitoring.
- Make evidence tamper-evident (hash chain or WORM/immutable store).
Implementation Checklist (8 steps)
- Scope high-risk schemas/roles and include failed attempts.
- Enable audit with minimal noise (
read,write,ddl). - Adopt a standard event schema (actor, role, object, action, status, tags).
- Apply sensitivity tags (PII/PHI/PCI) at ingestion.
- Create alerts: bulk reads, role change → DDL, dormant account login.
- Forward to SIEM and correlate with DataSunrise.
- Enforce rotation, retention, integrity (hash/WORM).
- Publish auditor-ready reports (SOX, GDPR, HIPAA, PCI DSS).
Native vs. DataSunrise — 10-second call
| Use Case | Native Only | DataSunrise |
|---|---|---|
| Single DB, lightweight evidence | ✔️ | — |
| Multi-DB estate, one console | — | ✔️ |
| Real-time alerts & behavior analytics | Limited | ✔️ |
| Compliance packs & exports | DIY | Pre-built |
| Immutable, normalized trails | Manual | Built-in options |
Rule of thumb: combine when you want DB-local logs + centralized correlation; replace when you manage many engines and need one pane of glass.
Enterprise Database Security and Monitoring
Real-Time Monitoring with DataSunrise
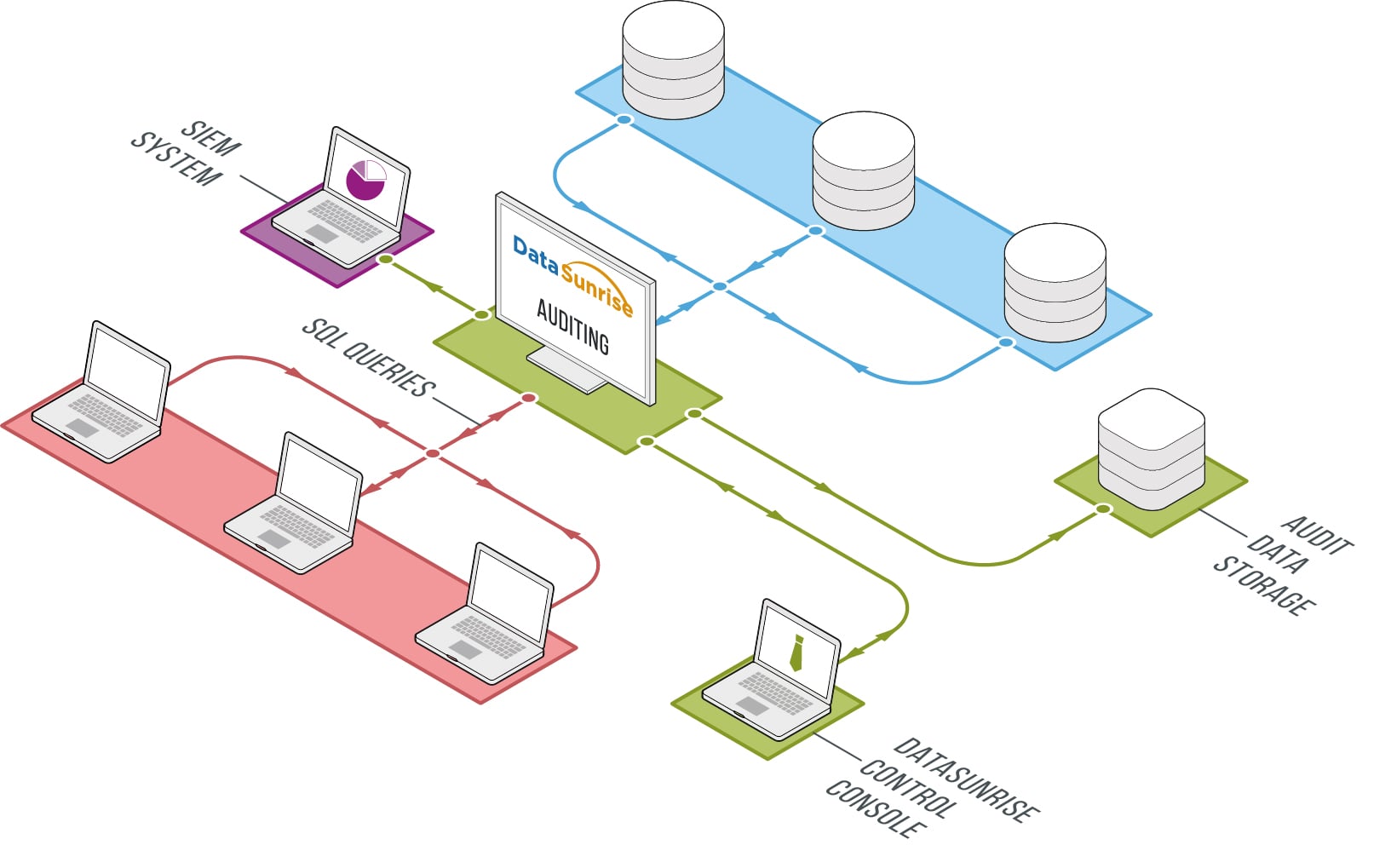
DataSunrise Security Suite performs deep packet inspection across multiple database platforms. Its activity monitoring engine tracks user behavior patterns, while audit logs can be exported to SIEM systems via Syslog for real-time correlation and alerting.
