Data Masking Tools and Techniques in ScyllaDB
ScyllaDB processes massive volumes of real-time data across distributed clusters. However, high throughput does not eliminate regulatory pressure. Modern architectures still store payment details, health records, credentials, and other forms of personal information. Without proper controls, even read-only access can expose sensitive values.
Regulators increasingly demand demonstrable protection mechanisms. According to the IBM Cost of a Data Breach Report, exposure of sensitive data continues to drive financial and operational impact across industries. Likewise, the official GDPR framework requires organizations to implement appropriate technical safeguards for protecting regulated data.
ScyllaDB provides strong authentication and role separation. Yet native controls alone do not deliver full-featured data masking for production-grade privacy enforcement.
This article explores native masking approaches in ScyllaDB, their limitations, and how DataSunrise deploys Zero-Touch Data Masking with Autonomous Compliance Orchestration to deliver seamless protection across distributed environments.
Importance of Data Masking Tools and Techniques
ScyllaDB delivers performance at scale, but speed does not eliminate compliance risk. When sensitive data appears in queries or dashboards, exposure becomes immediate and measurable — especially when handling personally identifiable information (PII) and other regulated fields.
Data masking tools address this challenge by controlling visibility rather than blocking access. Instead of restricting database usage, they ensure that users see only what they are authorized to view through structured data masking policies.
Masking reduces exposure from both internal and external threats, supports compliance with regulations such as GDPR, HIPAA, PCI DSS, and SOX, and protects non-production environments where production data is often replicated. Techniques such as dynamic data masking secure live query results, while static data masking protects lower environments used for development and testing.
At the same time, centralized enforcement combined with database activity monitoring provides scalable oversight across distributed systems, enabling teams to work safely with realistic datasets without increasing compliance risk.
In distributed architectures, masking is not optional. It is a foundational control that reduces risk without compromising usability.
Native Data Masking Techniques in ScyllaDB
ScyllaDB is compatible with Apache Cassandra Query Language (CQL). While it does not provide built-in masking policies, organizations often implement manual masking logic through schema design, application-layer transformation, or query rewriting.
Application-Level Masking
In many deployments, masking is implemented in backend services before data is displayed to end users. For example:
SELECT user_id,
substring(email, 1, 3) || '***' AS masked_email
FROM customers;
This method ensures that exposed results are partially obfuscated. However, it depends entirely on application logic consistency. If a developer bypasses transformation logic, raw data becomes visible.
This approach does not provide centralized enforcement or policy-level governance.
View-Based Data Exposure Control
Although ScyllaDB lacks traditional SQL views like relational systems, teams simulate controlled exposure using restricted service accounts or materialized views containing pre-processed data.
Example:
CREATE MATERIALIZED VIEW masked_customers AS
SELECT user_id, masked_email
FROM customers
WHERE user_id IS NOT NULL
PRIMARY KEY (user_id);
This technique separates masked and unmasked datasets. However, it duplicates storage and increases operational complexity.
Role-Based Access Controls (RBAC)
ScyllaDB supports role-based access controls to limit table-level access. Example:
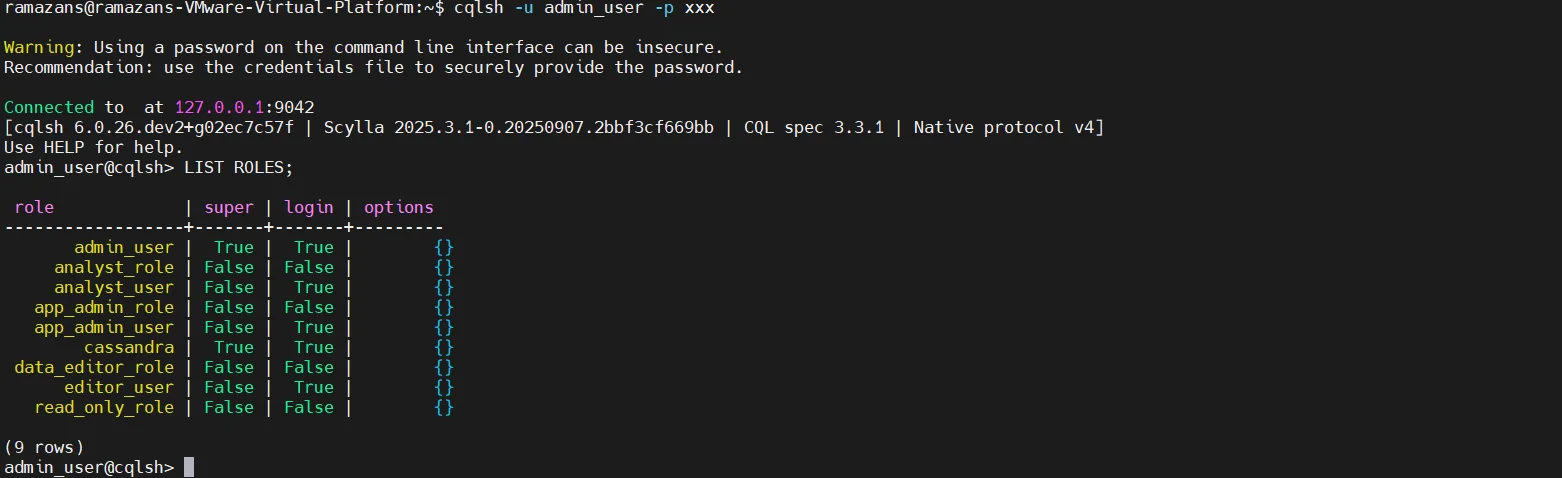
RBAC answers: Can a user access a table?
