Data Anonymization in ClickHouse
Modern analytical platforms process massive volumes of sensitive data. As organizations scale their use of real-time analytics, protecting personal and confidential information becomes a hard requirement, not a “nice-to-have.”
ClickHouse is built for speed and high-throughput analytics. However, it does not provide native, full-spectrum anonymization workflows out of the box. That leaves teams stitching together SQL logic, access controls, and external tooling. According to the GDPR framework, organizations must ensure personal data is properly protected or anonymized to prevent misuse. Similarly, guidance from NIST Privacy Framework emphasizes minimizing exposure of sensitive data in analytical environments.
This article walks through practical anonymization techniques in ClickHouse and shows how to extend them with automated, compliance-ready solutions. To better understand how anonymization fits into broader protection strategies, you can also explore data security, data discovery, and dynamic data masking approaches.
What is Data Anonymization in ClickHouse?
Data anonymization transforms sensitive data into a form that cannot be linked back to an individual, while still preserving analytical value.
Unlike masking (which hides data conditionally), anonymization is typically irreversible. Once applied, the original value cannot be reconstructed.
Typical use cases include:
- Analytics on user datasets
- Sharing data with third parties
- Testing and development environments
- Regulatory compliance (GDPR, HIPAA, PCI DSS)
Native Data Anonymization Techniques in ClickHouse
ClickHouse gives you raw power — but no safety rails. You build anonymization manually using SQL transformations.
1. Hash-Based Anonymization
A common approach is hashing sensitive values.
SELECT
user_id,
SHA256(email) AS email_hash,
SHA256(phone) AS phone_hash
FROM users;
This removes direct identifiers while keeping data usable for joins and grouping.
Reality check:
- Deterministic → can be vulnerable to dictionary attacks
- No salt by default → weak for high-risk data
2. Tokenization via Mapping Tables
You can replace real values with tokens using lookup tables.
CREATE TABLE token_map (
original String,
token String
) ENGINE = MergeTree()
ORDER BY original;
Then:
SELECT
u.id,
t.token AS email_token
FROM users u
JOIN token_map t ON u.email = t.original;
This keeps referential integrity across datasets.
Downside:
You now manage a sensitive mapping table — congrats, you just created another liability.
3. Data Generalization
Reduce precision instead of removing data.
SELECT
user_id,
toStartOfMonth(birth_date) AS birth_month,
substring(ip_address, 1, 7) AS ip_partial
FROM users;
Useful for:
- Aggregation
- Trend analysis
Not useful for:
- Anything requiring exact values (obviously)
4. View-Based Anonymization
Create controlled access layers using views.
CREATE VIEW users_anonymized AS
SELECT
id,
SHA256(email) AS email,
'REDACTED' AS phone
FROM users;
Grant access only to the view:
GRANT SELECT ON users_anonymized TO analyst_role;
This reduces exposure risk — assuming nobody gets direct table access (big assumption).
Automated Data Anonymization with DataSunrise
Here’s where things stop being duct tape engineering.
DataSunrise deploys Zero-Touch Data Masking and Anonymization with Autonomous Compliance Orchestration, eliminating manual rule management and reducing human error. Instead of relying on scattered SQL scripts and inconsistent transformations, it introduces a centralized layer that enforces anonymization policies across all data flows in real time.
This shifts anonymization from a one-time operation into a continuous, controlled process aligned with security and compliance requirements.