Tip: Pair database activity monitoring with advanced audit logging to reduce detection times and strengthen compliance posture across hybrid environments.
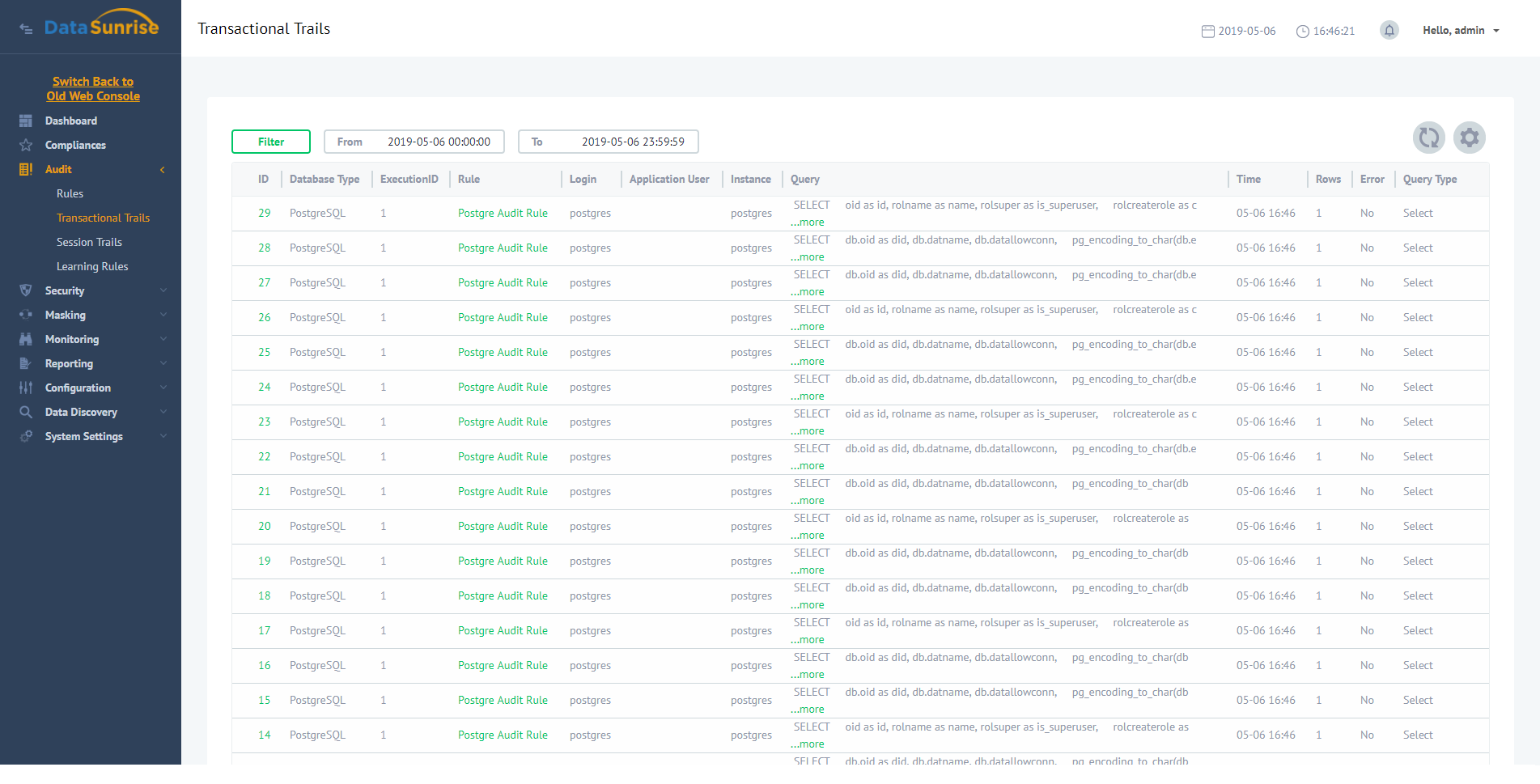
Beyond breach detection, audit logs help determine incident scope. Unusual query patterns, access spikes, or privilege abuse get flagged and traced. The Database Audit module uses pattern recognition to identify anomalies. It classifies them for detailed analysis.
