Data Obfuscation in ClickHouse
Modern analytical databases process massive volumes of sensitive business data, including customer identifiers, payment information, and internal operational records. As organizations increasingly rely on real-time analytics, protecting this information becomes a critical requirement. Industry reports such as the IBM Cost of a Data Breach Report consistently show that exposed sensitive data remains one of the most expensive security incidents organizations face.
ClickHouse is widely used for high-performance analytical workloads, but its speed and accessibility can also increase the risk of exposing confidential data if access is not carefully controlled.
One effective protection technique is data obfuscation. Data obfuscation transforms sensitive information into a protected format so that unauthorized users cannot easily read or misuse it. When implemented correctly, it allows analysts and developers to work with realistic datasets while ensuring that confidential values remain hidden. In many environments, obfuscation is implemented alongside technologies such as dynamic data masking to prevent direct exposure of sensitive values during queries.
In this article, we explore how to implement native data obfuscation techniques in ClickHouse and how platforms such as DataSunrise data security solutions can enhance protection through automated security policies, centralized monitoring, and intelligent protection of sensitive data across analytical environments.
What is Data Obfuscation?
Data obfuscation is a technique used to protect sensitive information by transforming it into a modified or partially hidden format while preserving its overall structure and usability. Instead of completely removing or encrypting the data, obfuscation alters specific elements so that unauthorized users cannot easily interpret the original values.
In practice, data obfuscation replaces real values with masked, truncated, randomized, or tokenized equivalents. For example, an email address such as [email protected] may appear as a***@example.com, while a phone number like 555-123-4567 may be displayed as ***-***-4567. This allows analysts and developers to work with realistic datasets without exposing the underlying confidential information.
Organizations commonly apply data obfuscation to protect fields such as:
- Personally identifiable information (PII)
- Financial data and payment identifiers
- Customer contact details
- Internal account identifiers
Unlike full encryption, which protects data at rest or in transit, obfuscation focuses on controlling how sensitive values appear in query results, reports, or application interfaces. This approach is particularly useful in analytical platforms where multiple users need access to large datasets but should not see raw sensitive data.
In modern data environments, obfuscation is often combined with security techniques such as dynamic data masking, data masking, database security, and access control mechanisms to ensure that sensitive information remains protected across production analytics workflows.
Native Data Obfuscation Techniques in ClickHouse
ClickHouse does not include a dedicated “data obfuscation module.” However, administrators can implement obfuscation through SQL transformations, views, and access control mechanisms.
These methods allow sensitive columns to be masked or transformed before they are returned to users.
Common native techniques include:
- SQL-based data transformation
- Masked views
- Role-based access control (RBAC)
These approaches provide a baseline method for protecting sensitive fields inside analytical queries.
Creating Obfuscated Data Views in ClickHouse
One of the most practical approaches to data obfuscation is creating database views that automatically transform sensitive columns.
Create a Sample Table
First create a simple dataset that contains sensitive information.
CREATE TABLE customers
(
id UInt32,
name String,
email String,
phone String
)
ENGINE = MergeTree()
ORDER BY id;
Insert example data:
INSERT INTO customers VALUES
(1,'Alice Johnson','[email protected]','555-123-4567'),
(2,'Bob Smith','[email protected]','555-987-6543');
Create an Obfuscated View
Now create a view that hides part of the sensitive data.
CREATE VIEW customers_obfuscated AS
SELECT
id,
name,
concat(left(email,1),'***@',splitByChar('@',email)[2]) AS email_masked,
concat('***-***-',right(phone,4)) AS phone_masked
FROM customers;
This view replaces most of the email and phone values with masked characters.
Query the Obfuscated Data
Users can query the masked data through the view:
SELECT * FROM customers_obfuscated;
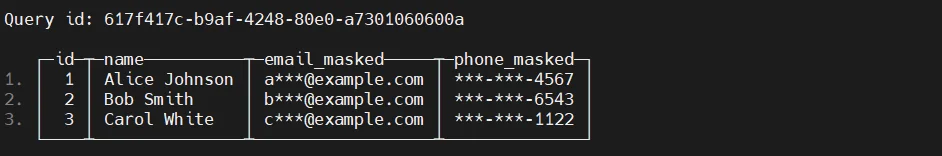
The original table still stores full values, but users accessing the view only see protected information.