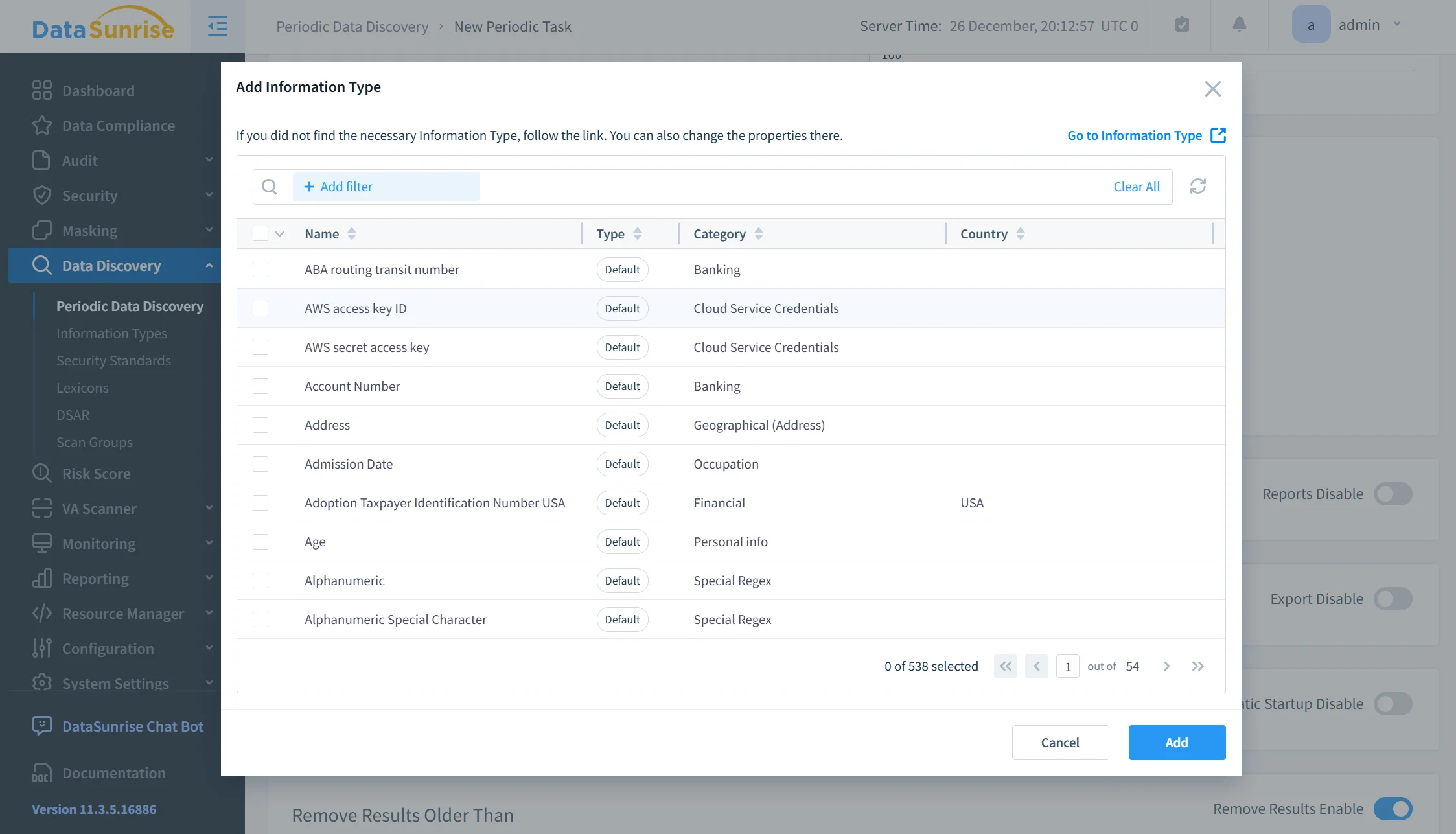
Auto-Discover & Classify Sensitive Data
Using data discovery,
DataSunrise automatically scans ClickHouse datasets to identify sensitive fields such as PII, financial data, credentials, and behavioral attributes.
It supports both structured and semi-structured data, which means it does not rely solely on obvious column names like email or phone. Instead, it detects patterns, context, and hidden sensitive values across large datasets. As a result, teams no longer depend on manual tagging or assumptions about where sensitive data resides — a common source of anonymization gaps.