Regulatory Compliance Through Audit Logging
SOX Compliance Through Audit Management
The Sarbanes-Oxley Act requires precise auditing of data access and privilege changes in financial systems. DataSunrise addresses these requirements by capturing:
- 1.1 Events from privileged users and unauthorized access attempts
- 1.2 Role escalations and access level changes
- 1.3 Failed authentication attempts and access denials
The System Events module logs authentication attempts and configuration changes. It helps identify unauthorized privilege use or system misconfigurations.
- 1.4 Database schema changes and data definition modifications
- 1.5 Unauthorized attempts to access protected financial data
Each audit entry includes session details and executed SQL statements. It captures IP addresses, user IDs, and affected tables. This enables compliance teams to track changes with exceptional precision.
PCI DSS Logging and Compliance
PCI DSS requires continuous audit logging for systems processing cardholder data. DataSunrise streamlines compliance with customizable rules and secure log storage.
- 10.1 Link each database operation to authenticated users
Sessions are monitored from login through logout. All queries and accessed objects get recorded comprehensively.
- 10.2 Automatically record access to sensitive tables and fields
- 10.3 Attach timestamps, usernames, source IPs, and result status
DataSunrise audit logs meet PCI format standards. They export in CSV and PDF formats. Optional data discovery adds classification for card numbers and PII.
- 10.5 Ensure logs are securely stored and protected from tampering
Logs write to PostgreSQL, MySQL, or SQLite databases. They can offload to external servers or SIEM tools for backup and retention.
- 10.6 Continuously monitor for suspicious activity in audit records
Each security rule can trigger real-time alerts. This gives security teams opportunities to respond before damage occurs.
Important Note: Additional PCI subclauses may require organization-specific configurations beyond this overview.
| Audit Event | ATT&CK ID | Detection Logic |
|---|---|---|
| Bulk SELECT on PII | T1030 | affected_rows > 10 000 |
| Schema change outside change window | T1070.006 | ddl_change & !business_hours |
| Dormant account login | T1078 | last_seen > 90 days |
Native Audit Cheatsheet (SQL Server & MySQL)
If you’re still running native-only, here are minimal, production-ready snippets to capture database activity history without third-party tooling.
SQL Server: Audit to File + Quick Read
-- Create a server audit writing to disk
CREATE SERVER AUDIT Audit_File
TO FILE (FILEPATH = 'C:\SQLAudits\', MAXSIZE = 1 GB, MAX_ROLLOVER_FILES = 20)
WITH (QUEUE_DELAY = 1000, ON_FAILURE = CONTINUE);
ALTER SERVER AUDIT Audit_File WITH (STATE = ON);
-- Track SELECT/WRITE on a critical DB (replace MyDB)
CREATE DATABASE AUDIT SPECIFICATION DbSpec_MyDB
FOR SERVER AUDIT Audit_File
ADD (SELECT, INSERT, UPDATE, DELETE ON DATABASE::MyDB BY PUBLIC),
ADD (SCHEMA_OBJECT_CHANGE_GROUP)
WITH (STATE = ON);
-- Read last hour of events
SELECT event_time, server_principal_name, database_name, statement
FROM sys.fn_get_audit_file('C:\SQLAudits\*.sqlaudit', DEFAULT, DEFAULT)
WHERE event_time > DATEADD(HOUR, -1, GETDATE())
ORDER BY event_time DESC;MySQL 8: Enterprise Audit (JSON)
-- Enable the audit plugin (paths vary by distro)
INSTALL PLUGIN audit_log SONAME 'audit_log.so';
-- JSON format; log everything but you should scope in prod
SET PERSIST audit_log_format = JSON;
SET PERSIST audit_log_policy = ALL;
-- Optional: rotate & size controls
SET PERSIST audit_log_rotate_on_size = 104857600; -- 100 MB
SET PERSIST audit_log_file = 'audit.log';
-- Example: verify plugin status
SHOW PLUGINS LIKE 'audit%';Native audit works—but every engine has different knobs, file formats, and blind spots. Correlation becomes a full-time job.
