How to Apply Dynamic Masking in ScyllaDB
Modern NoSQL platforms like ScyllaDB are built for speed, scale, and massive throughput. However, performance alone does not protect sensitive information. When applications query production tables that contain personal data, financial identifiers, or health records, access control alone is not enough.
Dynamic masking in ScyllaDB becomes essential when organizations must enforce Zero-Trust Data Access while preserving application functionality. Instead of blocking queries, dynamic masking transforms sensitive values at query runtime based on user roles, policies, or context. To better understand how runtime protection works, review the fundamentals of dynamic data masking and how it fits into a broader data security strategy.
ScyllaDB does not provide native column-level dynamic masking. Therefore, organizations that need runtime protection aligned with regulations such as GDPR, HIPAA, and PCI DSS must implement an external enforcement layer capable of delivering context-aware masking without disrupting performance.
What is Dynamic Masking
Dynamic masking is a runtime data protection technique that alters sensitive values in query results without modifying the original data stored in the database. The data remains intact in ScyllaDB, but users see only the information they are authorized to access.
Instead of blocking queries, dynamic masking evaluates predefined security policies when a request is executed. Based on user role, access level, or context, the system transforms sensitive fields before returning results to the client. This approach is a core component of modern data security strategies and helps organizations enforce granular access controls without disrupting operations.
For example, a database may store a full credit card number, but an analyst might see only the last four digits. A support engineer may see partially hidden email addresses. An administrator, however, may see the complete value. The stored record never changes — only the returned output differs.
Dynamic masking differs from encryption and static masking. Encryption protects data at rest or in transit but reveals full values after decryption. Static masking permanently alters copied datasets, usually for testing environments. Dynamic masking, in contrast, operates in real time and preserves production integrity. A deeper technical explanation of masking models is available in this overview of dynamic data masking.
In high-throughput environments like ScyllaDB, dynamic masking enables granular visibility control without affecting database performance, schema structure, or application logic. When combined with proper access controls, it significantly reduces the risk of unnecessary exposure of sensitive information while maintaining full application functionality.
Native Security Capabilities in ScyllaDB
ScyllaDB inherits much of its security architecture from Apache Cassandra. While it delivers strong foundational controls, these mechanisms primarily focus on access restriction and transport protection rather than granular data visibility.
Below is a breakdown of the core native capabilities.
Role-Based Access Control (RBAC)
ScyllaDB implements Role-Based Access Control to define which users can access specific keyspaces, tables, and functions. Permissions such as SELECT, MODIFY, CREATE, and ALTER are assigned to roles, and users inherit privileges through role membership.
Example role and permission configuration:
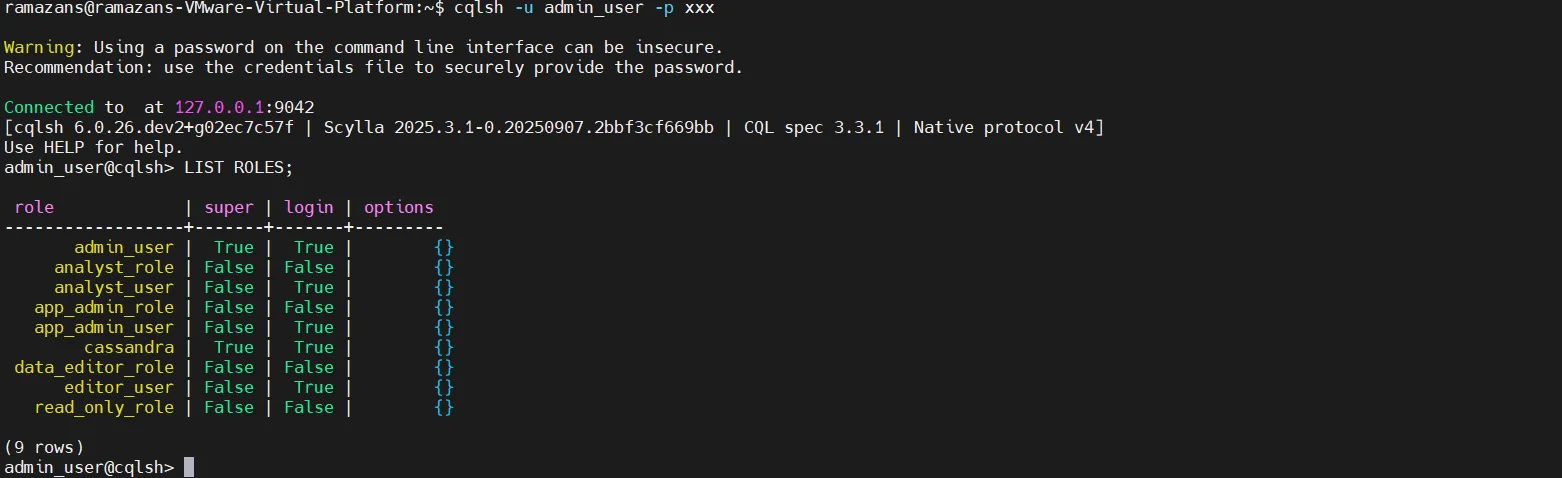
RBAC enforces object-level boundaries. It determines whether a user can execute a query against a table or perform schema changes. This model aligns with the Principle of Least Privilege and provides structured permission management across distributed clusters.
