Sensitive Data Protection in ClickHouse
Protecting sensitive information stored in analytical databases has become a major priority for organizations operating modern data platforms. Systems like ClickHouse process large volumes of business data, including customer records, financial transactions, behavioral analytics, and operational logs. As a result, strong data protection mechanisms are essential to prevent unauthorized exposure.
Data protection strategies typically include access control, masking techniques, auditing, and encryption. Without these safeguards, sensitive fields such as email addresses, phone numbers, payment information, or personally identifiable information (PII) may be exposed through analytical queries, exports, or dashboards.
In this article, we explore the native capabilities available in ClickHouse for protecting sensitive data and examine how centralized security platforms such as DataSunrise can strengthen data protection and compliance across analytical environments.
Importance of Sensitive Data Protection
Sensitive data protection is a fundamental requirement for organizations operating modern analytical databases. Platforms like ClickHouse often process large datasets containing personal information, financial records, authentication data, and internal business metrics. Without proper safeguards, this information can easily be exposed through analytical queries, exports, or integrations with BI tools. Implementing strong data security practices helps organizations maintain control over sensitive information across analytical environments.
Protecting sensitive data helps organizations prevent unauthorized access, reduce the risk of data breaches, and maintain trust with customers and partners. Many industries must also comply with strict regulatory frameworks such as GDPR, HIPAA, and PCI DSS, which require organizations to implement strong controls around how sensitive information is stored, accessed, and processed.
Another important aspect is the growing complexity of modern data ecosystems. Analytical databases frequently integrate with data lakes, dashboards, machine learning pipelines, and third-party applications. As data flows between these systems, the risk of accidental exposure increases. Implementing proper protection mechanisms such as dynamic data masking ensures that sensitive fields remain protected even when accessed by large numbers of analysts or automated processes.
By enforcing strict access policies, applying masking techniques, and continuously monitoring activity through database activity monitoring, organizations can significantly reduce security risks while still allowing teams to perform advanced analytics on large datasets.
Native Sensitive Data Protection Capabilities in ClickHouse
ClickHouse provides several built-in mechanisms that can help administrators protect sensitive information stored inside database tables. These tools focus primarily on access control and query-level restrictions.
Role-Based Access Control
ClickHouse implements a robust Role-Based Access Control (RBAC) model. Administrators can define roles and grant permissions to control which users can access specific databases, tables, or columns.
Example:
CREATE ROLE analysts;
GRANT SELECT ON database.customers TO analysts;
GRANT analysts TO user_analytics;
This approach limits exposure of sensitive tables to only authorized roles.
However, RBAC controls access to objects rather than masking data values themselves.
Column-Level Privileges
ClickHouse also allows administrators to restrict access to individual columns containing sensitive information.
Example:
GRANT SELECT(name, city)
ON database.customers
TO analysts;
In this case, the user can query non-sensitive columns but cannot retrieve protected attributes such as email or phone numbers.
This approach helps prevent accidental exposure of confidential information through analytical queries.
Masking with SQL Transformations
Another common approach in ClickHouse involves masking sensitive values using SQL expressions or functions.
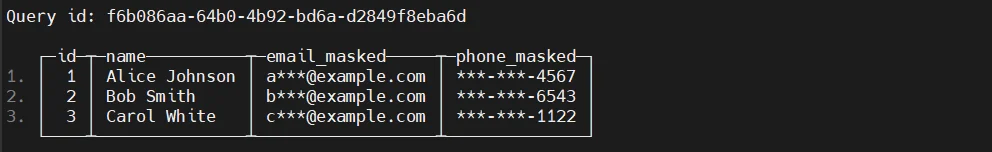
Example:
SELECT
id,
name,
concat(left(email,1),'***',substring(email,position(email,'@'))) AS masked_email
FROM customers;
The query returns partially masked email addresses instead of full values.
Although this method works, it relies heavily on query logic and user discipline.
Masked Views
To centralize masking logic, administrators often create views that transform sensitive columns before returning results.
Views simplify enforcement because masking logic remains consistent across queries.
