Sensitive Data Protection in IBM Db2
As enterprises grow increasingly reliant on relational databases to store their most critical assets, protecting sensitive information has never been more urgent. IBM Db2 handles everything from financial records and healthcare data to personally identifiable information—making sensitive data protection an operational priority rather than an afterthought. While Db2's comprehensive security architecture covers authentication, authorization, and auditing, organizations increasingly need to go further to meet modern compliance demands.
According to IBM's 2024 Cost of a Data Breach Report, the global average cost of a data breach has reached $4.88 million, with breaches involving regulated data types carrying steeper penalties. As a result, this article walks through IBM Db2's native sensitive data protection capabilities and demonstrates how DataSunrise can extend them with Zero-Touch Data Protection, automated compliance reporting, and intelligent behavioral analytics.
Understanding Sensitive Data in IBM Db2 Environments
Before configuring any protection mechanism, it is essential to understand what constitutes sensitive data in a typical Db2 deployment. To begin with, establishing a clear data security policy is the logical first step. Common sensitive data categories include PII (names, SSNs, email addresses) covered under GDPR, Protected Health Information governed by HIPAA, payment card data regulated by PCI DSS, and financial records subject to SOX compliance. In addition, understanding the full landscape of data compliance regulations that apply to your industry is essential before selecting protection controls. IBM Db2 provides native tools to address each of these categories, though they come with limitations that solutions like DataSunrise are designed to overcome.
Native IBM Db2 Sensitive Data Protection Capabilities
IBM Db2 offers several built-in mechanisms for protecting sensitive data at rest and in transit.
1. Label-Based Access Control (LBAC)
For multi-tiered security classifications, Db2 offers LBAC, which assigns security labels to both data rows and user credentials to ensure only users with matching clearance can access restricted information.
-- Create a security policy and classification labels
CREATE SECURITY POLICY data_classification
COMPONENTS sensitivity WITH DB2LBACRULES;
CREATE SECURITY LABEL data_classification.confidential
COMPONENT sensitivity 'CONFIDENTIAL';
-- Apply policy to a table and grant label to a user
ALTER TABLE finance.transactions SECURITY POLICY data_classification;
GRANT SECURITY LABEL data_classification.confidential TO USER finance_analyst;
2. Native Encryption and the db2audit Facility
IBM Db2 supports column-level database encryption via the built-in ENCRYPT function to protect data at rest, alongside SSL/TLS for data in transit. Additionally, the db2audit tool captures database activity that can be extracted and reviewed to confirm protection policies are being enforced correctly. This is especially important for detecting security threats early, before they escalate into full incidents.
# Enable auditing and capture data access events
db2audit start
db2audit configure scope dataaccess status both errortype normal
# Extract and review audit logs
db2audit extract file /tmp/db2audit.out from files /var/db2audit/
db2audit flush
For more details on event categories, refer to the IBM Db2 Audit Facility documentation.
Limitations of Native IBM Db2 Data Protection
While IBM Db2's built-in capabilities are enterprise-grade, organizations with evolving compliance obligations often find gaps when relying exclusively on native tools. Proper database security requires more than what any single platform's native tooling can offer, particularly when it comes to centralized audit logs and automated policy enforcement:
| Capability | Key Limitation | Business Impact |
|---|---|---|
| RCAC & Column Masking | Masking logic requires manual SQL authoring per column/table | Time-consuming to scale across large schemas |
| LBAC | Complex configuration requiring deep Db2 expertise | High administrative overhead; risk of misconfiguration |
| Native Encryption | Column-level encryption complicates queries and application logic | Development friction and performance degradation |
| db2audit | File-based logs require custom scripts for meaningful analysis | No real-time alerting or centralized dashboard |
| Compliance Reporting | No native automated mapping to GDPR, HIPAA, or PCI DSS formats | Audit preparation demands significant manual effort |
| Behavioral Analysis | No user behavior baselining or anomaly detection | Insider threats and data exfiltration may go undetected |
Enhanced Sensitive Data Protection for IBM Db2 with DataSunrise
DataSunrise deploys autonomous data protection technology to deliver seamless, enterprise-grade sensitive data security for IBM Db2. Unlike native tools that require SQL expertise and manual configuration per object, DataSunrise's No-Code Policy Automation lets security teams enforce sophisticated protection rules through an intuitive interface—reducing implementation time from weeks to hours. Furthermore, it operates in fully non-intrusive modes (sniffer, native log trailing, and proxy), ensuring existing Db2 applications experience zero disruption.