It does not answer: What portion of the data should they see?
Therefore, RBAC prevents unauthorized access but does not enforce column-level masking or context-aware redaction.
Zero-Touch Data Masking for ScyllaDB with DataSunrise
As discussed in the section Data Masking Tools and Techniques in ScyllaDB, native masking approaches in ScyllaDB typically rely on application-layer logic, RBAC configurations, or duplicated datasets through materialized views. Although these techniques can reduce exposure, they require manual implementation, continuous maintenance, and lack centralized governance.
DataSunrise extends these masking tools and techniques by introducing an external enforcement layer that operates independently of application code and database schema design. Instead of embedding masking logic inside services, it deploys a transparent control layer between users and the ScyllaDB cluster. This enables Zero-Touch Data Masking without modifying queries, schemas, or database nodes.
The platform functions as a Unified Security Framework and supports non-intrusive deployment modes such as Proxy mode, sniffer mode, and native log trailing mode. No changes to ScyllaDB configuration are required.
Centralized Enforcement Instead of Distributed Logic
In native implementations, masking rules are often distributed across multiple applications and microservices, which creates inconsistency and increases operational risk. With DataSunrise, policies are defined once and enforced centrally across all database interactions.
After connecting a ScyllaDB cluster, organizations gain centralized policy management through a unified data security policy framework, cross-cluster visibility, automatic rule generation, and consistent governance across environments. This replaces fragmented application-level masking with a single enforcement layer that integrates seamlessly with database activity monitoring.
Automated Sensitive Data Discovery
Native techniques assume that developers already know which fields contain sensitive data. DataSunrise removes that assumption by introducing automated Data Discovery capabilities.
