Data Obfuscation in ScyllaDB
Data obfuscation in ScyllaDB has become a strategic requirement for organizations running high-performance NoSQL environments that store sensitive customer, financial, and operational data. As ScyllaDB clusters scale horizontally and handle millions of requests per second, the potential exposure surface grows with them. According to the latest findings in the IBM Cost of a Data Breach Report, the financial impact of exposed sensitive data continues to rise year over year, reinforcing the need for proactive protection strategies.
Although ScyllaDB delivers exceptional throughput and low latency, it does not provide native, policy-driven data obfuscation mechanisms to protect sensitive fields in query results or non-production datasets. Once access is granted, full column values are returned unless additional controls are applied. For organizations subject to regulatory requirements such as GDPR and industry frameworks aligned with the NIST Cybersecurity Framework, this creates a visibility gap that cannot be ignored.
As a result, businesses must implement supplementary controls to prevent unauthorized access to personally identifiable information (PII), payment details, and other confidential records. Solutions that combine centralized governance with runtime enforcement — such as Dynamic Data Masking — help close that gap without sacrificing performance.
This article explores what data obfuscation means in the context of ScyllaDB, examines the limitations of native access controls, outlines practical obfuscation approaches, and explains how DataSunrise enables Zero-Touch Data Masking and Compliance Autopilot for ScyllaDB environments.
What Is Data Obfuscation?
Data obfuscation is the process of transforming sensitive data into a protected, non-readable, or partially hidden format while preserving its structure and usability for authorized workflows. Unlike encryption, which fully protects data until it is decrypted, obfuscation allows controlled visibility of masked values without exposing the original content.
In practical terms, data obfuscation modifies how information is presented rather than how it is stored. For example:
- A credit card number may appear as **** **** **** 4582
- An email address may display as j***@company.com
- A full name may be replaced with a consistent pseudonym
The goal is not to eliminate access, but to restrict unnecessary exposure.
In distributed systems such as ScyllaDB, obfuscation plays a critical role because once a user has permission to query a table, the database returns complete column values. Native access controls determine who can access a dataset, but they do not define how much of the data should be visible. This is where techniques such as Dynamic Data Masking and Static Data Masking become essential for enforcing controlled visibility.
This distinction becomes essential in regulated industries. Compliance frameworks such as GDPR, HIPAA, and PCI DSS require organizations to minimize data exposure, enforce the principle of least privilege, and protect personally identifiable information (PII). Obfuscation supports these requirements by aligning with structured Data Security Policies that govern how sensitive data is accessed and displayed.
Effective data obfuscation strategies typically include:
- Dynamic masking at query time
- Static masking for non-production environments
- Role-based conditional masking
- Tokenization or hashing of sensitive fields
When properly implemented as part of a broader Data Masking strategy, obfuscation reduces breach impact, limits insider risk, and supports continuous compliance without disrupting operational performance.
Native Security Capabilities in ScyllaDB
ScyllaDB includes several built-in security mechanisms designed to control access and protect data at the infrastructure level. These features include Role-Based Access Control (RBAC), authentication and authorization controls, TLS encryption for secure communication, and audit logging in the Enterprise edition.
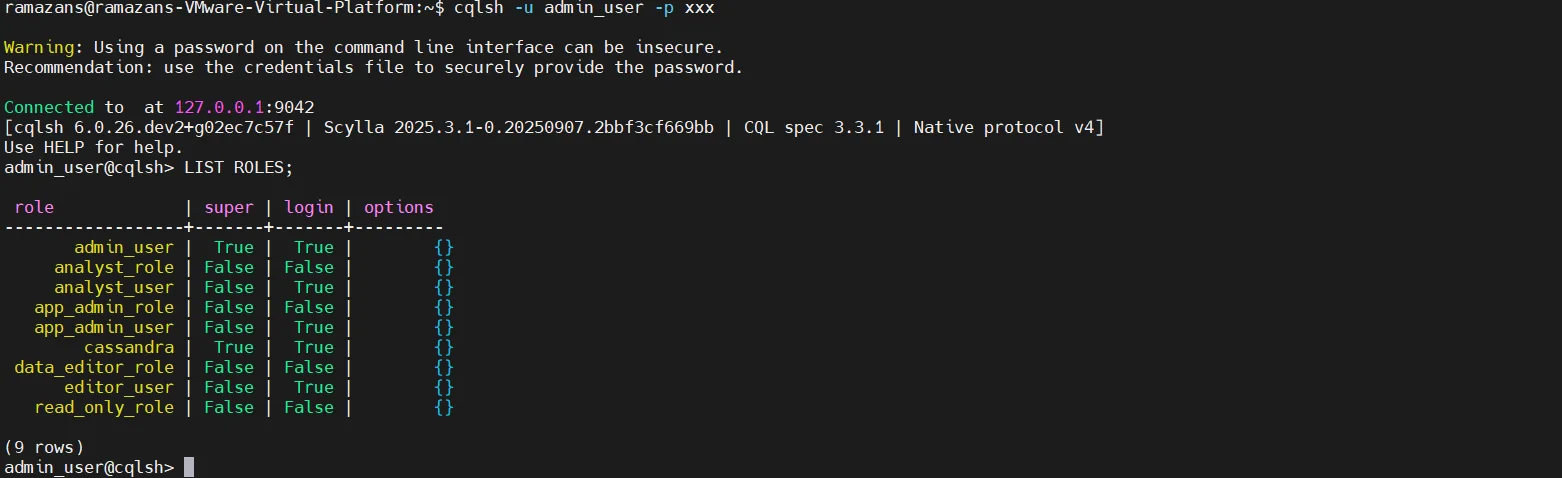
RBAC allows administrators to grant permissions at the keyspace or table level. For example:
GRANT SELECT ON keyspace.customers TO analyst_role;
This configuration determines who can access specific database objects. However, RBAC operates strictly at the object level. It does not support column-level masking or contextual transformations based on user role or query context.