Tamper-Evident Audit Store (PostgreSQL Hash Chain)
Compliance loves immutability. This pattern writes a hash chain over your audit events so any tampering is obvious. Pair it with WORM storage (e.g., S3 Object Lock) for the belt-and-suspenders approach.
-- Requirements: pgcrypto
CREATE EXTENSION IF NOT EXISTS pgcrypto;
-- Append-only audit table
CREATE TABLE audit_events (
id BIGSERIAL PRIMARY KEY,
event_time TIMESTAMPTZ NOT NULL DEFAULT now(),
actor TEXT NOT NULL,
action TEXT NOT NULL,
object TEXT,
ip INET,
payload JSONB,
prev_hash BYTEA, -- previous row hash
row_hash BYTEA -- current row hash
);
-- Prevent updates/deletes
ALTER TABLE audit_events
ALTER COLUMN actor SET NOT NULL,
ALTER COLUMN action SET NOT NULL;
REVOKE UPDATE, DELETE ON audit_events FROM PUBLIC;
-- Insert wrapper to compute the hash chain
CREATE OR REPLACE FUNCTION audit_events_append()
RETURNS TRIGGER AS $$
DECLARE
v_prev BYTEA;
BEGIN
SELECT row_hash INTO v_prev
FROM audit_events
ORDER BY id DESC
LIMIT 1;
NEW.prev_hash := v_prev;
NEW.row_hash := digest(
coalesce(NEW.actor,'') || '|' ||
coalesce(NEW.action,'') || '|' ||
coalesce(NEW.object,'') || '|' ||
coalesce(NEW.ip::text,'') || '|' ||
coalesce(NEW.payload::text,'') || '|' ||
coalesce(NEW.event_time::text,'') || '|' ||
encode(coalesce(NEW.prev_hash, '\\x'), 'hex'),
'sha256');
RETURN NEW;
END;
$$ LANGUAGE plpgsql;
CREATE TRIGGER trg_audit_chain
BEFORE INSERT ON audit_events
FOR EACH ROW EXECUTE FUNCTION audit_events_append();
-- Verification query: detect breaks in the chain
WITH ordered AS (
SELECT id, row_hash, prev_hash,
lag(row_hash) OVER (ORDER BY id) AS expected_prev
FROM audit_events
)
SELECT *
FROM ordered
WHERE prev_hash IS DISTINCT FROM expected_prev;Result set must be empty. Any row returned indicates tampering or a broken chain.
Key Components of a Modern Data Audit Architecture
To implement effective database audit strategies, teams must design secure, scalable architectures that support real-time monitoring, structured logging, and automated compliance reporting. Below are essential components found in high-performing audit systems:
- Audit Capture Layer: Intercepts SQL queries, data definition changes, and user logins without affecting application performance. Tools like DataSunrise act as transparent proxies across Oracle, PostgreSQL, MySQL, and more.
- Log Normalization Engine: Converts raw audit events into a structured schema with consistent metadata—username, IP, timestamp, session ID, object accessed—regardless of database engine.
- Secure Audit Store: Retains logs in tamper-proof, immutable formats. Options include append-only PostgreSQL tables, external S3 buckets, or hardened SIEM integrations.
- Alerting and Correlation: Detects anomalies through rule-based or ML-powered models. For example, repeated access to PII by dormant accounts triggers escalation workflows.
- Reporting and Evidence Layer: Generates audit-ready reports in PDF, CSV, or custom JSON formats. Supports regulatory audits for SOX, GDPR, HIPAA, and PCI DSS.
These components enable organizations to detect breaches early, enforce least-privilege principles, and produce defensible logs during investigations. A modern data audit architecture doesn’t just record—it responds, correlates, and proves compliance.
Data Audit Requirements Across Regulations
Audit logging is a cornerstone of modern compliance. Each framework emphasizes traceability and accountability in slightly different ways. Mapping your data audit practices to these frameworks ensures readiness for external reviews and reduces compliance risk:
| Framework | Audit Expectations | How DataSunrise Helps |
|---|---|---|
| GDPR | Log personal data access, prove lawful basis for processing, and detect misuse quickly. | Granular audit policies for PII with automated reports for regulators. |
| HIPAA | Maintain full trails of PHI access, modifications, and disclosure attempts. | Centralized, tamper-evident logging with PHI tagging and integrity checks. |
| PCI DSS | Track cardholder data usage, failed login attempts, and suspicious queries. | Real-time monitoring with rule-based alerts for sensitive payment data. |
| SOX | Ensure accountability for financial record changes and privileged user actions. | Detailed trails of schema changes and access escalations with auditor-ready exports. |
By aligning audit logs with regulatory frameworks, DataSunrise Database Audit transforms raw database traces into compliance evidence, reducing manual preparation and improving security posture.
