Data Masking Tools and Techniques for Sybase
Protecting sensitive data in Sybase (SAP ASE) is not about access anymore—it’s about exposure control.
Sybase provides authentication, encryption, and role-based access control. However, once a query is executed, those controls stop being useful. If a user can query a table, they typically see the full dataset. That’s the gap masking is supposed to fix. For a broader industry perspective, see the NIST data protection guidelines and IBM’s data security overview.
Data masking tools and techniques for Sybase address this problem by controlling how data is presented, copied, or shared. This article breaks down native masking approaches, their limitations, and how centralized platforms improve consistency, scalability, and compliance, including approaches like dynamic data masking and modern data protection strategies.
Importance of Data Masking Tools and Techniques
Data masking in Sybase functions as a control mechanism that limits data exposure beyond standard access control models.
Native security features—authentication, encryption, and role-based access control—govern access to database objects. However, they do not regulate the level of detail returned in query results. As a result, authorized users often receive full, unfiltered datasets. Data masking addresses this limitation by enforcing visibility constraints at query runtime or during data provisioning workflows.
This limitation becomes apparent in multi-role environments where different user groups interact with the same data structures. Developers, analysts, and support teams operate under different requirements, yet Sybase does not natively differentiate data visibility at the field level. Masking introduces controlled exposure by applying role-based transformations without requiring schema changes or application rewrites.
The same issue extends to non-production environments. Production datasets are frequently replicated for testing and development, which leads to uncontrolled distribution of sensitive data. Without masking, these environments become weak points in the security model. Techniques such as static data masking ensure that replicated datasets retain structural integrity while removing or transforming sensitive values.
From a compliance standpoint, frameworks such as GDPR, HIPAA, and PCI DSS require strict data minimization and controlled exposure. Masking enforces these requirements by limiting visibility at the data level, even when database permissions allow access. This ensures that sensitive information is not unnecessarily exposed during normal operations.
Operationally, native masking approaches—views, stored procedures, and transformation scripts—introduce fragmentation. Each implementation must be maintained independently, which increases the risk of inconsistencies and configuration errors. Centralized masking tools eliminate this overhead by applying uniform policies across environments and integrating with monitoring systems such as database activity monitoring.
In practice, access control determines whether a query can be executed, while masking governs the content of the result set. Without a masking layer, sensitive data remains fully exposed within the boundaries of authorized access.
Native Data Masking Techniques in Sybase
Sybase does not provide a native dynamic masking framework. Instead, masking is typically implemented through indirect mechanisms built on top of existing database features. These approaches can be effective in limited scenarios, but they introduce architectural and operational trade-offs that become more visible at scale.
1. View-Based Masking
The most commonly used method relies on views with conditional logic to control data visibility. For example, masking can be applied using a CASE expression that returns either the original value or a masked substitute depending on the current user.
CREATE VIEW masked_customers AS
SELECT
id,
name,
CASE
WHEN user_name() = 'admin' THEN email
ELSE '***MASKED***'
END AS email
FROM customers;
This approach enables basic role-based visibility control without modifying the underlying table. It is suitable for simple environments with a limited number of users and objects.
However, it does not scale well. Each table or access scenario requires a separate view, which leads to logic duplication. In addition, users can bypass masking if they query the base tables directly, and there is no centralized mechanism to enforce consistent masking policies.
2. Stored Procedure Masking
Another approach involves encapsulating access logic within stored procedures. Instead of querying tables directly, applications call procedures that return pre-masked data.
CREATE PROCEDURE get_customer_data
AS
BEGIN
SELECT
id,
name,
'***MASKED***' AS email
FROM customers;
END;
This method centralizes masking logic at the database level and can simplify enforcement within controlled application workflows.
However, it introduces tight coupling between applications and database procedures. All consumers must be rewritten to use these procedures, and any direct query access bypasses masking entirely. Maintaining consistent logic across multiple procedures and environments also becomes increasingly complex over time.
3. Static Masking via Data Substitution
Static masking modifies data directly in the database or in exported datasets before they are shared with other environments.
UPDATE customers SET email = 'user_' + CONVERT(VARCHAR, id) + '@example.com';
This technique is commonly used for test data preparation, where production data is transformed into a non-sensitive format prior to use.