However, RBAC does not control column-level data exposure at runtime. If a user has permission to query a table, full column values are returned:
SELECT credit_card_number FROM customers;
If access is granted, the full value is returned without masking.
Authentication (Password / LDAP Integration)
ScyllaDB supports internal password-based authentication as well as integration with external identity providers such as LDAP. Authentication verifies user identity before access is granted to database resources.
Enable password authentication in configuration:
authenticator: PasswordAuthenticator
authorizer: CassandraAuthorizer
Example user creation:
CREATE ROLE app_user
WITH PASSWORD = 'AppUserPass!'
AND LOGIN = true;
For LDAP integration, ScyllaDB can be configured to delegate authentication to an external directory service:
authenticator: com.scylladb.auth.LDAPAuthenticator
ldap_server: ldap://ldap.company.local
ldap_search_dn: cn=admin,dc=company,dc=local
Authentication ensures that only verified users can initiate sessions, but it does not control how returned data is displayed once access is granted.
TLS Encryption in Transit
ScyllaDB supports TLS encryption to secure communication between client and database nodes, as well as inter-node cluster communication.
Example client-to-node encryption configuration:
client_encryption_options:
enabled: true
certificate: /etc/scylla/ssl/node.crt
keyfile: /etc/scylla/ssl/node.key
truststore: /etc/scylla/ssl/ca.crt
Example inter-node encryption configuration:
server_encryption_options:
internode_encryption: all
certificate: /etc/scylla/ssl/node.crt
keyfile: /etc/scylla/ssl/node.key
truststore: /etc/scylla/ssl/ca.crt
TLS protects data in transit by encrypting network traffic, preventing interception or man-in-the-middle attacks. This is essential for compliance with security frameworks that require secure transmission of sensitive information.
Encryption in transit protects data movement but does not prevent authorized users from viewing full sensitive values once decrypted during query execution.
Audit Logging (Enterprise Edition)
ScyllaDB Enterprise includes audit logging capabilities that record database activities such as authentication attempts, query execution, schema modifications, and administrative actions.
Example audit configuration in scylla.yaml:
audit: "table"
audit_categories: "AUTH,DDL,DML"
audit_keyspaces: "finance,hr"
Audit logs can capture events such as:
CREATE TABLE customers (id UUID PRIMARY KEY, name text);
INSERT INTO customers (id, name)
VALUES (uuid(), 'John Doe');
SELECT * FROM customers;
Each action is recorded in the audit log with metadata such as user, timestamp, and operation type.
Audit logs help organizations track database activity, investigate incidents, and demonstrate compliance during regulatory reviews.
While audit logging improves visibility and accountability, it operates after access occurs. It records activity but does not enforce runtime protection or restrict sensitive data exposure within query results.
Applying Dynamic Masking in ScyllaDB with DataSunrise
DataSunrise delivers Zero-Touch Data Masking for ScyllaDB through a non-intrusive proxy architecture. Instead of modifying database schemas or rewriting applications, it operates at the database communication layer, enforcing Context-Aware Protection in real time. This approach is part of the broader DataSunrise security framework, designed to extend advanced protection to modern database environments.
Below are the core capabilities that enable dynamic masking in ScyllaDB environments.
Non-Intrusive Proxy Architecture
DataSunrise integrates with ScyllaDB using proxy mode, which allows traffic inspection and policy enforcement without altering the underlying database configuration. This architecture requires no schema changes, does not modify stored records, avoids application-level code adjustments, and preserves cluster performance and scalability.