The system scans datasets and detects payment card numbers, email addresses, phone numbers, and national identifiers, including various forms of personally identifiable information (PII). Discovery supports structured, semi-structured, and unstructured data across hybrid infrastructures. As schemas evolve or new columns appear, sensitive fields are identified automatically, reducing configuration gaps and improving data management practices.
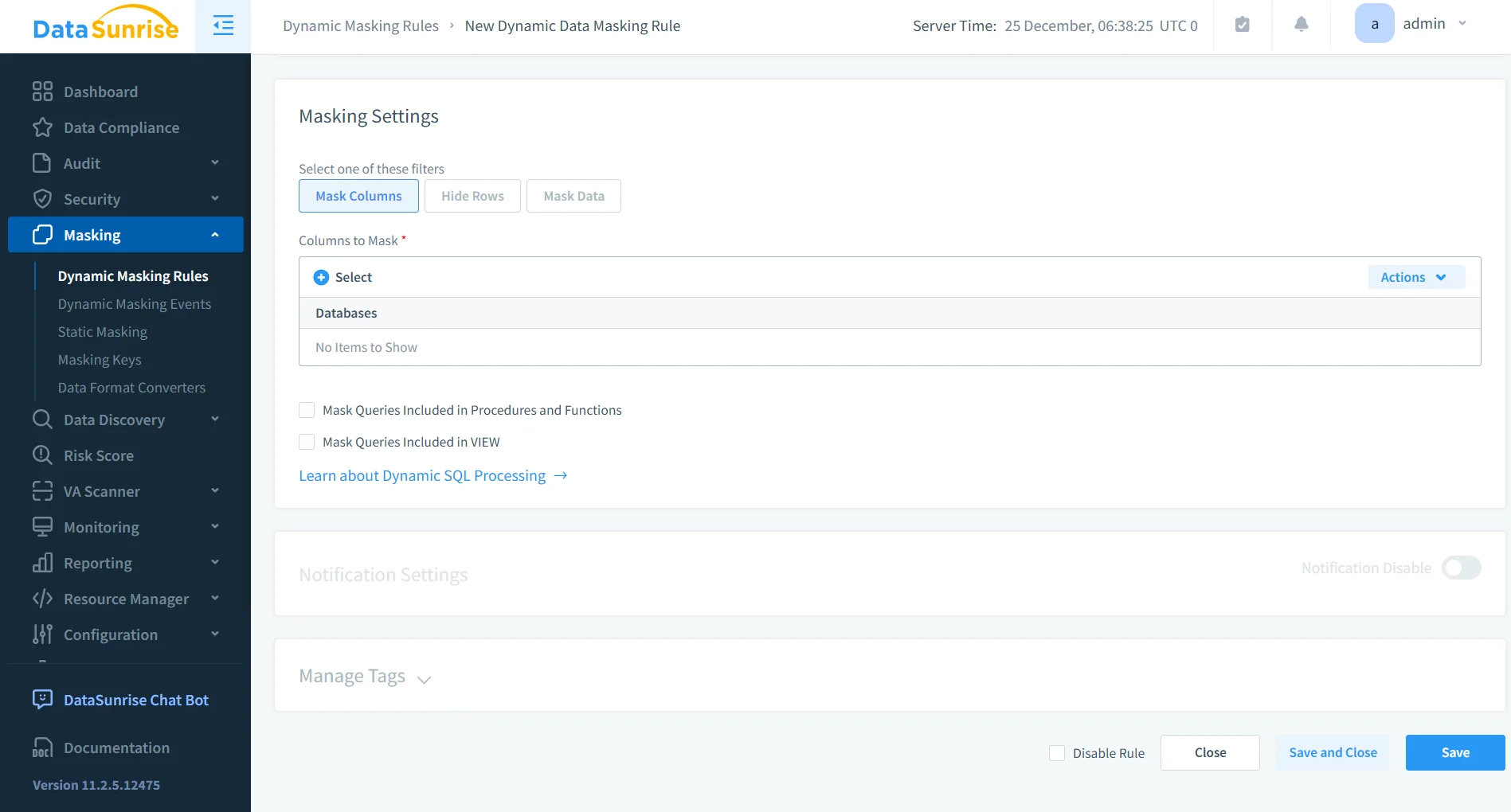
Advanced Masking Techniques
While native approaches depend on manual query transformations, DataSunrise provides a comprehensive masking framework that includes dynamic masking for real-time query response protection, static masking for secure non-production datasets, and in-place masking for controlled data transformation.
Policies can be role-based and context-aware, complementing existing role-based access controls (RBAC). Analysts may see partially masked emails, support teams may receive fully redacted payment data, and administrators may retain full visibility when required. The original data remains unchanged, as masking is applied dynamically to query results at execution time.
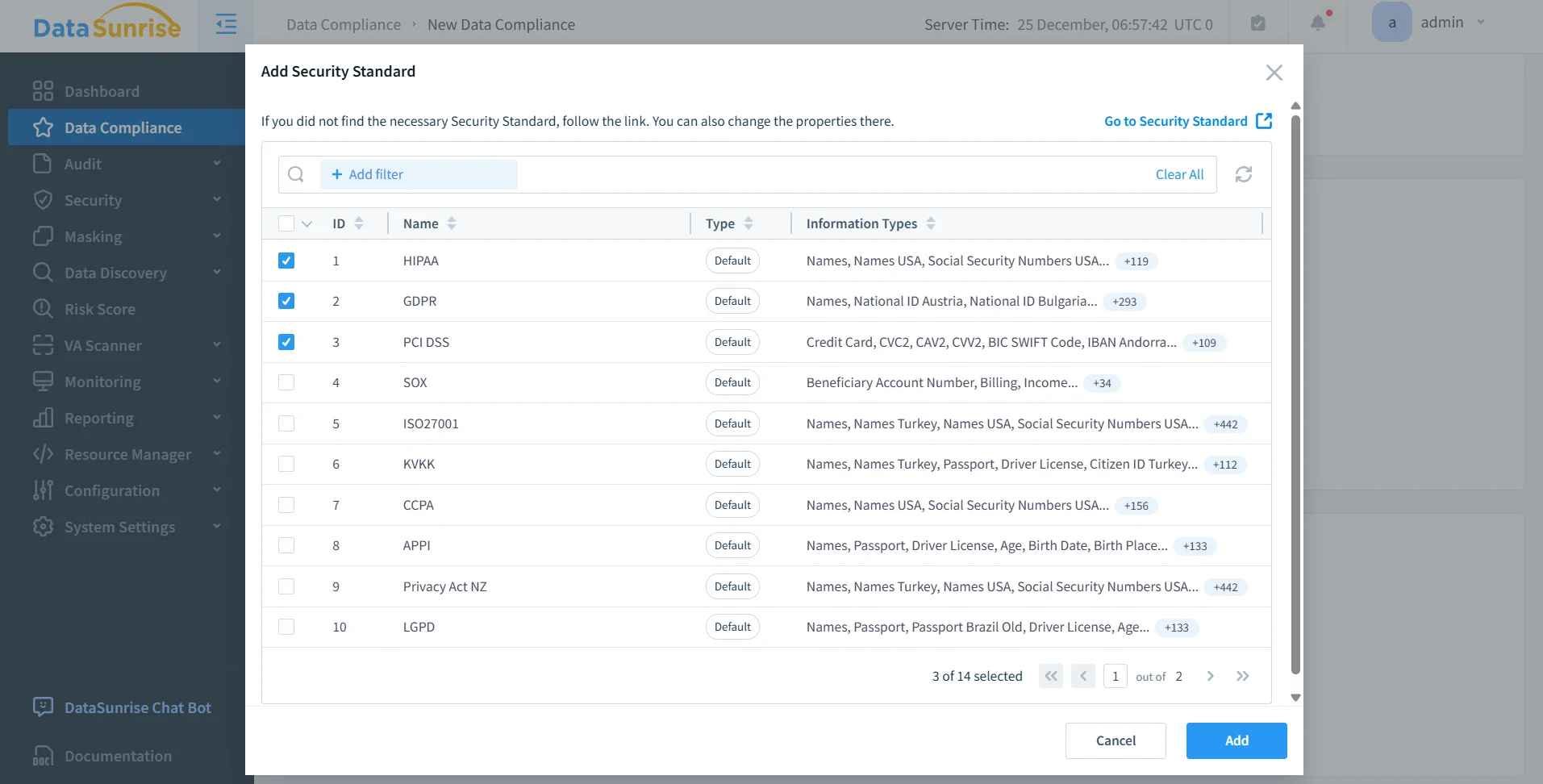
Alignment with Regulatory Requirements
Unlike manual masking logic, DataSunrise directly maps masking policies to regulatory frameworks such as GDPR, HIPAA, PCI DSS, and SOX. Through Compliance Manager, policies are automatically aligned with control requirements.
Continuous Regulatory Calibration prevents compliance drift when new sensitive columns appear, schemas change, or regulatory requirements evolve. Combined with automated report generation, this significantly reduces audit preparation time and manual oversight.
Extending Beyond ScyllaDB
Native masking techniques operate within a single database environment. DataSunrise extends enforcement across SQL and NoSQL systems, data warehouses, data lakes, and cloud storage platforms as part of a centralized data security architecture.
