Data Obfuscation in Sybase
Protecting sensitive data in SAP Sybase ASE requires more than access control and encryption. These mechanisms restrict who can access data, but they do not regulate what portion of data is exposed at query execution time. For a broader view of how access control fits into protection strategies, see Access Controls.
Data obfuscation addresses this gap by transforming sensitive values into protected representations while preserving data structure and usability. This enables controlled access for development, analytics, and third-party integrations without exposing raw data. In many cases, this works alongside techniques such as Data Masking to ensure consistent protection across environments. For a deeper technical comparison between masking and obfuscation approaches, refer to IBM Guardium documentation and NIST guidelines on protecting PII.
As shown in the provided material, Sybase does not natively support centralized or real-time obfuscation. Therefore, organizations rely on custom SQL-based techniques, which introduce operational complexity and inconsistent enforcement.
What is Data Obfuscation in Sybase
Data obfuscation in SAP Sybase ASE is a transformation technique used to protect sensitive information by modifying data values while preserving their structure, format, and relational integrity. This allows systems and users to continue working with realistic datasets without exposing actual confidential content.
Unlike encryption, which completely restricts access to data unless it is decrypted, obfuscation provides controlled visibility. Users can still query and process data, but sensitive elements are transformed based on defined rules and context. In many implementations, this works alongside broader data security strategies to ensure consistent protection across environments.
This approach is commonly applied in non-production environments such as development and testing, where realistic datasets are required but real data must not be exposed. It is also widely used in analytics and reporting scenarios, where data insights are needed without revealing personally identifiable information. In addition, organizations use obfuscation to safely provide limited data access to third parties or external systems, often in combination with role-based access control to enforce context-aware visibility.
Several techniques are typically used to implement data obfuscation. Substitution replaces original values with synthetic equivalents that follow the same format. Masking partially or fully hides sensitive fields. Tokenization maps real values to surrogate tokens stored separately, while shuffling rearranges data within a dataset to break direct associations. These techniques are closely related to dynamic data masking, which applies transformations in real time.
The primary objective of data obfuscation is to preserve data usability while eliminating the risk of sensitive data exposure.
Native Data Obfuscation Techniques in Sybase
SAP Sybase ASE does not provide built-in data obfuscation capabilities. As a result, organizations implement protection mechanisms using standard SQL constructs. These approaches operate at the query or data layer but lack centralized enforcement and scalability.
Views with Column-Level Transformation
One of the most common approaches is to create views that transform sensitive columns during query execution.
CREATE VIEW masked_customers AS
SELECT
id,
LEFT(email, 2) + '***@***.com' AS email,
'REDACTED' AS phone
FROM customers;
This method applies obfuscation logic directly in the SELECT statement. It operates at the query layer, meaning that sensitive data is transformed only when accessed through the view. However, it requires users to explicitly query the view instead of the base table. Additionally, it does not enforce protection outside the view, so direct access to underlying tables bypasses the obfuscation entirely.
Stored Procedures for Controlled Access
Another approach involves encapsulating obfuscation logic within stored procedures.
CREATE PROCEDURE get_masked_data
AS
BEGIN
SELECT
id,
'XXXX-XXXX-XXXX-' + RIGHT(card_number, 4) AS card_number
FROM payments;
END;
Stored procedures provide a controlled execution path by restricting how queries are executed. This allows administrators to define specific transformations and expose only masked results through predefined interfaces.
However, this method does not prevent users from executing direct queries against base tables if they have sufficient permissions. Over time, maintaining multiple procedures with embedded logic increases complexity and operational overhead.
Data Substitution via ETL Processes
For non-production environments, organizations often apply static data substitution through ETL or batch updates.
UPDATE customers SET email = 'user' + CAST(id AS VARCHAR) + '@example.com';
This approach replaces sensitive values with synthetic data, making it suitable for testing and development use cases. It is commonly used when production data must be replicated in a sanitized form.
