Sensitive Data Protection in Sybase
Data compliance and regulatory alignment are no longer optional when working with enterprise databases. Sybase environments often store financial records, personal data, and operational intelligence that require strict control over access, visibility, and exposure.
Unlike auditing, which answers who did what, sensitive data protection focuses on what users are actually allowed to see and extract. That distinction matters. A perfectly logged data leak is still a data leak.
According to IBM’s Cost of a Data Breach Report, data exposure incidents continue to rise in both frequency and impact. In parallel, organizations must align with frameworks such as GDPR, which explicitly require protection of sensitive data at every stage of processing.
This article explains how sensitive data protection works in Sybase using native capabilities and how a centralized approach improves security and compliance.
What is Sensitive Data Protection?
Sensitive data protection is the practice of identifying, classifying, and securing critical information to prevent unauthorized access, exposure, or misuse. This includes data such as personally identifiable information (PII), financial records, healthcare data, credentials, and proprietary business information.
In database environments like Sybase, sensitive data protection operates across several layers. It starts with data discovery—understanding where sensitive data exists. It then moves to access control and masking, ensuring that users only see the data they are allowed to see. Finally, it includes monitoring and enforcement, often supported by database activity monitoring, tracking how data is accessed and preventing suspicious or unauthorized activity.
Unlike traditional security models that rely only on permissions, sensitive data protection focuses on data visibility. A user may have access to a table, but that does not mean they should see every column or every value in clear form.
In practice, effective sensitive data protection combines multiple controls such as role-based access control, masking, encryption, and activity monitoring. When these controls are not centralized, they become difficult to manage and easy to bypass, which is why modern approaches shift enforcement closer to the query layer rather than relying solely on database logic.
Native Sybase Capabilities for Data Protection
Sybase ASE provides several mechanisms that contribute to data protection, but they operate separately and require manual implementation. These features were designed primarily for access control and data integrity, not for fine-grained control over data exposure in modern compliance-driven environments.
Role-Based Access Control
RBAC allows restricting access to tables and operations. For example:
GRANT SELECT ON employees TO analyst_role; REVOKE SELECT ON salaries FROM analyst_role;
This works at the object level but does not limit visibility within accessible data. Once a user has access to a table, they can retrieve all permitted columns in full. There is no native way to partially expose data based on context, role hierarchy, or query intent.
Views for Data Restriction
Views are often used to hide sensitive columns:
CREATE VIEW employee_public AS SELECT id, name, department FROM employees;
This approach introduces abstraction but does not enforce it. Users can still query the underlying tables directly if permissions allow it. Over time, managing multiple views for different roles leads to duplication, inconsistent logic, and increased maintenance overhead. In large environments, this becomes difficult to scale and audit.
Stored Procedures
Stored procedures can control what data is returned:
CREATE PROCEDURE get_employee_data AS SELECT id, name, NULL AS salary FROM employees;
This method attempts to centralize access logic, but it depends entirely on application discipline. If users bypass procedures and query tables directly, the protection is ineffective. Additionally, maintaining complex procedures for different access scenarios increases development and testing effort.
Centralized Sensitive Data Protection with DataSunrise
DataSunrise introduces a different model. Instead of embedding protection logic inside the database, it applies policies externally at the query layer.
It uses non-intrusive deployment modes such as proxy, sniffer, and log-based monitoring, allowing protection without changing database structure. This approach removes dependency on application logic and ensures that every query is evaluated against a centralized policy engine before execution.
Unlike native Sybase mechanisms, which require manual coordination between multiple database objects, DataSunrise enforces consistent protection across all access paths—whether queries originate from applications, BI tools, or direct connections.
