How to Mask Sensitive Data in Sybase
Masking sensitive data in Sybase ASE remains a practical challenge due to the absence of native runtime data masking capabilities.
Sybase provides foundational security features such as authentication, encryption, and access control. However, these mechanisms operate at the connection and object access level. Once a query is executed, the database does not natively restrict or transform the visibility of sensitive data within the result set.
In practice, this means that users with SELECT permissions on a table can access full, unmasked data, regardless of whether all fields are required for their role. This directly conflicts with modern data protection expectations outlined in regulations such as GDPR and industry standards like PCI DSS.
This limitation becomes significant in environments where multiple roles interact with the same datasets, including analysts, developers, support teams, and external systems. While access can be granted at the object level, Sybase does not provide built-in mechanisms for partial data exposure or context-aware masking at query time.
To address this gap, organizations rely on native workarounds such as views, stored procedures, and role-based access control. Although these approaches can reduce exposure, they introduce operational complexity, increase maintenance overhead, and are difficult to enforce consistently at scale. More advanced approaches typically involve external platforms that provide dynamic data masking, centralized data security, and automated data compliance controls.
This article examines how sensitive data masking is implemented in Sybase using native techniques, outlines their limitations, and explores more scalable approaches based on centralized, policy-driven masking.
Importance of Masking Sensitive Data
Protecting sensitive data is no longer optional. It is a baseline requirement for operating any system that processes personal, financial, or confidential business information.
In Sybase environments, the absence of native runtime masking increases the risk of unintended data exposure. Even when access controls are properly configured, users with legitimate permissions may still retrieve more data than necessary for their role. This violates the principle of least privilege and creates unnecessary risk, especially when handling personally identifiable information (PII).
Masking addresses this problem by limiting data visibility without restricting access to the underlying dataset. As a result, teams can continue working with production systems while sensitive fields remain protected using techniques such as dynamic data masking.
From a compliance perspective, masking plays a critical role in meeting regulatory requirements. Standards such as GDPR and PCI DSS require organizations to minimize exposure of sensitive data. Without masking, enforcing these requirements becomes significantly more complex and often relies on manual processes. Implementing structured data compliance controls helps ensure consistent protection across environments.
Operationally, masking also supports safer development and testing workflows. Instead of copying raw production data into non-production environments, masked data can be used to preserve structure and usability without exposing sensitive values. This aligns with modern test data management practices.
Finally, masking improves audit readiness. When sensitive fields are consistently protected across all access paths, organizations can demonstrate stronger control over data handling practices, reducing the risk of violations and simplifying compliance reporting.
In short, masking is not just a security enhancement—it is a necessary control for maintaining data integrity, regulatory compliance, and controlled access in modern database environments.
Native Sybase Data Masking Techniques
Sybase ASE does not provide a built-in framework for dynamic data masking at query execution time. As a result, organizations must rely on native SQL-based techniques to control how sensitive data is exposed to users.
These approaches are typically implemented at the application or database logic level and aim to simulate masking behavior by transforming query results or restricting access paths. While they can provide a basic level of protection, they are not centralized and require careful coordination between database design, access control, and query logic.
Below are the most commonly used techniques for masking sensitive data in Sybase environments.
1. Masking with Views
The most common workaround in Sybase is the use of masked views. Instead of granting direct access to base tables, administrators create views that apply string manipulation functions to hide sensitive values such as email addresses or card numbers. Users are then instructed to query these views rather than the underlying tables.
CREATE VIEW masked_customers AS
SELECT
id,
LEFT(email, 1) + '***@' + SUBSTRING(email, CHARINDEX('@', email)+1, LEN(email)) AS email,
'XXXX-XXXX-XXXX-' + RIGHT(card_number, 4) AS card_number
FROM customers;
While this approach appears structured, it introduces several issues. Each table requires its own masking logic, which leads to duplication and inconsistency over time. In addition, access control must be carefully enforced—any direct access to the base table immediately bypasses masking. As the number of views grows, performance overhead and maintenance complexity increase significantly.
2. Stored Procedures for Controlled Access
Another method involves encapsulating queries within stored procedures that return only masked or limited data. This allows administrators to control exactly what is exposed to the user.
CREATE PROCEDURE get_customer_data
AS
SELECT
id,
'***MASKED***' AS ssn,
name
FROM customers;
However, this approach restricts flexibility. Users cannot perform ad-hoc queries and must rely entirely on predefined procedures. In practice, developers and analysts often bypass these restrictions to regain query freedom. Over time, managing and updating multiple procedures becomes difficult, especially in dynamic environments with changing data requirements.
3. Role-Based Access Control (RBAC)
Role-Based Access Control is used to limit access to specific tables or columns by assigning permissions to user roles. In theory, this allows administrators to prevent access to sensitive fields.
