
What is Aurora PostgreSQL Audit Trail?

Introduction
An Aurora PostgreSQL audit trail is a comprehensive record-keeping mechanism that captures and documents all significant database activities, providing organizations with critical insights into database interactions, access patterns, and potential security events. In an era of increasing cybersecurity threats and stringent compliance requirements, understanding and implementing robust database audit trails has become essential for protecting sensitive data and maintaining organizational integrity.
According to NIST Database Security Guide, robust database auditing is crucial for detecting unauthorized access attempts, monitoring privileged operations, and maintaining evidence for security investigations and forensics analysis. This guide outlines a practical implementation using AWS services.
Understanding Aurora PostgreSQL Audit Trail
An audit trail in Amazon Aurora PostgreSQL provides systematic tracking of database changes, essential for compliance and security monitoring. This guide outlines a practical implementation using AWS services.
Architecture Overview
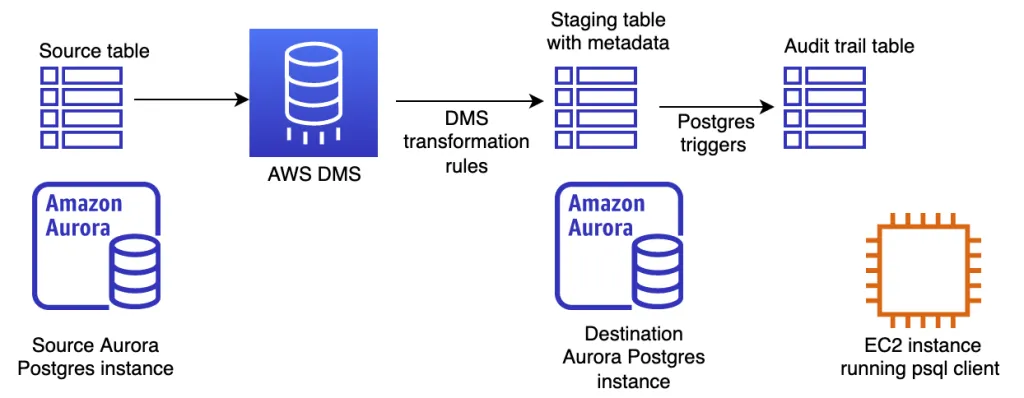
The audit system uses three core components:
- Source Database: Primary Aurora PostgreSQL instance
- AWS DMS: Change data capture service
- Destination Database: Audit log storage
Implementation Details
Enabling Audit Features
First, enable basic auditing in Aurora PostgreSQL:
-- Enable logging for all DDL operations
ALTER SYSTEM SET log_statement = 'ddl';
-- Enable logging for all operations
ALTER SYSTEM SET log_statement = 'all';
-- Enable connection logging
ALTER SYSTEM SET log_connections = 'on';
ALTER SYSTEM SET log_disconnections = 'on';
Schema Design
Source table example:
CREATE TABLE items (
item_id integer PRIMARY KEY,
name varchar(64),
price decimal(12,2),
created_at timestamp DEFAULT CURRENT_TIMESTAMP,
updated_at timestamp DEFAULT CURRENT_TIMESTAMP
);
Audit log table:
CREATE TABLE items_audit_log (
audit_id bigserial PRIMARY KEY,
item_id integer,
name varchar(64),
price decimal(12,2),
committed_at timestamp,
operation character(1),
transaction_id character varying,
old_row_data jsonb,
user_id text DEFAULT current_user
);
-- Create index for better query performance