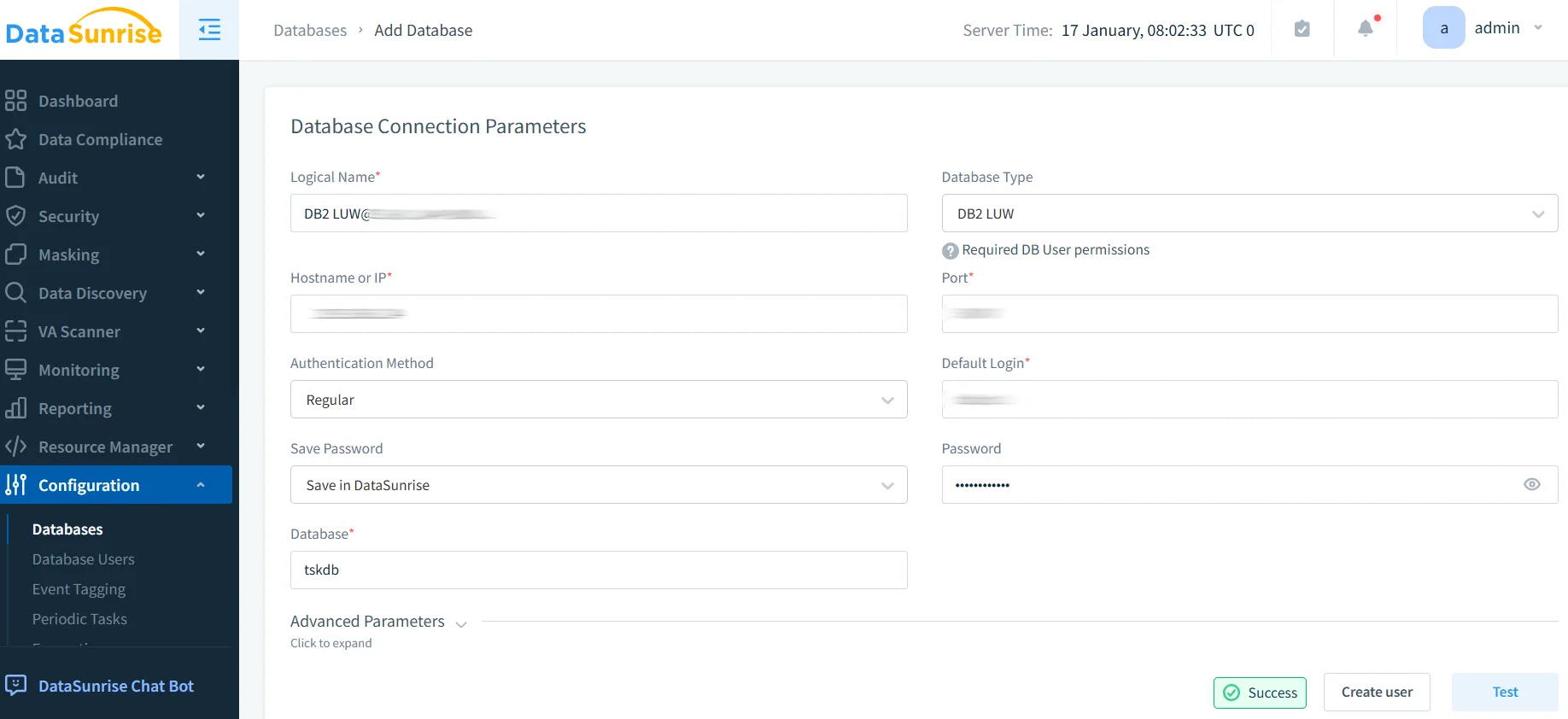
1. Connect IBM Db2 to DataSunrise
Establish a secure connection through the DataSunrise administrative interface by providing host, port, database name, and credentials. DataSunrise supports on-premise and cloud-hosted Db2 deployments (AWS, Azure, GCP), enabling consistent protection across hybrid environments. Importantly, applying the principle of least privilege during this setup ensures that DataSunrise itself operates with only the access it requires.
