Data Anonymization in IBM Db2
As data privacy regulations grow increasingly stringent, organizations managing sensitive information in enterprise databases must adopt robust anonymization strategies. IBM Db2 is one of the most widely deployed relational database management systems in the world, trusted by enterprises to handle financial records, protected health information, and customer PII. Db2's built-in security framework provides a solid starting point, but modern compliance demands increasingly require going further.
According to IBM's 2024 Data Breach Report, the average cost of a data breach reached $4.88 million in 2024, with excessive data exposure among the leading contributing factors. Data anonymization—transforming personally identifiable information so it cannot be traced back to a real individual—has become a foundational control in any enterprise database security posture.
This article walks through IBM Db2's native anonymization capabilities and explores how DataSunrise extends them with automated, compliance-ready protection.
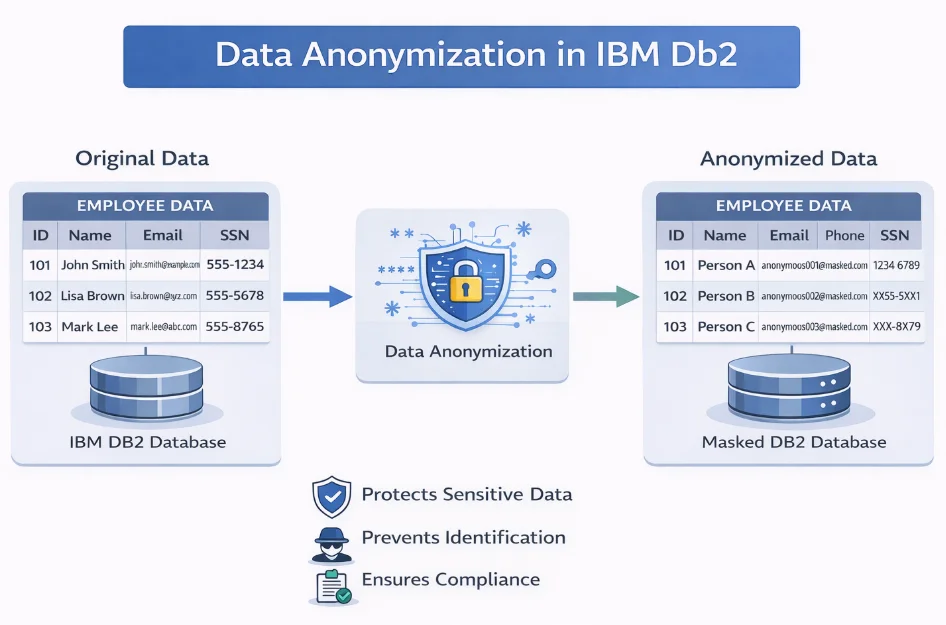
Understanding Data Anonymization in IBM Db2
Data anonymization in Db2 environments typically addresses PII (names, SSNs, email addresses), PHI (diagnoses, patient identifiers), financial data (credit card numbers, account details), and authentication credentials. Organizations apply these techniques when sharing data with third parties, populating non-production environments, generating analytics datasets, or fulfilling subject access requests under compliance regulations such as GDPR and HIPAA.
Native IBM Db2 Data Anonymization Capabilities
IBM Db2 provides several built-in mechanisms that administrators can combine to reduce sensitive data exposure. Properly configured, these controls form a meaningful layer within a broader data security policy.
1. Row and Column Access Control (RCAC)
Db2's RCAC feature allows fine-grained column-level masking based on session context, functioning similarly to role-based access controls applied directly at the data layer. Column masks substitute sensitive values transparently at query time, requiring no application code changes.
Enabling RCAC and creating a column mask for SSN:
ALTER TABLE hr.employees ACTIVATE COLUMN ACCESS CONTROL;
ALTER TABLE hr.employees ACTIVATE ROW ACCESS CONTROL;
CREATE OR REPLACE MASK ssn_mask ON hr.employees
FOR COLUMN ssn
RETURN
CASE
WHEN VERIFY_ROLE_FOR_USER(SESSION_USER, 'DB_ADMIN') = 1
THEN ssn
ELSE 'XXX-XX-' || SUBSTR(ssn, 8, 4)
END
ENABLE;
Administrators see the full SSN; all other users see only the last four digits. For full configuration details, refer to the IBM Db2 RCAC documentation.
