
How to Audit CockroachDB

In today’s data-driven environment, maintaining a robust audit trail for your database is essential for both security and regulatory compliance. According to Verizon’s 2024 Data Breach Investigations Report, 48% of data breaches involve database misconfigurations or inadequate access controls, highlighting the critical need for comprehensive database security.
CockroachDB, a distributed SQL database designed for scalability and resilience, offers organizations the foundation needed for modern applications. However, as with any database system, implementing proper database auditing capabilities is crucial for maintaining security, meeting compliance regulations, and investigating potential incidents.
While CockroachDB doesn’t include a built-in, dedicated auditing system like some traditional databases, it provides powerful features that allow organizations to implement effective database protection. This article will guide you through setting up a comprehensive audit system for CockroachDB using both native capabilities and enhanced solutions like DataSunrise.
Native CockroachDB Auditing Capabilities
CockroachDB offers several approaches to implementing audit trails through its SQL functionality, system tables, and transaction logs. Let’s explore these native methods for creating effective audit mechanisms.
1. Creating Custom Audit Tables
The most straightforward approach to auditing in CockroachDB is creating dedicated audit tables. These tables store records of database activities, including who performed actions, what changes were made, and when activities occurred.
CREATE TABLE audit_trail (
id UUID DEFAULT gen_random_uuid() PRIMARY KEY,
timestamp TIMESTAMPTZ DEFAULT current_timestamp(),
username STRING NOT NULL,
action_type STRING NOT NULL,
table_name STRING NOT NULL,
query_text STRING,
affected_rows INT,
connection_info JSONB,
INDEX idx_audit_timestamp (timestamp DESC),
INDEX idx_audit_username (username),
INDEX idx_audit_table (table_name)
);
This table structure captures essential audit information:
- Unique identifier for each audit record
- Timestamp of the action
- User who performed the action
- Type of operation (INSERT, UPDATE, DELETE, SELECT)