GRANT SELECT ON customers TO analyst_role;
DENY SELECT ON customers(ssn) TO analyst_role;
In reality, Sybase provides only limited support for fine-grained, column-level control. RBAC does not offer dynamic masking capabilities, meaning it cannot modify data visibility based on context. Instead, access is binary—users either see the full value or are denied access entirely. This makes RBAC insufficient for scenarios where partial data exposure is required.
4. Manual Data Obfuscation
Manual data obfuscation involves directly modifying sensitive values within the database, typically through update operations. This approach is sometimes used when preparing datasets for development or testing environments.
UPDATE customers
SET email = '[email protected]';
While effective for non-production use, it is not suitable for live systems. Once data is altered, the original values are lost, making this method irreversible in practice. As a result, it cannot support real-time access scenarios where both usability and data protection are required simultaneously.
Dynamic Data Masking Architecture with DataSunrise
Unlike native Sybase approaches, where masking logic is embedded into SQL objects, DataSunrise implements masking at the data access layer. It operates as an intermediary between the client and the database, intercepting queries and modifying result sets in real time based on predefined policies. This approach aligns with modern database security practices that separate protection logic from the data layer.
This architecture allows masking to be applied dynamically without altering database schemas, rewriting queries, or modifying applications. As a result, organizations can enforce consistent data protection across all access points, including direct queries, BI tools, APIs, and third-party integrations.
Masking rules are defined centrally and evaluated at runtime. When a query is executed, DataSunrise analyzes the request context—such as user role, source IP, or query type—and applies the appropriate transformation to sensitive fields before returning the result. This works in combination with database activity monitoring to ensure full visibility into how data is accessed.
Key Capabilities
Zero-Touch Data Masking
DataSunrise applies masking without requiring any changes to the underlying database, schema, or application logic. This eliminates the need to create views, modify stored procedures, or duplicate data structures.
Because masking is enforced externally, deployment is non-intrusive and can be implemented without disrupting existing workflows or requiring downtime. This is typically achieved through proxy-based architectures such as a reverse proxy.

Centralized Policy Management
All masking rules are managed from a single interface. Instead of distributing logic across multiple database objects, administrators define policies once and apply them consistently across all environments.
This reduces configuration drift, simplifies updates, and ensures that masking behavior remains uniform regardless of how data is accessed. Centralization also supports broader data management strategies.
Context-Aware Protection
Masking decisions are not static. DataSunrise evaluates multiple contextual parameters in real time, including user roles, application sources, IP addresses, and query patterns.
For example, the same query may return fully visible data for administrators, partially masked data for analysts, and fully obfuscated data for external users. This enables fine-grained control over data visibility without restricting access entirely.
Sensitive Data Discovery