2. Static Anonymization for Non-Production Environments
Db2 supports creating anonymized copies of production tables via INSERT...SELECT combined with scalar functions, producing development datasets that mirror the production schema without exposing real identities. This is a core practice in test data management, enabling QA teams to work with realistic data safely.
INSERT INTO dev.customers (customer_id, first_name, last_name, email, phone)
SELECT
customer_id,
'Anonymous' AS first_name,
'User' AS last_name,
'user' || CHAR(customer_id) || '@example.com' AS email,
'555-000-' || LPAD(CHAR(MOD(customer_id, 10000)), 4, '0') AS phone
FROM prod.customers;
3. Views for Persistent Data Abstraction
Views allow administrators to expose transformed data to specific roles without granting access to underlying tables, acting as a lightweight enforcement layer on top of Db2's access controls.
CREATE OR REPLACE VIEW reporting.masked_transactions AS
SELECT
transaction_id,
transaction_date,
amount,
'XXXX-XXXX-XXXX-' || SUBSTR(card_number, 13, 4) AS card_number,
merchant_name
FROM finance.transactions;
GRANT SELECT ON reporting.masked_transactions TO ROLE REPORTING_USERS;
REVOKE SELECT ON finance.transactions FROM ROLE REPORTING_USERS;
Summary of Native Db2 Anonymization Capabilities and Limitations
| Capability | Limitation |
|---|---|
| Column masks via RCAC | Applies only at query time; masks do not carry over to data exports |
| Static anonymization via INSERT…SELECT | Manual process with no automated scheduling or policy enforcement |
| View-based abstraction | Privileged users can still access underlying tables directly |
| Built-in scalar functions | Limited to simple substitution; no NLP-based PII detection |
| No native audit of anonymization events | Makes compliance verification and reporting difficult |
Enhanced Data Anonymization for IBM Db2 with DataSunrise