- Affected table
- Original query text
- Number of rows affected
- Connection metadata
2. Implementing Triggers for Automated Auditing
To automate the auditing process, you can implement triggers that populate audit tables whenever changes occur in monitored tables. This approach creates a data activity history that tracks all database modifications. Here’s an example:
CREATE OR REPLACE FUNCTION record_table_changes()
RETURNS TRIGGER AS $$
BEGIN
IF (TG_OP = 'INSERT') THEN
INSERT INTO audit_trail (username, action_type, table_name, query_text, affected_rows)
VALUES (current_user, 'INSERT', TG_TABLE_NAME, current_query(), 1);
ELSIF (TG_OP = 'UPDATE') THEN
INSERT INTO audit_trail (username, action_type, table_name, query_text, affected_rows)
VALUES (current_user, 'UPDATE', TG_TABLE_NAME, current_query(), 1);
ELSIF (TG_OP = 'DELETE') THEN
INSERT INTO audit_trail (username, action_type, table_name, query_text, affected_rows)
VALUES (current_user, 'DELETE', TG_TABLE_NAME, current_query(), 1);
END IF;
RETURN NULL;
END;
$$ LANGUAGE plpgsql;
-- Apply trigger to a sensitive table
CREATE TRIGGER audit_users_table
AFTER INSERT OR UPDATE OR DELETE ON users
FOR EACH ROW EXECUTE FUNCTION record_table_changes();
3. Creating Audit Views for Analysis
Custom views make it easier to analyze audit data for specific security needs:
-- View for suspicious activities in the last 24 hours
CREATE VIEW recent_suspicious_activities AS
SELECT
timestamp,
username,
action_type,
table_name,
query_text
FROM
audit_trail
WHERE
timestamp > (current_timestamp() - INTERVAL '24 hours')
AND (
(action_type = 'DELETE' AND table_name IN ('users', 'permissions', 'financial_data'))
OR (username NOT IN (SELECT username FROM authorized_users))
OR (query_text LIKE '%DROP%' OR query_text LIKE '%TRUNCATE%')
)
ORDER BY
timestamp DESC;
Example view output:
| timestamp | username | action_type | table_name | query_text |
|---|---|---|---|---|
| 2024-02-20 15:42:18 | unknown_user | SELECT | financial_data | SELECT * FROM financial_data WHERE… |
| 2024-02-20 14:30:55 | admin | DELETE | users | DELETE FROM users WHERE last_login < '2023-01'... |
| 2024-02-20 13:22:10 | system_user | UPDATE | permissions | UPDATE permissions SET role=’admin’ WHERE… |
