How to Mask Sensitive Data in ScyllaDB
ScyllaDB is built for speed. Its high-performance NoSQL architecture delivers ultra-low latency at massive scale. However, once clusters begin storing customer profiles, payment details, medical records, or authentication tokens, performance alone no longer protects your business. Instead, organizations must implement structured and enforceable data masking to control exposure.
For companies handling regulated information, masking is not optional. Regulations such as GDPR, HIPAA, and PCI DSS require strict control over access to personally identifiable information (PII), financial data, and healthcare records. Therefore, simply restricting access at the role level does not meet modern compliance expectations. Authorized access does not equal controlled visibility.
Moreover, an effective masking strategy must operate alongside broader database security controls and integrate directly into a centralized data compliance framework. Without runtime enforcement, sensitive values remain visible to users who should not see full records. As a result, organizations expose themselves to compliance violations and insider risk.
In this guide, we explain what masking means in ScyllaDB environments, outline the limitations of native approaches, and demonstrate how to implement enterprise-grade protection using DataSunrise with Zero-Touch Data Masking and Compliance Autopilot.
Overall, this structure follows the established format used in previous audit and activity history articles while aligning with internal content architecture standards.
Importance of Masking Sensitive Data
Masking sensitive data in ScyllaDB is not just a technical enhancement — it is a security and compliance necessity. High-performance NoSQL environments power customer-facing applications, analytics pipelines, IoT platforms, and financial systems. Consequently, they process and store large volumes of sensitive information. Without masking, any user or service account with query permissions can immediately view that data.
Encryption at rest protects stored files, while encryption in transit secures network traffic. Role-Based Access Control limits who can connect. However, these mechanisms do not control how data appears after a query executes. When a support engineer, analyst, or developer runs a SELECT statement against production data, the database returns full credit card numbers or medical identifiers in plain text. As a result, organizations face regulatory exposure and operational risk.
Dynamic masking solves this problem by enforcing Context-Aware Protection at query runtime. Instead of blocking access entirely, it transforms sensitive values according to user roles, policies, or contextual conditions. Therefore, teams maintain usability while sharply reducing unnecessary exposure. At the same time, this model aligns with Zero-Trust Data Access principles.
From a compliance perspective, masking directly supports regulatory frameworks such as GDPR, HIPAA, and PCI DSS. It ensures that only authorized roles can view complete sensitive values. In addition, it strengthens overall data security posture and reinforces continuous compliance management initiatives.
In modern distributed architectures, microservices and analytics tools often access the same database simultaneously. Therefore, masking acts as a critical control layer that prevents overexposure. It reduces insider risk, limits the blast radius of compromised credentials, and preserves protection even in high-speed, high-scale ScyllaDB environments.
Native Capabilities for Protecting Sensitive Data in ScyllaDB
ScyllaDB is API-compatible with Apache Cassandra and includes several built-in security mechanisms designed to control access and protect stored data. These native capabilities provide a strong baseline for securing clusters in production environments. They help enforce access restrictions, validate identities, and secure data storage and transmission. However, they primarily focus on perimeter control and encryption rather than runtime data protection.
Below is a detailed overview of ScyllaDB’s core native security features and their practical limitations in regulated environments.
Role-Based Access Control (RBAC)
ScyllaDB implements Role-Based Access Control to manage permissions at the role, keyspace, and table levels. Administrators can create roles, assign privileges, and restrict which operations specific users are allowed to perform within the database.
For example, creating a limited-access analyst role:
CREATE ROLE analyst WITH PASSWORD = 'secure_password' AND LOGIN = true;
GRANT SELECT ON KEYSPACE customer_data TO analyst;
With this configuration, the analyst can execute SELECT statements but cannot modify schema objects or perform write operations unless those privileges are explicitly granted. RBAC is effective for enforcing the principle of least privilege and limiting administrative risk.
However, RBAC operates at a structural level. Once a role is granted SELECT access to a table, all readable columns within that table are exposed in full. There is no built-in mechanism to selectively mask specific fields. RBAC does not provide column-level masking, conditional data visibility, context-aware protection, or runtime transformation of sensitive values.
If the analyst queries a table containing credit card numbers or medical identifiers, the database returns those values exactly as they are stored. This is where compliance gaps begin to appear.
Authentication and Authorization Mechanisms
ScyllaDB supports pluggable authentication mechanisms to verify user identities before granting access. These mechanisms typically include password-based authentication, integration with external authentication systems, and role-based privilege validation.
Authentication ensures that only verified users can establish connections to the database. Authorization determines which actions those users are permitted to perform once connected.