DataSunrise extends Db2's built-in capabilities with a policy-driven anonymization platform. Instead of manually writing and maintaining SQL masks, administrators benefit from automated data discovery, no-code rule creation, and real-time enforcement across all sessions—with support for over 40 database platforms alongside Db2.
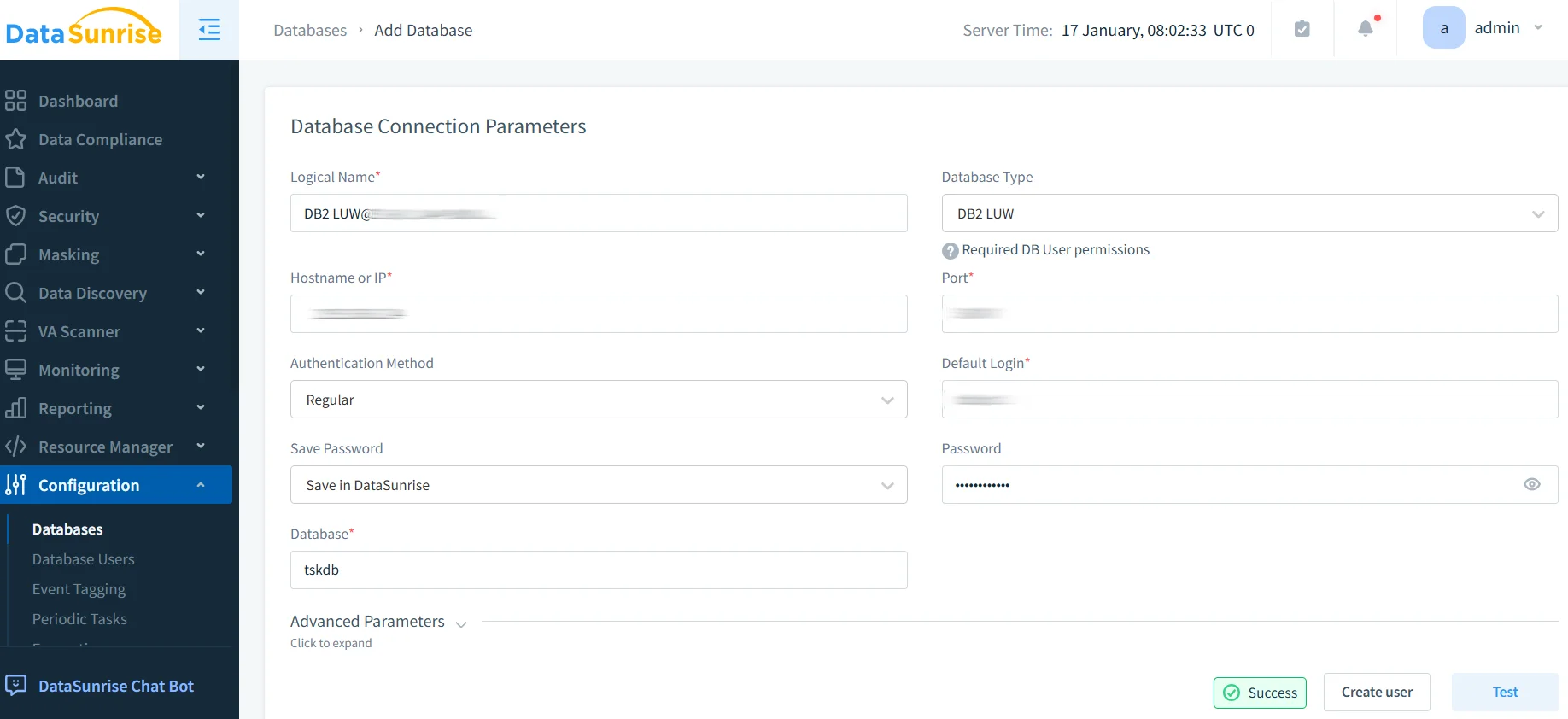
1. Connect IBM Db2 to DataSunrise
Establish a secure connection through the DataSunrise web interface by providing host, port, database name, and credentials. DataSunrise begins passively monitoring traffic immediately, with no disruption to existing applications.
2. Discover and Classify Sensitive Data
DataSunrise's Auto-Discover & Classify engine scans the Db2 schema using NLP algorithms and regulatory-aligned patterns to automatically flag columns containing PII, PHI, or financial data—eliminating blind spots that manual configuration leaves behind.
3. Create Dynamic Masking Rules
Administrators create dynamic data masking rules through a no-code interface, scoped by user role, source IP, or query type. The underlying Db2 data remains intact; values returned to non-privileged sessions are substituted in real time without any application-side changes.
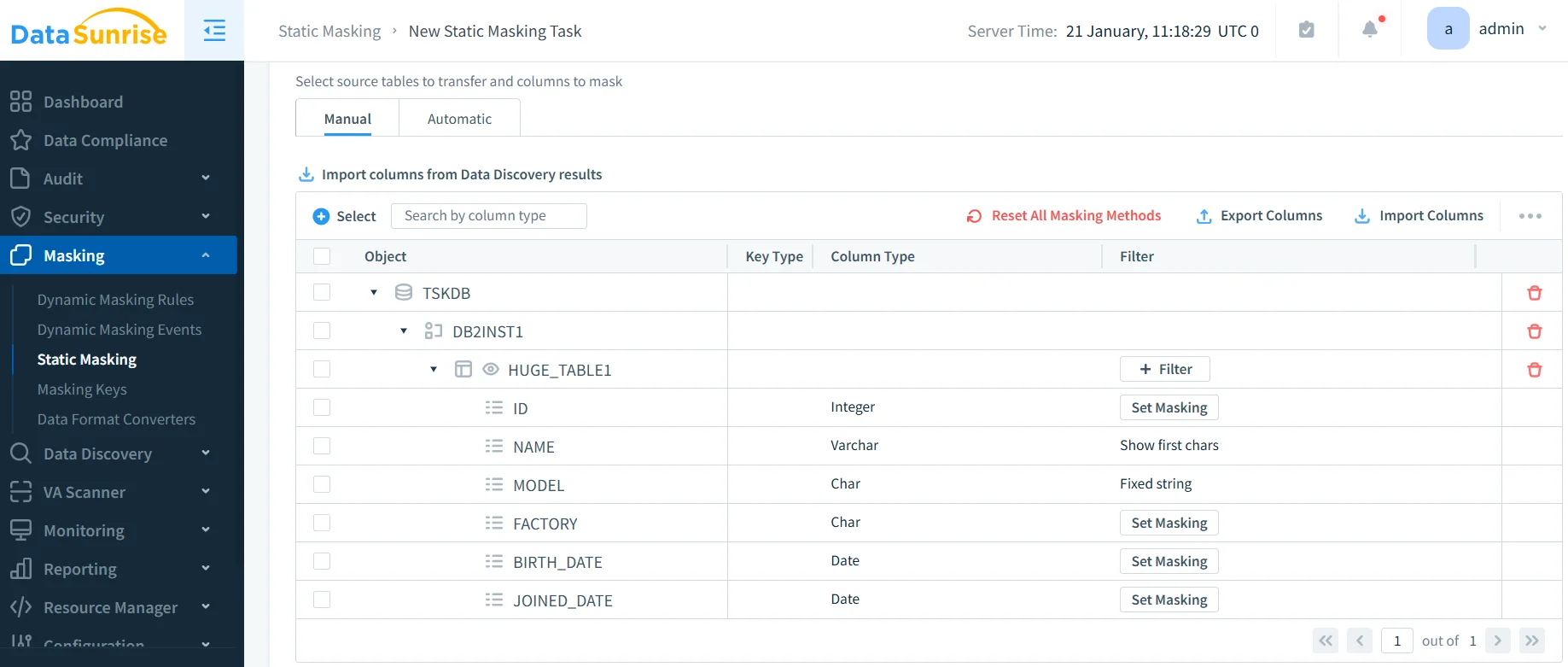
4. Apply Static Masking for Non-Production Data Management
DataSunrise's static data masking generates anonymized copies of production tables for QA and development use, applying format-preserving transformations, realistic value substitution, and date shifting to ensure data utility without re-identification risk. For teams that need entirely fabricated datasets, DataSunrise also offers synthetic data generation as a complementary capability.
5. Monitor and Audit Anonymization Events
Unlike Db2's native masks, DataSunrise records a complete audit trail of every anonymization event—who queried what, which rule was applied, and when—exportable to SIEM systems for centralized security operations.
Key DataSunrise Features for IBM Db2 Data Anonymization
- Auto-Discover & Classify: Automatically identify sensitive columns across all Db2 schemas using machine learning and NLP.
