
Static Data Masking in IBM DB2

Static data masking for IBM DB2 transforms sensitive data in non-production environments while preserving database functionality. Organizations rely on database copies for development and testing, making effective masking essential for security.
IBM’s 2024 Cost of a Data Breach Report shows that breaches cost companies about $4.45 million. Of these breaches, 19% come from stolen credentials. Proper DB2 masking implementation helps prevent such incidents by protecting sensitive information across development and testing environments.
What is Static Data Masking?
Static data masking (SDM) changes sensitive data in a database. This makes the data unreadable or unusable. It does not change the structure of the data.
The main difference between static data masking and dynamic data masking is how they handle data. Static data masking changes the data itself. In contrast, dynamic data masking works with the data in real time when it is accessed. Static data masking is especially useful when testing, development, or training environments need to work with realistic data without exposing actual sensitive information.
In IBM DB2, you can use SQL queries, views, and stored procedures for static data masking. You can also use third-party solutions like DataSunrise.
IBM DB2 Native Static Data Masking
Overview of IBM DB2’s Native Data Masking Capabilities
IBM DB2 does not have a simple, one-size-fits-all data masking solution. However, it offers strong tools through SQL, views, and stored procedures. These tools help users create their own masking strategies. These features offer flexibility in terms of how and where the data is masked, without needing additional software solutions.
Here are some common native IBM DB2 techniques for static data masking:
- SQL Language Features: You can use SQL functions like REPLACE, SUBSTRING, or CONCAT to mask specific data fields.
- Views: By creating views on sensitive data, you can return masked data instead of the original.
- Stored Procedures: With DB2 stored procedures, you can create more complex masking rules. This allows you to change sensitive information according to your business needs.
Implementing Native Static Masking
Here’s a practical example using the provided test data structure:
-- Create masked view for employee data CREATE VIEW masked_employees AS SELECT id, TRANSLATE(first_name, 'abcdefghijklmnopqrstuvwxyz', 'xxxxxxxxxxxxxxxxxxxxxxxxxxx') AS first_name, TRANSLATE(last_name, 'abcdefghijklmnopqrstuvwxyz', 'xxxxxxxxxxxxxxxxxxxxxxxxxxx') AS last_name, CONCAT(SUBSTR(email, 1, 2), '****@', SUBSTR(email, POSSTR(email, '@') + 1)) AS email, REPLACE(ip_address, SUBSTR(ip_address, 1, POSSTR(ip_address, '.', 1, 2)), '*.*.') AS ip_address FROM employees;
Using DB2 Command Line Interface
Connect to your database and apply masking:
-- Connect to database
db2 connect to SAMPLE user db2admin using password
-- Execute masking procedure
db2 "CALL SYSPROC.ADMIN_CMD('MASK DATA USING POLICY mask_policy1')"
Creating Stored Procedures for Masking
Implement reusable masking logic:
CREATE PROCEDURE mask_personal_data() LANGUAGE SQL BEGIN -- Create temporary masked table DECLARE GLOBAL TEMPORARY TABLE masked_data AS (SELECT * FROM masked_employees) WITH NO DATA; -- Insert masked data INSERT INTO SESSION.masked_data SELECT * FROM masked_employees; END
Enhancing IBM DB2 Static Data Masking with DataSunrise
IBM DB2 has useful data masking features. However, they can be complex to set up and maintain. This is especially true in large environments. This is where third-party tools like DataSunrise come into play. DataSunrise is a comprehensive data security solution that provides advanced static data masking features, among other security capabilities.
Benefits of Using DataSunrise for IBM DB2 Static Data Masking
- Centralized Control: With DataSunrise, you can manage masking rules across multiple databases, ensuring uniformity and consistency in your security policies.
- Flexible Masking Rules: DataSunrise supports a wide range of masking techniques, from simple text replacement to advanced algorithmic transformations.
- Ease of Use: DataSunrise has a simple user interface. This makes it easy to apply and manage masking rules, even without technical skills.
- Compliance: DataSunrise helps you stay compliant with data privacy regulations by ensuring sensitive data is protected in non-production environments.
