
Dynamic Data Masking for Cloudberry
Dynamic data masking for Cloudberry provides organizations with effective data protection capabilities. Verizon’s 2024 Data Breach Investigations Report shows that 83% of data breaches involve human factors. These include credential misuse and mishandling of sensitive information. This insight highlights the value of implementing dynamic data masking for Cloudberry databases in modern data management. The technology enables real-time data masking, ensuring sensitive information remains secure during regular database operations while maintaining necessary functionality for authorized users.
Understanding Dynamic Data Masking in Cloudberry
Dynamic data masking (DDM) allows organizations to hide sensitive data in real-time while preserving the original data format. Dynamic masking is different from static masking. It does not change the underlying data. This makes it great for development, testing, and customer service situations.
Native Masking Capabilities
Cloudberry provides built-in features for dynamic data masking through its SQL language implementation. These capabilities enable administrators to:
- Create masked views of sensitive data
- Implement role-based access controls
- Apply masking rules without modifying application code
- Maintain data integrity while protecting confidential information
Implementing Native Dynamic Data Masking
Setting Up Masking Rules via SQL
To implement dynamic data masking in Cloudberry, you can use SQL commands to create masked views. Here’s a practical example:
CREATE MASK EmailMask ON dbo.Customers
FOR COLUMN email
AS
CASE
WHEN IS_ROLEMEMBER('DataAdmin') = 1
THEN email
ELSE CONCAT(LEFT(email, 2), '***@', RIGHT(email, CHARINDEX('@', REVERSE(email)) - 1))
END;
This mask shows complete email addresses to users with the DataAdmin role while displaying partially masked emails to others.
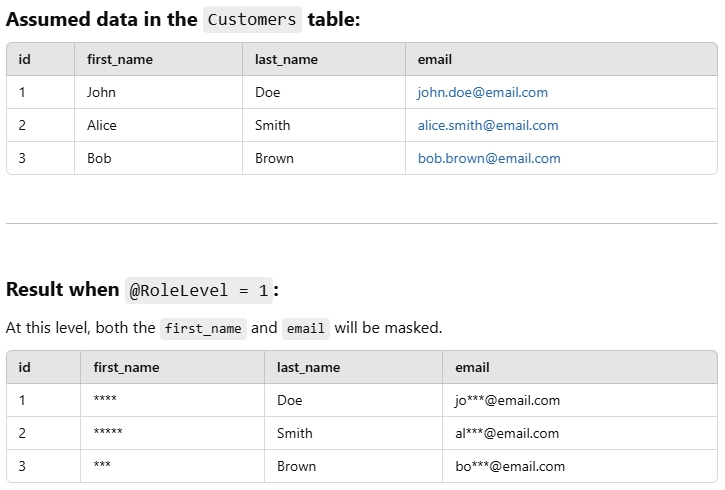
Working with Stored Procedures
Stored procedures offer additional flexibility for implementing dynamic masking:
CREATE PROCEDURE MaskCustomerData
@RoleLevel INT
AS
BEGIN
SELECT
id,
CASE WHEN @RoleLevel > 2
THEN first_name
ELSE REPLICATE('*', LEN(first_name))
END AS first_name,
last_name,
CASE WHEN @RoleLevel > 3
THEN email
ELSE LEFT(email, 2) + '***' + RIGHT(email, 4)
END AS email
FROM Customers;
END;
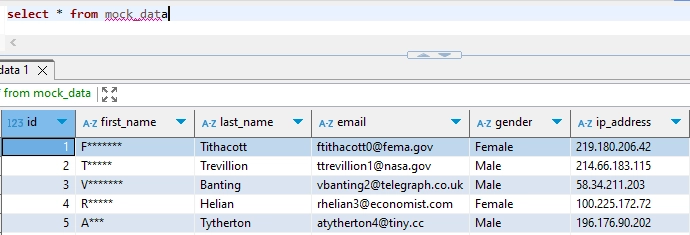
You can see the expected results below:
Using Command Line Interface
Cloudberry’s CLI provides essential tools for managing masking rules. Here are common commands:
# View existing masks cloudberry-cli --list-masks --database mydb # Apply new mask cloudberry-cli --create-mask --table Customers --column email --mask-type partial # Modify existing mask cloudberry-cli --modify-mask --mask-id EmailMask --new-type full
DataSunrise and Dynamic Data Masking for Cloudberry
While Cloudberry offers native dynamic data masking functionality, some organizations may seek additional security layers or centralized management of their masking policies. This is where DataSunrise comes into play. DataSunrise offers a comprehensive suite of database security tools, including dynamic data masking capabilities tailored for Cloudberry users.
