
Amazon Aurora MySQL Audit Log

Auditing is essential when managing sensitive data in cloud databases. Whether you're bound by compliance regulations or simply want better visibility into who is doing what with your data, enabling the Amazon Aurora MySQL Audit Log gives you that crucial trail — as explained in the DataSunrise overview on audit goals.
This article explores the Amazon Aurora MySQL Audit Log, focusing on native audit options and extending those capabilities with DataSunrise. If you're handling regulated data or investigating anomalies, this guide will help you set up and manage audit logs effectively.
To begin, it's helpful to review the Aurora MySQL auditing documentation and the general MySQL support in RDS. If your audit logs are used to meet compliance goals, consider exploring DataSunrise's Compliance Manager.
Native Amazon Aurora MySQL Audit Log Options
Amazon Aurora MySQL supports audit logging using the MariaDB Audit Plugin, a native method to monitor activity and generate logs you can send to CloudWatch or access via the RDS console. DataSunrise provides a clear explanation in its article on audit logs.
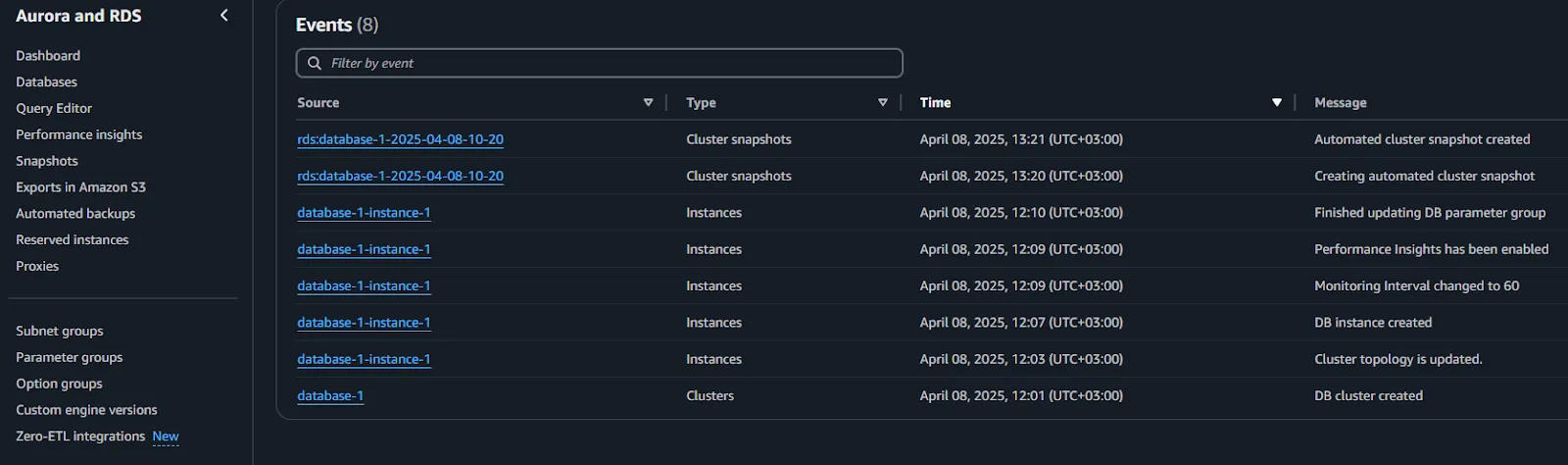
Enabling Audit Logs
To begin, modify your DB cluster parameter group and enable the SERVER_AUDIT_EVENTS and SERVER_AUDIT_LOGGING parameters. Commonly tracked events include CONNECT, QUERY, and TABLE. The logs are stored with other database logs, and you can export them for long-term analysis. Full details are available in the AWS documentation.