Extending ClickHouse Data Protection with DataSunrise
Organizations handling regulated or sensitive data often require more advanced protection mechanisms than those provided by native database features.
DataSunrise enhances ClickHouse security by introducing centralized governance, automated masking policies, and real-time monitoring across multiple database systems. Instead of relying on query-level transformations or manual privilege management, DataSunrise enforces protection rules through a proxy-based architecture. This approach allows organizations to secure sensitive information without modifying existing database schemas, queries, or applications.
By combining automated discovery, dynamic data masking, and continuous database activity monitoring, DataSunrise provides a unified platform for protecting sensitive data in analytical environments such as ClickHouse.
Implementing Sensitive Data Protection in DataSunrise
After deploying DataSunrise and connecting a ClickHouse instance, administrators can configure security controls directly through the platform’s centralized management interface. The system provides multiple capabilities designed to identify, protect, and monitor sensitive data across database environments using integrated data security technologies.
Secure ClickHouse Connections
DataSunrise connects to the ClickHouse database instance and begins inspecting database traffic in real time. Once registered in the DataSunrise console, the platform operates as a secure proxy layer that analyzes queries and applies protection policies before results are returned to users.
To configure the connection, administrators provide the host address, port number, and authentication credentials of the ClickHouse server. After the connection is established, DataSunrise continuously monitors incoming database traffic and automatically enforces security policies. This architecture enables organizations to implement sensitive data protection without modifying existing database infrastructure and helps maintain strong database security controls.