For example, enabling password authentication in cassandra.yaml:
authenticator: PasswordAuthenticator
authorizer: CassandraAuthorizer
Creating a role and granting permissions:
CREATE ROLE reporting_user
WITH PASSWORD = 'StrongPassword123'
AND LOGIN = true;
GRANT SELECT ON KEYSPACE analytics TO reporting_user;
In this configuration, the user must authenticate with valid credentials before establishing a session. Once authenticated, the user can only perform explicitly granted operations. Any unauthorized commands are rejected at execution time.
These mechanisms are essential for perimeter control. They protect against unauthorized access and ensure only approved identities can execute queries. However, their responsibility ends once a legitimate user runs a valid command.
If a user is authorized to execute a SELECT statement, the database does not evaluate whether the returned data should be partially masked or transformed:
SELECT customer_name, credit_card_number
FROM payments;
If access is granted, ScyllaDB returns full values exactly as stored.
Authentication controls who enters.
Authorization controls what actions are allowed.
Neither controls how sensitive values are displayed after access is granted.
Encryption at Rest and in Transit
ScyllaDB supports encryption at rest and in transit to secure data storage and communication channels.
Encryption at rest protects SSTables and commit logs stored on disk. This is typically configured at the filesystem or disk level, for example using Linux dm-crypt:
cryptsetup luksFormat /dev/sdb
cryptsetup open /dev/sdb scylla_encrypted_disk
Encryption in transit secures client-server and node-to-node communication using TLS. Example TLS configuration in cassandra.yaml:
server_encryption_options:
internode_encryption: all
keystore: /etc/scylla/conf/keystore.jks
keystore_password: changeit
truststore: /etc/scylla/conf/truststore.jks
truststore_password: changeit
client_encryption_options:
enabled: true
keystore: /etc/scylla/conf/keystore.jks
keystore_password: changeit
These measures ensure that data cannot be read directly from disk if storage media are compromised. They also prevent interception of network traffic in plain text and ensure that nodes authenticate each other in distributed clusters.
However, encryption protects data only during storage or transmission. Once decrypted inside the database engine and returned through a valid query, the data becomes fully readable to the requesting client:
SELECT ssn, medical_record_number
FROM patient_records;
Encryption protects storage.
RBAC protects entry points.
Authentication verifies identity.
None of these mechanisms protect what is displayed once access is granted.
The Compliance Gap
When an authorized user queries a sensitive table in ScyllaDB, they receive complete, readable values:
SELECT email, phone_number, credit_card_number
FROM customer_profiles;
There is no native capability to dynamically mask specific columns, obfuscate sensitive fields based on user roles, apply context-aware runtime transformations, or automatically discover and classify sensitive data.
For regulated environments handling personally identifiable information, financial records, or healthcare data, this creates a clear compliance gap. Modern regulatory standards require controlled exposure of sensitive information — not merely controlled access.
ScyllaDB’s native security features provide a solid foundation for infrastructure-level protection. However, enterprise-grade masking requires an additional layer capable of transforming sensitive data at query runtime without modifying applications or disrupting operational workflows.
Enterprise-Grade Masking for ScyllaDB with DataSunrise
DataSunrise delivers enterprise-grade masking for ScyllaDB through Zero-Touch Data Masking, ensuring seamless protection without disrupting applications or database performance. Instead of relying on manual rule updates or fragmented scripts, the platform provides autonomous protection built around automation, centralized governance, and a compliance-first architecture.
Below is a detailed explanation of the core capabilities that extend ScyllaDB beyond native access controls and encryption.
Zero-Touch Data Masking
Zero-Touch Data Masking enforces masking policies automatically at query runtime. Sensitive fields are transformed dynamically before results are returned to the user. This process does not require application modification, code refactoring, or changes to business logic.
Masking operates transparently between the client and the database layer. Queries continue to execute normally, but the returned dataset is evaluated against defined policies. This ensures that sensitive values are never exposed to unauthorized users while maintaining stable database performance.
This approach eliminates the risks associated with application-level masking logic and significantly reduces operational overhead.