For instance, if a user executes:
SELECT credit_card_number FROM customers;
and has the required permission, the database returns the full value of the column.
ScyllaDB does not natively provide dynamic data masking, field-level obfuscation policies, conditional masking based on user roles, or automated discovery of sensitive columns. Once access is granted, visibility is complete.
Because of these limitations, organizations often resort to application-layer obfuscation or manual query rewrites. While these approaches may appear workable at first, they are typically fragile, inconsistent, and difficult to maintain in large-scale environments.
Manual Obfuscation Approaches in ScyllaDB
In the absence of native masking controls, teams often implement workaround solutions. These methods introduce operational overhead, increase technical debt, and create governance challenges over time.
1. Application-Level Masking
In this approach, the application intercepts query results and modifies sensitive fields before presenting them to users. Masking logic is embedded directly into application code.
For example, an application may retrieve full values from ScyllaDB:
SELECT id, full_name, credit_card_number
FROM customers
WHERE id = 101;
Then mask the result inside application logic:
def mask_credit_card(cc):
return "**** **** **** " + cc[-4:]
result["credit_card_number"] = mask_credit_card(result["credit_card_number"])
Although this method provides basic control, it comes with significant limitations. It requires ongoing code modifications, increases development complexity, and leads to inconsistent enforcement across services. Every microservice must implement identical masking logic, which is rarely maintained uniformly.
Additionally, this model lacks centralized governance and makes auditing difficult, since masking rules are distributed across multiple application layers rather than enforced at the data access layer.
2. Data Duplication for Test Environments
Another common method involves exporting production data, transforming sensitive fields, and loading the modified dataset into staging or development environments.
Example export from production:
cqlsh -e "COPY keyspace.customers TO 'customers.csv';"
Transformation script:
import csv
with open("customers.csv") as infile, open("customers_masked.csv", "w") as outfile:
reader = csv.DictReader(infile)
writer = csv.DictWriter(outfile, fieldnames=reader.fieldnames)
writer.writeheader()
for row in reader:
row["credit_card_number"] = "****MASKED****"
writer.writerow(row)
Reload into staging:
cqlsh -e "COPY keyspace.customers FROM 'customers_masked.csv';"
While this enables safer non-production testing, it introduces operational complexity. Scripts must be maintained, transformation logic must be updated continuously, and there is always a risk of exporting unmasked data.
Moreover, this approach does not provide continuous regulatory calibration or centralized policy enforcement. Each export cycle becomes a potential compliance event.
3. Static Transformation via ETL
Some organizations implement obfuscation during ETL processing. Sensitive columns are transformed as part of the pipeline before being loaded into downstream systems.
For example, within a Spark job:
from pyspark.sql.functions import sha2
df = spark.read.format("org.apache.spark.sql.cassandra") \
.options(table="customers", keyspace="keyspace") \
.load()
df_masked = df.withColumn(
"credit_card_number",
sha2(df["credit_card_number"], 256)
)
df_masked.write.format("org.apache.spark.sql.cassandra") \
.options(table="customers_analytics", keyspace="keyspace") \
.mode("overwrite") \
.save()
Although this supports analytics or reporting environments, it does not protect live query responses in production systems. Users querying the primary cluster still receive full, unmasked values if access permissions allow it.
