Data Obfuscation in TiDB
TiDB gives teams a distributed SQL platform that can power transactional workloads, analytics, and operational reporting at the same time. That flexibility is useful until the same production tables start feeding dashboards, ad hoc SQL sessions, support workflows, and lower environments. At that point, names, emails, phone numbers, payment fields, address data, and internal notes can spread far beyond the application that originally needed them.
That is where data masking becomes a practical control rather than a vague security slogan. In TiDB, data obfuscation usually means transforming sensitive values so users and systems can still work with the dataset without seeing the raw truth. Depending on the use case, that can mean dynamic data masking for live query results, static data masking for copied datasets, or more specialized patterns described in common masking techniques. If you want the database background itself, the official TiDB GitHub repository is a useful technical companion.
What data obfuscation actually means in TiDB
In practical terms, obfuscation is not just about hiding a column. It is about changing the representation of a sensitive value so the record remains useful while the original content becomes unreadable, partially revealed, substituted, generalized, or otherwise protected. That matters most when teams use data discovery to locate risky fields and classify PII before those fields leak into the wrong workflow.
The control also has to work alongside broader governance. Strong access controls, sensible role-based access control, and the principle of least privilege define who should access the data. Obfuscation then refines what each user actually sees after that access is granted. Without both layers, a legitimate query can still expose fields that have no business appearing in the result.
Core obfuscation techniques that work well in TiDB