4. Utilizing System Tables for Authentication Monitoring
CockroachDB maintains internal system tables that track authentication attempts. You can query these tables to monitor login activities, providing database activity history capabilities:
-- View for monitoring authentication attempts
CREATE VIEW auth_monitor AS
SELECT
event_timestamp,
"eventType",
"targetName",
"applicationName",
"clientAddress"
FROM
system.eventlog
WHERE
"eventType" = 'CLIENT_AUTHENTICATION'
ORDER BY
event_timestamp DESC;
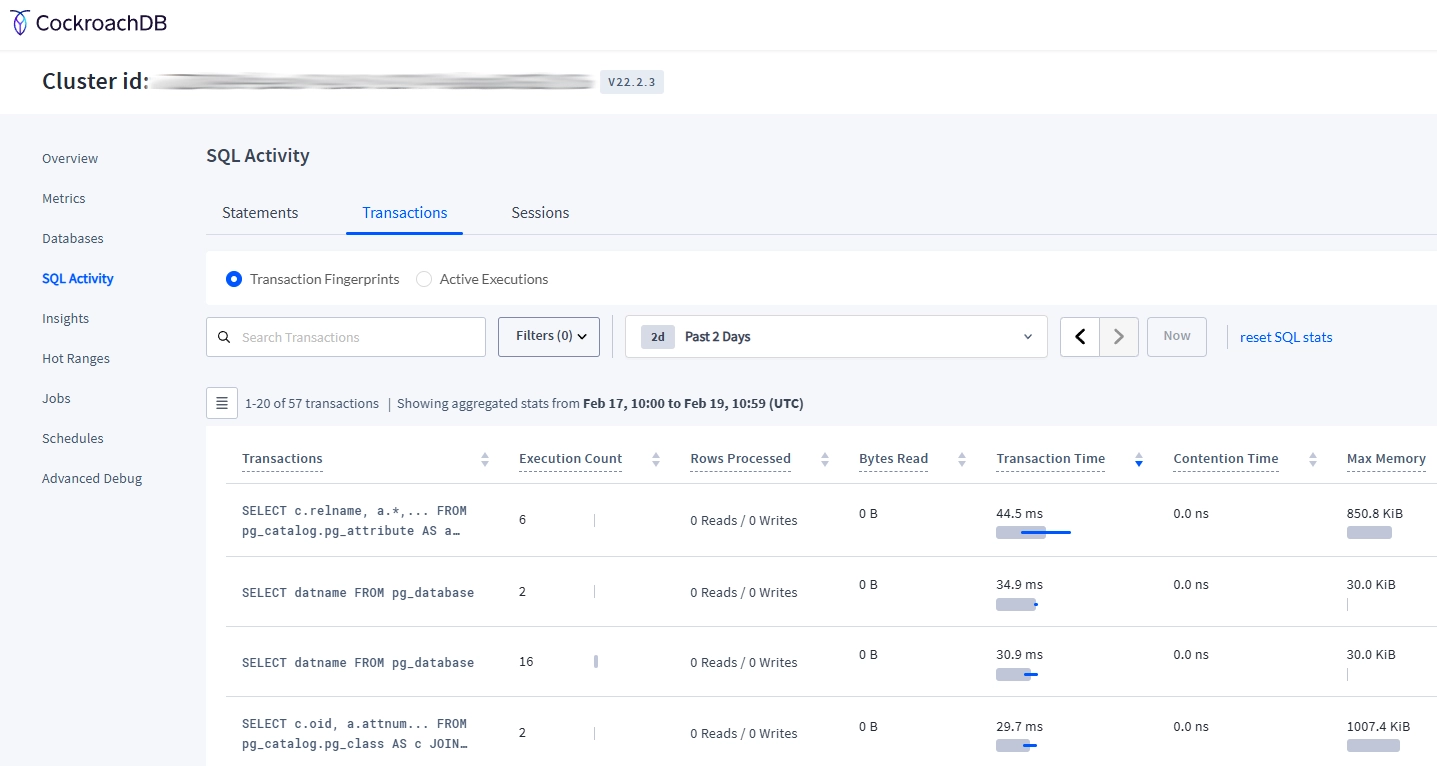
5. Using CockroachDB Web UI for Activity Monitoring
CockroachDB’s web-based administrative interface offers real-time monitoring capabilities that complement your audit implementation:
- Access the CockroachDB Admin UI (typically at http://localhost:8080)
- Navigate to the “SQL Activity” dashboard
- Review active queries, session information, and transaction metrics
- Monitor statement execution history for suspicious patterns
Limitations of Native CockroachDB Auditing
While CockroachDB’s native capabilities provide a foundation for auditing, they have several limitations:
- Manual Implementation: Requires custom creation of audit tables and triggers
- Limited Alerting: Lacks built-in notification capabilities for security threats
- Basic Reporting: Minimal support for compliance reporting requirements
- Management Complexity: Difficult to maintain consistency across growing deployments
Organizations with strict security or compliance needs may require enhanced solutions to address these limitations.
Enhanced Auditing with DataSunrise
DataSunrise provides comprehensive database security and auditing capabilities that significantly enhance CockroachDB’s native features. This integration delivers enterprise-grade monitoring, protection, and compliance management.
Key Benefits of DataSunrise for CockroachDB Auditing
- Comprehensive Audit Rules: Define granular policies based on users, operations, objects, and time periods.
- Real-Time Monitoring: Continuous observation of database activities with immediate alerts for suspicious events.