Data Obfuscation in ScyllaDB with DataSunrise
ScyllaDB delivers exceptional performance for distributed NoSQL workloads. However, performance alone does not address the challenge of controlled data visibility. DataSunrise extends ScyllaDB with Autonomous Compliance Orchestration and Zero-Touch Data Masking, enabling policy-driven obfuscation without modifying schemas or application logic.
Unlike application-based masking approaches, DataSunrise operates as a non-intrusive security layer. It supports proxy mode, native log trailing mode, and flexible deployment across on-premise, cloud, and hybrid infrastructures. This architecture ensures seamless integration while preserving ScyllaDB performance characteristics.
Below is how DataSunrise enables structured, centralized, and automated data obfuscation in ScyllaDB environments.
Non-Intrusive Integration with ScyllaDB
DataSunrise integrates using a Reverse Proxy architecture, allowing enforcement without altering database schemas or rewriting queries.
To connect a ScyllaDB instance, administrators configure the host, port, credentials, and deployment mode. Once connected, DataSunrise begins monitoring and policy enforcement in real time. This approach eliminates application rewrites and avoids intrusive database changes while enabling centralized governance and consistent enforcement.
Automated Sensitive Data Discovery
Effective obfuscation begins with visibility. DataSunrise performs automated discovery across structured and semi-structured datasets stored in ScyllaDB.
The discovery engine identifies personally identifiable information (PII), payment card data, healthcare identifiers, and custom business-sensitive attributes. Instead of manually locating sensitive columns, administrators receive structured insight into data exposure across the entire cluster.
Discovery results feed directly into Automatic Policy Generation. This allows organizations to implement compliance-aligned controls from the start rather than relying on reactive adjustments.
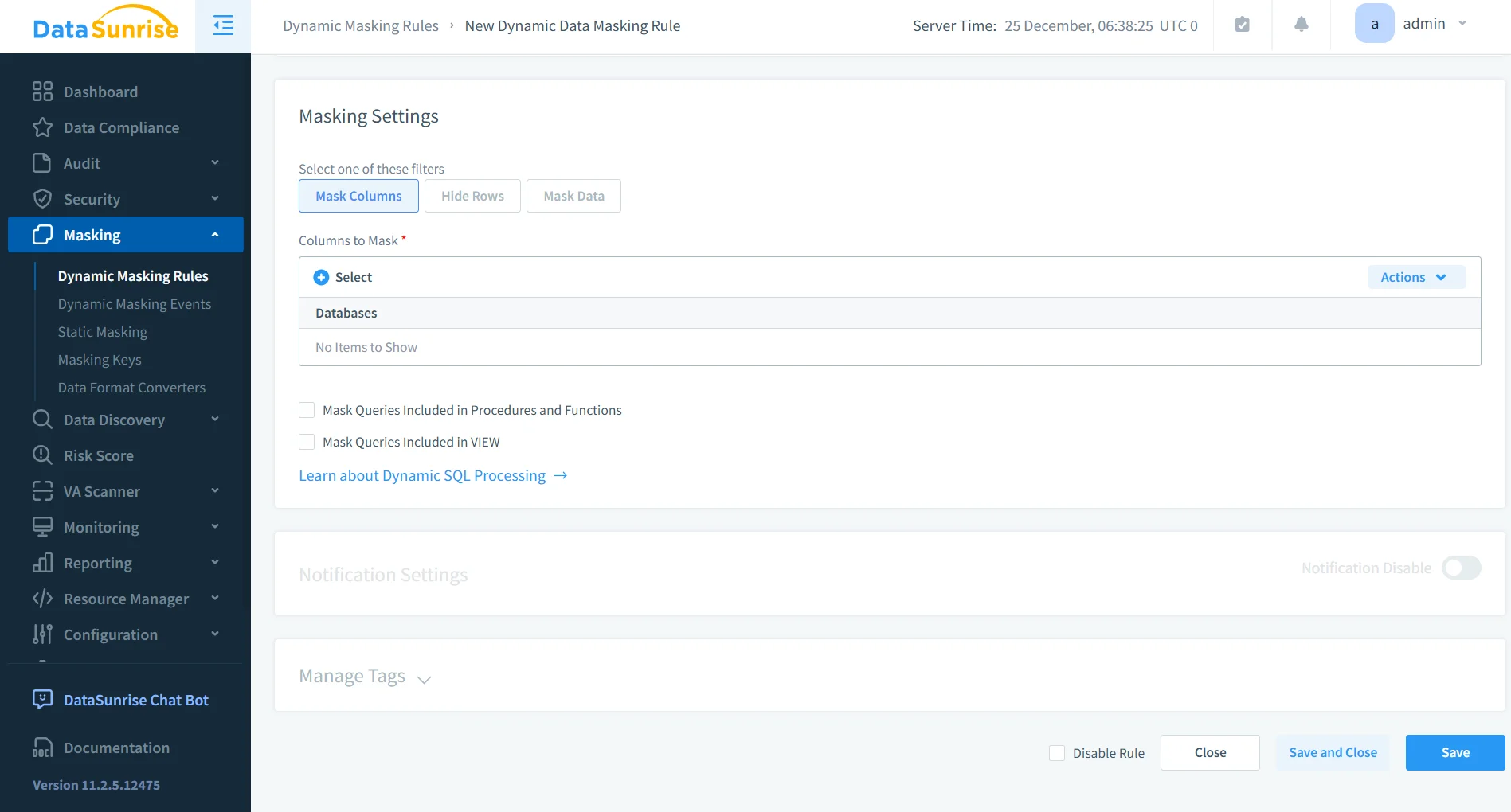
Granular Obfuscation Policy Configuration
Using the Data Masking engine, administrators define fine-grained obfuscation rules tailored to organizational requirements.
