How to Apply Dynamic Masking in Sybase
Applying dynamic masking in Sybase requires addressing limitations in native access control mechanisms.
Sybase ASE provides authentication, role-based access control, and permission management. These features define who can access database objects. However, they do not control data visibility at query execution time. Once access is granted, users typically retrieve full, unmasked values. This architectural limitation is also reflected in general database security models described in the official SAP ASE documentation: https://help.sap.com/docs/SAP_ASE
Dynamic masking addresses this limitation by modifying query results in real time without altering stored data. The same query executed against the same dataset can return different representations of sensitive fields based on user roles, policies, or contextual conditions. From a security and compliance perspective, this aligns with broader data protection principles outlined by NIST: https://csrc.nist.gov/publications/detail/sp/800-53/rev-5/final
This article examines how dynamic masking is implemented in Sybase using native techniques, outlines their limitations, and presents a scalable, policy-driven approach to enforcing data visibility controls. For additional context on masking strategies and implementation approaches, see Data Masking, Dynamic masking, and Data Security.
What Is Dynamic Masking?
Dynamic masking is a data protection technique that modifies sensitive values at query execution time without changing the underlying data stored in the database.
Unlike encryption or static masking, dynamic masking does not alter the original dataset. Instead, it applies transformation rules to query results before they are returned to the user. As a result, different users querying the same table can receive different representations of the same data depending on predefined policies. For a broader overview of masking approaches, see Data Masking and Masking types.
With dynamic masking, data remains unchanged at rest while masking is applied in real time during query execution. The output is context-aware and depends on user roles or other conditions, which eliminates the need for additional data copies or transformation pipelines. More details on runtime masking can be found in Dynamic masking.
For example, when executing a query such as:
SELECT name, credit_card FROM customers;
a privileged user may see full values:
John Doe | 4111-1111-1111-1111
while a restricted user receives masked data:
John Doe | XXXX-XXXX-XXXX-1111
In this model, access to the dataset is preserved, while exposure of sensitive fields is controlled. This approach enables organizations to maintain operational workflows while enforcing data protection and compliance requirements, particularly when handling Personal Information.
Native Approaches to Dynamic Masking in Sybase
Sybase ASE does not provide a built-in dynamic masking framework. Instead, masking is typically implemented using indirect methods that rely on SQL constructs and access control discipline.
1. Masking via Views
One common approach is to create views that return masked data instead of exposing the original tables. For example, a view can replace sensitive values such as credit card numbers with partially masked strings, while preserving the original data in the base table.
CREATE VIEW masked_customers AS
SELECT
name,
'XXXX-XXXX-XXXX-' + RIGHT(credit_card, 4) AS credit_card
FROM customers;
Access is then granted to the view rather than the underlying table.
This approach has several limitations. Direct access to base tables must be strictly restricted, otherwise users can bypass the masking logic. In addition, environments with multiple roles often require separate views for each use case, which increases complexity. Over time, managing and updating these views creates significant administrative overhead.
2. CASE-Based Masking Logic
Another method involves embedding masking logic directly into SQL queries using conditional expressions. This allows the system to return different results depending on the current user.
SELECT
name,
CASE
WHEN user_name() = 'admin' THEN credit_card
ELSE 'XXXX-XXXX-XXXX-' + RIGHT(credit_card, 4)
END AS credit_card
FROM customers;
In this model, masking is applied dynamically within the query itself.
However, this approach introduces several challenges. The masking logic must be repeated across multiple queries and application layers, making it difficult to maintain consistency. It also complicates auditing and governance, since the logic is distributed rather than centralized. Additionally, embedding security logic into queries breaks the separation between application and data layers.
3. Stored Procedures as Access Layer
A more controlled approach is to encapsulate data access within stored procedures. Users are expected to retrieve data only through predefined procedures that include masking logic.
CREATE PROCEDURE get_customer_data
AS
SELECT
name,
'XXXX-XXXX-XXXX-' + RIGHT(credit_card, 4)
FROM customers;
This method attempts to enforce masking by restricting how queries are executed.
Despite this, it still depends heavily on strict access control. If users gain direct access to tables, they can bypass the stored procedures entirely. It also increases reliance on controlled query paths, which can limit flexibility and create friction in development workflows.
Dynamic Masking in Sybase with DataSunrise
DataSunrise implements dynamic masking as an external control layer that intercepts database queries and applies masking policies before results are returned to the user. This approach eliminates the need for schema changes, avoids modifications to application logic, and ensures consistent enforcement across all access paths. Masking is applied at the query result level, which guarantees that sensitive data is never exposed in raw form, regardless of how the query is executed or which client tool is used.
