Cohesity + DataSunrise: Security Meets Resilience
Cohesity + DataSunrise
Cohesity and DataSunrise address different stages of data protection. For backup and recovery, Cohesity delivers immutable vaulting, air-gapped storage, and automated restore. DataSunrise monitors live database access, detects threats in real time, and controls data exposure at the SQL layer.
Together, they cover the full data security lifecycle — from real-time threat detection to immutable preservation and recovery.
Key Highlights
Database platforms monitored
Automated snapshot triggers
Manual intervention required
Although the two systems operate independently, they reinforce each other. DataSunrise detects threats at the database layer and signals Cohesity to act. In response, Cohesity preserves the data in an immutable, tamper-proof state — without any manual coordination.
How the Joint Solution Works
DataSunrise monitors every database query in real time. When it detects anomalous activity — SQL injection, privilege escalation, or behavioral anomalies — it triggers a response through the Cohesity REST API.
As a result, Cohesity creates an immutable snapshot, applies DataLock/WORM retention, or vaults data to FortKnox — depending on the configured policy. Because this response is automated, the system captures a clean copy of the data before damage can spread.
In effect, detection and preservation happen within the same event chain, without requiring SIEM orchestration or manual escalation.
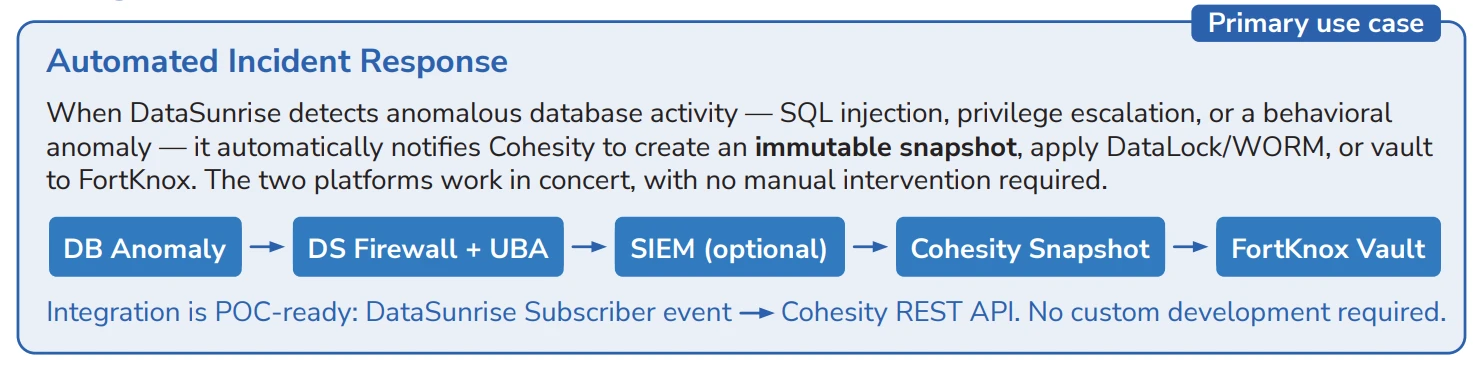
Automated Incident Response
The primary integration scenario connects DataSunrise threat detection directly to Cohesity data protection. Whenever a database anomaly is identified, the system automatically initiates a snapshot — preserving the current state before any potential data loss or corruption.
This approach eliminates the delay between detection and response. Rather than waiting for a security team to assess and act, the system triggers an immediate backup and stores it in an immutable format.
Moreover, the integration path is straightforward: DataSunrise Subscriber events feed into the Cohesity REST API, so no custom development or middleware is required.
Compliance Evidence Chain
On the detection side, DataSunrise captures a complete SQL audit trail — every query, bind parameters, session metadata, user identity, and affected objects. This provides the detailed evidence required for regulatory compliance.
Cohesity then stores that audit data under DataLock/WORM retention, making it tamper-proof and admin-resistant. For stricter isolation requirements, Cohesity can also vault the data to FortKnox with air-gapped protection.
Consequently, the combined chain — from query capture to immutable storage — satisfies requirements across SOX, HIPAA, GDPR, and PCI DSS 4.0 without requiring separate archival systems.
Secured Restored Environments
When Cohesity restores or clones production data for development, testing, or forensic analysis, the restored environment inherits the same security exposure as the original. Without additional controls, sensitive data in restored copies remains fully accessible.
However, DataSunrise addresses this by applying dynamic masking, firewall rules, and activity monitoring to restored environments immediately. As a result, security policies follow the data regardless of where it is deployed.
This means that cloned databases used for development or investigation do not become unmonitored copies of production data.