With support for more than 40 data platforms, Zero-Touch Data Masking becomes part of a unified, enterprise-grade protection strategy rather than an isolated database feature. In this way, DataSunrise does not replace native ScyllaDB capabilities; it enhances and operationalizes them at enterprise scale.
Business Impact of Autonomous Data Masking in ScyllaDB
| Business Outcome | Impact Description |
|---|---|
| Quantifiable Risk Reduction | Sensitive data never leaves production in readable form, significantly lowering breach exposure. |
| Streamlined Compliance Workflows | Automatic compliance policy generation simplifies audit preparation and regulatory reporting. |
| Significant Reduction in Manual Effort | Eliminates application rewrites and the need for maintaining duplicate masked datasets. |
| Optimized Total Cost of Compliance | Centralized enforcement reduces operational overhead and ongoing administrative effort. |
| Scalable for Growth | Suitable for startups to Fortune 500 enterprises, supporting expansion with flexible pricing models. |
Conclusion
ScyllaDB delivers high-performance distributed data processing. However, it does not natively provide dynamic, policy-driven masking controls required in regulated environments.
Manual CQL transformations and application-level masking introduce operational risk and inconsistent enforcement, especially when handling sensitive fields such as personally identifiable information (PII).
DataSunrise delivers Zero-Touch Data Masking, Autonomous Compliance Orchestration, and Enterprise-Grade Policy Enforcement for ScyllaDB across on-premise, cloud, and hybrid infrastructures.
By combining Auto-Discover & Mask through Data Discovery, Compliance Autopilot via Compliance Manager, and Continuous Regulatory Calibration, organizations eliminate sensitive data exposure at query time while accelerating time-to-compliance.
Protect Your Data with DataSunrise
Secure your data across every layer with DataSunrise. Detect threats in real time with Activity Monitoring, Data Masking, and Database Firewall. Enforce Data Compliance, discover sensitive data, and protect workloads across 50+ supported cloud, on-prem, and AI system data source integrations.
Start protecting your critical data today
Request a Demo Download Now