Centralized Policy Enforcement
Instead of embedding anonymization logic into queries, views, or pipelines, DataSunrise allows policies to be defined once and enforced consistently across all access points. This includes queries coming from BI tools, API access, direct database connections, and internal analytical workflows.
Because enforcement happens at the platform level, there is no easy way to bypass controls through custom queries or alternative access paths. Every request is evaluated against the same rule set, which removes inconsistencies between teams and environments and ensures uniform protection.
Compliance Autopilot
DataSunrise maps anonymization policies directly to regulatory frameworks such as GDPR, HIPAA, and PCI DSS.
Instead of manually interpreting compliance requirements, organizations can rely on predefined templates that enforce key principles like data minimization, controlled access, and irreversible anonymization where required. This approach reduces the risk of misconfiguration and significantly shortens audit preparation cycles, removing the typical last-minute scramble before regulatory checks.
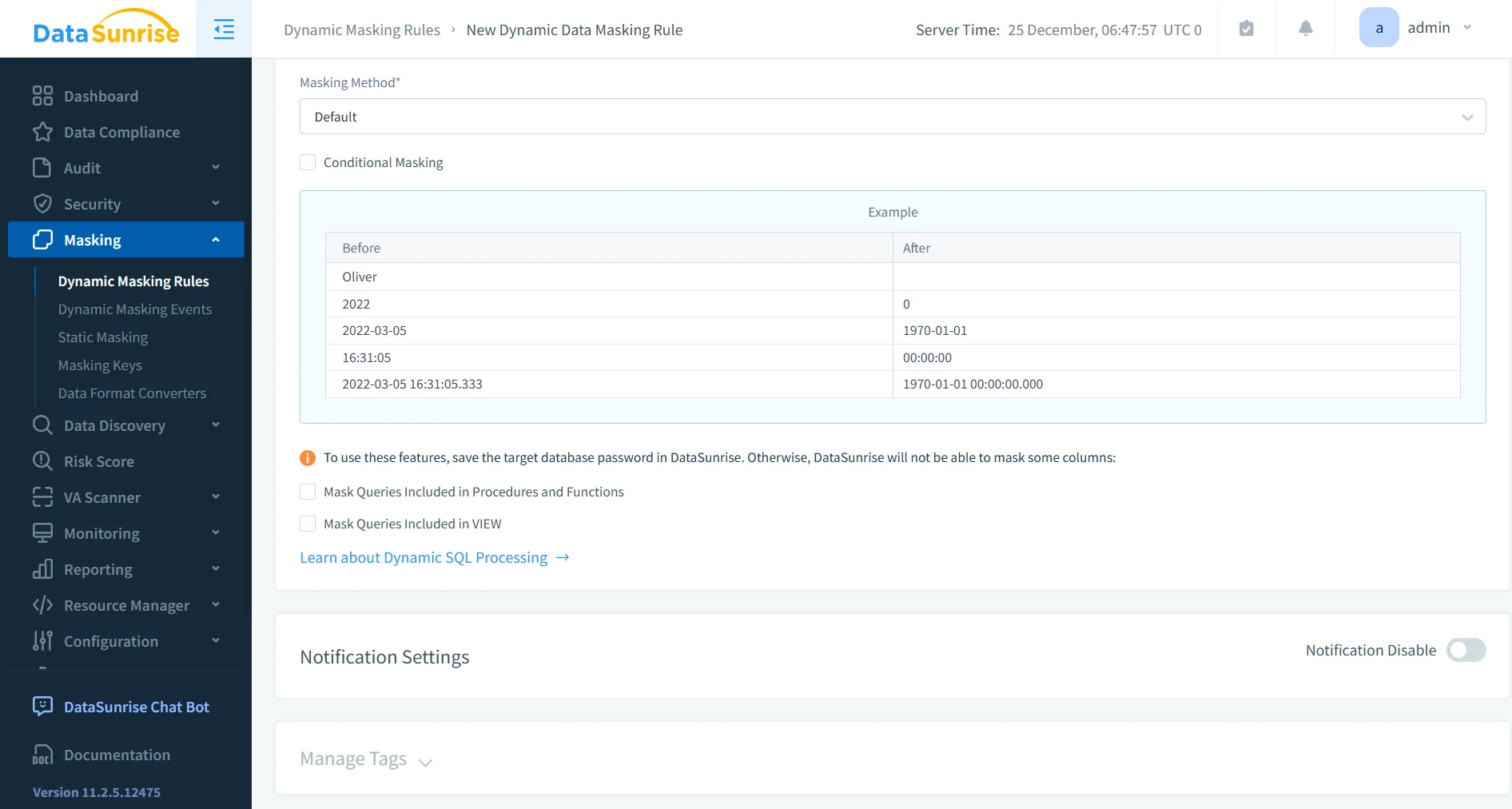
Dynamic + Static Anonymization
DataSunrise supports both static and dynamic anonymization approaches, allowing organizations to apply the right method depending on the use case.