Choosing the right technique matters more than people expect. A blanket “mask everything” approach usually creates either broken workflows or weak protection. Different fields need different treatment, and the choice should follow the intended workload, not just the column name. For compliance-sensitive environments, those decisions should also map back to the relevant regulatory requirements.
| Technique | Best Fit in TiDB | Why It Helps |
|---|---|---|
| Full redaction | National identifiers, secrets, internal tokens | Completely blocks direct exposure of high-risk values |
| Partial reveal | Email, phone, customer references | Keeps limited business utility while hiding the full value |
| Format-preserving masking | Card data, structured identifiers | Retains data shape for testing and UI validation |
| Substitution | Names, addresses, free-text fields | Replaces real values with safe alternatives |
| Generalization | Location data, age ranges, date groups | Preserves analytical usefulness while reducing precision |
| Deterministic obfuscation | Keys reused across tables | Keeps joins and referential relationships stable |
Match the obfuscation method to the workload that will consume the data. Support engineers, BI dashboards, QA scripts, and vendor test runs rarely need the same version of the same field.
How DataSunrise applies obfuscation to TiDB data
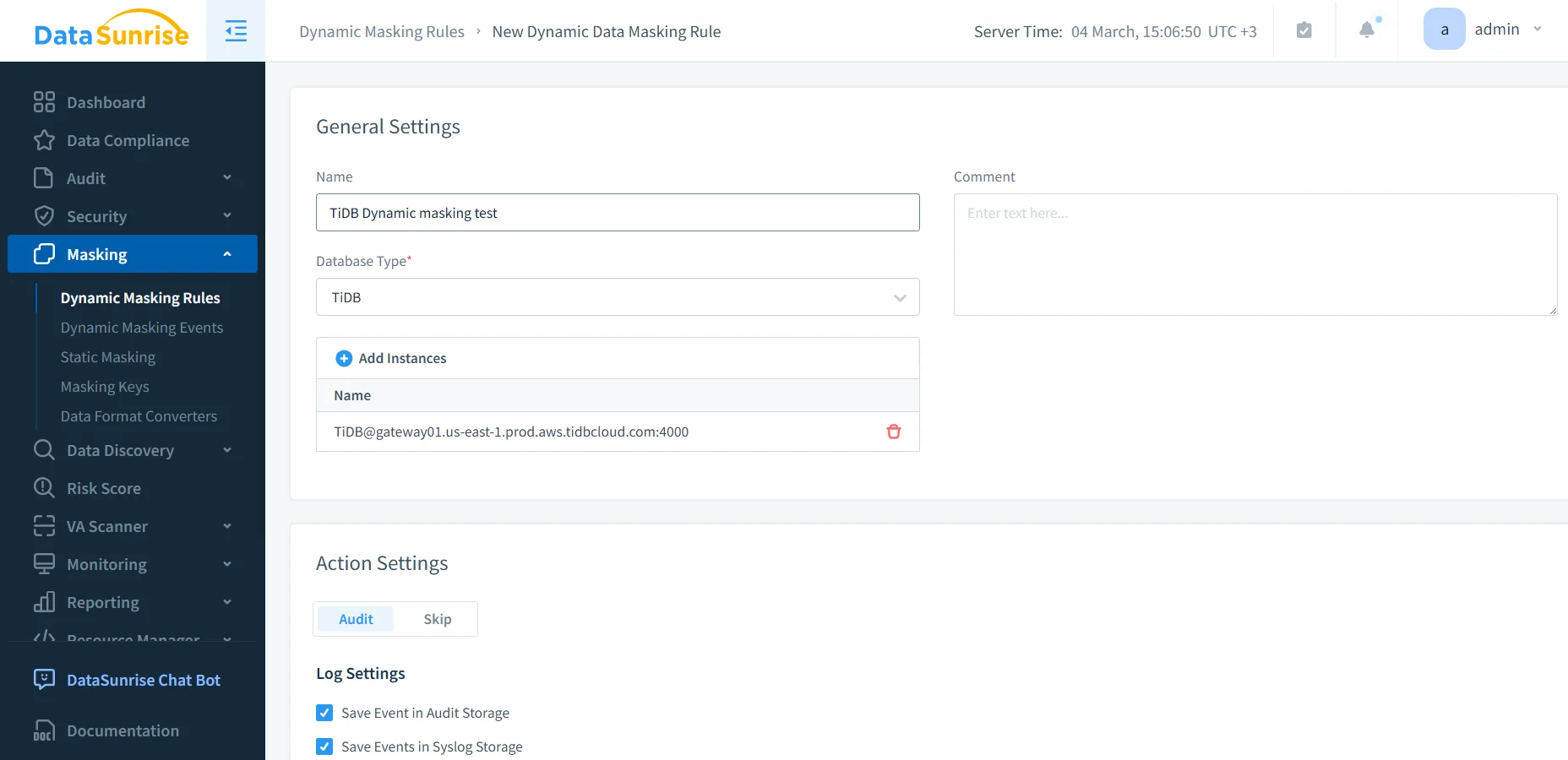
At the tooling level, the workflow is refreshingly straightforward. You connect the TiDB instance, define the rule, select the objects that contain sensitive data, and assign the appropriate masking methods. The actual protection logic can then run at query time or as part of a controlled dataset copy, depending on the environment.
The screenshot below shows the object and column selection stage, where the table ds_masking_demo exposes fields such as full_name, email, phone, national_id, card_number, address_line, ip_addr, and notes. In real deployments, that mix is painfully normal. It is also exactly why obfuscation needs column-level precision instead of lazy table-level assumptions.