- Audit and Monitoring: DataSunrise has built-in tools for auditing and monitoring. These tools help you see your data masking activities. They also help you stay compliant with regulatory standards.
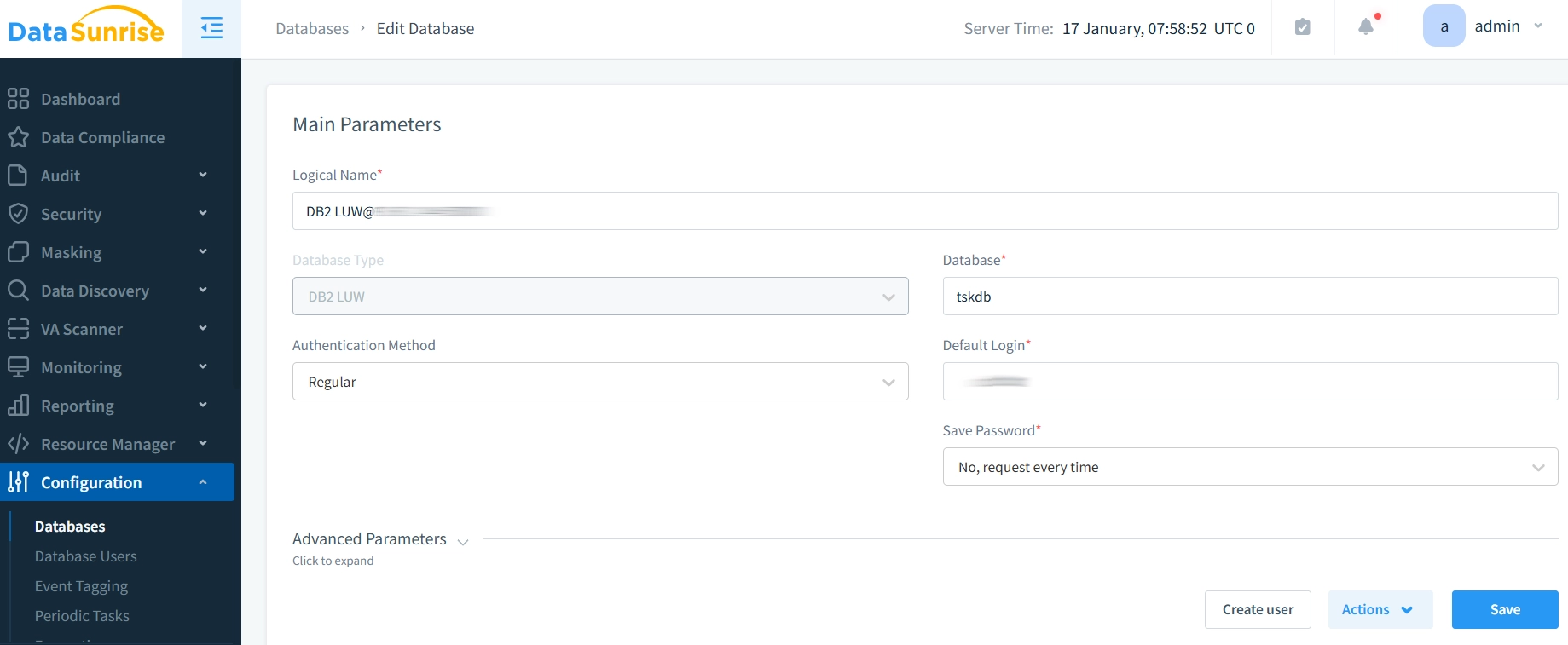
Creating a DataSunrise Instance for IBM DB2
Assuming DataSunrise is already installed, creating a new instance to manage static data masking for IBM DB2 is straightforward:
- Login to DataSunrise: Access the DataSunrise admin interface.
- Add IBM DB2 Database: Connect to your IBM DB2 instance. Provide the needed credentials, like database name, username, password, and host.
