Sensitive Data Protection in ScyllaDB
Sensitive Data Protection in ScyllaDB requires more than basic authentication and encryption. Modern distributed NoSQL environments process high-volume transactional workloads, often containing Personally Identifiable Information (PII), payment records, healthcare data, and confidential operational details. As regulatory pressure increases under frameworks such as GDPR, HIPAA, and PCI DSS, organizations must implement continuous, intelligent controls that protect sensitive data in real time.
According to the latest IBM Cost of a Data Breach Report, the global average cost of a breach continues to rise year over year, reinforcing the importance of proactive data protection strategies in distributed systems environments:
https://www.ibm.com/reports/data-breach
Additionally, regulatory guidance such as the NIST Zero Trust Architecture framework emphasizes minimizing implicit trust and enforcing strict access verification across systems and workloads:
https://csrc.nist.gov/publications/detail/sp/800-207/final
ScyllaDB delivers high-performance distributed processing. However, native capabilities alone do not provide full lifecycle protection across discovery, masking, monitoring, compliance reporting, and cross-environment governance. Effective protection requires centralized Database Security controls and continuous Data Protection enforcement across hybrid and multi-cloud deployments. This article explains how to approach sensitive data protection in ScyllaDB using both native controls and an enterprise-grade Unified Security Framework.
Importance of Sensitive Data Protection
Sensitive Data Protection in ScyllaDB is not just a technical task — it is a business necessity. Distributed NoSQL clusters scale horizontally across nodes and regions, meaning a single misconfiguration or over-privileged account can expose millions of records within seconds.
ScyllaDB commonly powers financial systems, healthcare platforms, and large SaaS environments. These workloads store identifiers, payment data, authentication tokens, and behavioral information, including Personally Identifiable Information (PII). Without layered controls, such data becomes vulnerable to insider misuse, credential theft, and privilege escalation.
Regulatory exposure under GDPR, HIPAA, and PCI DSS is only part of the risk. Organizations also face reputational damage, incident response costs, contractual penalties, and loss of customer trust.
Because data is replicated across nodes for performance and availability, the attack surface expands with scale. Protection must therefore operate consistently across all replicas and environments, supported by centralized Database Security policies.
Effective Sensitive Data Protection in ScyllaDB requires continuous discovery, context-aware access control, real-time monitoring through Database Activity Monitoring, and centralized compliance visibility. Encryption and authentication alone are not enough. Protection must enforce policy at query time — not after a breach — as part of a broader Data Protection strategy.
Sensitive data protection is now a core element of operational resilience and long-term business stability.
Native Sensitive Data Protection Capabilities in ScyllaDB
ScyllaDB includes foundational security mechanisms that support secure cluster operations. These controls provide baseline protection for distributed NoSQL environments, but they are primarily infrastructure-focused rather than policy-driven.
1. Role-Based Access Control (RBAC)
ScyllaDB implements role-based access restrictions similar to Apache Cassandra. Administrators can define roles and assign privileges:
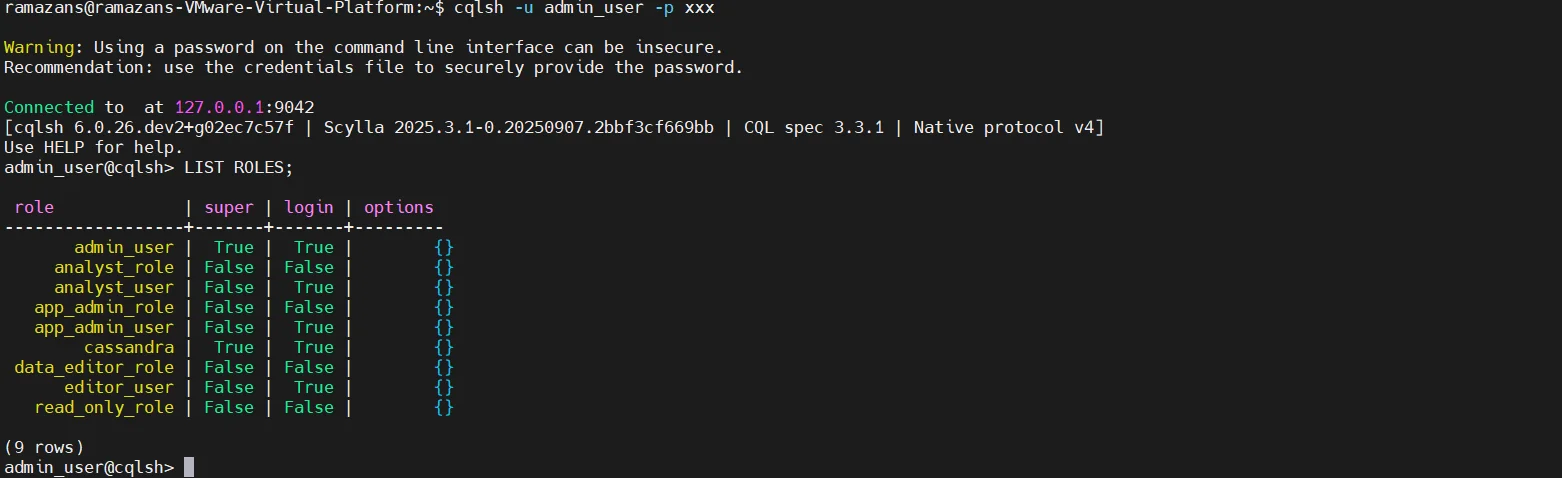