Applying Role-Based Access Control
ClickHouse supports Role-Based Access Control (RBAC), which can ensure that users interact only with obfuscated views rather than the raw data tables.
Create a restricted role:
CREATE ROLE analyst_role;
Grant access only to the obfuscated view:
GRANT SELECT ON customers_obfuscated TO analyst_role;
Assign the role to a user:
GRANT analyst_role TO analyst_user;
With this configuration, analysts can query masked data while the original table remains restricted to administrators.
Enhancing ClickHouse Data Obfuscation with DataSunrise
While ClickHouse native tools provide basic protection, enterprise environments often require centralized security management and consistent policy enforcement across multiple data systems. DataSunrise extends ClickHouse security by introducing automated data obfuscation, centralized policy control, and real-time monitoring capabilities as part of a broader data security and database security framework.
Instead of relying solely on manual SQL transformations or view-based masking, DataSunrise operates as a proxy between users and the database. This architecture allows security policies to be enforced dynamically without requiring changes to existing queries or application logic. As a result, organizations can implement consistent data protection rules across analytical workloads while maintaining the full performance benefits of ClickHouse. In addition, the platform integrates capabilities such as data discovery and dynamic data masking to automatically identify and protect sensitive information.
Connect ClickHouse to DataSunrise
After deploying DataSunrise, the first step is to connect the ClickHouse database instance through the DataSunrise management interface. Administrators provide the connection parameters such as host address, port number, and authentication credentials.
Once the instance is added, DataSunrise begins monitoring database traffic flowing between users and the ClickHouse server. This connection enables the platform to inspect queries in real time and apply security rules whenever sensitive data is accessed. These monitoring capabilities are part of the platform’s broader database activity monitoring functionality.
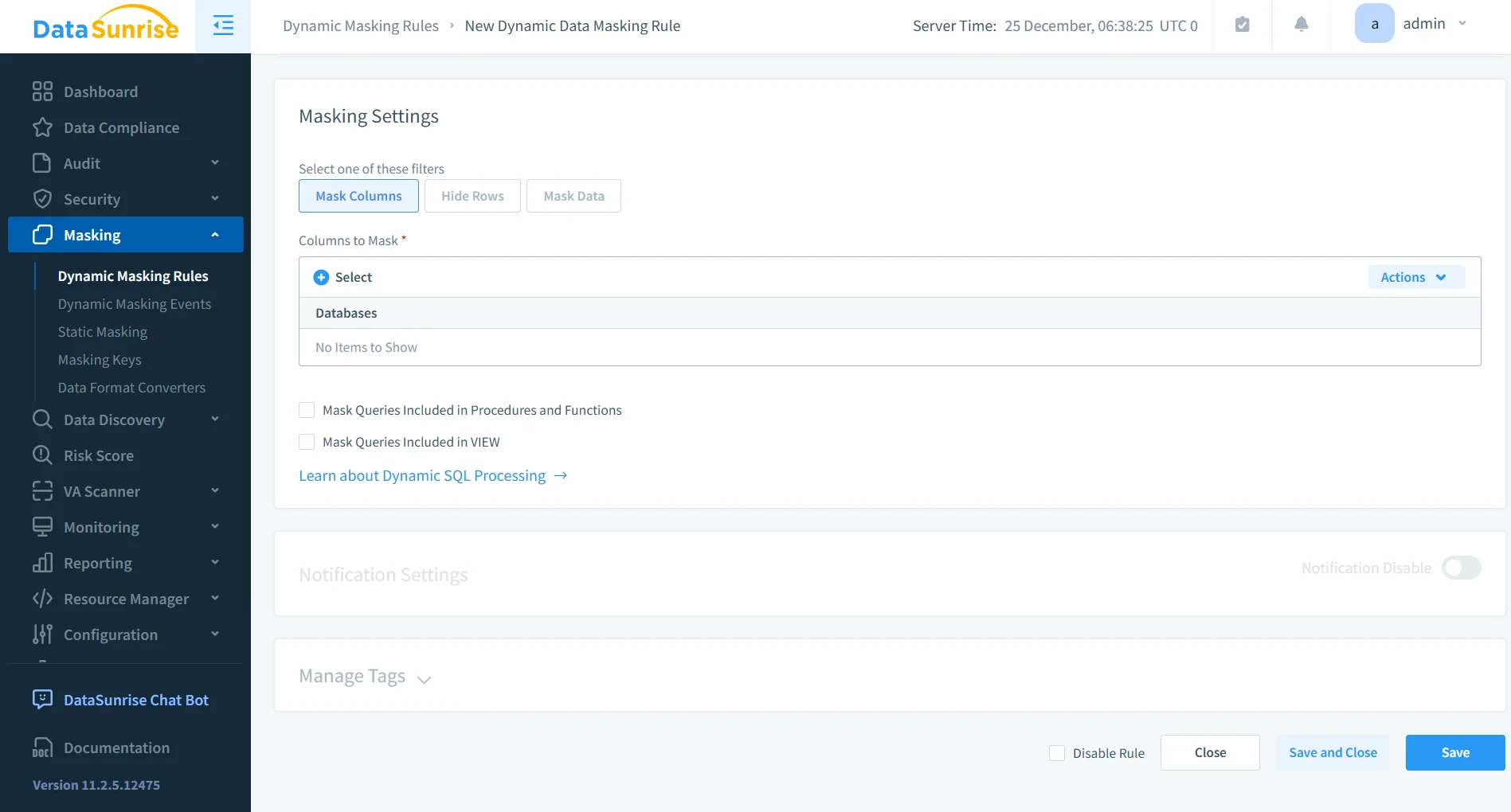
Configure Obfuscation Rules
After the database connection is established, administrators can create obfuscation policies that automatically protect sensitive columns. These rules define how specific data elements should be transformed before being returned to the user.
Obfuscation rules can be applied to various categories of sensitive information, including personally identifiable information, payment data, customer contact details, and internal identifiers used within enterprise systems. The platform also supports protection of personally identifiable information, helping organizations enforce consistent security controls across analytical datasets.