Automated Sensitive Data Discovery
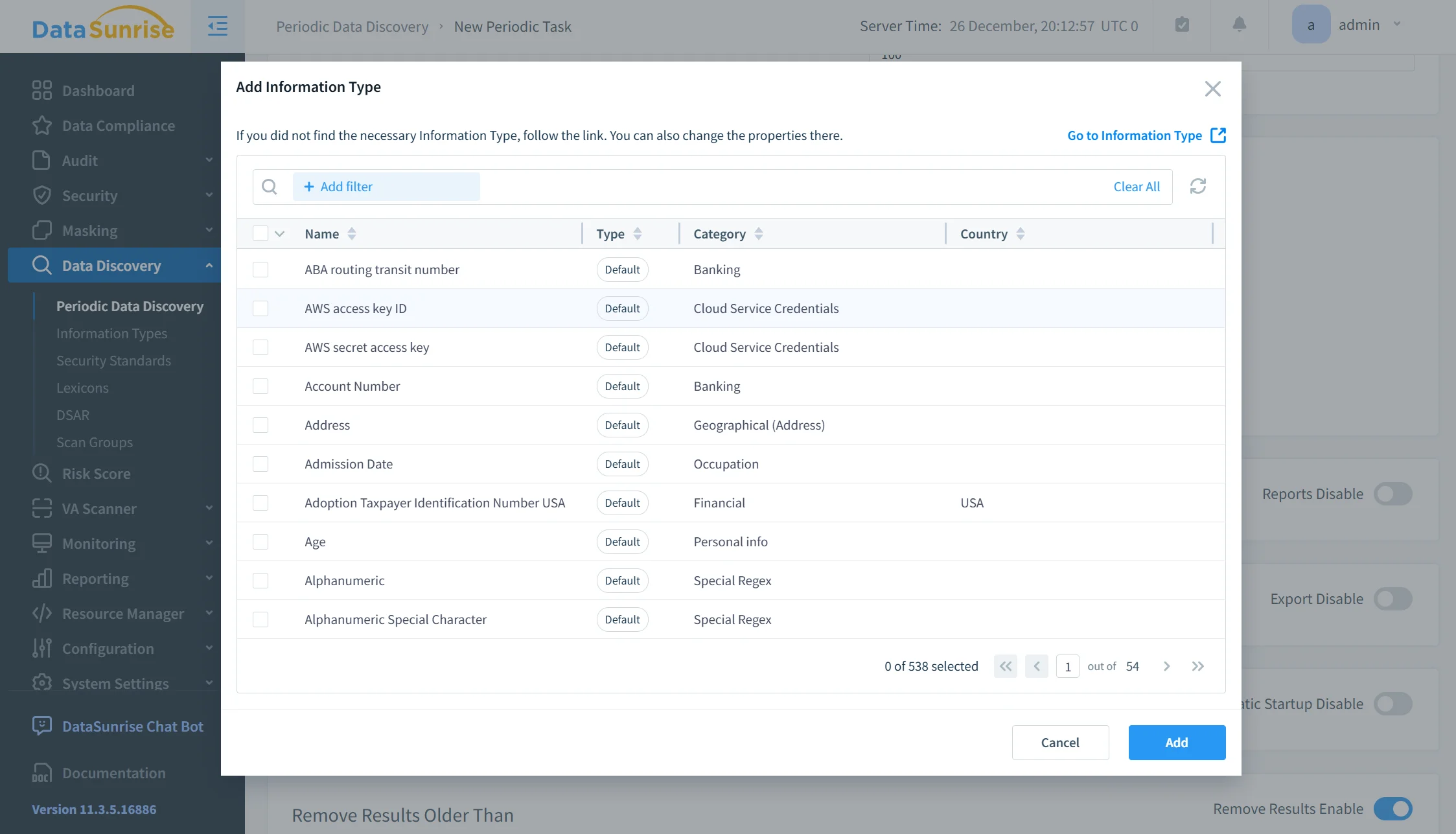
DataSunrise automatically scans database schemas to identify sensitive information stored within ClickHouse tables. The platform analyzes metadata and column values to detect attributes that may require protection.
Typical categories discovered during this process include personal identifiers, financial information, authentication credentials, and contact details. This automated discovery significantly reduces manual classification efforts and ensures that sensitive columns are consistently identified across large analytical datasets through integrated data discovery capabilities.
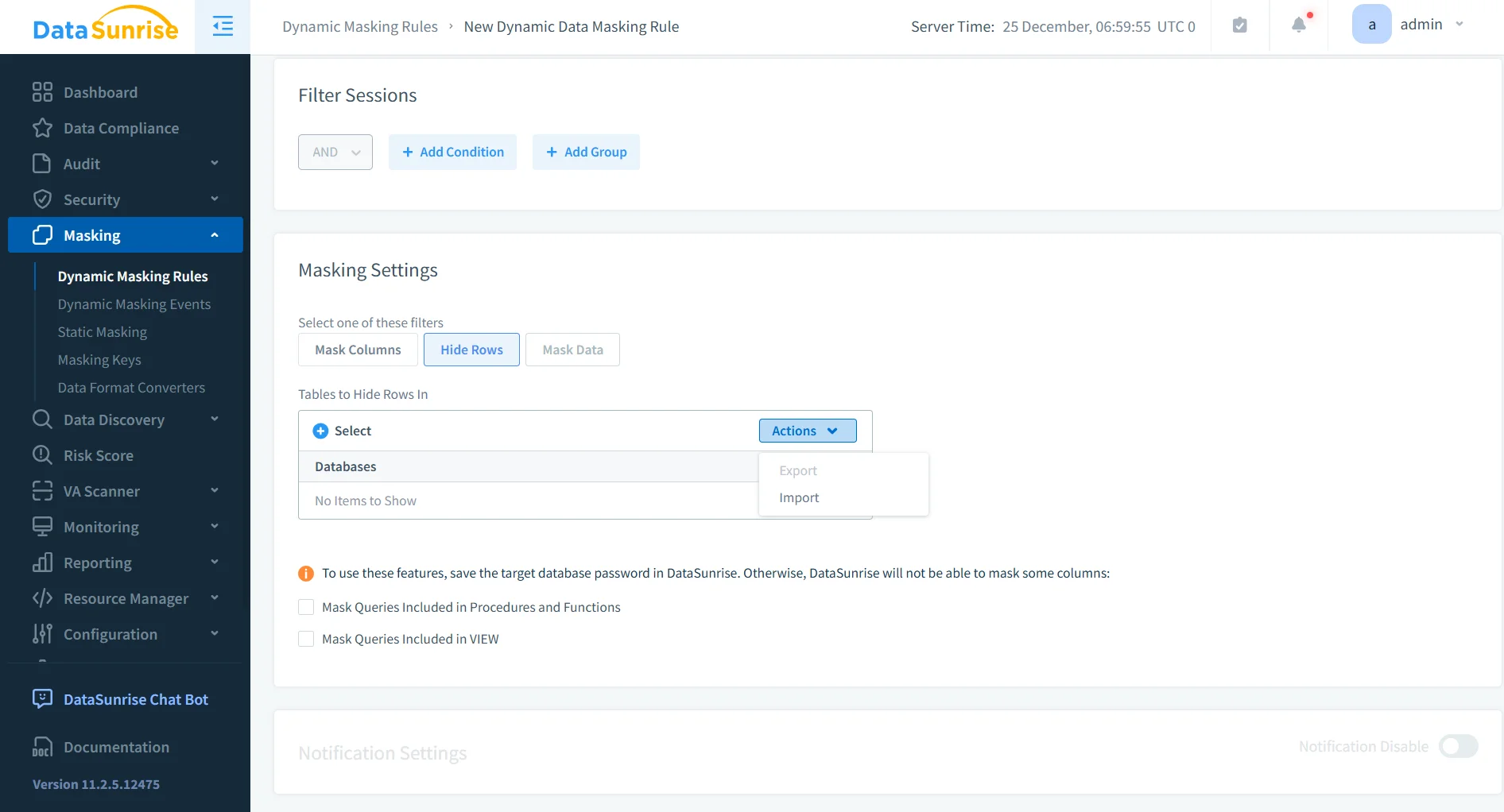
Dynamic Data Masking Policies
Once sensitive columns are identified, administrators can configure masking policies that protect confidential values during query execution.
Masking policies can be applied based on contextual parameters such as user roles, individual accounts, client applications, or network locations. When an unauthorized user attempts to access protected fields, DataSunrise automatically replaces sensitive values with masked data in the query results. At the same time, the original information remains unchanged in the database, ensuring both security and operational continuity.
Continuous Monitoring of Sensitive Data Access
In addition to protecting data during queries, DataSunrise continuously records activity involving sensitive information. The platform maintains detailed access trails that allow security teams to track how protected data is accessed within ClickHouse environments.
Administrators can analyze user access behavior, executed SQL statements, timestamps of database activity, and potential anomalies or suspicious patterns. This level of visibility strengthens data governance, supports security investigations, and helps organizations maintain compliance with modern data protection regulations through centralized monitoring and reporting capabilities.