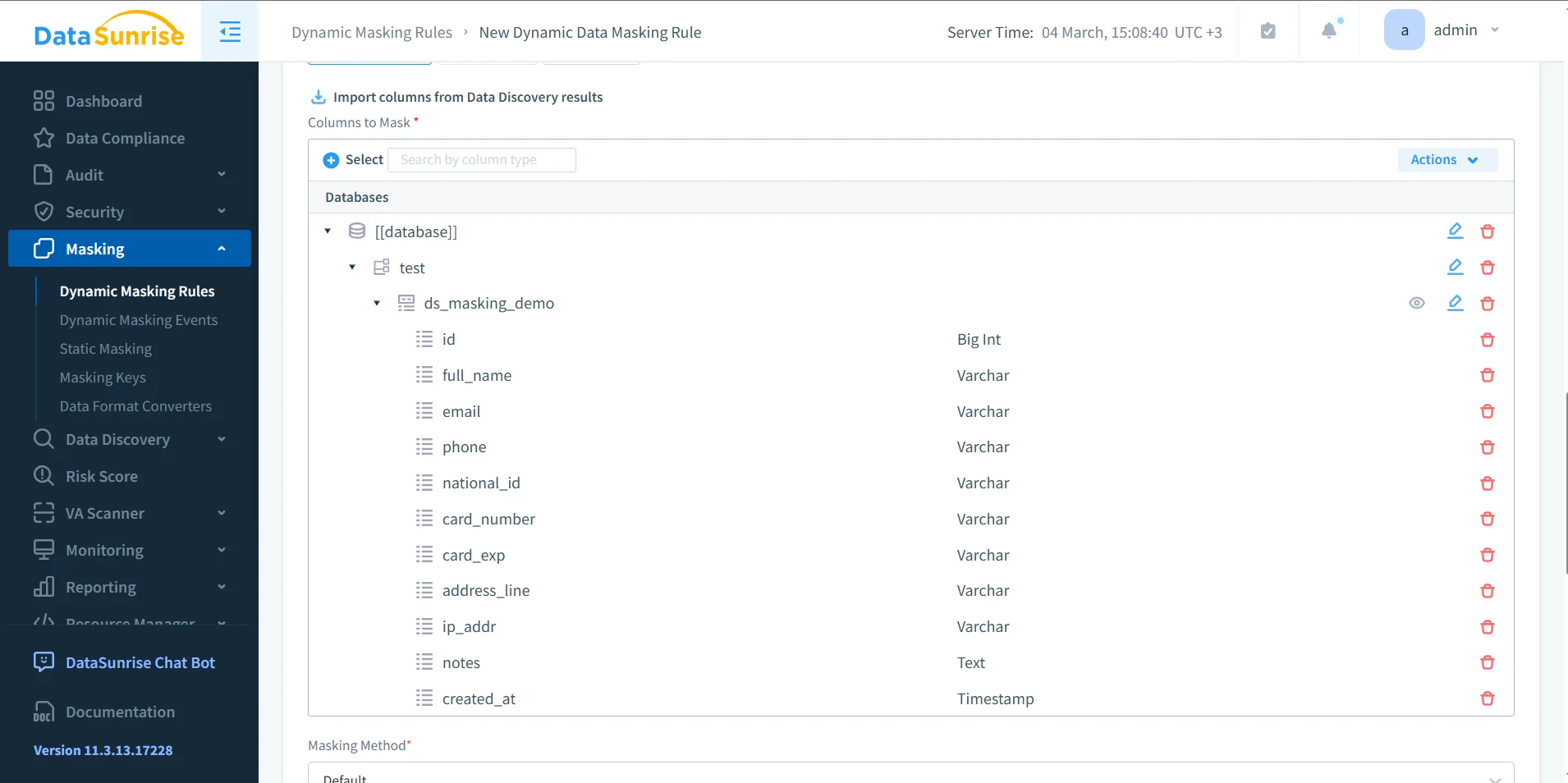
- Connect the instance. Choose the TiDB source and define the enforcement context.
- Select the objects. Focus on tables and views that actually expose sensitive business data.
- Assign the technique. Pick redaction, substitution, partial reveal, format preservation, or another transformation that fits the field.
- Validate the result. Test with the same queries and tools people already use in production or lower environments.
Validating obfuscated results before rollout
A protection rule is only useful if the resulting data remains safe and usable. That means testing the output with real SQL, real dashboards, real joins, and real application flows instead of admiring a screenshot and declaring victory. The simplest validation pattern is still the obvious one:
SELECT
id,
full_name,
email,
phone,
national_id,
card_number,
card_exp,
address_line,
ip_addr,
notes,
created_at
FROM ds_masking_demo;
The screenshot below shows what a strongly obfuscated result can look like. The structure remains queryable, but the sensitive values themselves are stripped away or reduced to safe placeholders.