Because these policies operate at the proxy layer, they are enforced transparently whenever queries access protected fields. Applications continue to function normally while sensitive values remain hidden from unauthorized users.
Monitor Query Results
Once obfuscation rules are configured, DataSunrise automatically intercepts query responses and replaces protected values with masked or randomized equivalents before they reach the client.
Administrators can monitor database activity through the platform’s centralized dashboards, which display query events, user access patterns, and security rule execution. These capabilities are complemented by features such as user behavior analysis and automated compliance monitoring, helping organizations understand how sensitive information is accessed and ensuring that obfuscation policies are consistently applied across their ClickHouse environments.
Business Benefits of Data Obfuscation
Implementing data obfuscation in analytical platforms delivers measurable business advantages.
| Benefit | Description |
|---|---|
| Reduced Risk of Data Exposure | Sensitive data remains protected even when analysts query production datasets. |
| Safer Development and Testing | Obfuscated data allows teams to work with realistic datasets without exposing confidential information. |
| Improved Regulatory Compliance | Security policies help organizations meet regulatory requirements for protecting personal and financial data. |
| Operational Efficiency | Centralized security controls simplify management of large data environments. |
Conclusion
ClickHouse provides powerful analytical capabilities, but protecting sensitive information remains an essential responsibility for organizations managing large datasets.
Native techniques such as SQL transformations, masked views, and RBAC policies can provide basic data obfuscation capabilities. However, these approaches require manual configuration and careful operational management.
Solutions like DataSunrise extend ClickHouse security with automated data discovery, centralized masking policies, and real-time database activity monitoring.
By implementing automated data obfuscation strategies, organizations can maintain strong data protection while continuing to leverage the full performance and scalability of ClickHouse.
To explore advanced security capabilities for ClickHouse environments, review the DataSunrise deployment options or request a live demonstration.
Protect Your Data with DataSunrise
Secure your data across every layer with DataSunrise. Detect threats in real time with Activity Monitoring, Data Masking, and Database Firewall. Enforce Data Compliance, discover sensitive data, and protect workloads across 50+ supported cloud, on-prem, and AI system data source integrations.
Start protecting your critical data today
Request a Demo Download Now