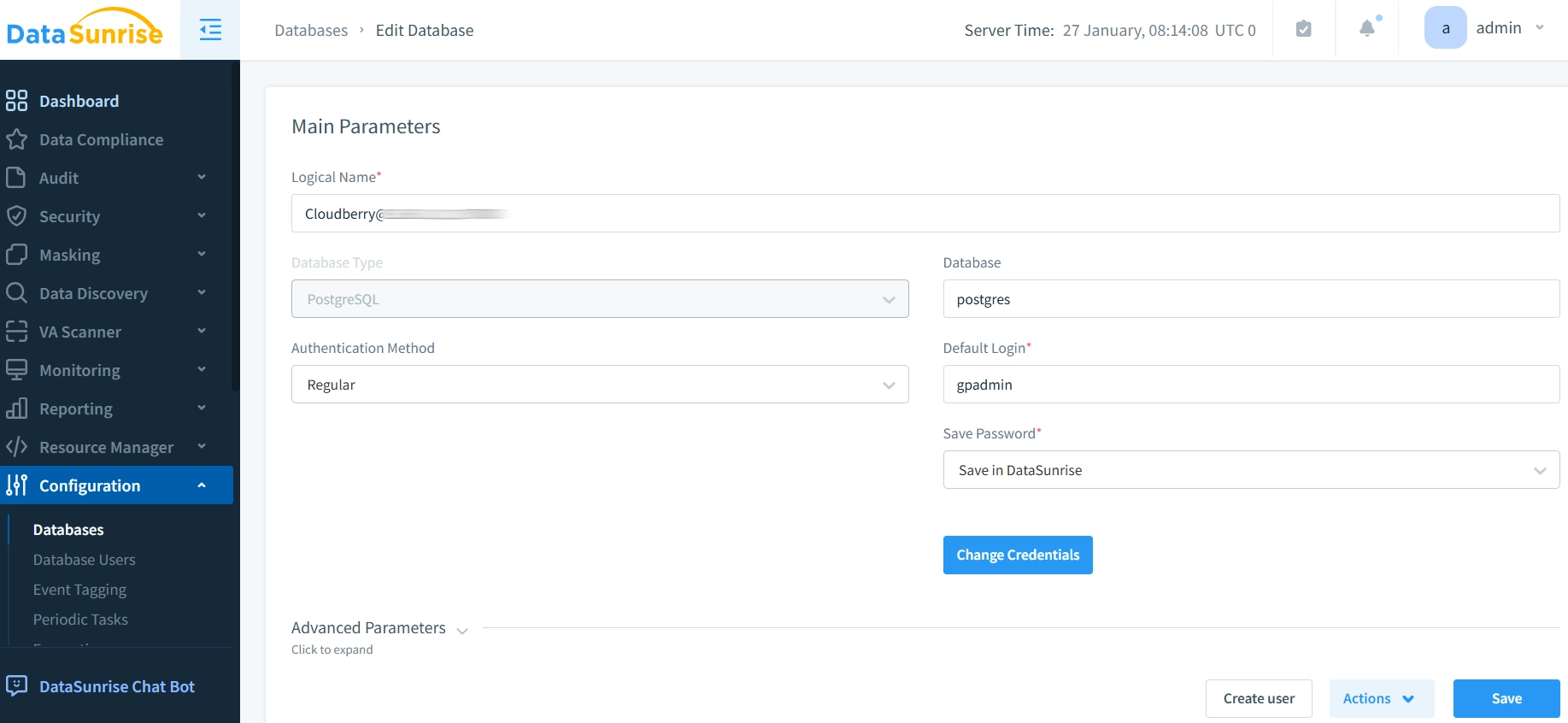
Setting Up DataSunrise for Cloudberry
- Install DataSunrise: Begin by installing DataSunrise on your system. You can do this on our website. There, you will find clear instructions for setting up the software for your database.
- Configure DataSunrise Instance: Once installed, configure a DataSunrise instance for the Cloudberry database. You need to connect DataSunrise to your Cloudberry database. To do this, provide the required authentication details. This includes the database type, server address, and your credentials.