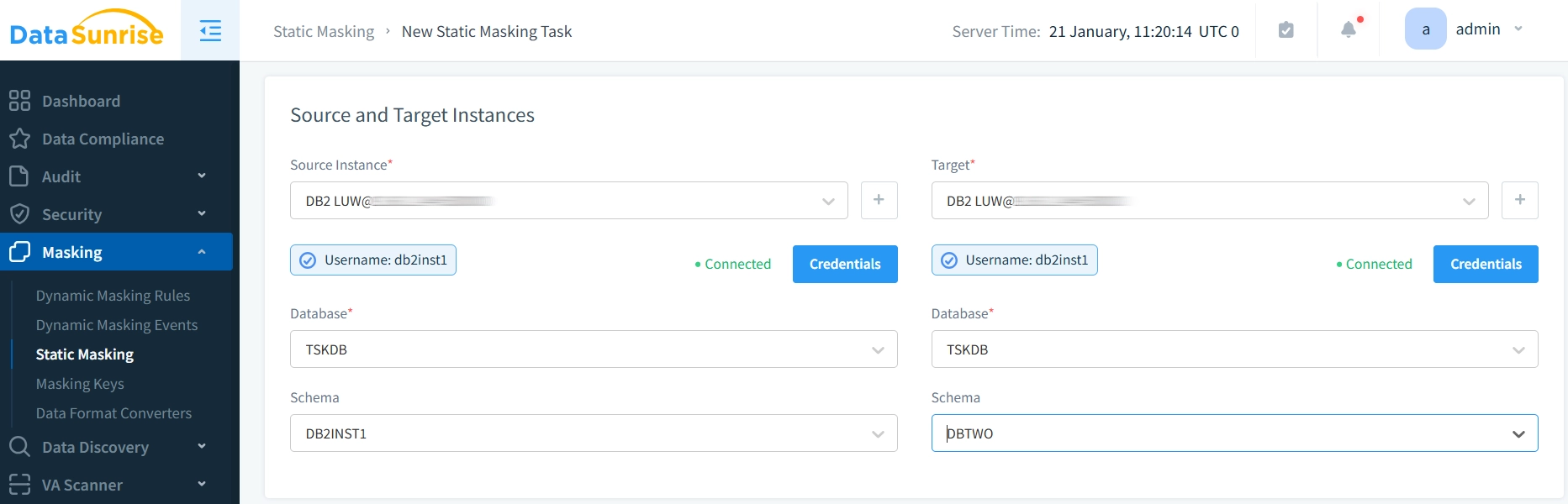
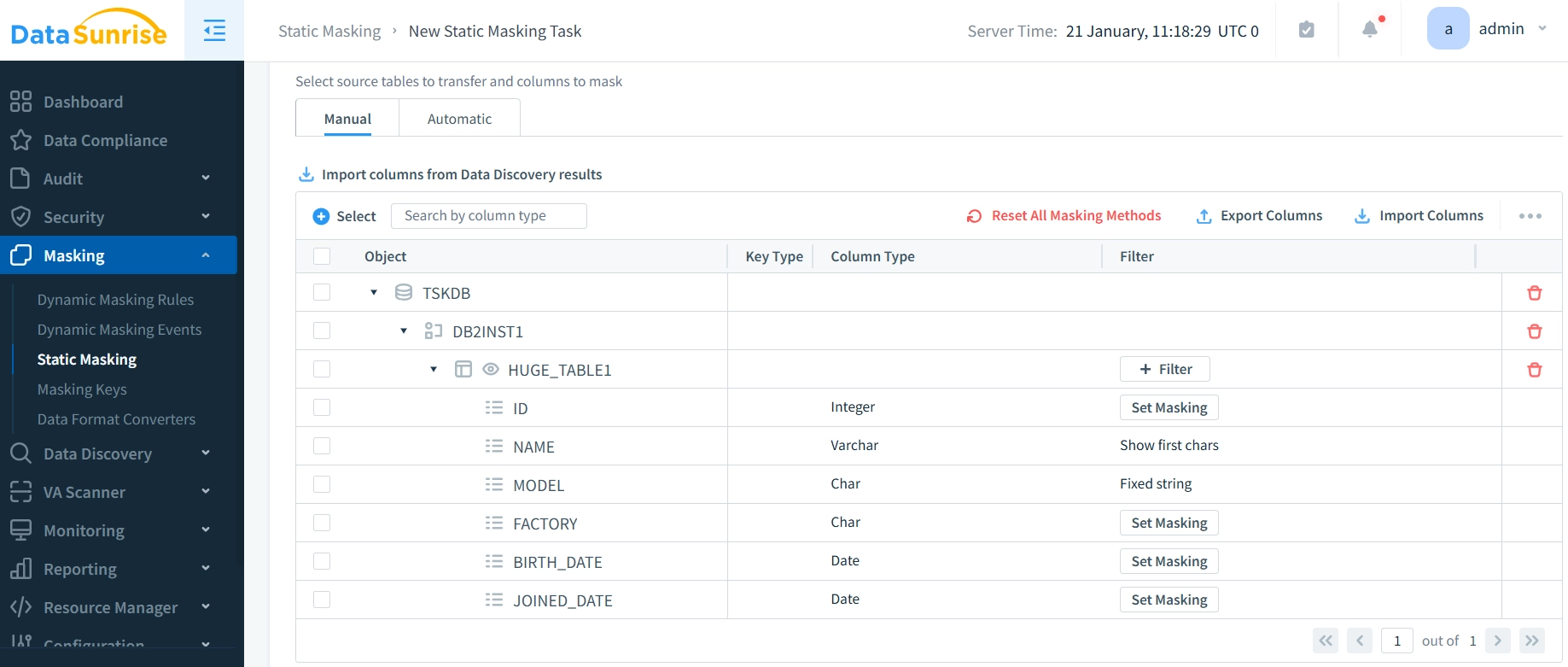
- Define Masking Rules: Create masking rules for each sensitive field (e.g., email, IP address) based on your business requirements. Choose from predefined rules or create custom patterns.
- Apply Masking: Once the rules are defined, you can apply them to the database, ensuring that sensitive data is masked across the environment.
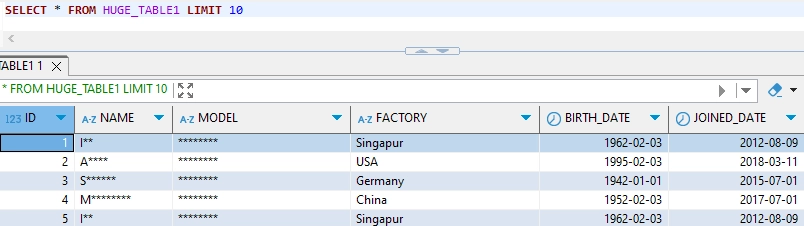
- Monitor Results: After you apply the masking rules, you can see the masked data. You can do this by querying the database or using DataSunrise’s reporting tools. DataSunrise gives detailed logs and reports. These help track masking activities. They ensure that all sensitive data is well protected.
Best Practices for DB2 Static Data Masking
Data Integrity: Effective static data masking in DB2 requires careful attention to data relationships and system performance. When implementing masking operations, start by ensuring referential integrity across your database. This means applying consistent masking rules to related tables and carefully preserving unique key constraints that maintain data relationships.
Performance: Performance considerations play a crucial role in successful masking implementation. Configure appropriate indexing for masked columns and schedule masking operations during periods of low database activity. Regular monitoring of system resources helps prevent impact on production workloads.
Security Management: Security controls form another essential component of masking strategy. Implement comprehensive access controls and maintain detailed audit logs of all masking operations. Consider using third-party solutions like DataSunrise to centralize security management and simplify compliance reporting.
Testing Strategy: Testing and validation should be integrated throughout the masking process. Regularly verify that masked data maintains its usability for development and testing while effectively protecting sensitive information. This includes validating masked data relationships and ensuring that masking rules meet compliance requirements.
Conclusion
Static data masking in IBM DB2 provides essential protection for sensitive information in non-production environments. While native DB2 features offer basic masking capabilities, DataSunrise’s comprehensive security suite delivers advanced features for enterprise-scale data protection.
Visit DataSunrise’s website to check out our advanced database security tools. We offer static data masking, dynamic data masking, database activity monitoring, and compliance management features. Schedule an online demo to see how DataSunrise can strengthen your DB2 data security strategy.