RBAC determines who can access keyspaces and tables. However, it does not control data visibility within approved queries. If a user has SELECT permission, full column values are returned without masking. RBAC answers the question, “Can this user access this object?” It does not answer, “How much of the data should this user see?”
In regulated environments, that distinction is critical. Access control alone cannot prevent overexposure of sensitive fields such as payment numbers, medical identifiers, or authentication tokens. Once access is granted, data is delivered in full without contextual restriction.
2. TLS Encryption in Transit
ScyllaDB supports encrypted client-to-node and inter-node communication using TLS. Encryption protects data from interception during transmission and secures communication between application services and cluster nodes.
A typical TLS configuration in scylla.yaml may include:
client_encryption_options:
enabled: true
certificate: /etc/scylla/certs/db.crt
keyfile: /etc/scylla/certs/db.key
truststore: /etc/scylla/certs/ca.crt
require_client_auth: true
server_encryption_options:
internode_encryption: all
certificate: /etc/scylla/certs/db.crt
keyfile: /etc/scylla/certs/db.key
truststore: /etc/scylla/certs/ca.crt
However, TLS secures only the communication channel. Once a query is authenticated and authorized, the database returns complete results to the requesting user. Encryption protects data in motion, not data usage. It does not provide field-level masking, contextual filtering, behavioral monitoring, or runtime policy enforcement.
3. Disk-Level Encryption
Encryption at rest protects data files stored on disk and reduces risk in cases of physical theft or storage compromise. In cloud environments, encryption at rest is typically enabled at the storage layer. For example, on AWS EBS:
aws ec2 create-volume \
--availability-zone us-east-1a \
--size 100 \
--encrypted
On Linux systems, disk encryption can be configured using LUKS:
cryptsetup luksFormat /dev/sdb
cryptsetup open /dev/sdb secure_volume
While this ensures raw storage files cannot be read without proper keys, disk encryption does not provide query-level inspection, user activity tracking, context-aware access control, or runtime policy enforcement. If credentials are compromised, encrypted storage does not prevent legitimate database queries from exposing sensitive information. Protection ends once authorized access is granted.
4. Audit Logging (Enterprise Editions)
ScyllaDB Enterprise provides audit logging features capable of capturing login events, schema changes, data modification attempts, and authentication failures. Audit logging can be enabled in configuration:
audit: "table"
audit_categories: "AUTH,DDL,DML"
audit_tables: "finance.transactions"
audit_keyspaces: "finance"
These logs assist with forensic investigation and post-incident analysis. However, native audit logging is reactive rather than preventive. It records what has already occurred but does not block suspicious queries, mask sensitive fields, or dynamically enforce compliance policies at runtime.
In addition, audit logs typically require manual parsing, integration with external log aggregation tools such as SIEM platforms, and custom reporting workflows. They do not automatically align with regulatory templates such as SOX Compliance or centralized Database Activity Monitoring frameworks.
Zero-Touch Sensitive Data Protection with DataSunrise
DataSunrise deploys Autonomous Compliance Orchestration to deliver Sensitive Data Protection in ScyllaDB with zero-touch implementation. Through Flexible Deployment Modes—including proxy mode, sniffer mode, and native log trailing—organizations gain frictionless integration without modifying applications or restructuring infrastructure. Protection operates transparently between clients and the database cluster, ensuring consistent enforcement without disrupting workloads. Deployment flexibility is described in Deployment Modes of DataSunrise.