2. Auto-Discover Sensitive Data
DataSunrise's Data Discovery engine automatically scans your Db2 schema to identify columns containing sensitive information—PII, PHI, financial data—using NLP algorithms and pattern-matching rules aligned to regulatory frameworks. As a result, this eliminates manual cataloging and ensures no critical data falls outside your protection perimeter.
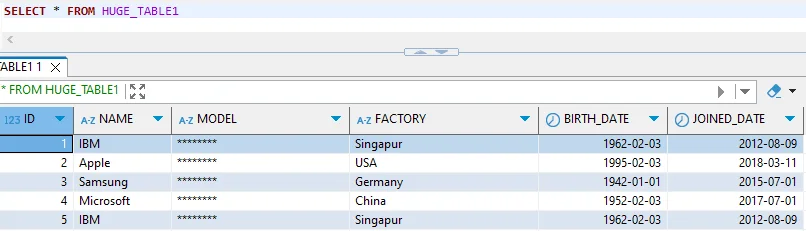
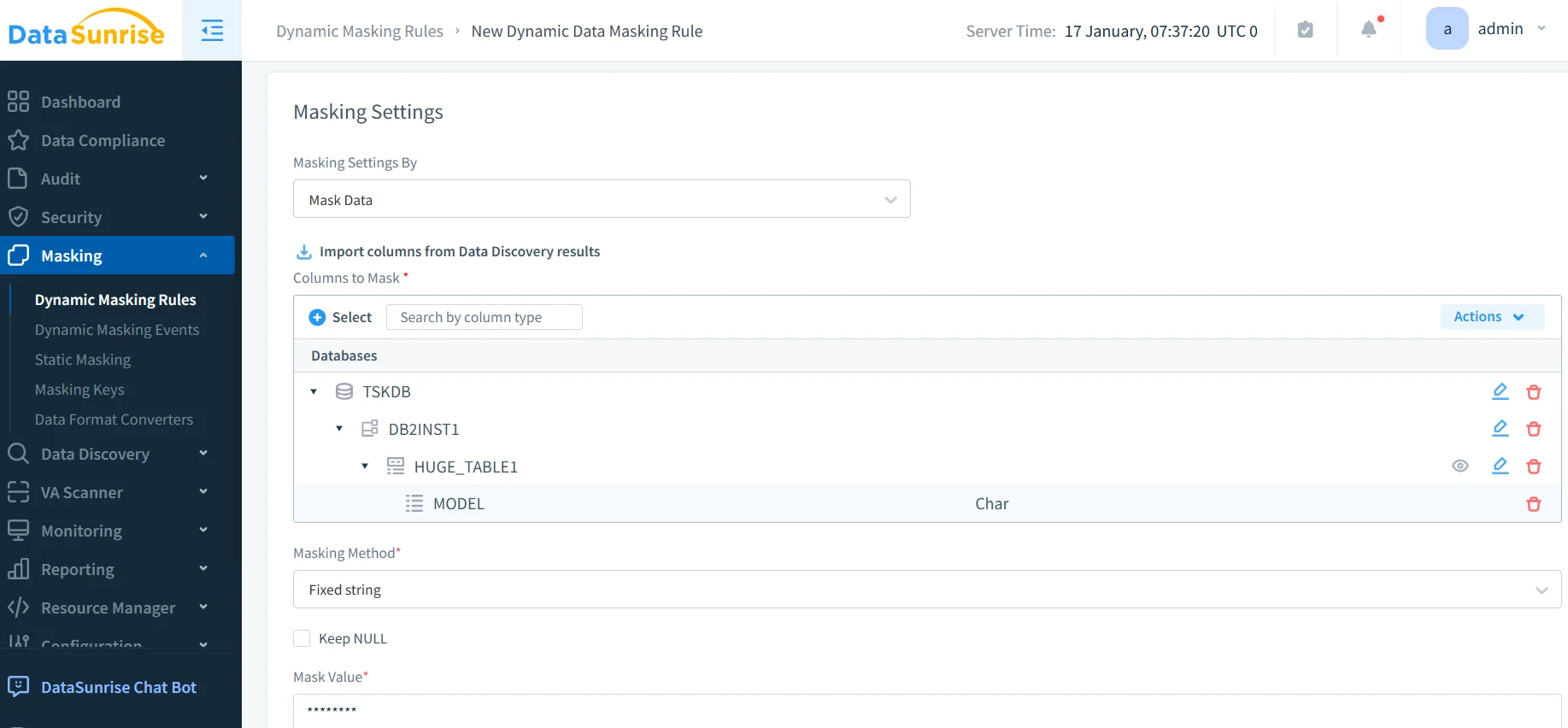
3. Configure Dynamic Data Masking Rules
Create dynamic data masking rules that apply contextual masking in real time based on user roles or access context. Unlike Db2's static column masks, DataSunrise's masking adapts automatically—authorized users see real data, while others receive masked output—with no schema changes or application modifications required.
4. Define Security Rules and Blocking Policies
Configure proactive security rules that block or alert on dangerous query patterns, including SQL injection attempts and bulk data exports. Together, these rules act as a database firewall, preventing sensitive data exfiltration before it occurs.
5. Monitor and Review Sensitive Data Access
Navigate to the DataSunrise Transaction Trails section to review a comprehensive, searchable log of all access events involving sensitive Db2 data—including user identity, query text, timestamp, and accessed objects. These detailed audit trails provide the forensic foundation needed for both internal investigations and regulatory audits. Moreover, the 'Create Rule' button in Event Details lets you instantly convert any observed event into an audit, masking, or security rule.
Key DataSunrise Advantages for IBM Db2 Sensitive Data Protection
- Auto-Discover & Classify: Automatically identify PII and regulated data types across your Db2 schema using ML and NLP—no manual inventory required.
- Dynamic Data Masking: Apply real-time, role-aware masking with surgical precision—no schema changes, no application modifications. For offline or test environments, static data masking is also available.