While effective for isolating sensitive data, this approach is destructive by design. Original values are permanently replaced, making the process irreversible unless backups are maintained. It also depends on manual execution or custom scripts, which limits repeatability and introduces risk of human error. Additionally, there is no built-in audit trail to track how and when masking was applied.
4. Export-Level Masking Pipelines
In more complex environments, masking is performed outside the database as part of ETL or data pipeline processes. Data is extracted from production systems, transformed using custom scripts, and then loaded into downstream environments such as testing or analytics platforms.
This approach allows flexibility in how data is transformed, but it shifts masking responsibility into external workflows. As a result, it introduces additional infrastructure, increases operational complexity, and creates multiple points of failure. Ensuring consistency across pipelines becomes difficult, especially when multiple teams or tools are involved.
DataSunrise: Centralized Masking for Sybase
DataSunrise implements data masking for Sybase as an externalized control layer rather than embedding logic inside database objects. It applies Zero-Touch Data Masking combined with Autonomous Compliance Orchestration, allowing organizations to enforce consistent masking policies without modifying schemas, queries, or application code.
Instead of relying on views, stored procedures, or transformation scripts, DataSunrise operates at the query interception layer. All incoming SQL traffic is analyzed before execution, and masking rules are applied dynamically to the result set. This approach ensures that sensitive data is never exposed in raw form, regardless of how the query is constructed or which application initiates it. It aligns closely with broader Data Masking strategies and integrates into a unified Data Security framework.