Seamless Integration with Sybase
DataSunrise integrates with Sybase using proxy, sniffer, or log-based deployment modes, allowing organizations to introduce dynamic masking without modifying database schemas or application logic. This non-intrusive approach ensures that existing systems continue to operate as expected while masking policies are enforced transparently. It also supports deployment across on-premises, cloud, and hybrid infrastructures, making it suitable for environments with diverse architectural requirements.
- Non-intrusive deployment without schema or code changes
- Support for proxy, sniffer, and log-based integration modes
- Compatible with on-premises, cloud, and hybrid environments
- Transparent query interception without impacting applications
- Rapid deployment with minimal infrastructure adjustments
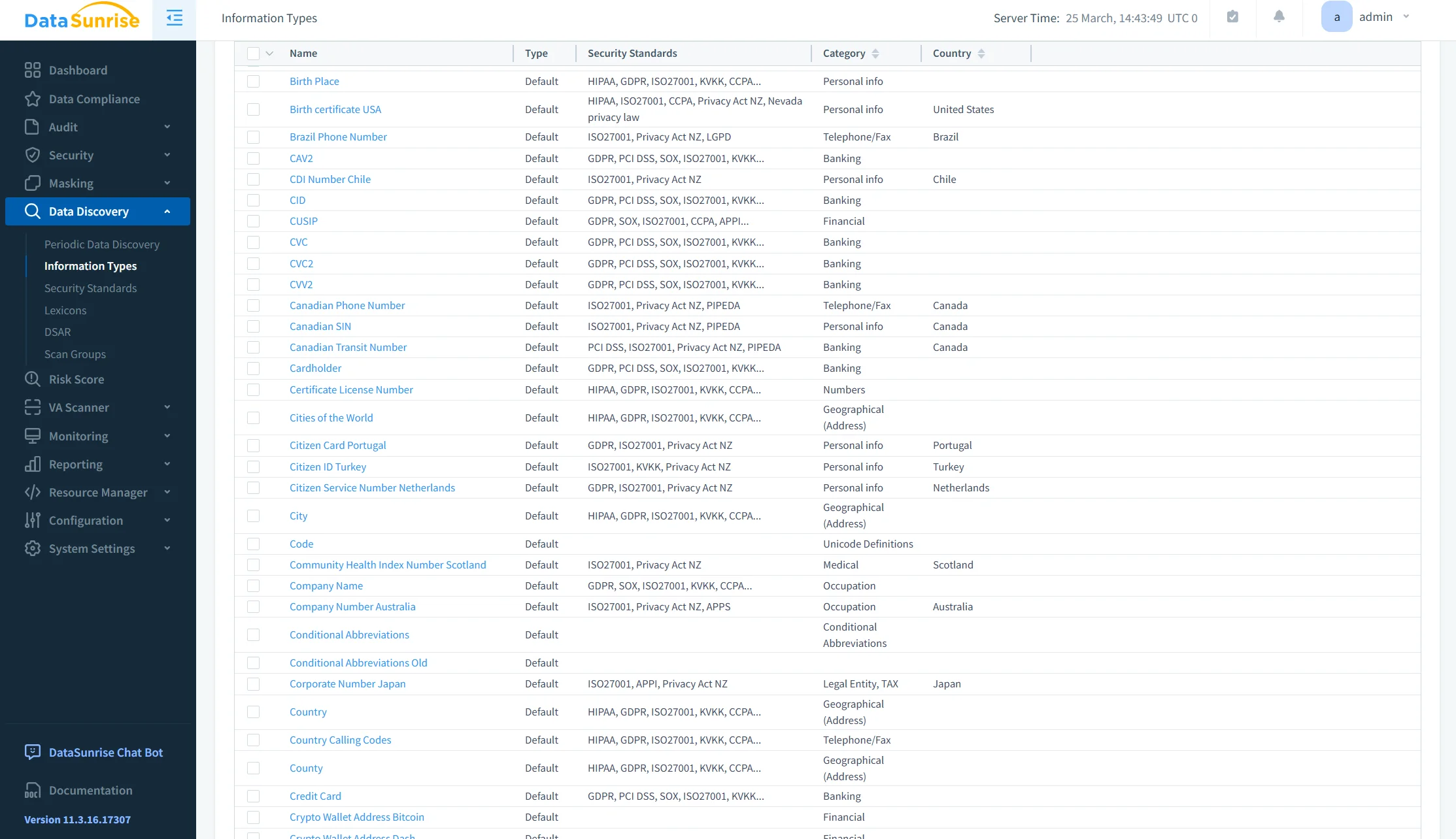
Automated Sensitive Data Discovery
The platform includes built-in discovery mechanisms that scan database structures to identify sensitive data such as personally identifiable information (PII), financial records, authentication data, and other regulated fields. Classification is applied automatically based on predefined patterns and detection rules, which reduces reliance on manual configuration. Continuous discovery processes ensure that newly added or modified data is evaluated and incorporated into masking policies, maintaining consistent protection over time.