Here’s an example of how to configure audit logging using SQL:
-- Enable audit logging globally
CALL mysql.rds_set_configuration('server_audit_logging', 'ON');
-- Specify which events to log: CONNECT, QUERY, TABLE
CALL mysql.rds_set_configuration('server_audit_events', 'CONNECT,QUERY,TABLE');
-- Exclude system users from auditing (optional)
CALL mysql.rds_set_configuration('server_audit_excl_users', 'rdsadmin');
-- Include specific application user(s) for auditing
CALL mysql.rds_set_configuration('server_audit_incl_users', 'app_user');
This configuration enables logging for selected users and specific event types, helping reduce noise and improve focus on critical database actions. Full details are available in the AWS documentation.
For setup instructions, refer to the Aurora audit guide. Planning for storage is equally important—check out DataSunrise’s audit storage performance guide.
Where the Logs Go
Logs are stored alongside general logs and slow query logs. You can access them via the RDS console, AWS CLI, or API. In production environments working with sensitive data, routing logs to CloudWatch improves alerting and retention. Learn more about protecting this data in the DataSunrise Data Security guide.
If your logs aren't appearing, AWS provides a helpful troubleshooting resource.
Using DataSunrise with Amazon Aurora MySQL Audit Log
While the native plugin logs key events, it lacks filtering, masking, and smart analytics. That’s where DataSunrise enhances functionality, particularly in compliance-heavy environments. You can read more in their article on data-inspired security.
How DataSunrise Integrates with Aurora
To connect DataSunrise to Aurora:
Deploy it in reverse proxy mode between your app and Aurora.
Use DB credentials to establish the link.
Create audit rules for users, IPs, SQL types, and access times. A guide on reverse proxy configuration is available for setup help.

DataSunrise supports Aurora as part of over 40 compatible platforms, detailed in their supported databases list.
Defining Custom Audit Rules
Inside the DataSunrise dashboard:
Navigate to Audit, then add a rule.
Select operations (e.g.
SELECT,INSERT) on tables with sensitive data.Tailor triggers by user, time, or query type. The learning rules guide covers how to build effective filters.
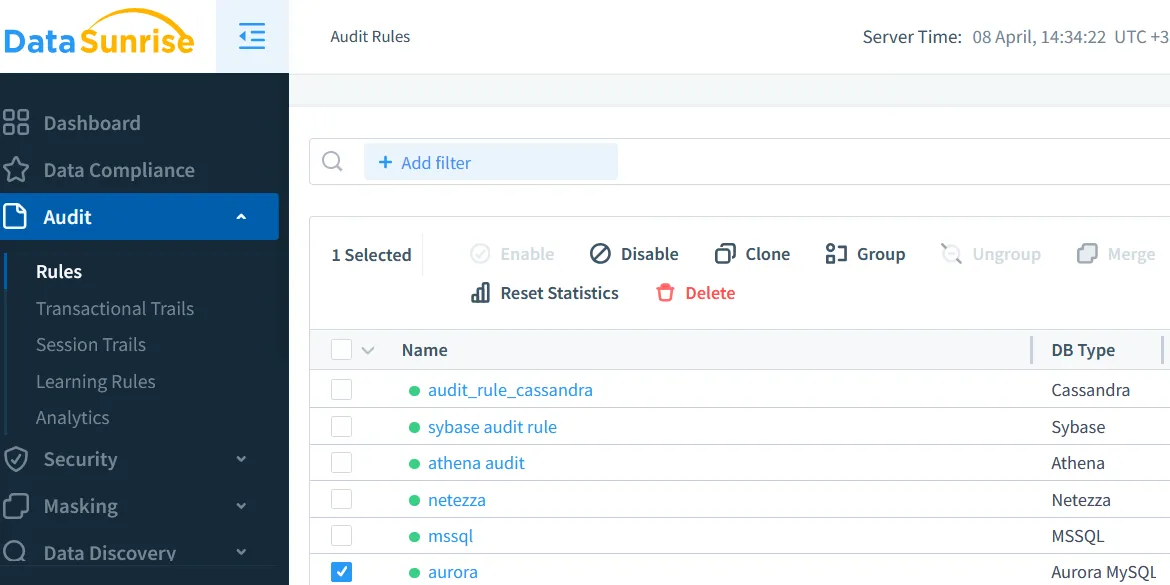
You can also refine the logging scope by setting audit rule priority.
