Dynamic Data Masking in TiDB
TiDB handles scalable SQL workloads, high concurrency, and production-grade analytics, which is exactly why teams point multiple tools, users, and service accounts at the same live dataset. Convenient? Sure. Safe by default? Not even close. The moment analysts, contractors, BI platforms, or support engineers can run direct queries, sensitive values can spill into dashboards, exports, and logs.
That is where data masking helps, and where dynamic data masking makes the most sense for production environments. Instead of changing source records, dynamic masking transforms query results on the fly, so the database stays intact while each user sees only the level of detail they are allowed to access. Combined with data discovery and classification of PII, it gives security teams a practical way to reduce exposure without wrecking operational access.
If you want the official product and architecture background, the TiDB GitHub repository and product documentation provide the platform context. What matters here is simple: TiDB is fast, flexible, and very good at serving data; your job is to make sure it does not serve the wrong data to the wrong people.
Why dynamic masking matters in TiDB
Dynamic masking matters in TiDB because production clusters often support more than application traffic. Reporting tools, internal admin panels, data science notebooks, and troubleshooting sessions all compete for direct SQL access. That creates a familiar mess: users may need access to tables, but they do not need the raw contents of every field.
Strong access controls help, but access alone does not solve the whole problem. A user may legitimately query a customer table and still have no business seeing full card numbers, personal phone numbers, or national identifiers. That is why dynamic masking complements role-based access control and the principle of least privilege: permissions answer “can this user query the object?” while masking answers “what should this user actually see?”
Start with the fields that create the biggest operational and compliance risk—email, phone, national identifiers, payment data, and address information—then validate the masked output in real dashboards and SQL clients before you expand the policy to more schemas.
How dynamic data masking works in practice
In a typical deployment, DataSunrise acts as a policy enforcement layer between the client and the database, with several supported deployment modes depending on your environment. A user sends a query to TiDB, DataSunrise evaluates the request against masking rules, and then returns a transformed result set. TiDB keeps the original values unchanged. That distinction matters because it lets you protect production visibility without modifying the underlying records.
The control becomes even more valuable when you pair it with database activity monitoring and a well-maintained audit trail. In other words, you do not just hide sensitive data—you also record who requested it, where the request came from, and which rule masked the result. That is the difference between “we think we protected it” and “we can prove we did.”

Building a TiDB dynamic masking rule in DataSunrise
The first step is straightforward: create a new masking rule, choose TiDB as the database type, and attach the target instance. Then define the rule name, add optional comments, and choose the action settings that control how DataSunrise handles requests. In the screenshot above, the rule uses auditing, which is exactly what you want in a production rollout because it creates traceable events in audit logs.
Next comes the part where people either make a smart choice or create a total clown show: selecting the actual columns to mask. Dynamic masking works best when you apply it intentionally to high-value sensitive fields instead of spraying it across an entire schema with zero thought. Review the data model, identify regulated fields, and map the exposure risk to actual business roles.
For TiDB environments that store customer or employee records, typical candidates include:
- Full name
- Email address
- Phone number
- National ID or tax ID
- Payment card fields
- Address data
- Free-text notes that may contain sensitive fragments
These choices are rarely just technical—they come from compliance regulations, internal security policies, and plain common sense. If a reporting role only needs customer trends, showing the full card number is not analytics; it is negligence dressed up as convenience.

Choosing the right masking strategy for live TiDB queries
Not every column needs the same masking behavior. Some values need full redaction, while others can keep limited business utility. Email can be partially masked, phone numbers can show only the last four digits, and card data can use a fixed pattern that preserves the format without exposing the original value.
The point is not to make data look pretty. The point is to make it safe and still useful. Security teams often combine dynamic masking with a database firewall and defensive security rules against SQL injections so that suspicious or abusive traffic does not turn a perfectly normal query path into a leak factory. Because obviously some people cannot be trusted to behave like civilized adults around production data.