Deployment flexibility is supported through multiple deployment modes, including on-premise environments, AWS, Microsoft Azure, Google Cloud Platform, and hybrid infrastructures. This ensures Seamless Multi-Environment Coverage across distributed and heterogeneous environments while maintaining operational stability.
The proxy model also complements advanced controls such as Database Firewall capabilities for real-time traffic inspection and enforcement.
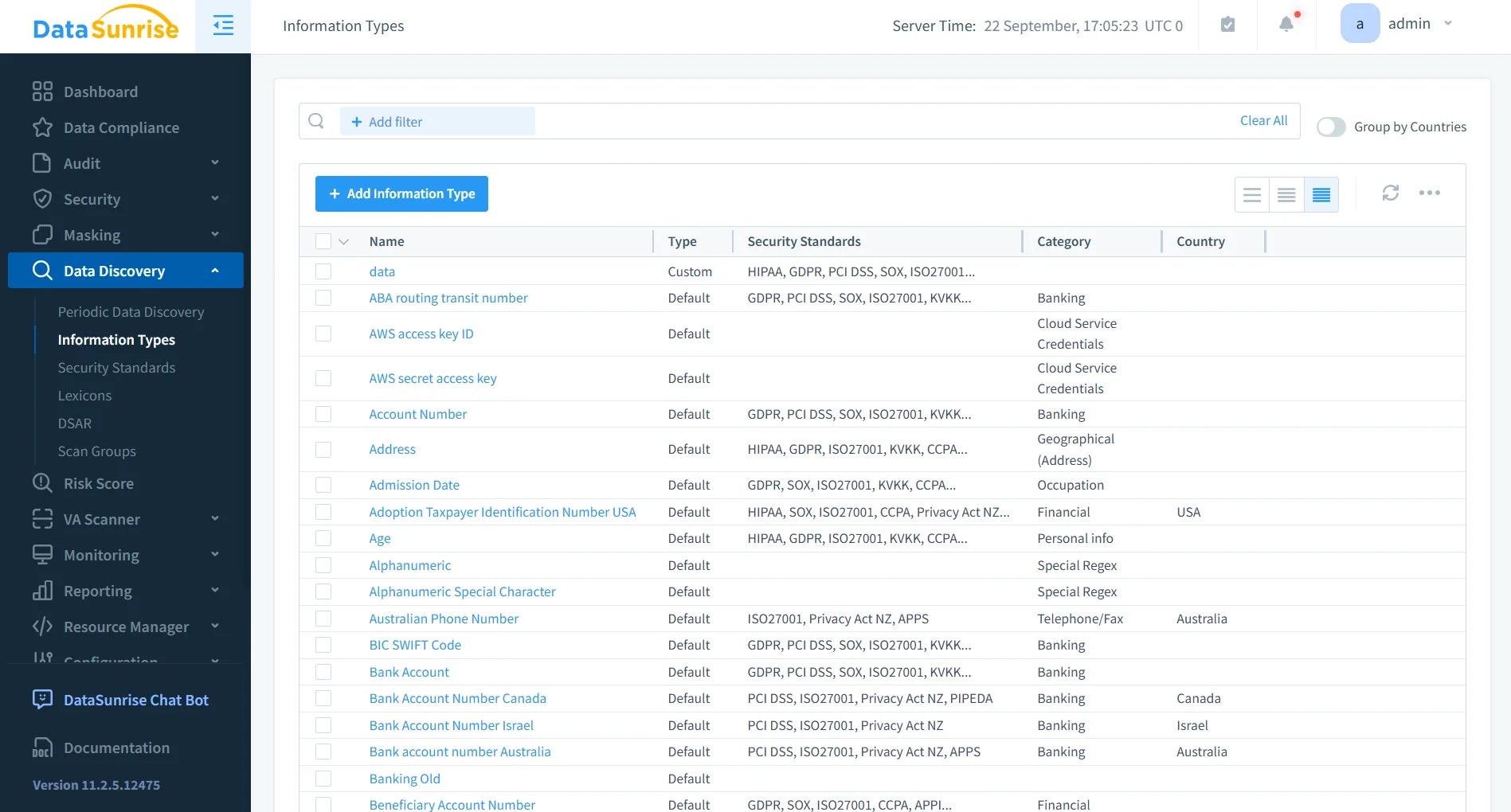
Automated Sensitive Data Discovery
Before applying masking policies, DataSunrise automatically identifies sensitive data across ScyllaDB keyspaces and tables. Using its Data Discovery engine, the platform detects credit card numbers, national identification numbers, email addresses, health-related identifiers, and custom-defined sensitive patterns.