CREATE INDEX idx_items_audit_committed_at ON items_audit_log(committed_at);
CREATE INDEX idx_items_audit_item_id ON items_audit_log(item_id);
Key Components of Aurora PostgreSQL Audit Trail

AWS DMS Configuration
- Uses
$AR_H_COMMIT_TIMESTAMPfor precise timing - Records operation types (I/U/D)
Example DMS task settings:
{
"TargetMetadata": {
"TargetSchema": "",
"SupportLobs": true,
"FullLobMode": false,
"LobChunkSize": 64,
"LimitedSizeLobMode": true,
"LobMaxSize": 32768
},
"FullLoadSettings": {
"TargetTablePrepMode": "DROP_AND_CREATE"
}
}
Trigger Function
CREATE OR REPLACE FUNCTION process_audit_trail()
RETURNS TRIGGER AS $$
BEGIN
IF (TG_OP = 'DELETE') THEN
INSERT INTO items_audit_log (
item_id, name, price, committed_at,
operation, transaction_id, old_row_data
)
VALUES (
OLD.item_id, OLD.name, OLD.price, CURRENT_TIMESTAMP,
'D', txid_current()::text, to_jsonb(OLD)
);
RETURN OLD;
ELSIF (TG_OP = 'UPDATE') THEN
INSERT INTO items_audit_log (
item_id, name, price, committed_at,
operation, transaction_id, old_row_data
)
VALUES (
NEW.item_id, NEW.name, NEW.price, CURRENT_TIMESTAMP,
'U', txid_current()::text, to_jsonb(OLD)
);
RETURN NEW;
ELSIF (TG_OP = 'INSERT') THEN
INSERT INTO items_audit_log (
item_id, name, price, committed_at,
operation, transaction_id, old_row_data
)
VALUES (
NEW.item_id, NEW.name, NEW.price, CURRENT_TIMESTAMP,
'I', txid_current()::text, NULL
);
RETURN NEW;
END IF;
RETURN NULL;
END;
$$ LANGUAGE plpgsql;
CREATE TRIGGER items_audit_trigger
AFTER INSERT OR UPDATE OR DELETE ON items
FOR EACH ROW EXECUTE FUNCTION process_audit_trail();
Query Examples
-- View recent changes
SELECT * FROM items_audit_log
ORDER BY committed_at DESC
LIMIT 10;
-- View changes for specific item
SELECT * FROM items_audit_log
WHERE item_id = 123
ORDER BY committed_at;
-- View changes by specific user
SELECT * FROM items_audit_log
WHERE user_id = 'admin'
AND committed_at >= CURRENT_DATE - INTERVAL '1 day';
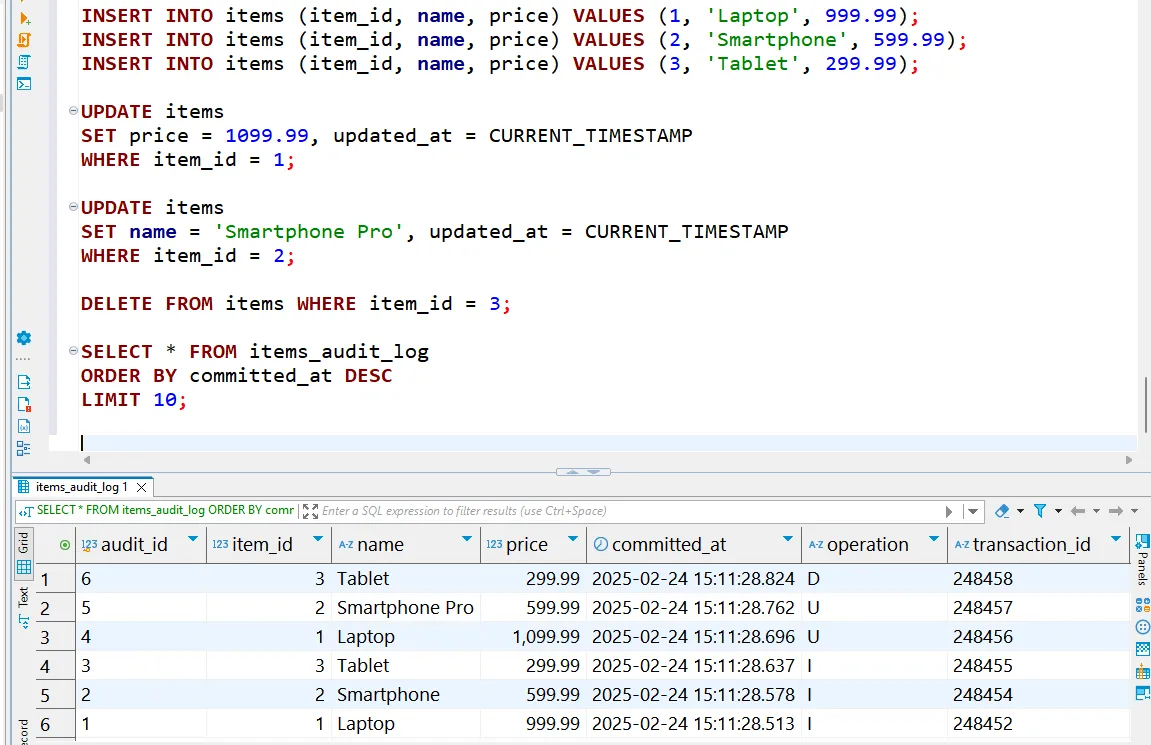
You can see the example queries and audit table output below:
Best Practices
- Monitor replication lag
- Encrypt data in transit and at rest
- Implement proper IAM roles
- Regularly archive old audit data
- Set up alerts for suspicious activities
For a detailed implementation guide, refer to the AWS Database Blog.