Supported masking techniques include full masking, partial masking, hashing, tokenization, and role-based conditional masking. For example, developers may see fully masked sensitive columns, support teams may view only the last four digits of payment data, while administrators retain full access.
This model enables Surgical Precision Masking, where visibility is dynamically determined by user role, query context, and compliance requirements. Policies are centrally managed and consistently enforced across all ScyllaDB nodes, eliminating policy drift.
Real-Time Context-Aware Enforcement
DataSunrise applies Context-Aware Protection at query time. When a user executes a query such as selecting credit card data from a customer table, the response is dynamically transformed according to the user’s role, the defined masking policy, and the applicable compliance framework.
No application changes are required. Masking occurs transparently at the data access layer. This enables Zero-Trust Data Access, Enterprise-Grade Policy Enforcement, and integration with ML Audit Rules for behavioral correlation.
Sensitive data remains protected even during legitimate access, ensuring operational continuity without compromising compliance.
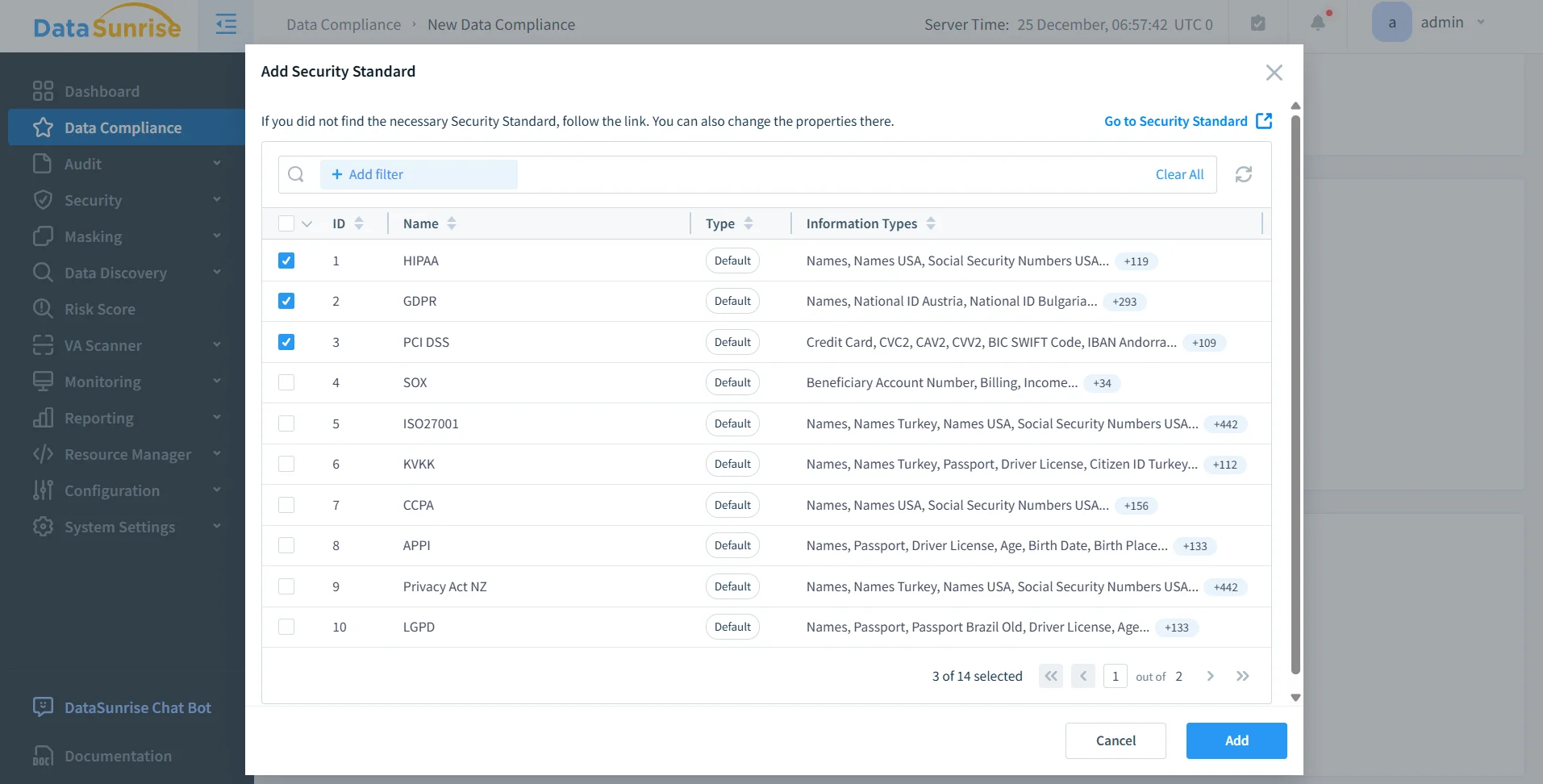
Compliance Autopilot for ScyllaDB
DataSunrise integrates Compliance Autopilot aligned with major regulatory frameworks, including GDPR, HIPAA, PCI DSS, and SOX.
It delivers Automatic Compliance Policy Generation, Continuous Regulatory Calibration, Audit-Ready Reporting, and Real-Time Regulatory Alignment. Unlike solutions that require constant manual tuning, DataSunrise provides autonomous protection supported by centralized governance. Compliance controls evolve alongside regulatory requirements and data growth.
Unified Security Framework Across Platforms
DataSunrise supports ScyllaDB alongside more than 40 other data storage platforms within a Unified Security Framework.
Capabilities extend beyond obfuscation to include Database Activity Monitoring, advanced Security Rules, Behavior Analytics, and Database Firewall protection. This ensures Seamless Multi-Environment Coverage across SQL databases, NoSQL systems, data lakes, and cloud storage platforms.
Deployment flexibility spans on-premise environments as well as AWS, Azure, and GCP, without introducing configuration complexity.