- Behavioral Analytics: AI-powered analysis of access patterns to detect anomalies and potential security threats.
- Dynamic Data Masking: Protect sensitive information in audit trails while maintaining visibility for authorized personnel.
- Automated Compliance Reporting: Pre-built report templates for GDPR, HIPAA, SOX, and PCI DSS requirements.
- Multi-Database Support: Unified interface for managing audit policies across multiple database platforms.
Implementing DataSunrise for CockroachDB Auditing
Connect to CockroachDB Instance
- Access the DataSunrise dashboard
- Create a new database connection
- Enter your CockroachDB connection details (host, port, authentication credentials)
- Test and save the connection
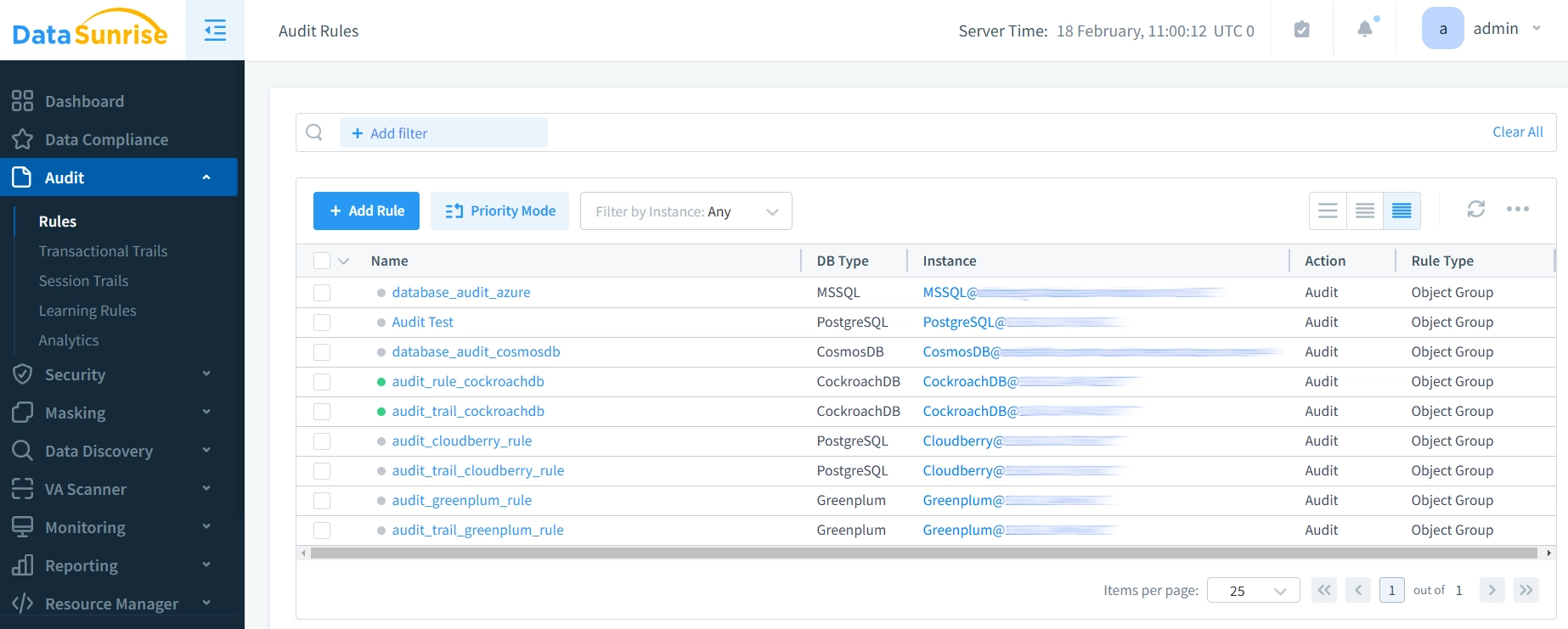
Configure Audit Rules
Create customized audit rules to specify which database activities should be monitored:
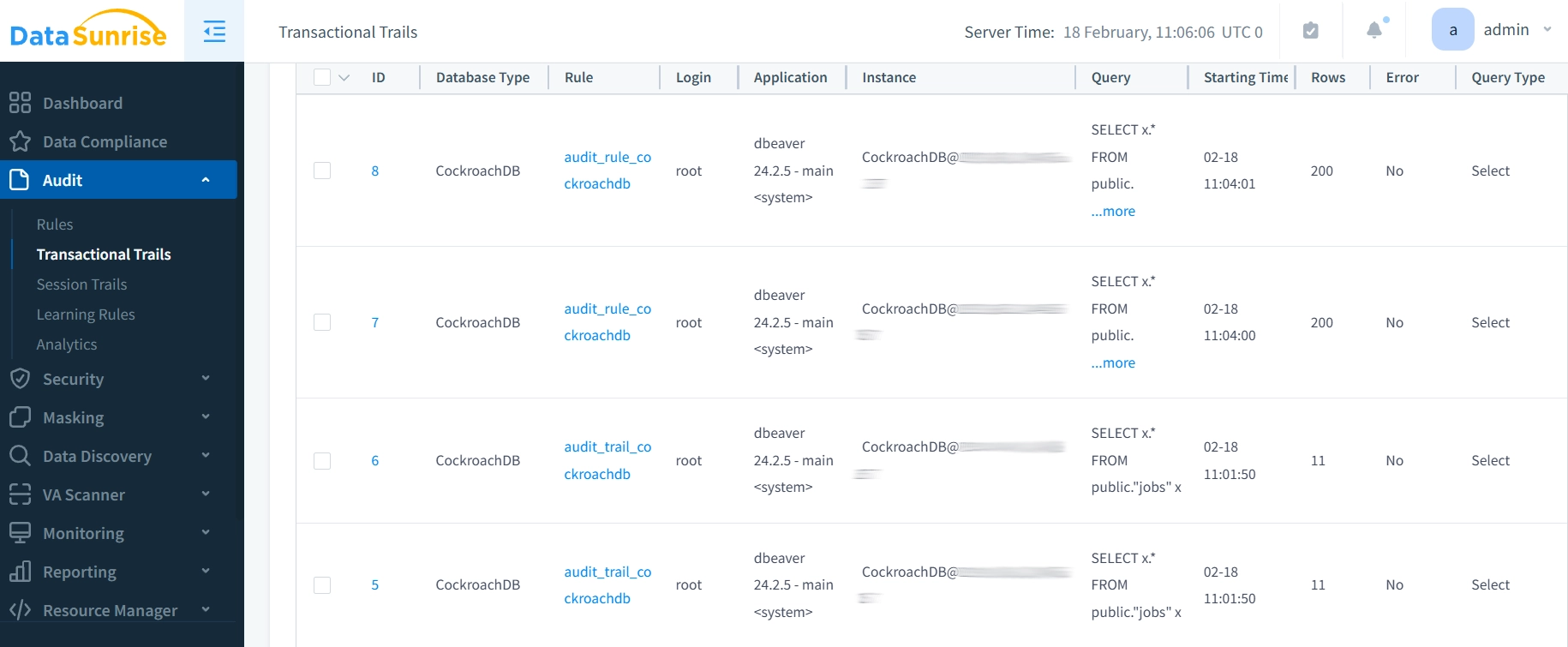
Monitor Audit Trails
Access comprehensive audit logs through the DataSunrise interface:
Best Practices for CockroachDB Auditing
1. Performance Optimization
- Selective Auditing: Only audit essential tables and operations to minimize performance impact
- Efficient Indexing: Create appropriate indexes on audit tables for faster query performance
- Audit Storage Management: Implement automatic archiving of older audit records
- Batch Processing: Consider asynchronous audit logging for high-transaction environments
- Regular Maintenance: Monitor audit table growth and performance impact
2. Security Implementation
- Protect Audit Data: Implement encryption for audit logs at rest and in transit
- Separation of Duties: Ensure audit administrators cannot modify the logs they oversee
- Access Controls: Apply role-based access controls to audit information
- Tamper Prevention: Implement checksums or digital signatures to detect log tampering
- Secure Transmission: Use encrypted channels for audit data collection and reporting
3. Compliance and Documentation
- Audit Logs: Periodically test audit logs completeness and accuracy
- Chain of Custody: Establish protocols for handling audit data during investigations
- Compliance Mapping: Document how audit implementations satisfy specific regulatory requirements
4. Monitoring and Analysis