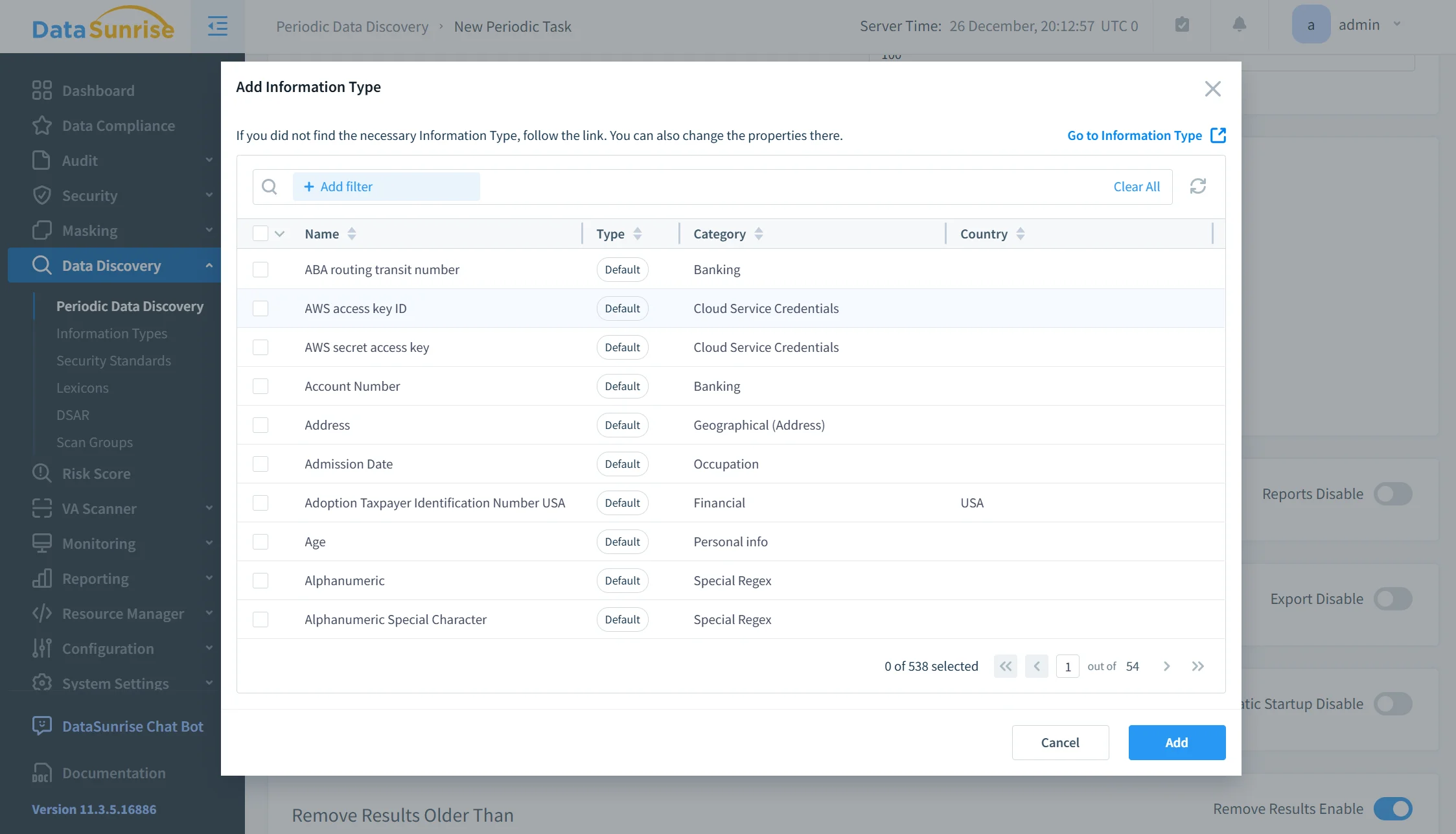
Auto-Discover & Mask
The Auto-Discover & Mask capability identifies sensitive data automatically across ScyllaDB environments. Instead of manually locating protected columns, administrators can rely on built-in discovery mechanisms that scan keyspaces, tables, columns, and JSON structures.
Once sensitive attributes are detected, masking policies can be generated and applied automatically. This reduces dependency on manual classification and minimizes the likelihood of unprotected data fields remaining undetected.
By continuously scanning evolving datasets, the system maintains visibility even as schemas change.
