Data Obfuscation in PostgreSQL
Data obfuscation in PostgreSQL is a practical strategy for protecting sensitive information while preserving database usability. Modern PostgreSQL deployments often contain Personally Identifiable Information (PII), financial identifiers, HR data, and operational secrets. When this data is exposed to development teams, analytics platforms, contractors, or third-party tools without proper controls, the risk multiplies quickly.
According to the IBM Cost of a Data Breach Report, the average cost of a breach continues to rise globally. Organizations cannot rely on access restrictions alone. Instead, they must implement layered controls including data masking, monitoring, encryption, and governance frameworks.
This guide explains how data obfuscation works in PostgreSQL, how to implement dynamic and static approaches with DataSunrise, and how similar techniques apply to MySQL in Dev/Test environments.
What Is Data Obfuscation in PostgreSQL?
Data obfuscation refers to transforming sensitive values so they cannot be reverse-engineered or misused, while still keeping datasets functional. In PostgreSQL, obfuscation techniques include:
- Redaction (complete masking)
- Partial masking (e.g., last four digits)
- Hashing and tokenization
- Format-preserving substitutions
- Synthetic replacements
These methods are commonly implemented through Dynamic Data Masking and Static Data Masking, depending on whether the transformation happens at runtime or in a cloned dataset.
Obfuscation should preserve structure and constraints whenever possible. Applications must continue to function without modification after masking.
Dynamic Obfuscation for Production PostgreSQL
Dynamic masking transforms data at query time. The original values remain stored in PostgreSQL, but users who match specific rules receive masked output. This is ideal for support teams, analysts, and internal users who need access to records but not raw identifiers.
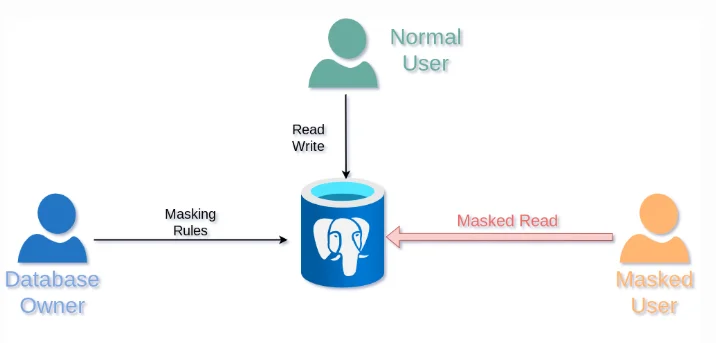
Dynamic obfuscation workflow: masking rules intercept queries and return transformed values to restricted users while preserving full access for authorized roles.
Dynamic obfuscation works best when paired with Role-Based Access Control and the Principle of Least Privilege. It should also be reinforced with Database Activity Monitoring and centralized Audit Logs.
How to Configure Dynamic Obfuscation in DataSunrise
- Create a new masking rule under PostgreSQL.
- Select target schemas and sensitive columns.
- Assign transformation methods (redaction, partial masking, hashing).
- Define rule conditions based on user roles or connection attributes.
- Test with real user contexts.