Discovery works across structured and semi-structured data and leverages NLP-based classification to improve detection accuracy. It integrates with broader data management processes to maintain an accurate inventory of sensitive assets.
This capability eliminates manual data inventory efforts and significantly reduces compliance blind spots while strengthening overall data security posture.
Granular Dynamic Masking Policy Engine
DataSunrise provides a centralized policy engine for defining runtime masking rules with surgical precision. Masking rules are implemented using the platform’s dynamic data masking capabilities and can be configured based on the target keyspace and table, specific columns such as credit_card_number, selected masking methods including full, partial, randomized, or hash-based transformations, and contextual conditions such as role-based, user-based, or IP-based logic.
For example, if the role equals analyst_role, the system can mask the credit_card_number column and display only the last four digits. The underlying data remains unchanged in ScyllaDB. Masking is applied dynamically during query execution, ensuring production data integrity.
Masking policies can also align with structured data security policies to maintain consistency across environments.
Real-Time Enforcement and Validation
Dynamic masking policies are enforced in real time without requiring any changes to ScyllaDB configuration. When an administrator executes:
SELECT credit_card_number FROM customers;
the full value is returned. When an analyst executes the same query, the masked value is returned instead.
Enforcement occurs transparently at runtime and integrates with Database Activity Monitoring for complete visibility into user actions. Detailed logs can be analyzed through centralized audit logs to maintain traceability and accountability.
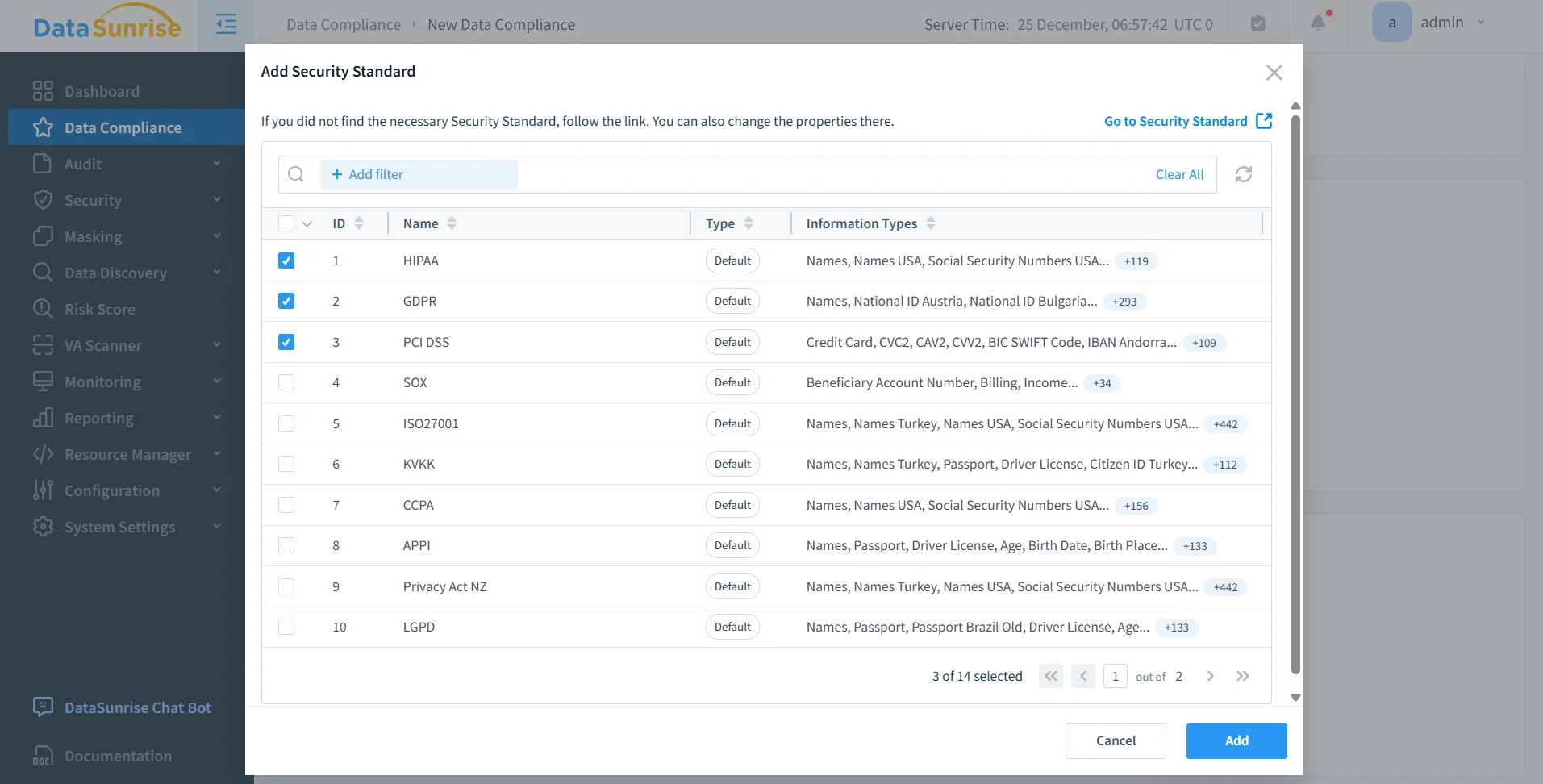
Compliance Autopilot and Regulatory Alignment
DataSunrise integrates Compliance Autopilot to align dynamic masking policies with major regulatory frameworks. Organizations can accelerate alignment with global data compliance regulations, including GDPR Compliance, HIPAA Compliance, PCI DSS Compliance, SOX, and ISO 27001.
Pre-configured compliance templates accelerate time-to-compliance, while Continuous Regulatory Calibration automatically adjusts enforcement policies as regulatory requirements evolve. Unlike solutions that require constant manual rule tuning, DataSunrise delivers autonomous protection across ScyllaDB clusters and heterogeneous data environments, ensuring sustained regulatory alignment and reduced compliance risk.
Business Impact of Dynamic Masking for ScyllaDB
| Impact Area | Business Outcome |