1. Sensitive Data Discovery & Auto-Discover & Mask
DataSunrise performs automated discovery across structured sources such as CQL-based schemas, semi-structured formats like JSON, and unstructured data repositories. The platform identifies Personal Information (PII), financial identifiers, healthcare attributes, and fully customizable sensitive data categories defined by organizational policy. More details about this mechanism are available in the Data Discovery section.
Discovery is continuous rather than one-time. As schemas evolve or new tables appear, periodic scanning detects newly introduced sensitive elements. Identified assets can automatically trigger Auto-Discover & Mask workflows. This enables Zero-Touch Data Masking before sensitive information leaves the cluster, eliminating exposure at query time rather than after incident detection. General masking principles are described in the Data Masking overview.
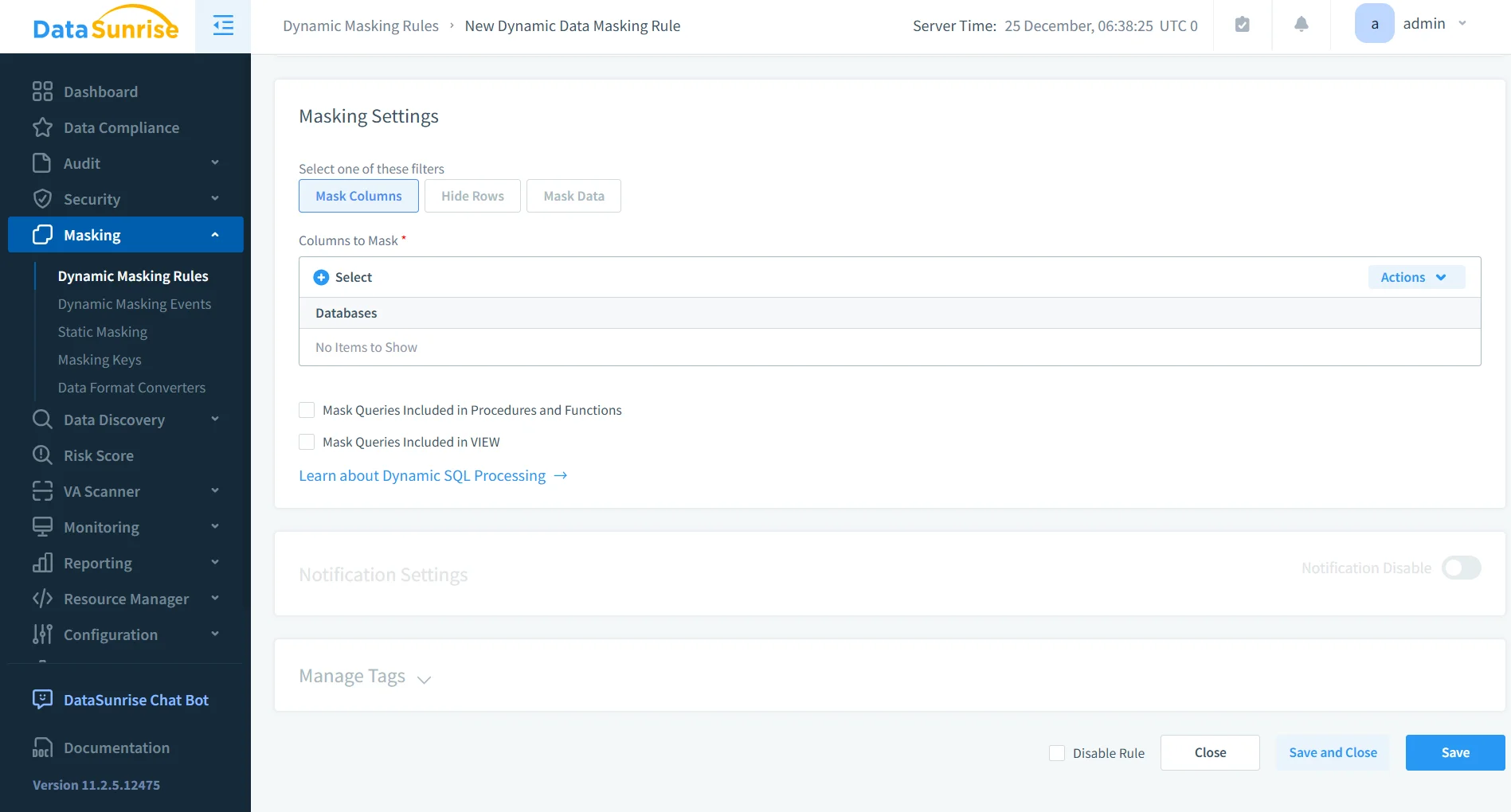
2. Dynamic and Static Masking
Unlike basic RBAC controls, DataSunrise enables Surgical Precision Masking that enforces Context-Aware Protection at runtime. Dynamic masking policies adjust output results based on user roles, IP addresses, application identity, and query context. Implementation details are available in the Dynamic Data Masking section.