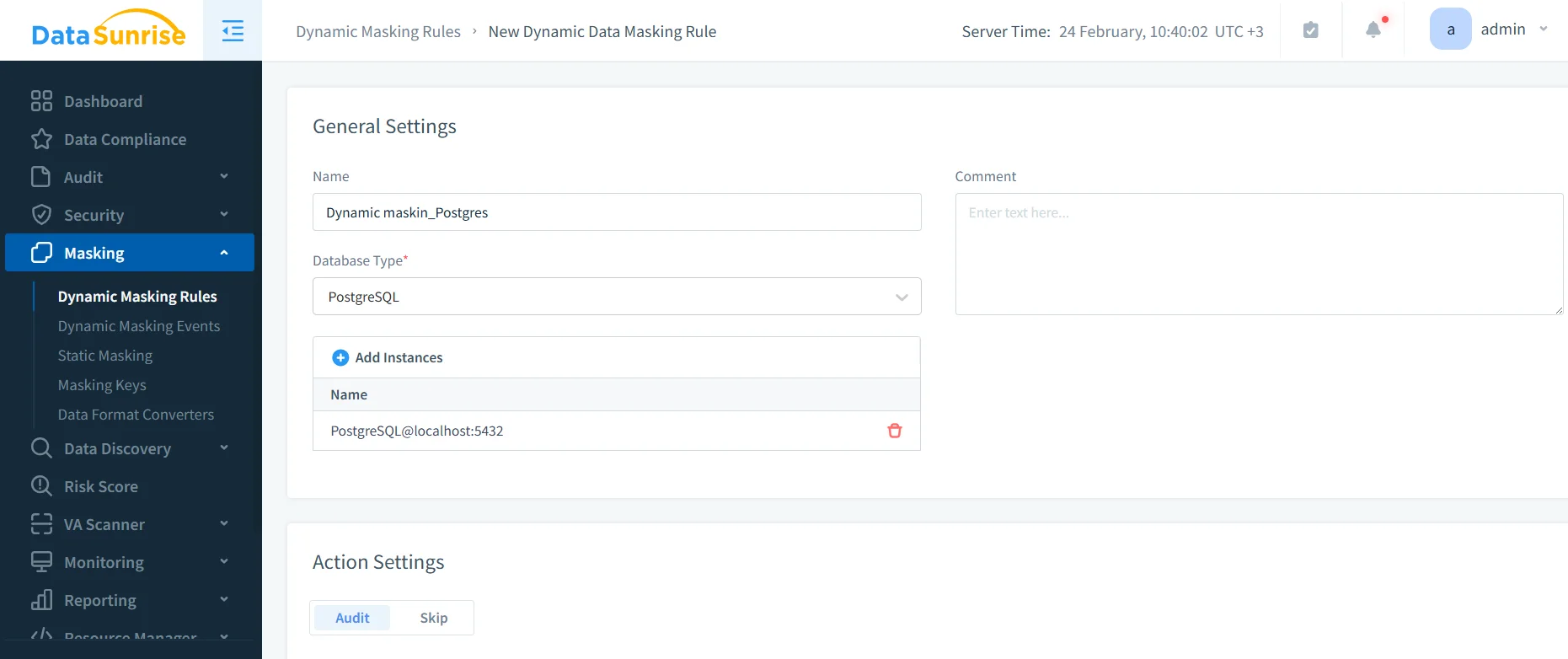
Dynamic masking does not replace access control. If roles are over-permissioned, masking reduces exposure but does not eliminate structural security flaws.
Static Obfuscation for Non-Production Environments
Static masking permanently transforms sensitive data in a copy of the database. This is essential when data is exported to development, QA, analytics, or training environments.
DataSunrise supports structured static masking workflows, including in-place masking when needed. The system also integrates with Data Discovery to ensure all sensitive columns are identified before masking begins.
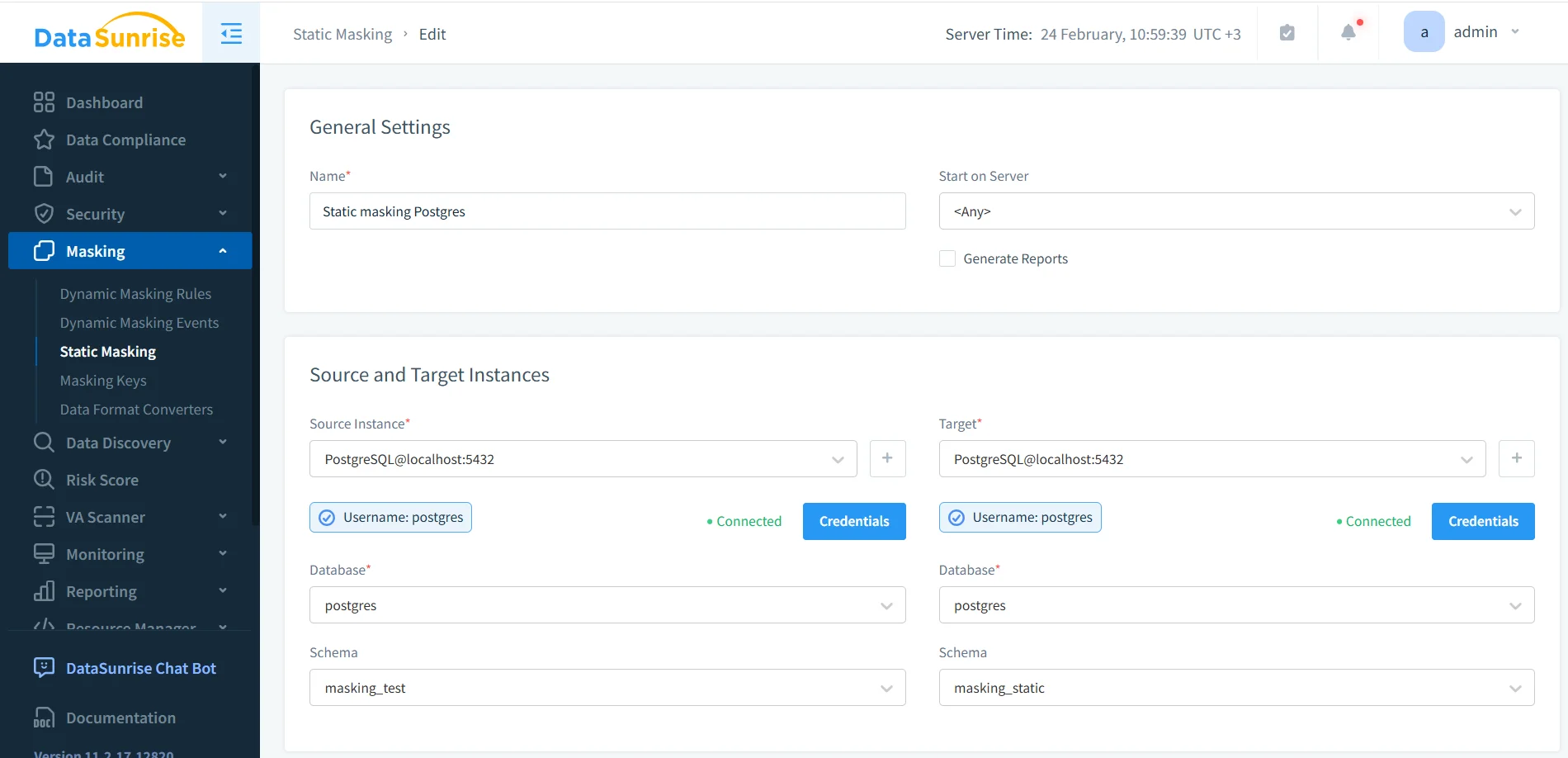
Static obfuscation task configuration with defined source and target PostgreSQL schemas.
When applying static obfuscation, validate output using structured SQL checks:
SELECT * FROM masking_static.employee_sensitive
Always verify referential integrity after static masking. Deterministic masking techniques preserve relationships across foreign keys.
Supporting Controls for PostgreSQL Data Protection
Data obfuscation should be part of a broader security posture including:
- Database Firewall enforcement
- Vulnerability Assessment scanning
- Database Encryption for data at rest
- Security Guide policy baselines
- SQL injection protection rules
For regulatory compliance, DataSunrise supports frameworks such as GDPR, HIPAA, PCI DSS, and SOX, managed centrally via the Compliance Manager.
Static Masking in MySQL: Practical Considerations
Many organizations use MySQL in development or analytics workflows. Static masking in MySQL follows the same principles:
- Sanitize a copy, not production data.
- Preserve foreign key relationships.
- Maintain data types and formatting.
- Validate application compatibility.
Combining static masking with Test Data Management and Data-Driven Testing ensures masked datasets remain realistic and useful.
Manual masking processes inevitably fail under time pressure. Automate masking as part of your environment provisioning pipeline.
Compliance and Governance Alignment
Obfuscation is not only a security control but a compliance enabler. DataSunrise maps masking policies to regulatory standards via data compliance regulations documentation and centralized governance tools. For technical standards reference, consult the official PostgreSQL documentation for baseline security features.
Conclusion
Data obfuscation in PostgreSQL strengthens your overall security posture by limiting sensitive data exposure without compromising operational workflows. When combined with monitoring, encryption, access governance, and static masking for non-production datasets, it forms a comprehensive protection strategy across PostgreSQL and MySQL environments.
Protect Your Data with DataSunrise
Secure your data across every layer with DataSunrise. Detect threats in real time with Activity Monitoring, Data Masking, and Database Firewall. Enforce Data Compliance, discover sensitive data, and protect workloads across 50+ supported cloud, on-prem, and AI system data source integrations.
Start protecting your critical data today
Request a Demo Download Now