Dynamic Data Masking
Dynamic masking is enforced at query execution time. Each request is evaluated against defined policies, taking into account user identity, roles, query context, and targeted data fields. Based on this evaluation, sensitive values are modified in the result set before being returned to the client.
This ensures that data remains intact in the database while exposure is controlled at runtime. Unlike native approaches, masking cannot be bypassed through direct table access or alternative query paths, since enforcement occurs outside the database engine. See how this works in practice with Dynamic Data Masking.
Static Data Masking
Static masking is used for controlled data provisioning in non-production environments. DataSunrise generates sanitized datasets by replacing sensitive values while preserving format, structure, and referential integrity.
This allows development, QA, and analytics teams to work with realistic datasets without exposing actual sensitive information. The process is repeatable and policy-driven, eliminating the need for manual transformation scripts or one-off masking operations. More details are available in Static Data Masking and Test Data Management.
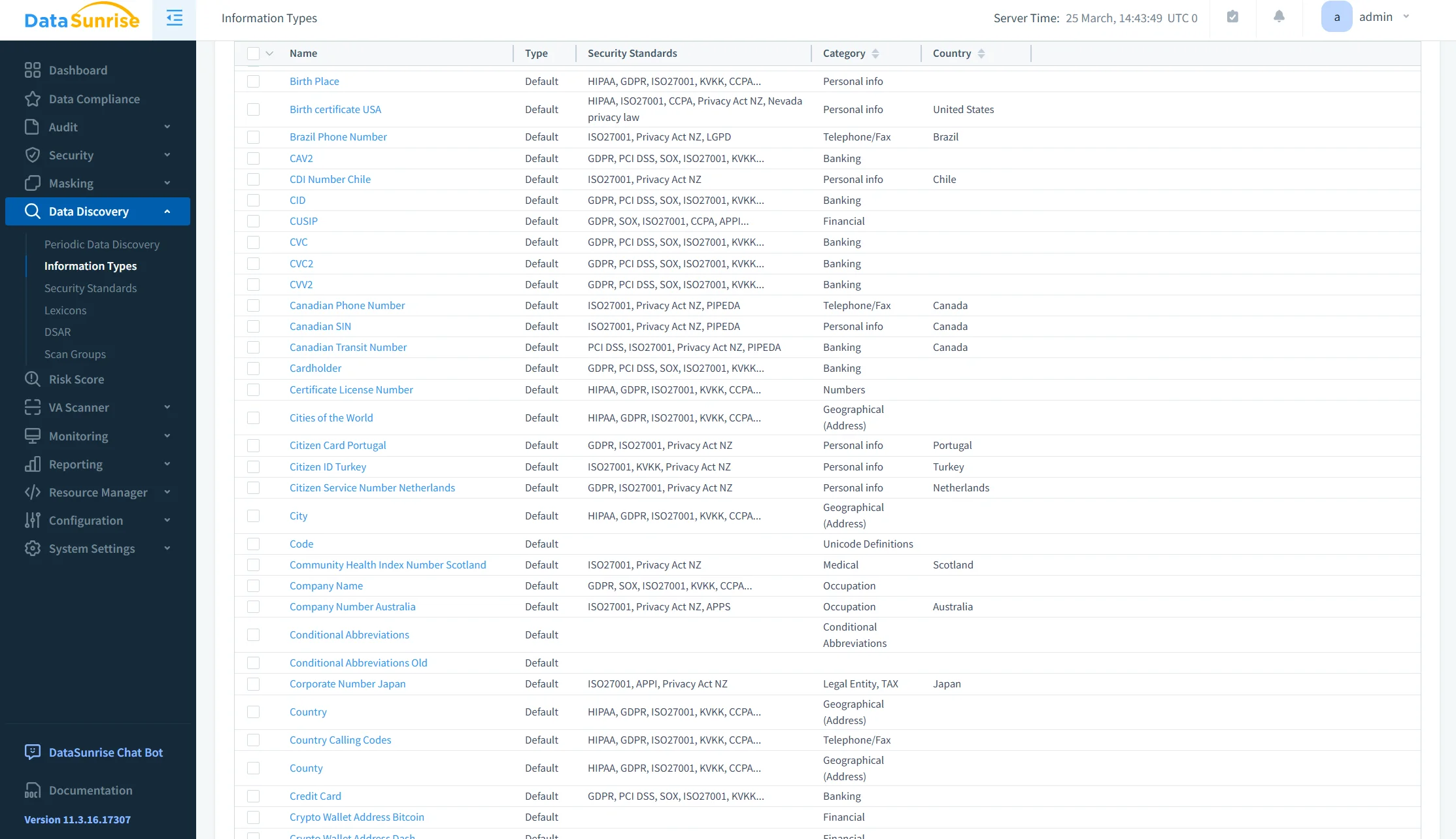
Auto-Discover & Mask
DataSunrise includes automated data discovery capabilities that identify sensitive data across the database environment. This includes detection of personally identifiable information, financial records, credentials, and other regulated data types.
Discovered fields are automatically mapped into masking policies, ensuring that new or previously unknown sensitive data is not left unprotected. This reduces dependency on manual classification and minimizes the risk of incomplete coverage. This capability is powered by Data Discovery.
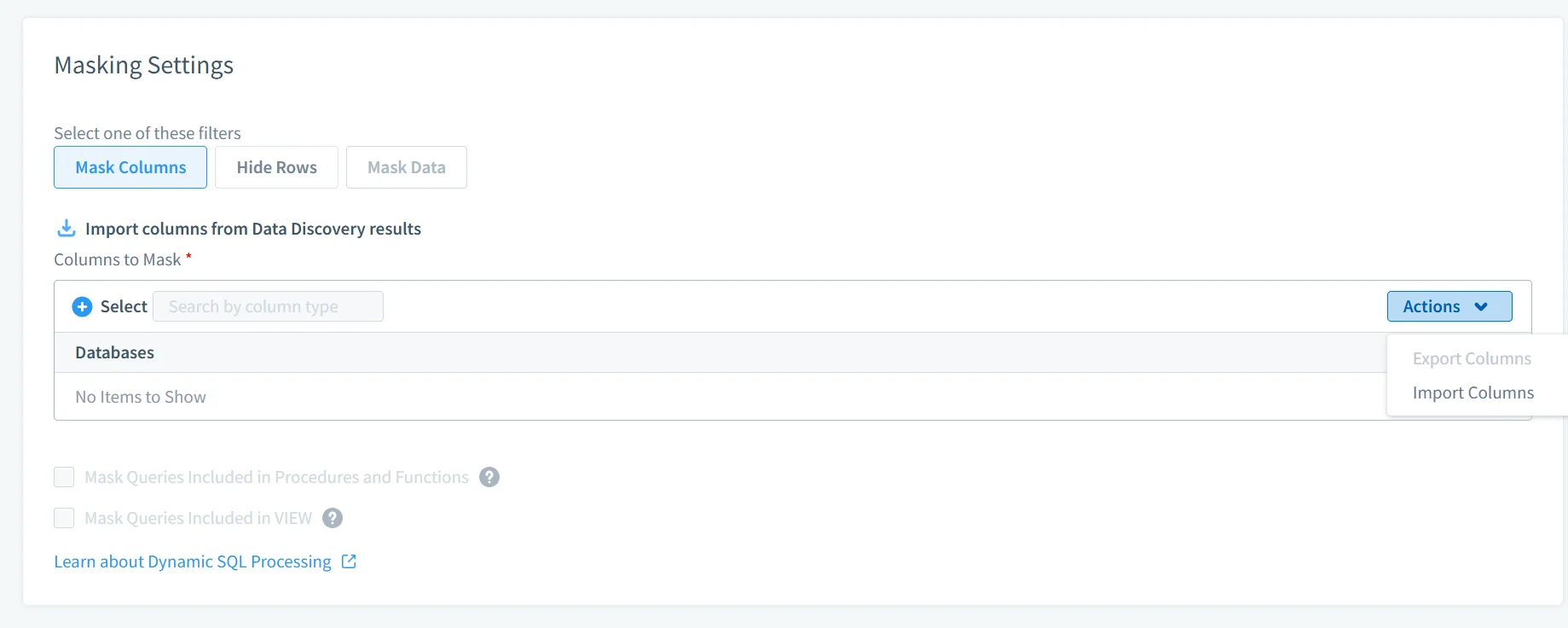
No-Code Policy Automation