- Automated identification of PII, financial, and regulated data
- Pattern-based and rule-based classification mechanisms
- Continuous scanning for newly added or modified data
- Reduced reliance on manual data mapping
- Improved accuracy in policy targeting and enforcement
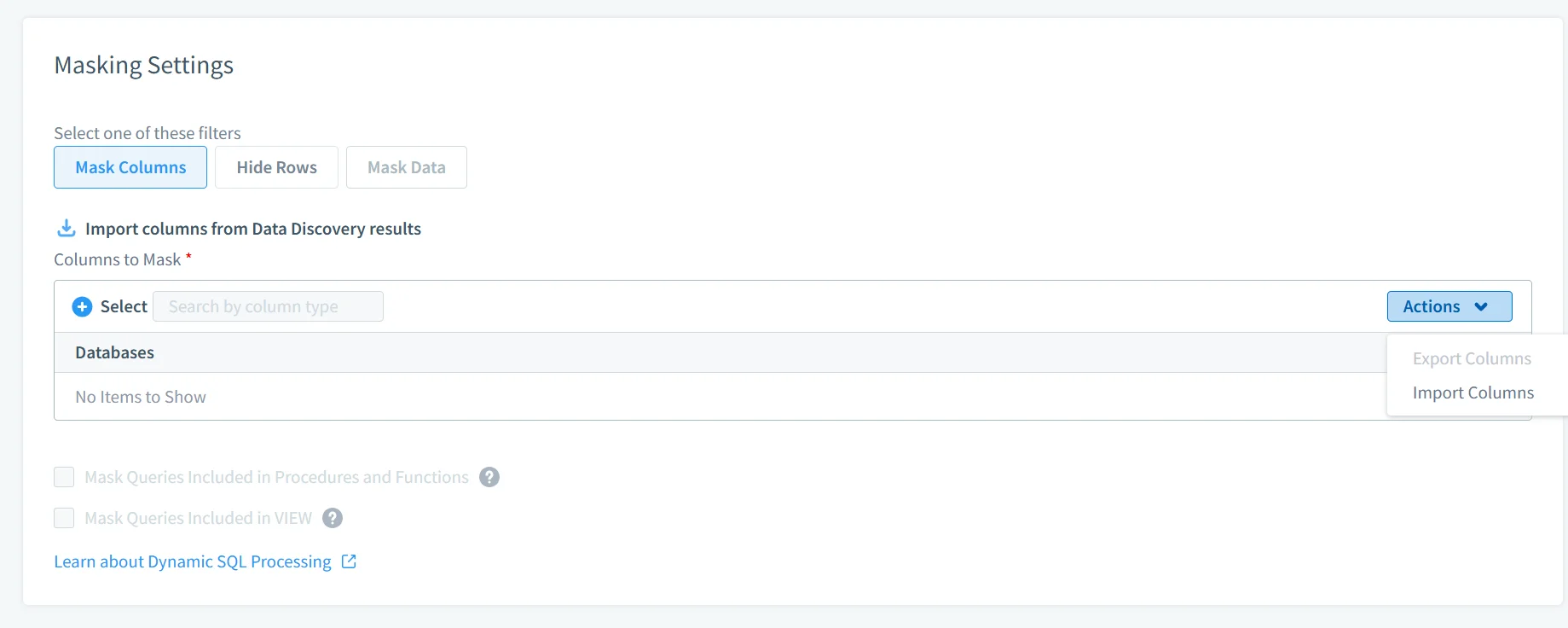
Centralized Dynamic Masking Policies
Masking policies are defined and managed centrally, enabling consistent enforcement across all database queries and access points. Administrators can configure rules at various levels, including schema, table, and column, and associate them with specific user roles or access conditions. This eliminates the need to embed masking logic into SQL queries or application code, reducing complexity and ensuring that all users receive data according to the same policy framework.
- Centralized management of masking rules and policies
- Policy definition at schema, table, and column levels
- Role-based and context-driven access control
- Elimination of SQL-level masking logic duplication
- Consistent enforcement across all database clients
Flexible Masking Methods
DataSunrise supports multiple masking techniques that can be selected based on data sensitivity and business requirements. These include full masking for complete data obfuscation, partial masking to preserve limited visibility (such as last four digits), hashing for irreversible transformations, tokenization for referential integrity, and format-preserving masking for structured datasets. This flexibility allows organizations to maintain usability for analytics and operational processes while ensuring sensitive data remains protected.