Measuring Data Audit Effectiveness
- MTTD: Detect suspicious activity in under 5 minutes
- Coverage: ≥95% of sensitive objects continuously monitored
- False Positive Rate: <1% with refined rules and tagging
- Compliance Readiness: Audit evidence available on demand
- Storage Efficiency: Log rotation and compression save 40–60% space
Industry Use Cases
Effective data auditing supports:
- Finance: Trace privilege abuse and insider fraud
- Healthcare: Prove PHI access accountability for HIPAA
- SaaS: Deliver audit evidence to customers for trust and compliance
- Government: Strengthen oversight and transparency
Data Audit FAQ
What is data auditing?
Data auditing is the systematic collection and review of database events—queries, logins, privilege changes, and schema updates—to establish accountability, support investigations, and demonstrate compliance.
How does database auditing differ from traditional DLP?
Traditional DLP inspects files and network traffic. Database auditing observes SQL activity at the data layer, linking actions to authenticated identities and specific objects, which improves traceability and evidence quality.
Which regulations rely on database audit evidence?
Regulatory frameworks such as SOX, GDPR, HIPAA, and PCI DSS require or strongly recommend audit logging to establish access transparency and control effectiveness.
How do I limit performance impact?
- Prioritize sensitive schemas and high-risk actions.
- Stream events to SIEM or a proxy to offload processing.
- Apply rotation, compression, and retention policies.
- Review noise routinely and refine rules.
What metrics show an effective audit program?
- Coverage of sensitive objects monitored.
- Mean time to detect (MTTD) and respond (MTTR).
- Alert precision (true/false positive ratio).
- Log integrity verification rate.
- Storage growth vs. retention objectives.
When should we move beyond native tools?
Scale, multi-DB estates, and compliance reporting needs typically warrant a platform with centralized policies, normalization, real-time alerting, and reporting. See DataSunrise Database Audit and Activity Monitoring.
The Future of Data Auditing
As threats evolve and compliance standards tighten, data auditing is shifting beyond simple log collection. Emerging trends include:
- AI-Powered Anomaly Detection: Machine learning models highlight deviations in SQL activity that human analysts might miss.
- Zero-Trust Enforcement: Every query is verified against contextual policies, reducing reliance on perimeter security.
- Immutable Audit Records: Blockchain and hash-chained storage provide tamper-proof evidence for regulators.
- Cloud-Native Integration: Direct pipelines to SIEM, SOAR, and CSPM platforms for unified security operations.
Organizations adopting these strategies move from reactive logging to proactive defense, ensuring data audit practices remain both compliant and resilient.
Conclusion: Strengthening Data Auditing and Governance
DataSunrise combines automated policy management, real-time monitoring, and compliance-oriented audit logging into a unified solution. Rather than relying on periodic manual checks, security and compliance teams gain continuous insight into all database activity, including queries, configuration updates, and access attempts. Each audit entry is enriched with detailed metadata—such as user identity, source IP address, application context, and executed SQL—enabling precise tracking and faster investigation of incidents.
Beyond basic logging, the platform offers flexible, rule-based auditing that allows organizations to monitor specific database objects, schemas, users, or query types. Teams can configure alerts, automate responses, and leverage centralized dashboards to quickly detect anomalies or policy breaches. This approach transforms security operations from reactive troubleshooting to proactive control, enhancing threat detection and strengthening governance practices.
Built for diverse IT environments, DataSunrise supports leading database platforms including Oracle, Microsoft SQL Server, Amazon Redshift, PostgreSQL, and MySQL. It accommodates both on-premises infrastructures and cloud-native deployments, making it well-suited for hybrid and multi-cloud architectures. Organizations can explore the solution through local deployments or access it via the AWS Marketplace and Microsoft Azure Marketplace, ensuring seamless adoption with minimal disruption.
Through policy-driven, automated auditing, DataSunrise enables organizations to meet regulatory requirements, accelerate investigations, and produce trustworthy audit evidence for both internal and external reviews. Audit logs become dynamic, insight-driven assets that contribute to risk management and governance strategies. As data environments grow more complex and compliance demands intensify, DataSunrise delivers consistent visibility, operational stability, and long-term data protection.
Protect Your Data with DataSunrise
Secure your data across every layer with DataSunrise. Detect threats in real time with Activity Monitoring, Data Masking, and Database Firewall. Enforce Data Compliance, discover sensitive data, and protect workloads across 50+ supported cloud, on-prem, and AI system data source integrations.
Start protecting your critical data today
Request a Demo Download Now