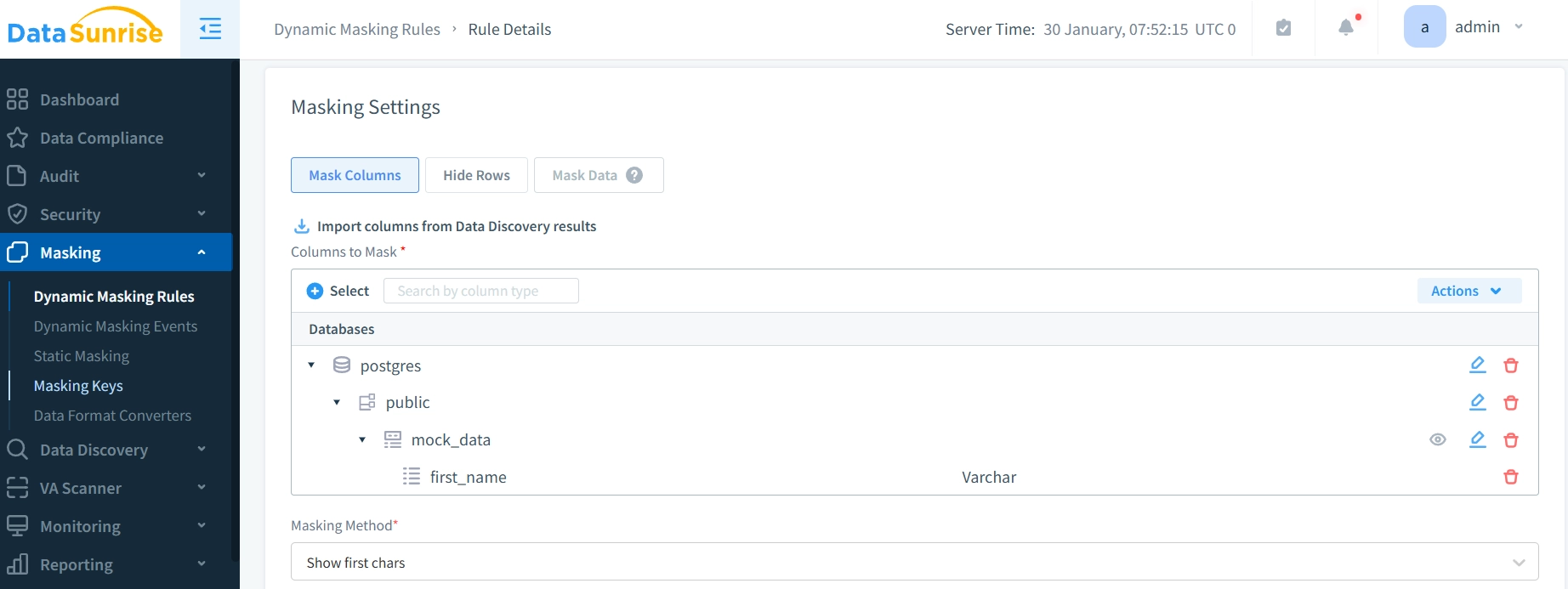
- Create Masking Rules: After you establish the connection, you can define dynamic data masking rules in the DataSunrise interface. You can make custom masking functions for different types of sensitive data. This includes PII, financial records, and other private information.
- Monitor and Control: DataSunrise provides a unified interface to monitor and control all your dynamic data masking rules. This centralized control ensures that your database’s security protocols are consistent across all applications, including Cloudberry. You can check the results of masking rules by using special programs like DBeaver.
Benefits of Using DataSunrise’s Dynamic Data Masking Suite
- Centralized Control: By using DataSunrise, database administrators can manage dynamic data masking policies across all databases and applications from a single platform.
- Improved Security: DataSunrise’s advanced masking tools boost Cloudberry’s built-in masking features. This allows users to have better control over how they mask and view data.
- Audit and Compliance: DataSunrise’s auditing features help organizations see who accesses sensitive data. This ensures they follow rules like GDPR and HIPAA.
- Flexibility: DataSunrise provides flexible tools to customize masking rules for your security needs. You can mask email addresses, financial data, or customer records easily.
Best Practices for Dynamic Data Masking
Data Classification: The foundation of effective data masking begins with thorough classification of your data assets. Organizations should identify and categorize sensitive information in their databases. They need to map out which fields need masking. Deciding the right masking levels for different user roles is also important.
Access Control: The principle of least privilege forms the cornerstone of access management in data masking. Using this approach makes sure that users can only see the least amount of unmasked data they need. This greatly lowers the risk of unauthorized data exposure.
Monitoring and Auditing: Regular system oversight maintains the effectiveness of your masking strategy. Regularly checking masking rules and access patterns helps find security gaps. This ensures that protection measures match changing business needs.
Testing Protocol: Comprehensive testing in development environments must precede any production deployment. This systematic approach allows organizations to verify that masking doesn’t interfere with application functionality while effectively protecting sensitive data.
Third-Party Integration: Modern security challenges often require advanced solutions like DataSunrise to enhance masking capabilities. These specialized tools provide centralized management, additional masking formats, and integrated security features that extend beyond Cloudberry’s native capabilities.
Documentation Standards: Clear record-keeping serves as the final pillar of a robust masking strategy. Maintaining detailed documentation of masking implementations, policies, and procedures ensures consistency in security practices and facilitates compliance reporting.
Enhance Your Security with DataSunrise
While Cloudberry’s native masking capabilities provide a solid foundation for data protection, DataSunrise takes database security to the next level. Our cutting-edge security suite offers flexible, comprehensive tools that go beyond basic masking. DataSunrise offers strong protection for modern organizations. It has features like advanced audit logging and real-time security monitoring. It also provides automated compliance reporting for GDPR, HIPAA, and other regulations.
For organizations seeking centralized control over their data masking policies and a comprehensive database security solution, DataSunrise’s advanced suite is a game-changer. Visit DataSunrise’s website today and schedule an online demo and learn how its flexible tools can help enhance your database security strategy.