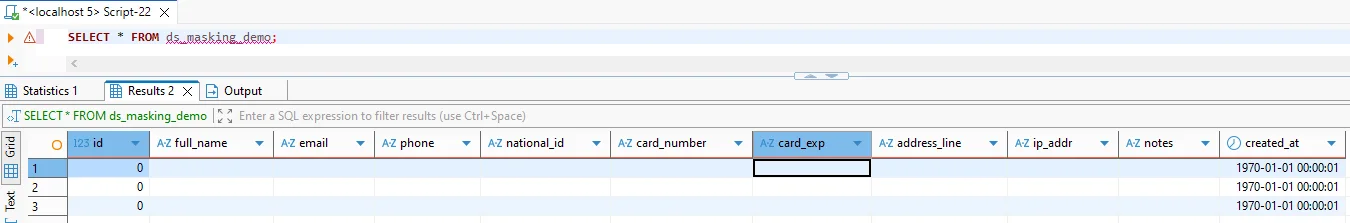
That validation step should also feed into your operational evidence. Teams normally pair masking with database activity monitoring, collect enforcement detail in audit logs, and maintain a defensible audit trail for later review. If someone asks whether a rule was active, when it ran, or which fields it touched, “we think so” is not a serious answer.
Obfuscation can still fail operationally even when the rule executes correctly. If transformed values break filters, joins, reporting logic, or application behavior, teams will work around the control and drag raw data back into the process. Test the protected output against real workloads before calling the rollout finished.
Supporting controls that make obfuscation stronger
Obfuscation works better when it is part of a larger control set. The security guide helps frame masking decisions inside a broader protection strategy. Query paths can be hardened with a database firewall, targeted security rules against SQL injections, and periodic vulnerability assessment checks. Those controls matter because one weak access path can undo an otherwise solid masking design.
At the governance layer, DataSunrise can also feed evidence and review workflows into Compliance Manager. That becomes especially useful when TiDB is only one system in a wider estate and teams need consistency across many supported data platforms instead of rebuilding policy from scratch every time a new engine appears. In practice, that is how obfuscation becomes part of a real database security program instead of a scattered set of one-off rules.
Why obfuscation supports compliance in TiDB
Obfuscation is not merely cosmetic. It helps reduce the blast radius of live SQL access, copied datasets, and downstream reporting by lowering the amount of raw sensitive data that any single workflow can expose.
| Framework | Typical TiDB Exposure | Obfuscation Outcome |
|---|---|---|
| GDPR | Personal data appears in queries, support tools, and analytics | Supports data minimization and controlled disclosure |
| HIPAA | Healthcare-related fields reach non-clinical workflows | Limits unnecessary visibility of protected health information |
| PCI DSS | Payment details leak into result sets and copied environments | Restricts exposure of cardholder data |
| SOX | Financial records spread too widely across reporting access | Improves accountability and controlled handling |
Conclusion
Data obfuscation in TiDB is less about hiding data for the sake of it and more about making the platform usable without letting raw sensitive values roam freely through every query path and copied environment. The winning pattern is not complicated: discover the risky fields, pick the right transformation technique, enforce it with the right tooling, and validate the result against real workloads.
With the right mix of DataSunrise controls, teams can protect live results, support lower-risk copies, and generate the evidence needed for security and compliance review. That is the real point of obfuscation in TiDB: keep the dataset functional, keep the exposure down, and stop treating raw production values like harmless decoration in every tool that happens to connect.
Protect Your Data with DataSunrise
Secure your data across every layer with DataSunrise. Detect threats in real time with Activity Monitoring, Data Masking, and Database Firewall. Enforce Data Compliance, discover sensitive data, and protect workloads across 50+ supported cloud, on-prem, and AI system data source integrations.
Start protecting your critical data today
Request a Demo Download Now