Despite its simplicity, this method introduces several limitations. The transformation is irreversible, meaning original data cannot be restored. It requires maintaining duplicate datasets, which increases storage and management overhead. Additionally, it cannot support real-time scenarios, as changes are applied only during batch processing.
Centralized Data Obfuscation with DataSunrise
DataSunrise introduces a proxy-based architecture that externalizes data protection logic from the database engine. Instead of embedding obfuscation rules inside SQL code, all policies are enforced at the data access layer. This ensures that every query is inspected, evaluated against defined security policies, and transformed before results are returned to the client.
This architecture removes the need for application changes, schema modifications, or custom SQL implementations. As a result, organizations achieve consistent and enforceable data protection across all access paths, including direct database connections, BI tools, and application-level queries. It also reduces reliance on development teams by shifting data protection into a centralized control layer.
Sensitive Data Discovery
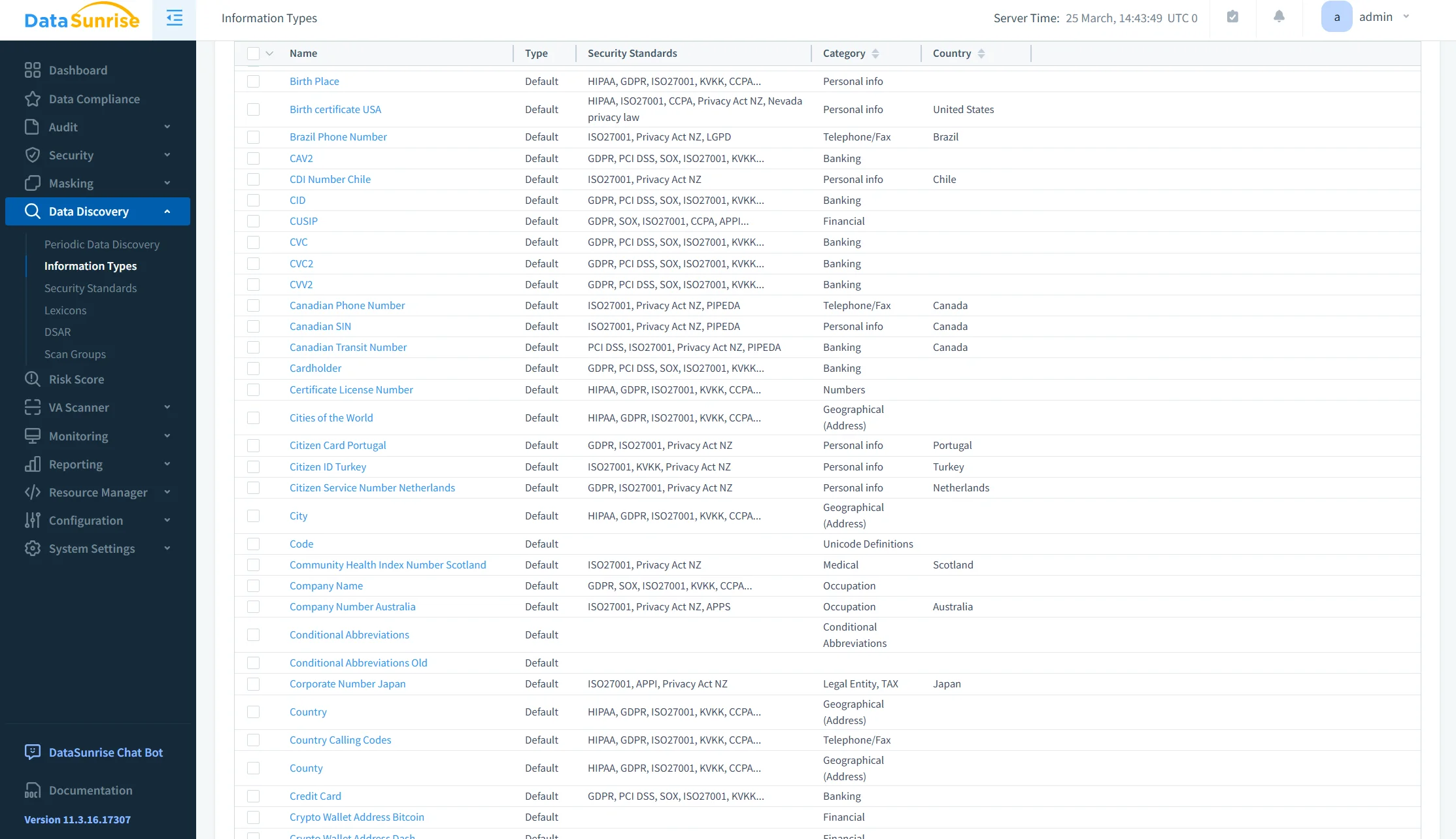
Data Discovery automatically scans databases to identify sensitive data. It supports both structured and semi-structured sources and applies pattern matching, dictionaries, and contextual analysis to detect personally identifiable information, financial data, and credentials.