For non-production environments, in-place static masking replaces sensitive values directly in stored datasets, ensuring that test and analytics systems never contain real production data. This model is described in the Static Data Masking documentation. Together, dynamic and static masking strategies ensure Zero-Trust Data Access across environments without breaking application logic.
3. ML Audit Rules & Suspicious Behavior Detection
DataSunrise extends ScyllaDB logging capabilities with ML Audit Rules, advanced User Behavior Monitoring, and UEBA-driven anomaly detection. Instead of relying solely on static filters, the platform analyzes behavioral patterns and identifies deviations using mechanisms described in the Behavior Analytics section.
In addition, the platform enhances visibility through centralized Database Activity Monitoring, providing detailed operational insight across distributed environments.
Compliance Drift Detection ensures that policy enforcement remains aligned with regulatory requirements as infrastructure evolves. Unlike solutions that require constant manual tuning, DataSunrise delivers Continuous Regulatory Calibration, dynamically adjusting enforcement across hybrid and multi-cloud deployments.
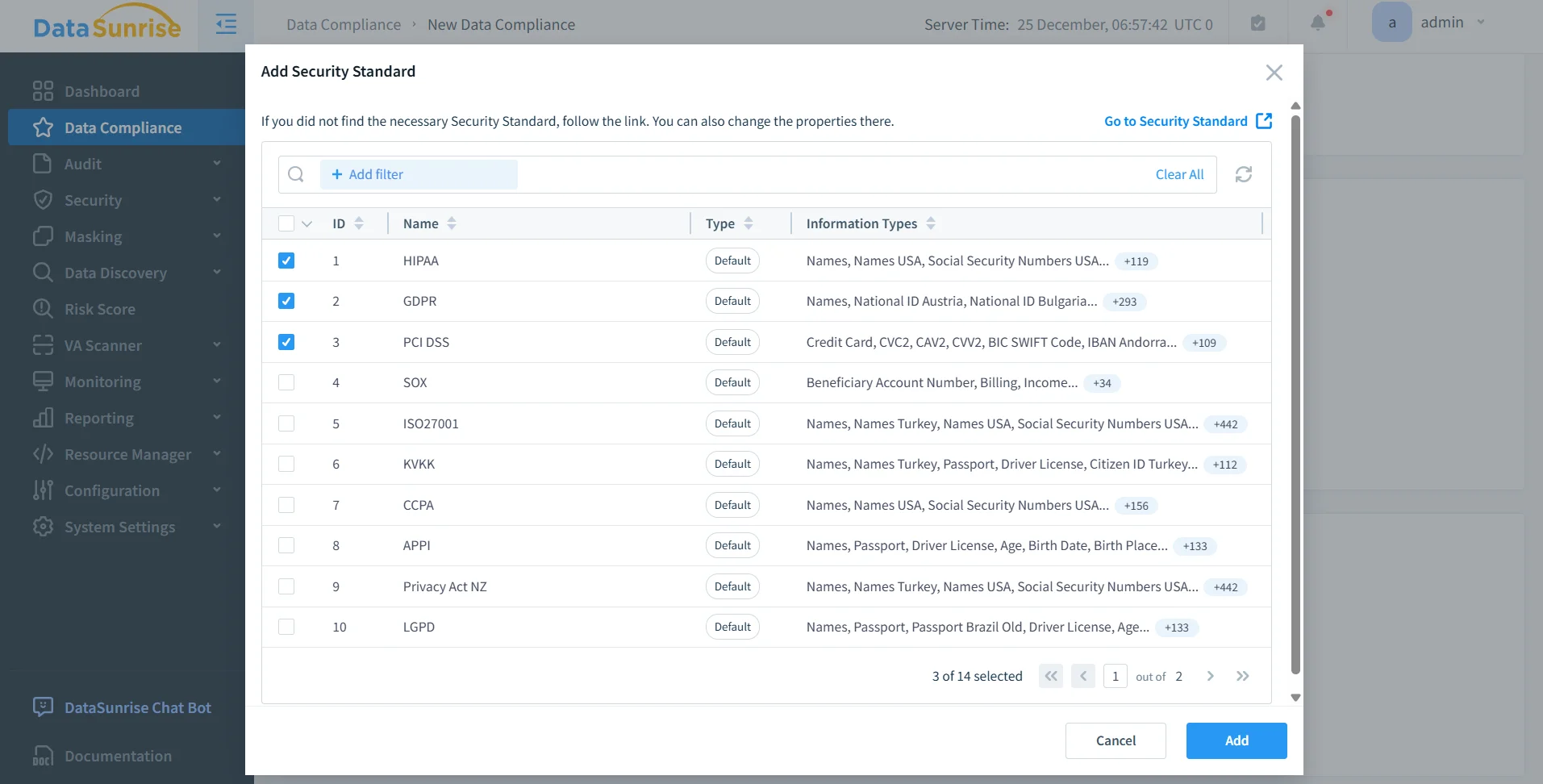
4. Compliance Autopilot & Automatic Policy Generation
DataSunrise implements Compliance Autopilot aligned with regulatory frameworks including GDPR, HIPAA, PCI DSS, SOX, ISO 27001, and SOC 2. Centralized compliance management is provided through Compliance Manager.
Automatic Policy Generation creates audit, masking, and security rules based on discovered sensitive data categories. The platform delivers one-click audit-ready reporting, minimizing manual oversight while accelerating time-to-compliance.
5. Centralized Data Compliance Platform
Sensitive Data Protection in ScyllaDB should not operate in isolation. DataSunrise delivers a Unified Security Framework spanning SQL and NoSQL databases, data warehouses, cloud storage platforms, and hybrid or heterogeneous environments.
Centralized policy management ensures consistent enforcement across distributed clusters and multi-environment architectures. By providing seamless multi-environment coverage and unified governance, the platform eliminates fragmented security controls and significantly reduces operational complexity while strengthening the overall Database Security strategy.