Business Benefits of Protecting Sensitive Data in ClickHouse
Implementing strong sensitive data protection mechanisms provides measurable operational advantages.
| Benefit | Description |
|---|---|
| Reduced Risk of Data Breaches | Sensitive values remain protected even when users run analytical queries on production datasets. |
| Improved Regulatory Compliance | Automated security policies simplify adherence to privacy and financial regulations. |
| Simplified Security Management | Centralized policy enforcement reduces administrative overhead and simplifies security administration. |
| Safer Analytics Workflows | Analysts and developers can access datasets for analytics without exposing confidential information. |
Conclusion
ClickHouse delivers powerful analytical capabilities for modern data platforms, but protecting sensitive information remains a critical responsibility for organizations handling large datasets.
Native security features such as RBAC, column privileges, and masked views provide useful baseline protection. However, these methods often require manual configuration and careful operational management.
Solutions like DataSunrise extend ClickHouse security with automated data discovery, centralized data masking policies, and real-time database activity monitoring.
By implementing automated sensitive data protection strategies, organizations can safely leverage the performance of ClickHouse while maintaining strong data governance and regulatory compliance.
To explore advanced protection capabilities for ClickHouse environments, review the DataSunrise deployment options and security tools.
Protect Your Data with DataSunrise
Secure your data across every layer with DataSunrise. Detect threats in real time with Activity Monitoring, Data Masking, and Database Firewall. Enforce Data Compliance, discover sensitive data, and protect workloads across 50+ supported cloud, on-prem, and AI system data source integrations.
Start protecting your critical data today
Request a Demo Download Now