|---|---|
| Quantifiable Risk Reduction | Eliminates exposure of live PII to non-privileged users, reducing insider risk and minimizing the potential impact of data breaches. |
| Streamlined Compliance Workflows | Automates enforcement aligned with GDPR, HIPAA, and PCI DSS requirements, simplifying audit preparation and regulatory reporting. |
| Significant Reduction in Manual Effort | Removes the need for application rewrites, custom masking logic, or maintaining duplicate masked environments for analytics and testing. |
| Optimized Total Cost of Compliance | Zero-touch proxy architecture lowers operational overhead, reduces engineering effort, and minimizes ongoing policy maintenance costs. |
| Scalable for Growth | Suitable for startups through Fortune 500 enterprises, supporting flexible deployment models across on-premise, cloud, and hybrid infrastructures. |
Dynamic masking ensures that high-performance ScyllaDB clusters remain compliant and secure without sacrificing speed, scalability, or usability.
Conclusion
ScyllaDB provides strong authentication and access control mechanisms. However, it does not natively support runtime dynamic masking, leaving a visibility gap when sensitive data is queried by authorized but non-privileged users.
To protect sensitive data in high-throughput NoSQL environments, organizations must implement a context-aware enforcement layer capable of controlling how data is exposed at query time—not just who can access it.
DataSunrise delivers Zero-Touch Data Masking, Compliance Autopilot, and Enterprise-Grade Policy Enforcement for ScyllaDB across on-premise, cloud, and hybrid environments. By combining dynamic data masking with centralized Database Activity Monitoring, organizations gain full visibility and real-time control over sensitive information flows.
Through automated Data Discovery and alignment with global data compliance regulations, DataSunrise ensures that masking policies remain consistent, auditable, and adaptable to evolving regulatory requirements.
As a result, enterprises can maintain performance-driven ScyllaDB clusters while achieving measurable risk reduction, streamlined compliance workflows, and sustainable long-term security governance—without compromising speed, scalability, or operational efficiency.
Protect Your Data with DataSunrise
Secure your data across every layer with DataSunrise. Detect threats in real time with Activity Monitoring, Data Masking, and Database Firewall. Enforce Data Compliance, discover sensitive data, and protect workloads across 50+ supported cloud, on-prem, and AI system data source integrations.
Start protecting your critical data today
Request a Demo Download Now