No-Code Policy Automation
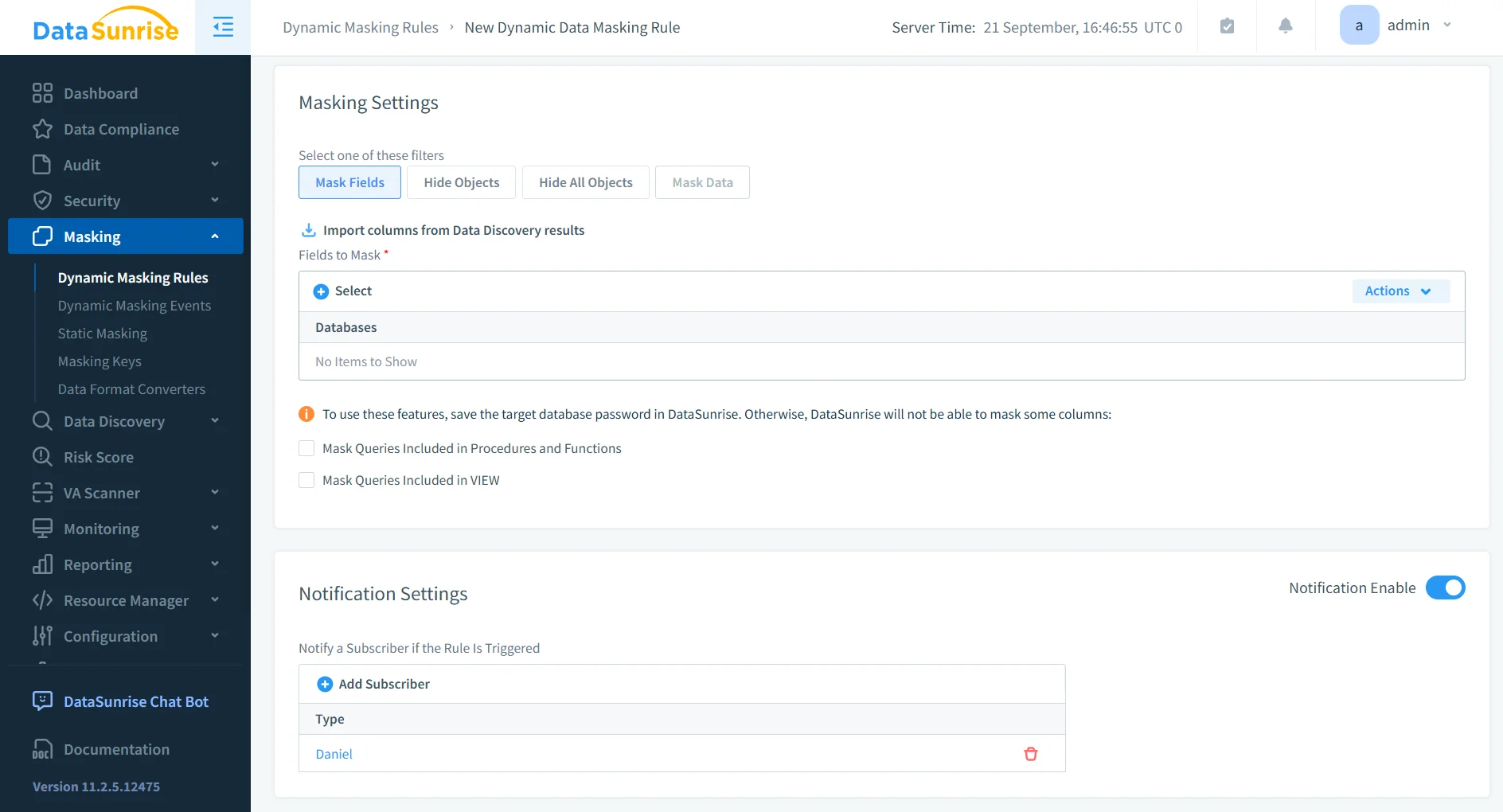
No-Code Policy Automation enables security and compliance teams to define masking rules through a centralized management interface. There is no need for development cycles or schema redesign.
Policies can be configured based on user roles, IP ranges, applications, query types, or time-based conditions. This flexibility ensures that data visibility aligns precisely with business requirements and regulatory expectations.
Centralized policy management accelerates implementation while preserving granular control over data exposure.
Dynamic Data Masking
Dynamic Data Masking applies context-aware transformations in real time. When a query is executed, the platform evaluates identity, role, and policy conditions before returning results.
For example, analysts may see partially masked credit card numbers, finance administrators may see full values, and external integrations may receive tokenized data. All transformations occur during query execution.
Because masking is applied at runtime, raw sensitive values are never exposed beyond authorized boundaries. This ensures operational continuity while enforcing strict access differentiation.
Static and In-Place Masking
In addition to runtime masking, DataSunrise supports static and in-place masking for non-production environments.
Organizations can generate sanitized datasets for development, protect sensitive information in testing environments, and safely share masked data with analytics teams. By removing real personally identifiable information from non-production systems, insider risk is reduced and compliance exposure is minimized.
This capability ensures that test and staging environments do not become weak points in the security posture.
