Data Obfuscation in IBM Db2
As organizations manage growing volumes of sensitive information, data obfuscation has become a cornerstone of modern database security. According to IBM's 2024 Cost of a Data Breach Report, the average breach cost reached $4.88 million — a record high — making proper data protection controls an urgent priority for IBM Db2 deployments. You can explore Db2's full security feature set in the IBM Db2 documentation.
This article covers Db2's native obfuscation capabilities and shows how DataSunrise can extend them with enterprise-grade, automated protection.
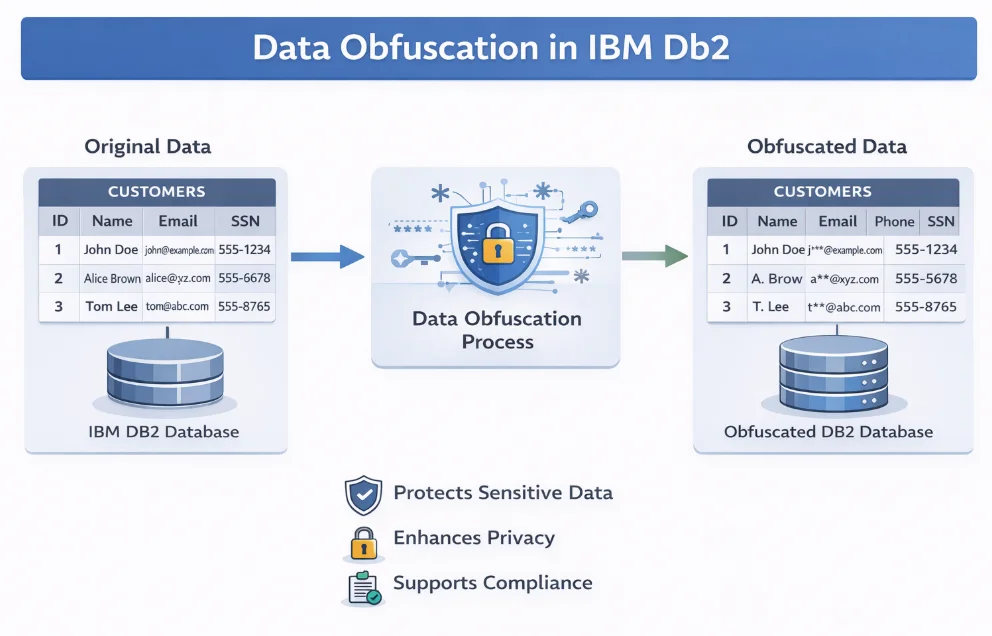
What Is Data Obfuscation in IBM Db2?
Data obfuscation transforms sensitive information into realistic but fictitious substitutes — preserving application functionality while eliminating exposure risk. Unlike database encryption, obfuscation maintains referential integrity and remains transparent to applications. IBM Db2 supports it through Row and Column Access Control (RCAC), role-based access controls, and dynamic data masking.
Native IBM Db2 Data Obfuscation Capabilities
Enable Row and Column Access Control (RCAC)
Before applying masks, activate RCAC on the target table. Properly scoping access controls at this level is the foundation of any Db2 obfuscation strategy:
ALTER TABLE hr.employees ACTIVATE ROW ACCESS CONTROL;
ALTER TABLE hr.employees ACTIVATE COLUMN ACCESS CONTROL;
Create Column Masks for Data Obfuscation
Column masks define how field values are presented based on user role. In the example below, SSNs are partially masked for anyone outside the HR_ADMIN role:
CREATE MASK ssn_mask ON hr.employees
FOR COLUMN ssn
RETURN
CASE
WHEN VERIFY_ROLE_FOR_USER(SESSION_USER, 'HR_ADMIN') = 1
THEN ssn
ELSE 'XXX-XX-' || RIGHT(ssn, 4)
END
ENABLE;
Masks are enforced transparently at query time — no application changes required.
Apply Row Permissions for Context-Aware Access
Row permissions restrict which records different users can retrieve:
CREATE PERMISSION region_access ON hr.employees
FOR ROWS WHERE
VERIFY_GROUP_FOR_USER(SESSION_USER, 'EMEA_STAFF') = 1
AND region = 'EMEA'
OR VERIFY_ROLE_FOR_USER(SESSION_USER, 'GLOBAL_VIEW') = 1
ENFORCED FOR ALL ACCESS
ENABLE;
Test Obfuscation with Sample Queries
Verify masking behavior across different user contexts:
INSERT INTO hr.employees (emp_id, full_name, ssn, salary, region)
VALUES (1001, 'Alice Johnson', '123-45-6789', 85000.00, 'EMEA');
-- As restricted user: SSN returns 'XXX-XX-6789', salary returns NULL
SET SESSION AUTHORIZATION = 'SUPPORT_USER';
SELECT emp_id, full_name, ssn, salary FROM hr.employees;
-- As HR admin: full values visible
SET SESSION AUTHORIZATION = 'HR_ADMIN_USER';
SELECT emp_id, full_name, ssn, salary FROM hr.employees;
Refer to the IBM Db2 RCAC documentation for available mask functions and permission predicates.