By combining centralized governance, automated policy enforcement, and cross-platform coverage, DataSunrise transforms data obfuscation in ScyllaDB into a scalable, compliance-driven security strategy.
Business Impact of Data Obfuscation in ScyllaDB
| Outcome | Business Impact |
|---|---|
| Quantifiable Risk Reduction | Sensitive values are never exposed to unauthorized roles, reducing breach impact and insider risk. |
| Streamlined Compliance Workflows | Compliance Autopilot eliminates manual policy tracking and simplifies regulatory alignment. |
| Significant Reduction in Manual Effort | No script maintenance, no application rewrites, and no distributed masking logic across services. |
| Optimized Total Cost of Compliance | Centralized governance lowers operational overhead and reduces audit preparation time. |
| Scalable for Growth | Designed for startups to Fortune 500 enterprises with flexible pricing policies and scalable deployment models. |
Conclusion
ScyllaDB delivers unmatched performance for distributed workloads. However, it does not natively provide the dynamic, policy-driven data obfuscation capabilities required in regulated industries.
Manual transformations and application-level masking introduce operational risk, inconsistent enforcement, and compliance gaps that become harder to manage as clusters scale.
DataSunrise addresses these limitations by delivering Dynamic Data Masking, Autonomous Compliance Orchestration, Continuous Regulatory Calibration, and Enterprise-Grade Policy Enforcement. Instead of relying on scripts or scattered application logic, organizations gain centralized governance and real-time enforcement at the data access layer supported by a comprehensive Compliance Manager.
By combining Auto-Discover & Mask with a Centralized Data Compliance Platform and advanced Database Activity Monitoring, businesses eliminate sensitive data exposure at query time while accelerating time-to-compliance.
To learn how DataSunrise enhances ScyllaDB with intelligent obfuscation and compliance automation, explore the DataSunrise Overview or schedule a live demo.
Protect Your Data with DataSunrise
Secure your data across every layer with DataSunrise. Detect threats in real time with Activity Monitoring, Data Masking, and Database Firewall. Enforce Data Compliance, discover sensitive data, and protect workloads across 50+ supported cloud, on-prem, and AI system data source integrations.
Start protecting your critical data today
Request a Demo Download Now