Masking policies are defined and managed through a centralized interface. Rules can be configured based on user roles, query attributes, data types, or access patterns without modifying SQL queries or database objects.
This approach removes the need for custom development and simplifies policy management across multiple databases and environments. Changes to masking logic can be applied instantly and consistently, without requiring application updates or database refactoring. These policies integrate with broader Security Policies for unified control.
Flexible Deployment Modes
DataSunrise supports multiple deployment models to fit different infrastructure and security requirements.
In proxy mode, queries are intercepted and modified in real time, enabling full enforcement of masking and security policies. In sniffer mode, traffic is analyzed passively without introducing latency or modifying query execution. Log-based integration allows retrospective analysis and policy validation using database activity logs.
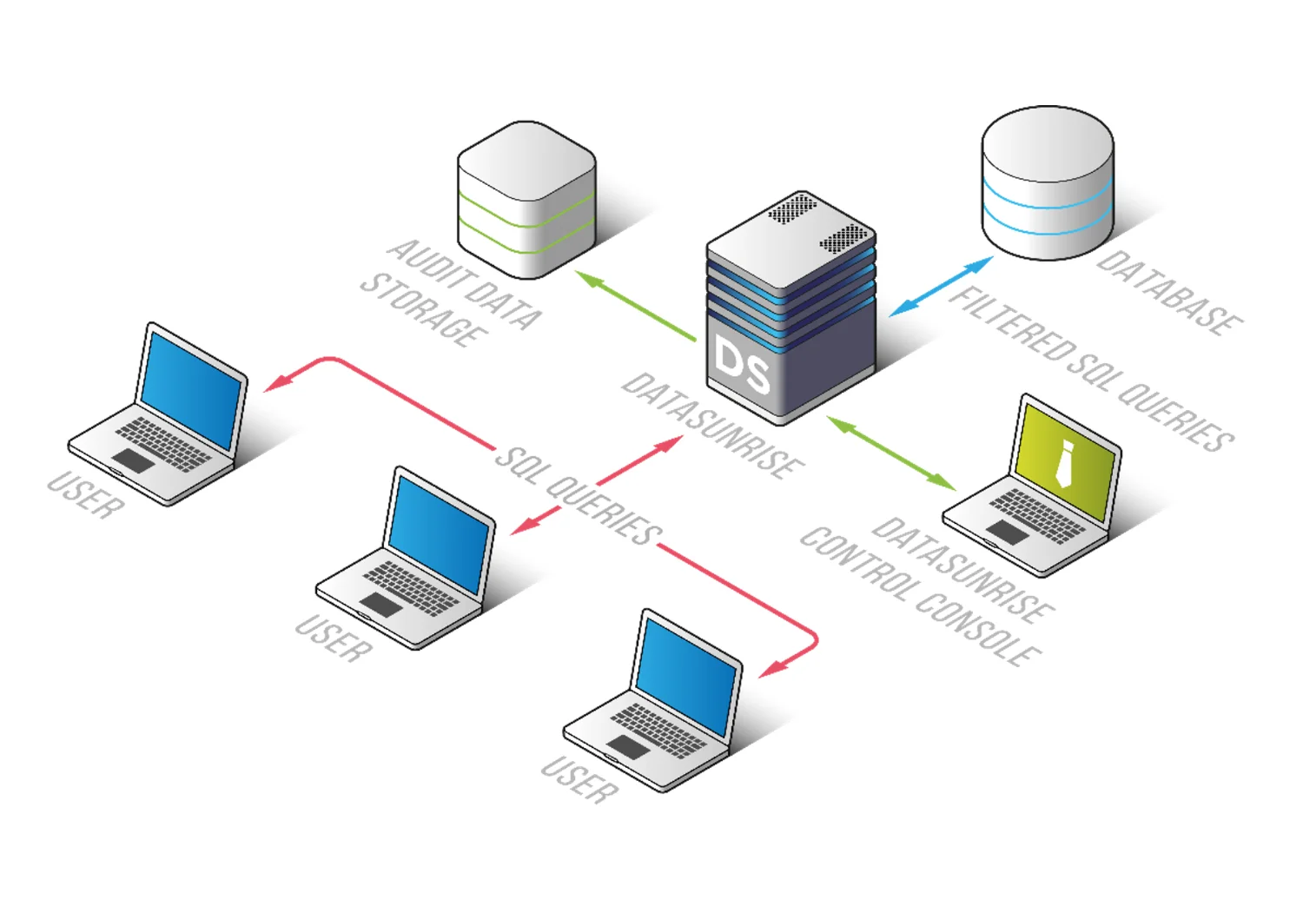
These options enable integration into existing environments without disruption, while maintaining consistent masking enforcement across all access paths. Deployment flexibility is detailed in Deployment Modes and works alongside monitoring capabilities such as Database Activity Monitoring.
Business Impact of Data Masking in Sybase
| Impact | Description |
|---|---|
| Reduced Data Exposure | Sensitive data is never exposed in raw form through techniques like Dynamic Data Masking |
| Faster Compliance | Policies are enforced automatically in alignment with frameworks such as Data Compliance Regulations |
| Lower Maintenance | Eliminates custom SQL masking logic by centralizing control within Data Masking solutions |
| Safer Testing | Realistic but sanitized datasets generated using Static Data Masking |
| Audit Readiness | Full visibility into masking behavior supported by Audit Logs |
Conclusion