Business Impact of Autonomous Sensitive Data Protection
Organizations implementing Zero-Touch Sensitive Data Protection in ScyllaDB achieve measurable outcomes:
| Impact Area | Business Outcome |
|---|---|
| Quantifiable Risk Reduction | Sensitive data is never exposed to unauthorized or over-privileged users, reducing breach probability and regulatory penalties. |
| Streamlined Compliance Workflows | Automatic Compliance Policy Generation eliminates manual mapping to GDPR, HIPAA, and PCI DSS controls, simplifying audit preparation. |
| Significant Reduction in Manual Effort | No custom scripts, no application rewrites, and no fragmented audit collection across distributed environments. |
| Optimized Total Cost of Compliance | Centralized governance lowers operational overhead and accelerates regulatory audits, improving overall cost efficiency. |
Conclusion
ScyllaDB delivers high-performance distributed data processing. However, native encryption and RBAC mechanisms alone cannot guarantee full Sensitive Data Protection in regulated environments or provide comprehensive Database Security governance across distributed clusters.
DataSunrise provides Zero-Touch Data Masking, Autonomous Compliance Orchestration, Continuous Regulatory Calibration, and Enterprise-Grade Policy Enforcement for ScyllaDB across cloud, on-premise, and hybrid infrastructures. Its capabilities extend traditional monitoring through advanced Dynamic Data Masking and centralized policy control.
By combining Auto-Discover & Mask, ML Audit Rules, Compliance Autopilot, and Unified Security Framework capabilities, organizations eliminate sensitive data exposure at query time while accelerating compliance readiness and reducing operational risk through automated Compliance Manager integration.
Protect Your Data with DataSunrise
Secure your data across every layer with DataSunrise. Detect threats in real time with Activity Monitoring, Data Masking, and Database Firewall. Enforce Data Compliance, discover sensitive data, and protect workloads across 50+ supported cloud, on-prem, and AI system data source integrations.
Start protecting your critical data today
Request a Demo Download Now