The discovery process can run on a scheduled basis or continuously, allowing detection of newly introduced sensitive fields. This approach removes the need for manual classification, reduces the likelihood of human error, and provides complete visibility into sensitive data assets across environments.
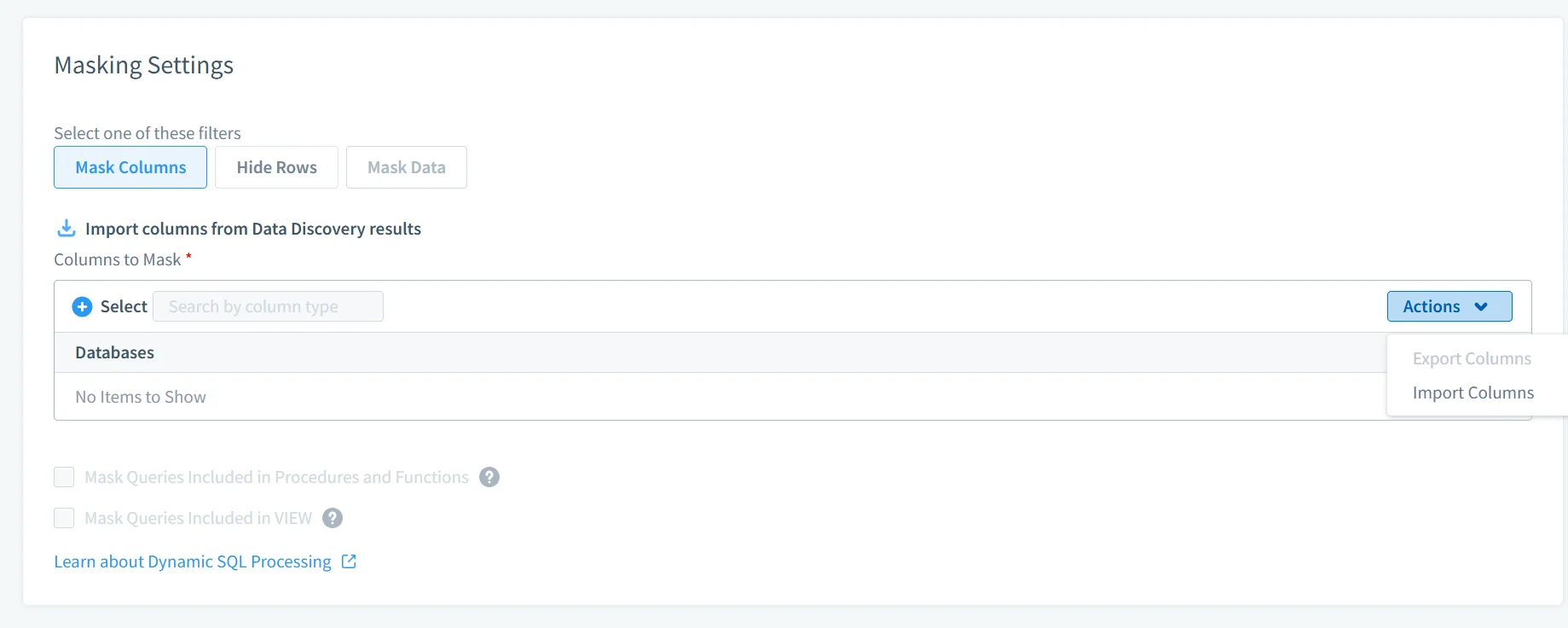
Dynamic Data Masking
Dynamic Data Masking applies obfuscation at runtime. Policies are defined based on contextual attributes such as user roles, query context, source IP address, or application type.