Enhanced Data Obfuscation for IBM Db2 with DataSunrise
DataSunrise operates as a transparent proxy layer — intercepting queries in real time and applying masking rules based on user identity, role, application context, and query content, without any changes to your application or schema.
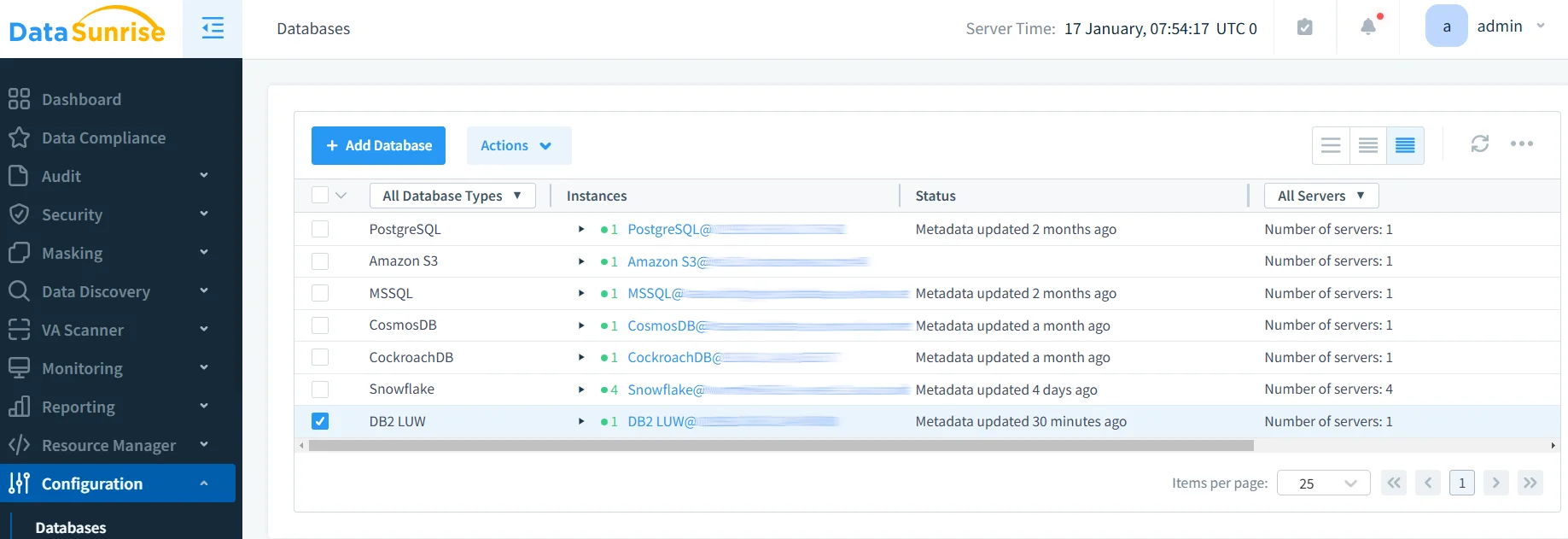
Implementing DataSunrise for IBM Db2 Data Obfuscation
Connect Your Db2 Instance — Register your database in DataSunrise's web interface. A secure proxy connection is established with minimal performance overhead.
Run Sensitive Data Discovery — DataSunrise uses NLP and ML tools to automatically scan schemas via its data discovery engine and classify PII, PHI, and financial data columns — eliminating the manual discovery gap in native Db2 tooling.