Sensitive Data Discovery
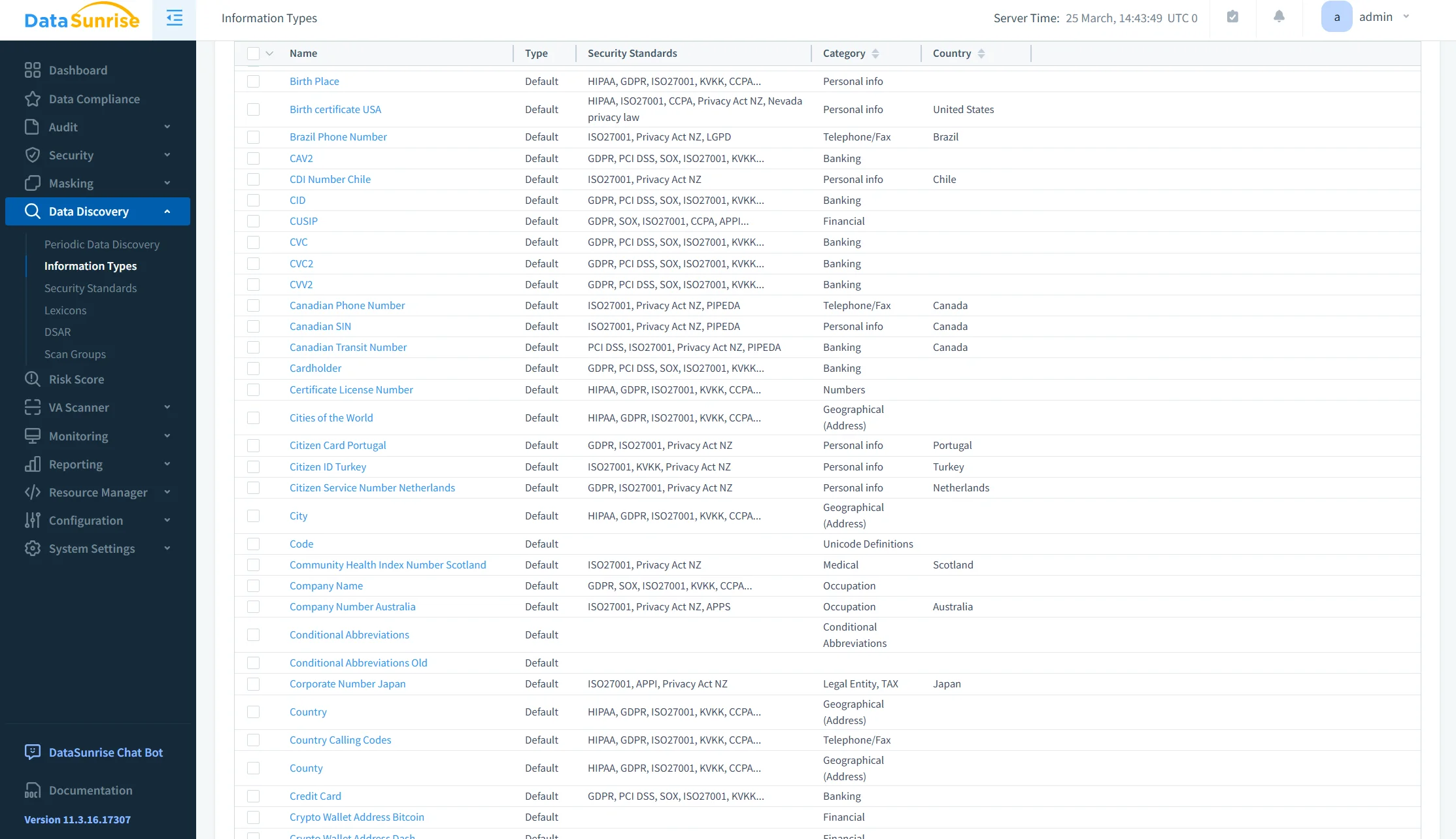
Sensitive Data Discovery automatically identifies critical fields across the database using pattern matching, dictionaries, and classification rules.
Instead of relying on manual tagging, the system scans schemas and data content to detect elements such as PII, financial data, and credentials. This ensures that no sensitive column is overlooked, even in large or evolving environments.
Discovery also supports continuous scanning, which means newly created tables or modified structures are automatically evaluated. This eliminates blind spots and keeps protection aligned with real data usage.
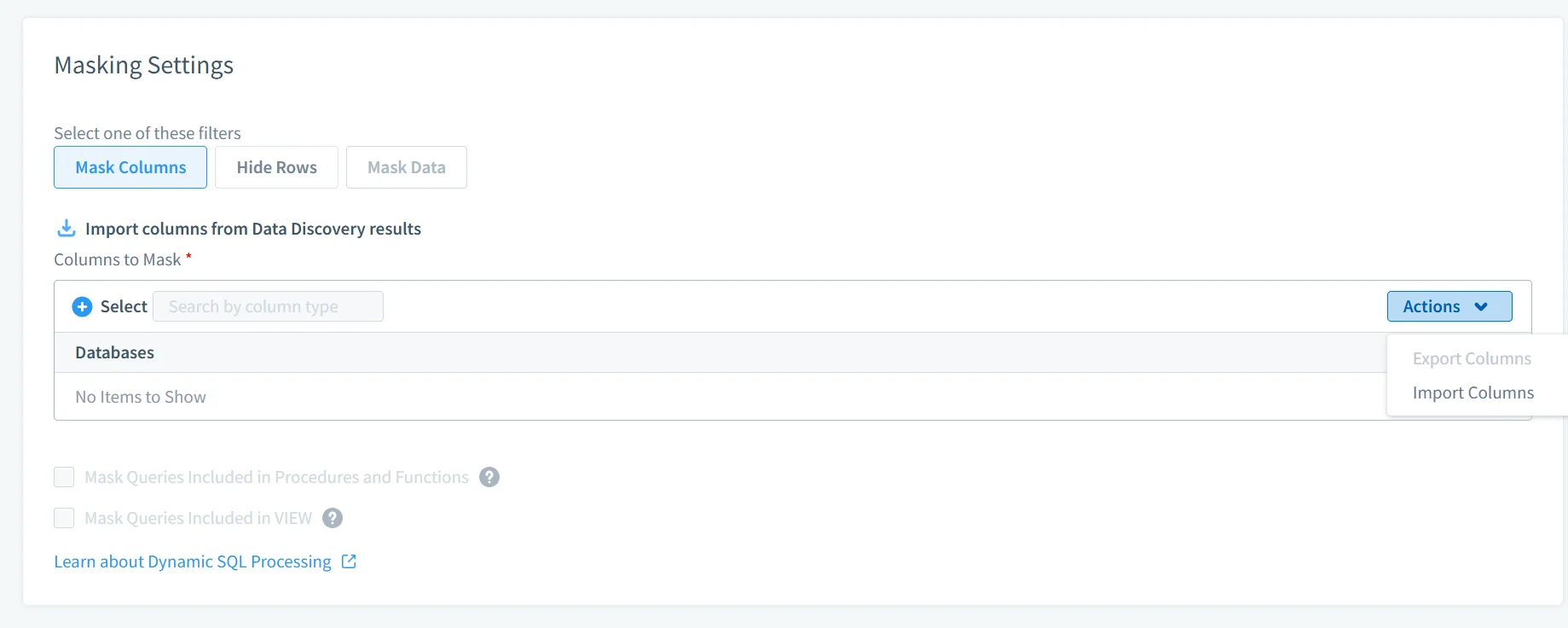
Dynamic Data Masking
Dynamic Data Masking applies real-time transformations to query results based on user roles, access context, and defined policies.
Masking happens at the query interception layer, meaning the original data remains unchanged in the database. Different users can see different versions of the same data depending on their privileges.
This approach ensures that sensitive information is never exposed unnecessarily while maintaining full usability for authorized operations. It also removes the need for views and stored procedures designed solely for masking purposes.
Database Activity Monitoring
Database Activity Monitoring provides full visibility into how sensitive data is accessed, including query details, users, timestamps, and affected objects.
Every interaction with protected data is logged and analyzed in real time. This allows security teams to detect unusual patterns, investigate incidents, and maintain a complete history of data access.
Unlike native logging, which often requires post-processing, monitoring is integrated directly into the protection layer, ensuring that visibility and control operate together.
Database Firewall
The Database Firewall enforces security policies by inspecting and controlling incoming queries before they reach the database.
It can block unauthorized access attempts, restrict dangerous query patterns, and prevent data exfiltration. Policies can be defined based on user roles, query structure, or data sensitivity.
This adds an active protection layer that complements monitoring. Instead of just recording suspicious behavior, the system can stop it in real time.