Static anonymization permanently transforms stored data, making it suitable for data sharing scenarios and non-production environments such as testing and development. Dynamic anonymization, on the other hand, modifies data in real time based on user roles, access levels, and query context, which is essential for production analytics and controlled access.
By combining both approaches, organizations achieve full coverage across the data lifecycle without sacrificing usability or analytical accuracy.
Real-Time Monitoring & Audit Integration
Every anonymization action is tracked and correlated with user activity through database activity monitoring.
This provides complete visibility into who accessed which data and how anonymization policies were applied in each case. It also enables immediate detection of suspicious access patterns, allowing security teams to respond quickly to potential threats.
Unlike native ClickHouse setups, where anonymization and auditing are often disconnected, DataSunrise integrates both into a unified control layer. This eliminates blind spots and provides clear, traceable evidence during investigations and compliance reviews.
Business Benefits of Data Anonymization
Implementing data anonymization in analytical platforms delivers measurable business advantages.
| Benefit | Description |
|---|---|
| Reduced Risk Exposure | Sensitive data remains anonymized even when analysts query production datasets, minimizing the risk of leaks and unauthorized access. |
| Faster Compliance | Automated anonymization policies reduce manual effort and help organizations meet regulatory requirements more efficiently. |
| Safe Data Sharing | Anonymized datasets can be shared with third parties without exposing personally identifiable information (PII). |
| Operational Efficiency | Centralized anonymization removes fragmented SQL logic and simplifies data protection across environments. |
Conclusion
ClickHouse gives you speed. It does not give you safety.
Native anonymization techniques — hashing, tokenization, views — work, but they require constant control and discipline. In small environments, that’s manageable. At scale, it turns into fragmented logic, inconsistent protection, and growing operational risk. The more teams and data sources you add, the harder it becomes to guarantee that sensitive data is actually anonymized everywhere it should be.
The real issue is not the lack of tools, but the lack of coordination. Without centralized control, anonymization becomes dependent on individual queries, developers, and assumptions — which is exactly how data exposure incidents happen.
DataSunrise replaces manual anonymization with centralized, automated, compliance-driven protection, covering ClickHouse and dozens of other platforms under a unified security framework. By combining data discovery, dynamic data masking, database activity monitoring, and compliance automation,
it transforms anonymization from a fragile workaround into a controlled, scalable process.
This approach ensures that sensitive data is consistently protected across environments, access points, and use cases — without relying on manual intervention or scattered SQL logic. At the same time, it provides auditability, visibility, and alignment with regulatory requirements, which are non-negotiable in modern data architectures.
If you want anonymization that actually scales — not just survives — it’s time to stop writing ad-hoc SQL and start using a system built for it.
Protect Your Data with DataSunrise
Secure your data across every layer with DataSunrise. Detect threats in real time with Activity Monitoring, Data Masking, and Database Firewall. Enforce Data Compliance, discover sensitive data, and protect workloads across 50+ supported cloud, on-prem, and AI system data source integrations.
Start protecting your critical data today
Request a Demo Download Now