- Full masking for complete data concealment
- Partial masking for controlled data exposure
- Hashing for irreversible anonymization
- Tokenization to preserve referential integrity
- Format-preserving masking for structured datasets
Context-Aware Policy Enforcement
Masking decisions are not static but are evaluated dynamically using contextual attributes. These include user identity, role, IP address, application source, query type, and time-based conditions. This enables fine-grained control over data visibility, allowing organizations to apply stricter policies for external access, limit exposure in non-production environments, or adjust masking behavior based on operational context without changing underlying configurations.
- Dynamic evaluation based on user identity and role
- Policy enforcement using IP and source context
- Query-type and operation-aware masking decisions
- Time-based access control for sensitive data
- Fine-grained control without changing configurations
Comprehensive Monitoring and Audit Trails
All database interactions are logged, including both masked and unmasked query results. This provides detailed visibility into user activity, including which data was accessed, how it was transformed, and when the interaction occurred. These audit trails support security monitoring, incident investigation, and compliance reporting by providing a complete and verifiable record of data access and masking enforcement.
- Full logging of masked and unmasked query activity
- Detailed tracking of user actions and data access
- Visibility into applied masking transformations
- Support for forensic analysis and investigations
- Audit-ready reporting for compliance requirements
Consistent Cross-Platform Enforcement
DataSunrise applies masking policies uniformly across multiple database platforms, ensuring consistent data protection in environments that use different database technologies. This reduces the need to maintain separate masking implementations for each system and helps standardize security practices across the organization, particularly in large-scale or distributed infrastructures.
- Unified masking policies across multiple databases
- Consistent enforcement in heterogeneous environments
- Reduced duplication of security configurations
- Standardized data protection across systems
- Scalable approach for distributed infrastructures
Reduced Operational Complexity
By externalizing masking logic from both the database and application layers, DataSunrise reduces the operational burden associated with maintaining masking implementations. Security teams can manage all policies from a centralized interface, eliminating the need to maintain multiple views, stored procedures, or embedded query logic. This simplification improves maintainability and reduces the likelihood of configuration errors.
- Centralized policy management interface
- Elimination of SQL-based masking maintenance
- Reduced dependency on views and stored procedures
- Lower risk of configuration errors
- Simplified administration across environments
Improved Compliance Alignment
Centralized masking and auditing capabilities support alignment with regulatory frameworks such as GDPR, HIPAA, and PCI DSS. Automated enforcement ensures that sensitive data is consistently protected, while detailed audit logs provide the evidence required for compliance assessments. This reduces the effort needed to prepare for audits and helps organizations maintain a continuous compliance posture.
- Support for GDPR, HIPAA, and PCI DSS requirements
- Automated enforcement of compliance policies
- Detailed audit logs for regulatory reporting
- Reduced audit preparation effort
- Continuous compliance posture maintenance
Business Impact of Dynamic Masking in Sybase
| Impact | Description |
|---|---|
| Reduced Exposure | Sensitive data never appears in raw form, ensuring continuous Data Security across all query results |
| Faster Compliance | GDPR, HIPAA, and PCI DSS policies are enforced automatically with support from Compliance Manager |
| Lower Maintenance | A single centralized policy replaces dozens of SQL constructs typically used in Dynamic masking implementations |
| Safer Operations | Teams can safely interact with production systems without exposing Personal Information |
| Audit Readiness | Full visibility into masked and unmasked access is maintained through Database Activity Monitoring |
Conclusion
Sybase provides strong mechanisms for access control but does not address data visibility at query runtime. This limitation becomes critical when handling sensitive data that requires controlled exposure rather than simple access restriction.
Native masking techniques—views, conditional logic, and stored procedures—introduce complexity and do not scale effectively in production environments. They rely on consistent implementation and strict discipline, which is difficult to maintain over time, especially in distributed systems.
Dynamic masking should be implemented as a centralized, policy-driven control applied at the query layer. This approach ensures consistent enforcement, reduces operational overhead, and improves compliance posture. It also aligns with modern Data Security practices and supports principles such as Role-Based Access Controls.
DataSunrise enables this model by externalizing masking logic, applying real-time policies, and providing full auditability of data access without requiring changes to existing systems. Its capabilities in Dynamic masking, Data Audit, and Database Activity Monitoring ensure that sensitive data remains protected while maintaining operational efficiency.
Protect Your Data with DataSunrise
Secure your data across every layer with DataSunrise. Detect threats in real time with Activity Monitoring, Data Masking, and Database Firewall. Enforce Data Compliance, discover sensitive data, and protect workloads across 50+ supported cloud, on-prem, and AI system data source integrations.
Start protecting your critical data today
Request a Demo Download Now