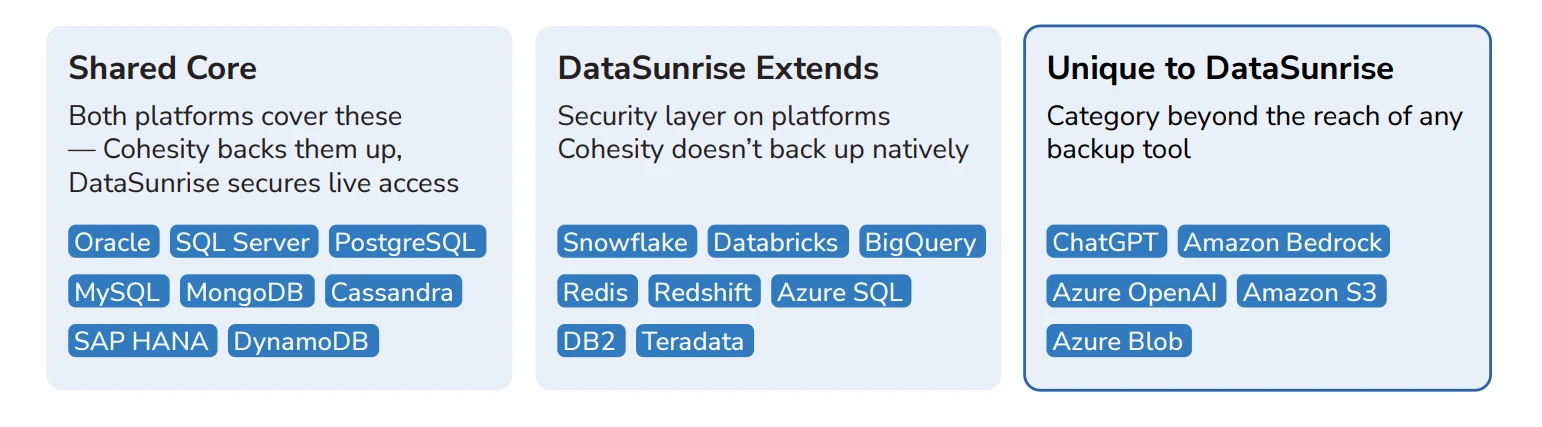
Database Coverage
Cohesity provides backup and recovery for major database platforms including Oracle, SQL Server, PostgreSQL, MySQL, MongoDB, Cassandra, SAP HANA, and DynamoDB.
In addition, DataSunrise extends security coverage to platforms beyond what backup tools typically reach — including Snowflake, Databricks, BigQuery, Redis, Redshift, Azure SQL, DB2, and Teradata. It also covers AI and cloud storage services such as ChatGPT, Amazon Bedrock, Azure OpenAI, Amazon S3, and Azure Blob.
Together, the two platforms therefore cover a broader range of data infrastructure than either could address alone. Cohesity protects what can be backed up, while DataSunrise secures what needs to be monitored.
Who This Is For
The combined approach is relevant for organizations that need both real-time threat response and resilient data recovery. It applies to environments handling regulated data, operating critical databases, or requiring demonstrable compliance evidence chains.
Different teams benefit in different ways depending on their responsibilities and recovery requirements.
Security Operations
Reduces the gap between threat detection and data preservation.
- Automated snapshot creation on anomaly detection
- Full attack timeline with query-level detail
- Coordinated response without manual escalation
Compliance Teams
Provides a tamper-proof evidence chain from query to vault.
- SQL audit trails preserved under WORM retention
- Air-gapped vaulting for sensitive audit data
- Supports SOX, HIPAA, GDPR, and PCI DSS 4.0
Infrastructure Teams
Ensures restored environments are secured from the moment of recovery.
- Dynamic masking applied to cloned databases
- Activity monitoring on restored environments
- Consistent policies across production and non-production
Conclusion
Cohesity and DataSunrise address different phases of data protection. One preserves data through immutable backup and recovery, while the other monitors and controls live access at the database layer.
Because they are connected through API integration, the two systems form a closed loop: detect, preserve, recover. Threats identified in real time trigger automated protection, and consequently, recovery operations inherit security controls from the start.
The result is a coordinated model for protecting data across its full lifecycle — from the moment of first access to the moment of full recovery.
FAQ
How do Cohesity and DataSunrise work together?
The integration works in real time. DataSunrise monitors database activity and detects threats such as SQL injection or privilege escalation. When an anomaly is detected, it triggers Cohesity through its REST API to create an immutable snapshot, apply WORM retention, or vault data to FortKnox — all without manual intervention.
Is custom development required for the integration?
No. The integration uses DataSunrise Subscriber events and the Cohesity REST API. It is POC-ready and does not require custom middleware or code changes.
What happens when DataSunrise detects a threat?
When a threat is detected, DataSunrise automatically notifies Cohesity to create an immutable backup snapshot, apply DataLock/WORM retention, or vault the data to FortKnox. This preserves a clean copy of the data before any damage can spread.
How does this help with compliance?
The system generates a full SQL audit trail including queries, parameters, and session metadata. Cohesity then preserves this evidence under tamper-proof WORM retention or air-gapped FortKnox vaulting. Together, the combined chain supports SOX, HIPAA, GDPR, and PCI DSS 4.0 requirements.
Are restored databases automatically secured?
Yes. When Cohesity restores or clones a database, DataSunrise can apply dynamic masking, firewall rules, and activity monitoring to the restored environment immediately, ensuring cloned data does not become an unmonitored copy of production.
Protect Your Data with DataSunrise
Secure your data across every layer with DataSunrise. Detect threats in real time with Activity Monitoring, Data Masking, and Database Firewall. Enforce Data Compliance, discover sensitive data, and protect workloads across 50+ supported cloud, on-prem, and AI system data source integrations.
Start protecting your critical data today
Request a Demo Download Now