Context-Aware Protection
Context-Aware Protection evaluates identity, session attributes, and policy logic before determining how data should be displayed. Instead of blocking access entirely, the system adjusts data visibility dynamically based on predefined conditions.
This aligns with Zero-Trust Data Access principles, where every query is assessed before data is returned. The system balances usability and protection, allowing authorized operations while minimizing unnecessary exposure.
Sensitive Data Discovery Engine
The Sensitive Data Discovery Engine identifies regulated information across structured and semi-structured datasets. It detects personally identifiable information, financial identifiers, healthcare records, and custom business-defined sensitive attributes.
Discovery tasks can be scheduled periodically, ensuring that new tables, columns, or JSON fields are automatically evaluated as the environment evolves. This continuous visibility prevents compliance gaps from emerging over time.
Compliance Autopilot
Compliance Autopilot continuously aligns masking and security policies with major regulatory frameworks such as GDPR, HIPAA, PCI DSS, and SOX.
The system monitors policy coverage, detects configuration drift, and ensures sensitive data exposure remains aligned with regulatory requirements. This reduces manual compliance validation efforts and supports audit readiness through structured reporting and automated evidence generation.
Centralized Data Compliance Platform
DataSunrise unifies masking, auditing, monitoring, and reporting into a centralized governance layer. Rather than operating multiple disconnected tools, organizations gain consolidated visibility into masked fields, access events, policy violations, and compliance reports.
This centralized model simplifies operations, improves accountability, and reduces administrative complexity across distributed environments.
Unified Security Framework
The Unified Security Framework extends protection beyond ScyllaDB. It provides cross-database visibility and policy consistency across both NoSQL and SQL systems.
Organizations operating hybrid infrastructures can enforce uniform masking rules across ScyllaDB clusters, relational databases, data warehouses, and cloud storage platforms. This ensures consistent protection regardless of infrastructure architecture.
Enterprise-grade masking for ScyllaDB is not limited to hiding fields. It represents a comprehensive security strategy that integrates automated discovery, real-time transformation, centralized governance, and regulatory alignment into a scalable, enterprise-ready solution.
Business Impact of Masking in ScyllaDB
| Business Outcome | Impact Description |
|---|---|
| Quantifiable Risk Reduction | Eliminates live exposure of PII, financial, and healthcare data by enforcing runtime masking policies, reducing breach surface and insider risk. |
| Streamlined Compliance Workflows | Automates masking policy enforcement and regulatory alignment, simplifying adherence to GDPR, HIPAA, PCI DSS, and SOX requirements. |
| Significant Reduction in Manual Effort | Removes reliance on manual scripts and application-level masking, decreasing workload for DevOps, security, and compliance teams. |
| Optimized Total Cost of Compliance | Centralized governance reduces tool sprawl, minimizes operational overhead, and lowers long-term compliance management costs. |
| Faster Audit Preparation | Provides real-time visibility and structured evidence generation, accelerating internal and external audit readiness. |
Unlike fragmented masking scripts, DataSunrise combines enterprise-grade policy enforcement with the granular controls technical teams require. The solution scales from startups to Fortune 500 enterprises, offering flexible deployment modes and alignment with long-term infrastructure growth strategies.
Conclusion
ScyllaDB delivers exceptional performance and scalability for high-throughput NoSQL workloads. However, its native security controls focus primarily on access management and encryption. They do not provide centralized, compliance-aligned masking capable of controlling how sensitive data is displayed after access is granted.
DataSunrise extends ScyllaDB with Zero-Touch Data Masking, autonomous compliance orchestration through its Compliance Manager, continuous regulatory alignment, and a Unified Security Framework. Together, these capabilities deliver runtime data transformation, automated regulatory enforcement, and centralized governance across distributed environments.
By combining masking with Database Activity Monitoring and intelligent Sensitive Data Discovery, organizations gain full visibility alongside protection. This integrated approach eliminates compliance gaps while reducing operational complexity.
The platform is deployable across on-premise, cloud, and hybrid infrastructures without configuration friction, allowing organizations to strengthen security posture without disrupting performance.
Masking is not simply about hiding values in query results. It is about enforcing controlled exposure, eliminating compliance gaps, and protecting sensitive information with precision and consistency at enterprise scale.
Protect Your Data with DataSunrise
Secure your data across every layer with DataSunrise. Detect threats in real time with Activity Monitoring, Data Masking, and Database Firewall. Enforce Data Compliance, discover sensitive data, and protect workloads across 50+ supported cloud, on-prem, and AI system data source integrations.
Start protecting your critical data today
Request a Demo Download Now