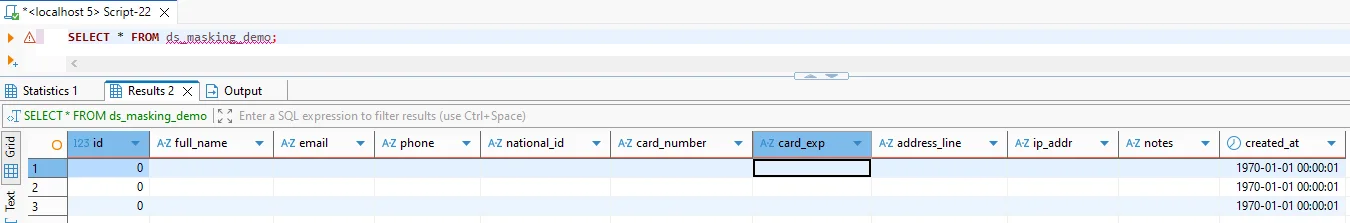
A basic test query in TiDB might look like this:
SELECT
id,
full_name,
email,
phone,
national_id,
card_number,
address_line,
notes,
created_at
FROM ds_masking_demo;
Privileged users may still see full values. Restricted users see masked results according to policy. You do not need to copy the table, and you do not need to rewrite the application. That is the elegance of dynamic masking: same data source, same query shape, different visibility based on who asks.
Masking the wrong columns can break reporting, support workflows, or application logic if downstream users expect raw values for filtering, exports, or reconciliation. Test service accounts, BI dashboards, saved queries, and admin roles before you enforce rules broadly in production.
Dynamic masking versus static masking in TiDB
Dynamic masking is the right choice when you need to protect live data access in production. It does not alter the source table, and it works at query time. That makes it ideal for support teams, analysts, third-party access, and operational users who need some visibility but not the raw secrets.
It is not the same as static data masking, which teams usually use to create sanitized non-production copies, and it is definitely not the same as in-place masking, where the source data itself changes. If your goal is a safe development or QA dataset, static masking makes more sense. If your goal is controlled access to production data without duplication, dynamic masking is the sharper tool.
Best practices for rolling out dynamic masking in TiDB
First, discover before you protect. You cannot reliably mask what you have not classified. Use discovery results to identify columns that carry personal, financial, or otherwise confidential data. Then build rules around real roles and business processes instead of fantasy architecture diagrams that nobody follows after kickoff.
Second, define policies by context. A finance analyst, customer support engineer, outsourced vendor, and DBA should not see the same representation of the same row. Good masking rules use role, application, source IP, and environment to decide what gets exposed. If your data estate extends beyond TiDB, that consistency gets much easier when your tooling supports 40+ data platforms rather than turning each new database into a fresh governance headache.
Third, keep evidence. A masking policy that cannot prove itself during an incident review or audit season is just security theater with extra screenshots. The audit guide and security guide help when you want to operationalize masking, logging, monitoring, and rule governance as part of a broader data protection program.
Compliance value of dynamic masking in TiDB
Dynamic masking is not just a neat technical trick. It directly supports data minimization and controlled disclosure across regulated workloads. When a production TiDB cluster contains customer, patient, payment, or financial records, reducing unnecessary exposure becomes part of routine governance rather than an optional hardening exercise.
That is why dynamic masking maps naturally to requirements under major frameworks and often works alongside reporting and evidence collection in Compliance Manager.
| Regulation | Why masking matters in TiDB | Control objective |
|---|---|---|
| GDPR | Limit exposure of personal data in analytics, operations, and support workflows | Data minimization and controlled access |
| HIPAA | Reduce visibility of protected health information for non-clinical or support roles | Safeguard sensitive healthcare data |
| PCI DSS | Prevent unnecessary display of payment card data in production query results | Restrict cardholder data exposure |
| SOX | Control access to financial records while preserving traceability and accountability | Support governance and audit readiness |
Conclusion: dynamic protection for live TiDB workloads
Dynamic data masking in TiDB solves a painfully common problem: people need access to live data, but they do not need the full truth of every field. With DataSunrise, you can define masking policies by role and context, keep the underlying TiDB records unchanged, monitor what users request, and generate evidence that shows the controls are working. That is a much better outcome than trusting every direct SQL consumer to act wise, careful, and not disastrously curious.
For organizations running TiDB in production, dynamic masking is one of the cleanest ways to balance usability, security, and compliance. Done properly, it protects sensitive results without crippling analytics, support operations, or administrative workflows. That is the whole game: keep the data useful, keep exposure down, and stop pretending raw production access is harmless.
Protect Your Data with DataSunrise
Secure your data across every layer with DataSunrise. Detect threats in real time with Activity Monitoring, Data Masking, and Database Firewall. Enforce Data Compliance, discover sensitive data, and protect workloads across 50+ supported cloud, on-prem, and AI system data source integrations.
Start protecting your critical data today
Request a Demo Download Now