- Database Activity Monitoring: Gain a unified real-time view of sensitive data access across Db2 and over 40 supported platforms.
- Behavioral Analytics: Detect anomalies such as bulk reads of sensitive columns or off-hours access using ML-powered UEBA monitoring.
- Automated Compliance Reporting: Generate one-click compliance reports pre-mapped to GDPR, HIPAA, PCI DSS, and SOX.
- Real-Time Notifications: Receive instant alerts via email, Slack, or MS Teams when suspicious access is detected.
- Role-Based Access Controls: Enforce granular, policy-driven access governance across all Db2 users, complementing Db2's native controls with a centralized management layer.
- Flexible Deployment Modes: Deploy on-premise, in the cloud, or in hybrid environments without configuration complexity.
Conclusion
IBM Db2 provides a solid native foundation for sensitive data protection through RCAC, LBAC, encryption, and its audit facility. However, as data volumes grow and regulatory requirements multiply, native tools alone are insufficient for organizations that need scalable, automated, and centrally governed security.
DataSunrise bridges this gap—automatically discovering sensitive data, enforcing dynamic masking policies, detecting anomalous behavior, and generating audit-ready compliance reports across IBM Db2 and the broader data ecosystem. With flexible deployment options and no-code policy management, DataSunrise enables organizations of all sizes to achieve enterprise-grade protection without the overhead of traditional approaches.
Protect Your Data with DataSunrise
Secure your data across every layer with DataSunrise. Detect threats in real time with Activity Monitoring, Data Masking, and Database Firewall. Enforce Data Compliance, discover sensitive data, and protect workloads across 50+ supported cloud, on-prem, and AI system data source integrations.
Start protecting your critical data today
Request a Demo Download Now