Managing and Exporting Logs in DataSunrise
Audit logs can be stored locally or sent to SIEM tools. Filters and dashboards make it easy to view patterns, and you can export logs in CSV or JSON formats. Refer to the report generation guide for more.
DataSunrise also offers automated compliance reporting for GDPR, HIPAA, and PCI DSS. These features complement tools like historical activity tracking.
Benefits of Combining Native and DataSunrise Logs
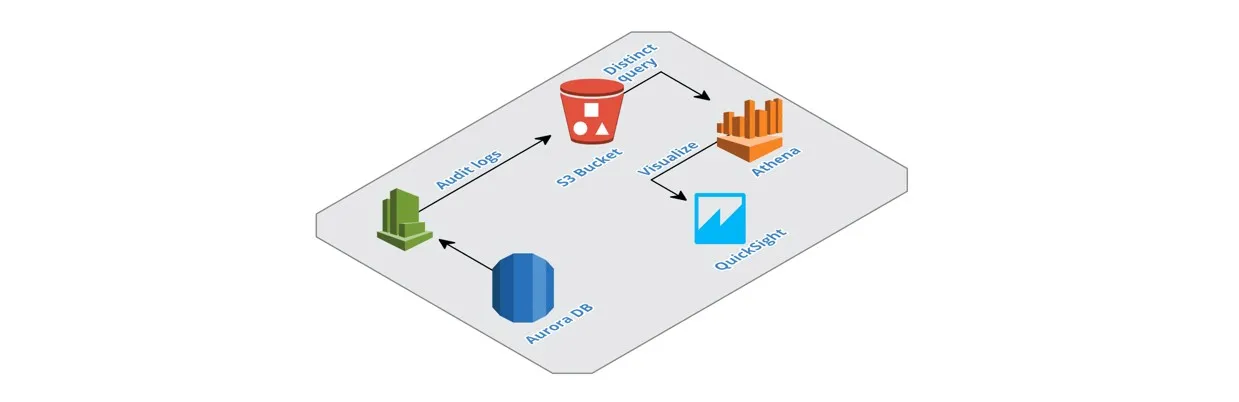
Native Aurora audit logs offer built-in reliability, while DataSunrise brings extended controls. Together, you benefit from detailed engine-level tracking plus smart real-time filtering and analytics. Read about this hybrid approach in the database activity monitoring guide.
| Feature | Aurora Native Audit Logs | DataSunrise Audit Logs |
|---|---|---|
| Audit Scope | Tracks SQL statements like SELECT, DDL, DCL; limited granularity | Tracks queries, responses, object-level activity, and access context |
| Real-Time Monitoring | Limited to log streaming to CloudWatch | Yes, with instant alerting and rule-based actions |
| Configuration Flexibility | Set via parameter groups; system-wide settings | Fine-grained rules per user, role, query type, table, column |
| Compliance Reports | Manual report extraction from logs | Built-in report engine with scheduling and filtering |
| Data Masking | Not supported | Supports dynamic and static masking |
| Storage Options | Stored in CloudWatch or local log files | Customizable: database, file system, SIEM integration |
If you're handling personal data, explore dynamic masking and role-based access control options for additional protection.
Conclusion
Auditing your Amazon Aurora MySQL setup helps meet both internal and external data governance standards. Start with the native plugin, then scale with DataSunrise for broader auditing and masking capabilities. You can also explore a live demo of DataSunrise to see these features in action.
For further learning, explore the Data Audit overview, their insights on treating data as a valuable asset, and see how AWS handles data masking via DMS.