Advanced Features
For enhanced security, consider integrating with:
- AWS Database Activity Streams
- pgAudit PostgreSQL extension
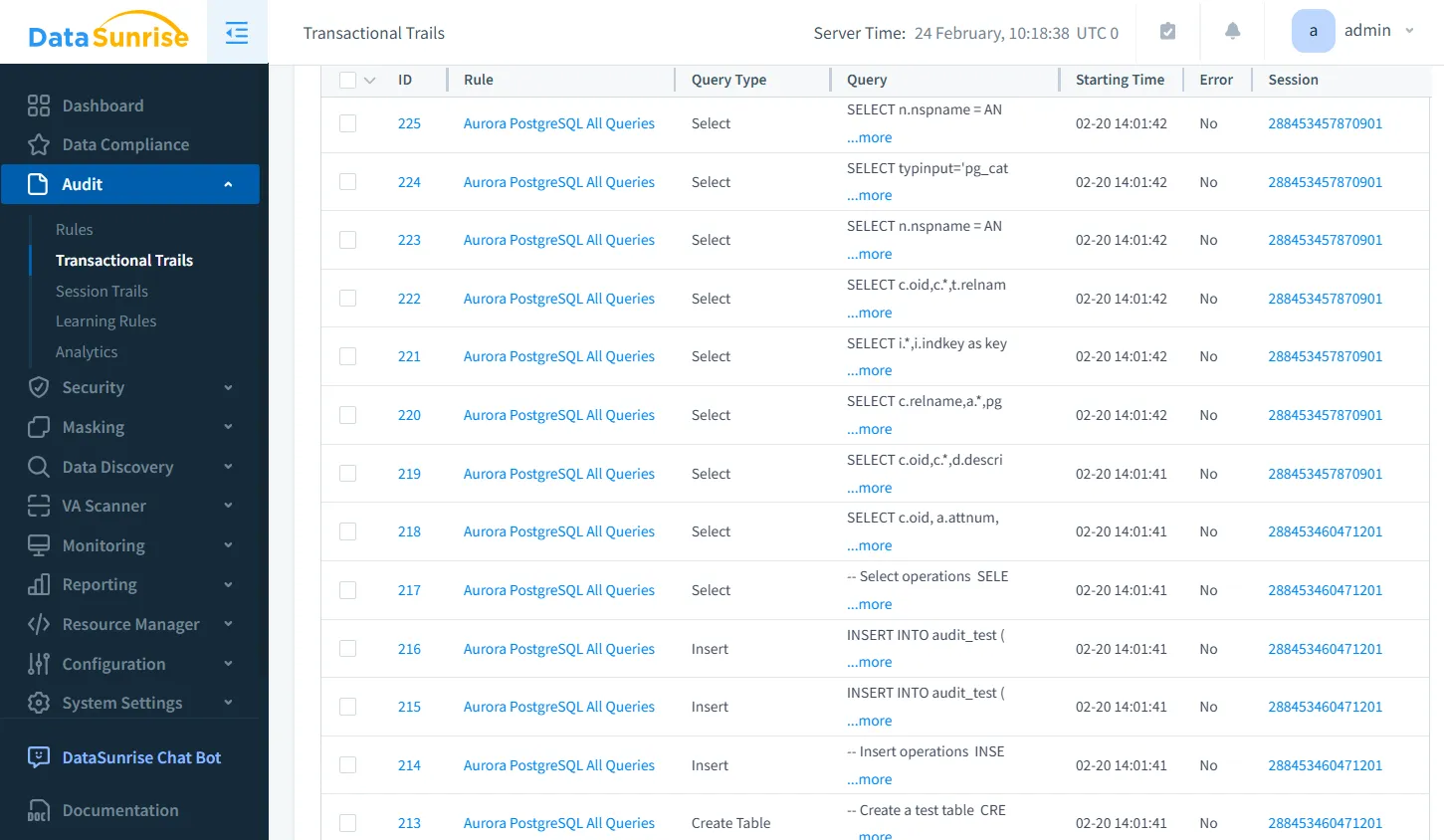
- DataSunrise for advanced auditing
DataSunrise: Comprehensive PostgreSQL Audit Trail Capabilities

While native audit tools provide essential tracking, DataSunrise Platform elevates audit trail capabilities for enterprise environments:
Enhanced Monitoring Features
- Intelligent Audit Rules:
- Customizable tracking mechanisms
- Precise control over monitored activities
- Behavioral Analytics:
- Detects unusual access patterns
- Identifies potential security threats
- Real-Time Alerting:
- Instant notifications of suspicious activities
- Proactive threat detection
Business Benefits of Aurora PostgreSQL Audit Trail Implementation
Enhanced Security
- Real-time threat detection and alerts
- Comprehensive forensic investigation capabilities
- Proactive identification of suspicious patterns
Regulatory Compliance
- GDPR, HIPAA, SOX, and PCI DSS adherence
- Automated compliance reporting
- Clear demonstration of security controls
Operational Efficiency
- Database performance optimization insights
- Complete visibility into user activities
- Streamlined audit processes and reporting
Conclusion
An audit trail for Amazon Aurora PostgreSQL is more than just a compliance requirement – it's a critical security and operational intelligence tool. While AWS provides powerful native auditing capabilities, enterprise environments benefit from additional layers of monitoring and analysis.
DataSunrise offers a comprehensive solution that extends native audit capabilities, providing deep insights, advanced threat detection, and seamless compliance management.
Take the Next Step
Ready to transform your audit trail strategy? Schedule a personalized demonstration and discover how advanced database security can protect your most valuable data assets.