Compliance Automation
Compliance Automation aligns sensitive data protection with regulatory requirements such as GDPR, HIPAA, PCI DSS, and SOX.
Policies are defined once and applied consistently across environments. The system continuously evaluates data access against compliance rules and generates audit-ready reports.
This reduces manual effort and ensures that protection mechanisms remain aligned with evolving regulatory standards. Instead of reacting to audits, organizations maintain a continuous state of compliance.
Business Impact of Sensitive Data Protection in Sybase
| Impact | Description |
|---|---|
| Reduced Data Exposure | Sensitive data is never returned in raw form to unauthorized users through dynamic data masking |
| Faster Compliance | Policies align automatically with regulatory requirements using compliance automation |
| Lower Operational Overhead | No need to maintain views, procedures, and custom scripts thanks to automated data discovery |
| Centralized Control | All protection rules are managed in one place via a centralized security framework |
| Audit Readiness | Full visibility into data access and usage with database activity monitoring |
Conclusion
Sybase provides strong access control and encryption, but it does not regulate data visibility at query execution.
Native protection methods such as views and stored procedures are difficult to maintain and do not scale in environments that require consistent data security.
A centralized approach to sensitive data protection ensures consistent enforcement, reduces operational overhead, and improves compliance posture through unified security policies.
DataSunrise delivers this through zero-touch masking, automated data discovery, and unified policy enforcement across environments.
If your current setup depends on developers remembering which view to use, that’s not protection. That’s a liability.
Protect Your Data with DataSunrise
Secure your data across every layer with DataSunrise. Detect threats in real time with Activity Monitoring, Data Masking, and Database Firewall. Enforce Data Compliance, discover sensitive data, and protect workloads across 50+ supported cloud, on-prem, and AI system data source integrations.
Start protecting your critical data today
Request a Demo Download Now