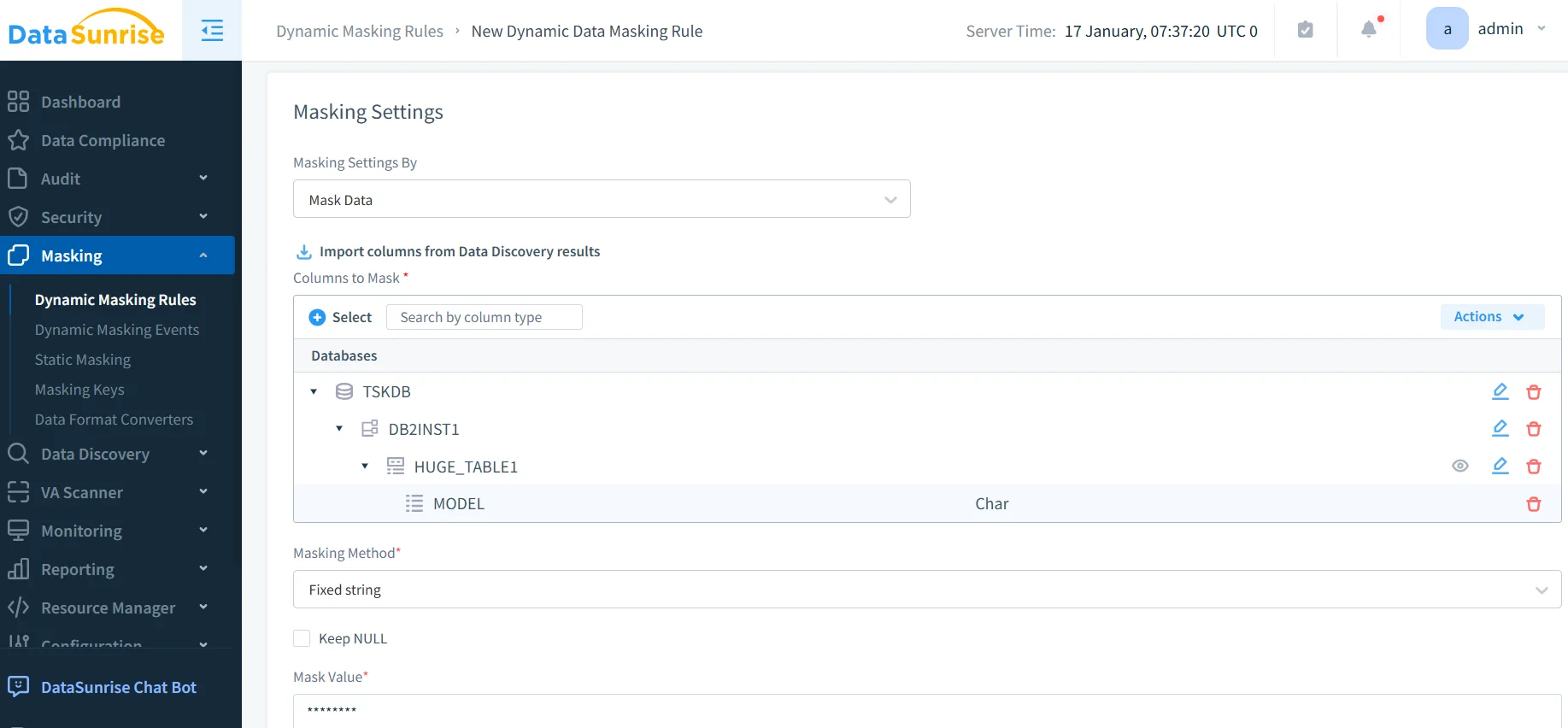
Create Masking Rules — Configure masking rules through a no-code interface: select columns, choose a transformation method (partial mask, nullification, randomization), and define conditions by user role, IP, or time of day.
Test and Validate — Query Db2 through DataSunrise's proxy with different user accounts and review results in the audit logs to confirm correct masking behavior.
Configure Alerts and Compliance Reporting — Enable real-time notifications for suspicious access and schedule automated compliance reports for GDPR, HIPAA, PCI DSS, and SOX.
Key Advantages of DataSunrise for IBM Db2
- Auto-Discover & Classify: Automatically identifies sensitive columns across all Db2 schemas without manual catalog review.
- Dynamic Data Masking: Replaces sensitive values in query results on the fly based on user context, with no application changes needed.
- Static Masking: Permanently obfuscates data in non-production Db2 clones for safe developer and QA use.
- Behavioral Analytics: Detects anomalies such as bulk masked-column downloads or off-hours access before they escalate.
- Automated Compliance: One-click reports aligned to GDPR, HIPAA, PCI DSS, and SOX and other compliance regulations.
- Database Activity Monitoring: Full visibility into who accesses what data, when, and from where — across all connected instances.
- Centralized Management: Unified policy control across 40+ data platforms from a single console.
Business Benefits of Data Obfuscation for IBM Db2
| Benefit | Description |
|---|---|
| Reduced Breach Impact | Obfuscated data has no value to attackers even if exfiltrated |
| Regulatory Compliance | Automated masking policies satisfy GDPR, HIPAA, PCI DSS, and SOX requirements |
| Safe Non-Production Environments | Developers work with realistic but fictitious data, eliminating accidental exposure |
| Insider Threat Mitigation | Role-aware masking ensures users — including DBAs — see only what they're authorized to |
| Operational Efficiency | Automated discovery and no-code policies free security teams from manual configuration |
| Audit Readiness | Timestamped logs and auto-generated reports demonstrate compliance posture on demand |
Conclusion
Db2's native RCAC and LBAC tools provide a solid obfuscation foundation, but manual configuration, absent automated discovery, and per-instance management make them difficult to scale. Enforcing the least privilege principle across a growing database estate requires tooling that goes beyond native capabilities. DataSunrise closes these gaps with autonomous data classification, no-code masking policies, real-time dynamic obfuscation, and automated compliance reporting — available across on-premises, cloud, and hybrid environments.
Protect Your Data with DataSunrise
Secure your data across every layer with DataSunrise. Detect threats in real time with Activity Monitoring, Data Masking, and Database Firewall. Enforce Data Compliance, discover sensitive data, and protect workloads across 50+ supported cloud, on-prem, and AI system data source integrations.
Start protecting your critical data today
Request a Demo Download Now