Masking rules are evaluated in real time for each query. This ensures that different users receive different representations of the same dataset. For example, privileged users may access full data, while other users receive masked or partially obfuscated values. This enables granular access control without duplicating datasets or modifying application logic.
Database Activity Monitoring
Database Activity Monitoring provides full visibility into database interactions. Every query, including those involving obfuscated data, is logged, analyzed, and correlated with user identity and session context.
This capability supports detection of unauthorized access attempts, monitoring of sensitive data usage, and generation of audit trails required for compliance. Collected activity data can also be used for forensic investigations, anomaly detection, and integration with external monitoring or SIEM systems.
Compliance Enforcement
Compliance Manager automates alignment with regulatory frameworks such as GDPR, HIPAA, PCI DSS, and SOX. Security policies are mapped to regulatory requirements and enforced consistently across all monitored databases.
This reduces manual compliance efforts and ensures that protection mechanisms remain aligned with regulatory expectations. Automated reporting further simplifies audit preparation by providing verifiable records of access control, masking policies, and user activity.
Deployment and Integration
DataSunrise supports deployment across on-premises environments, cloud platforms, and hybrid infrastructures. It can operate in proxy, sniffer, or log-based modes, depending on performance and security requirements.
Because the platform functions independently of the database engine, it integrates into existing architectures without requiring redesign or downtime. This makes it suitable for complex, heterogeneous environments where multiple databases, access channels, and user roles must be managed under a unified security framework.
Business Impact of Data Obfuscation in Sybase
| Impact | Description |
|---|---|
| Reduced Data Exposure | Sensitive data is never returned in raw form, supported by dynamic data masking |
| Compliance Enablement | Aligns with GDPR, HIPAA, PCI DSS requirements through data compliance frameworks |
| Operational Efficiency | Eliminates custom SQL-based masking logic using centralized data masking approaches |
| Centralized Governance | Unified control across environments via data security policies |
| Audit Visibility | Full traceability of data access through logging, monitoring, and audit mechanisms |
Conclusion
SAP Sybase ASE provides robust access control and encryption mechanisms. However, it does not regulate data visibility at query execution. To address this limitation, organizations typically combine native controls with additional layers such as database security solutions.
Native obfuscation techniques—views, stored procedures, and ETL-based substitution—introduce fragmentation and lack enforceability. These approaches often rely on manual implementation and do not integrate well with broader data security strategies.
A centralized approach is required to ensure consistent protection.
DataSunrise implements policy-driven data obfuscation as an external control layer, enabling real-time enforcement, automated compliance alignment, and unified governance across environments. It integrates with capabilities such as database activity monitoring and compliance manager to provide full visibility and control.
This reduces operational overhead while improving security posture and audit readiness.
Protect Your Data with DataSunrise
Secure your data across every layer with DataSunrise. Detect threats in real time with Activity Monitoring, Data Masking, and Database Firewall. Enforce Data Compliance, discover sensitive data, and protect workloads across 50+ supported cloud, on-prem, and AI system data source integrations.
Start protecting your critical data today
Request a Demo Download Now