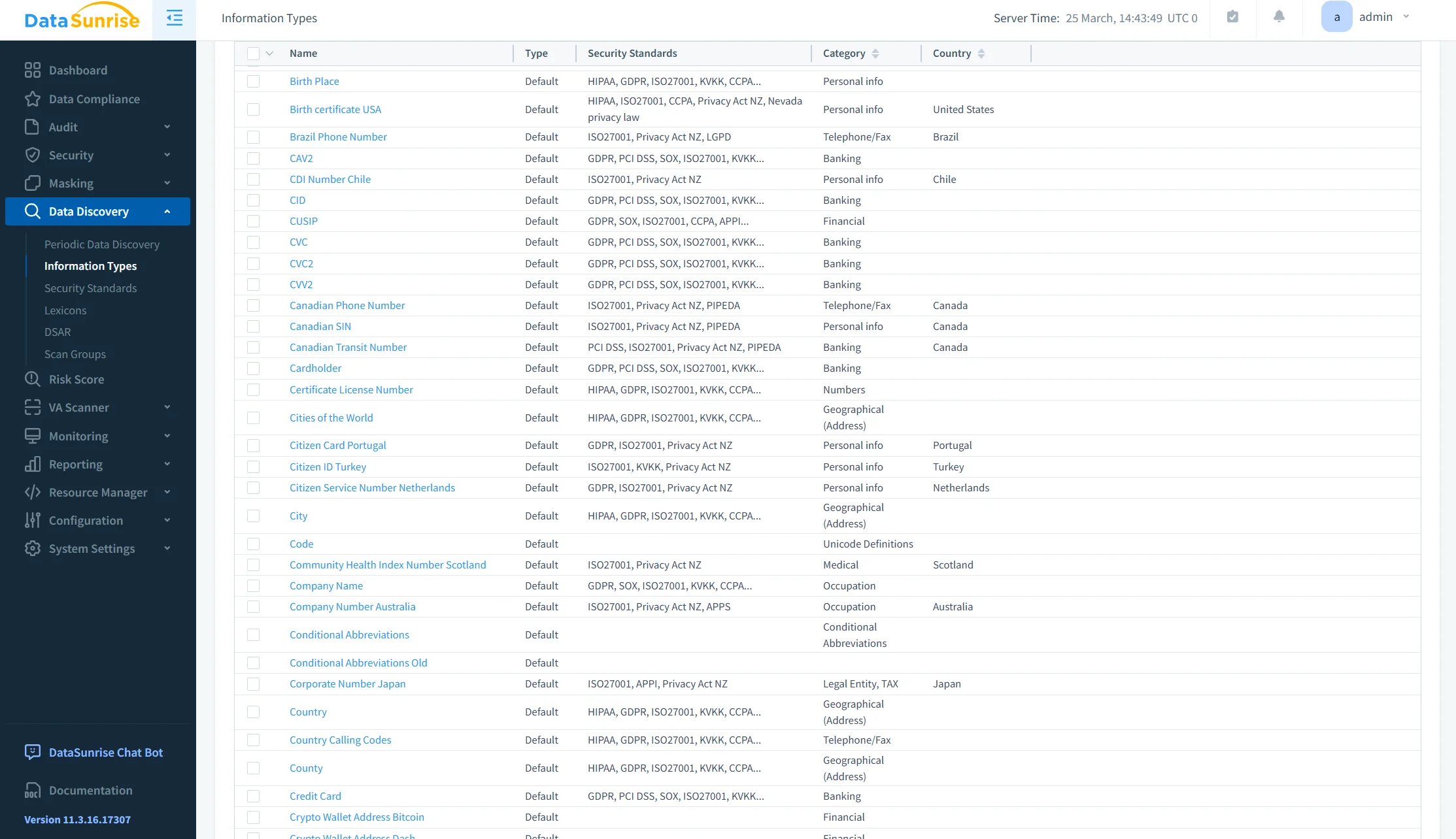
Before masking can be applied effectively, sensitive data must be identified. DataSunrise includes automated discovery capabilities that scan databases to detect sensitive fields such as PII, financial data, or credentials.
This reduces reliance on manual classification and helps ensure that no critical data is left unprotected due to oversight. Automated data discovery ensures continuous coverage as new data appears.
Compliance Autopilot
DataSunrise supports alignment with major regulatory frameworks such as GDPR, HIPAA, and PCI DSS by providing predefined policies and automated enforcement mechanisms.
Masking rules can be mapped directly to compliance requirements, enabling continuous enforcement and simplifying audit preparation. Instead of manually configuring controls for each regulation, organizations can rely on automated policy orchestration to maintain compliance across environments using compliance management tools.
Business Impact of Data Masking in Sybase
| Impact | Description |
|---|---|
| Reduced Exposure | Sensitive data remains protected at query time, preventing unauthorized visibility and supporting data security best practices. |
| Faster Compliance | Masking policies help align with GDPR, HIPAA, and PCI DSS requirements through automated data compliance controls. |
| Lower Maintenance | Eliminates the need to manage multiple views, stored procedures, and fragmented logic by centralizing dynamic data masking rules. |
| Secure Data Access | Users can safely work with production data while sensitive fields are protected, aligned with access control strategies. |
| Audit Readiness | Consistent masking policies improve traceability and simplify reporting through automated reporting and audit processes. |
Conclusion
Sybase provides control over access through authentication, permissions, and role-based mechanisms. However, it does not provide native control over data visibility at the query result level.
As a result, native masking techniques—such as views, stored procedures, and RBAC—can only partially address data protection requirements. While these approaches may be sufficient in limited environments, they introduce fragmentation, increase maintenance overhead, and are difficult to enforce consistently at scale. They also lack integration with broader data security and database security strategies.
Effective protection of sensitive data requires masking to be applied dynamically at runtime, directly within query results. This ensures that data exposure is controlled without modifying application logic or database structures.
DataSunrise addresses these limitations by implementing centralized, policy-driven masking at the data access layer. It enables consistent enforcement of dynamic data masking rules across all access channels, while integrating with database activity monitoring for visibility and control.
In addition, alignment with regulatory requirements is supported through automated data compliance capabilities, reducing manual effort and improving audit readiness.
In this model, masking becomes a controlled, scalable mechanism rather than a collection of isolated SQL-based workarounds.
Protect Your Data with DataSunrise
Secure your data across every layer with DataSunrise. Detect threats in real time with Activity Monitoring, Data Masking, and Database Firewall. Enforce Data Compliance, discover sensitive data, and protect workloads across 50+ supported cloud, on-prem, and AI system data source integrations.
Start protecting your critical data today
Request a Demo Download Now