- Dynamic Data Masking: Real-time, context-aware masking based on user roles, IPs, and query patterns—no code changes required.
- Static Data Masking: Generate fully anonymized non-production datasets with format-preserving and realistic replacement techniques.
- Automated Compliance Reporting: One-click reports for GDPR, HIPAA, PCI DSS, and SOX, dramatically reducing audit preparation time.
- Behavioral Analytics: Detect anomalous query patterns—such as bulk downloads of sensitive columns—and trigger real-time alerts.
- Centralized Policy Management: Manage anonymization rules across Db2 and 40+ other platforms from a single console.
- Flexible Deployment Modes: On-premises, cloud, or hybrid deployment with minimal reconfiguration.
Conclusion
IBM Db2's native capabilities—RCAC column masks, view-based abstraction, and scalar function transformations—provide a solid foundation for basic data anonymization. However, as regulatory requirements grow more complex, manual mechanisms struggle to keep pace with schema changes, new user roles, and evolving compliance standards. Complementary controls like database encryption are valuable, but without a centralized anonymization layer, sensitive data remains at risk wherever it is queried or exported.
DataSunrise bridges this gap with automated sensitive data discovery, real-time dynamic masking, static masking for non-production use, and comprehensive compliance reporting—transforming data anonymization in IBM Db2 from a labor-intensive process into a scalable, policy-driven security asset.
Protect Your Data with DataSunrise
Secure your data across every layer with DataSunrise. Detect threats in real time with Activity Monitoring, Data Masking, and Database Firewall. Enforce Data Compliance, discover sensitive data, and protect workloads across 50+ supported cloud, on-prem, and AI system data source integrations.
Start protecting your critical data today
Request a Demo Download Now