Sybase provides mechanisms for access control but does not regulate data exposure at the query result level. As a result, authorized users can retrieve full datasets without restrictions on sensitive fields.
Native masking techniques—such as views, stored procedures, and transformation scripts—introduce fragmented implementations. These approaches require manual maintenance, are difficult to enforce consistently, and do not scale effectively across environments.
A centralized masking strategy addresses these limitations by applying policy-driven controls outside the database engine. This ensures consistent enforcement of data visibility rules regardless of how data is accessed, aligning with modern Data Security practices.
DataSunrise implements this approach through zero-touch masking, autonomous compliance orchestration, and unified security coverage across multiple platforms. Masking policies are applied centrally, reducing operational overhead while improving consistency and control. This model builds on capabilities such as Dynamic Data Masking and integrates with Database Activity Monitoring for full visibility.
Unlike traditional methods that require ongoing adjustments and manual oversight, this model enables continuous compliance alignment and standardized enforcement across all environments, supporting regulatory requirements through Compliance Manager.
When masking depends on application logic or developer discipline, data exposure remains uncontrolled. A centralized masking layer establishes enforceable boundaries on data visibility within authorized access, consistent with modern approaches to Data Masking.
Protect Your Data with DataSunrise
Secure your data across every layer with DataSunrise. Detect threats in real time with Activity Monitoring, Data Masking, and Database Firewall. Enforce Data Compliance, discover sensitive data, and protect workloads across 50+ supported cloud, on-prem, and AI system data source integrations.
Start protecting your critical data today
Request a Demo Download Now