- Regular Reviews: Establish scheduled audit log review procedures
- Baseline Establishment: Define normal behavior patterns to identify anomalies
- Alert Thresholds: Configure notification thresholds based on risk profiles
- Correlation Analysis: Integrate audit data with other security information for comprehensive threat detection
- Visualization: Implement dashboards for security metrics and compliance status
5. Third-Party Solution Integration
- Specialized Tools: Implement solutions like DataSunrise for enhanced audit capabilities
- Centralized Management: Utilize unified platforms to manage security across multiple database clusters
- Automated Compliance: Leverage pre-built compliance templates and reporting features
- Advanced Analytics: Employ role-based access controls and machine learning for threat detection
- Real-Time Notifications: Configure instant notifications through third-party security platforms
Conclusion
Effective auditing is essential for CockroachDB environments, providing both security assurance and compliance capabilities. While CockroachDB’s native features offer a foundation for basic auditing, organizations with advanced requirements benefit from comprehensive solutions like DataSunrise.
By combining CockroachDB’s scalable architecture with robust data audit trails, organizations can maintain visibility, ensure compliance, and protect critical data assets. Whether implementing custom audit tables or leveraging advanced security platforms, establishing a comprehensive audit strategy should be a priority for any organization using CockroachDB in production environments.
For organizations seeking to enhance their CockroachDB security posture, DataSunrise offers specialized solutions that address advanced auditing needs while simplifying compliance management. Through centralized control, real-time monitoring, and sophisticated analytics, DataSunrise provides the tools needed to maintain robust database security in today’s challenging threat landscape.
Ready to strengthen your CockroachDB security with advanced auditing capabilities? Schedule a demonstration to see how DataSunrise can enhance your database protection strategy.
