NLP, LLM & ML Data Compliance Tools for YugabyteDB
Introduction
YugabyteDB is architected for distributed workloads, but aligning its native capabilities with regulatory frameworks such as GDPR, HIPAA, PCI-DSS, and SOX requires more than baseline encryption and access control. These standards call for sustained visibility, auditability, and a degree of automation not available through out-of-the-box configurations alone.
This article explores YugabyteDB’s built-in support for data compliance, along with methods for improving governance and automation using third-party tools like DataSunrise. For background, see the supporting study on compliance challenges. Additional implementation guidance is available in the YSQL audit logging documentation.
Compliance Requirements and Gaps
GDPR
The General Data Protection Regulation emphasizes user consent, access transparency, and data minimization. YugabyteDB offers:
- Role-Based Access Control (RBAC)
- TLS for in-transit security
- AES-256 encryption at rest
- Audit logging using PostgreSQL’s
pgaudit
Yet it lacks runtime data masking and automated user-specific visibility restrictions.
HIPAA
To meet HIPAA requirements for PHI (Protected Health Information), organizations must enforce audit trails, data segmentation, and access justification. YugabyteDB supports:
- Session and object-level audit logging
- Encrypted storage and transport layers
- Fine-grained access policies via RBAC
However, enforcement still depends on manual monitoring and lacks adaptive breach detection.
PCI-DSS
Credit card data requires masking, access logs, and restricted views. YugabyteDB enables:
- Privilege assignment to isolate access
- Logging of DDL/DML activity
But native tools do not provide masking at query time or centralized alerting for anomalous access.
SOX
The Sarbanes-Oxley Act prioritizes traceability and accountability in financial data systems. While YugabyteDB supports:
- Session tracking through PostgreSQL logs
- Object-specific logging with
pgaudit
It does not include built-in reporting tools or continuous validation checks.
Configuring Native Audit Logging in YugabyteDB
YSQL: Session and Object-Level Logging
Audit logging in YugabyteDB’s YSQL layer is driven by PostgreSQL’s pgaudit extension.
Enable audit logging at cluster startup:
--ysql_pg_conf_csv="log_line_prefix='%m [%p %l %c]'", pgaudit.log='write, ddl', pgaudit.log_parameter=on, pgaudit.log_relation=on
Activate the extension within SQL:
CREATE EXTENSION IF NOT EXISTS pgaudit;
Example of object-level access tracking:
CREATE ROLE auditor;
SET pgaudit.role = 'auditor';
CREATE TABLE transactions (
id SERIAL PRIMARY KEY,
amount INT,
customer_id INT,
created_at TIMESTAMP DEFAULT now()
);
GRANT SELECT, INSERT ON transactions TO auditor;
SELECT * FROM transactions;
This configuration logs each statement involving the transactions table if executed by or on behalf of the auditor role.
Session Tracing
To improve traceability, configure log_line_prefix with session and process metadata:
--ysql_pg_conf_csv="log_line_prefix='timestamp: %m pid: %p session: %c '", ysql_log_statement=all
Sample log output:
timestamp: 2025-03-20 14:05:33.184 UTC pid: 1930 session: 6356c208.78a LOG: statement: INSERT INTO transactions VALUES (101, 200, 5);
This information can help in mapping specific data changes to session-level user activity.
YCQL Audit Logging
For transactional workloads via the YCQL API, enable audit logging at the node level:
--ycql_enable_audit_log=true
Example of YCQL query logging:
BEGIN TRANSACTION; UPDATE customer_balance SET balance = balance - 100 WHERE id = 101; COMMIT;
These events are recorded with metadata such as client IP, node ID, and table name—important for PCI-DSS and SOX visibility. Learn more in the audit guide.
Operational Example: Hybrid YSQL and YCQL Security
In many deployments, YSQL manages normalized relational data, while YCQL handles denormalized high-throughput access patterns. For instance, a support application might use YSQL for customer records and YCQL for audit logs or cache.
Restrict access to support roles in YSQL:
CREATE ROLE support_user WITH LOGIN PASSWORD 'supp0rt!'; GRANT SELECT ON customers TO support_user;
Track related access in YCQL logs:
tail -f ~/var/data/yb-data/tserver/logs/cassandra-audit.log
This design supports high availability while preserving clear access boundaries and traceability.
Extending Governance with DataSunrise
Centralized Masking and Visibility Control
DataSunrise introduces dynamic masking to YugabyteDB environments. Sensitive fields like credit_card_number or ssn can be masked on-the-fly based on user roles.
Unmasked vs. masked access:
SELECT full_name, credit_card_number FROM customers;
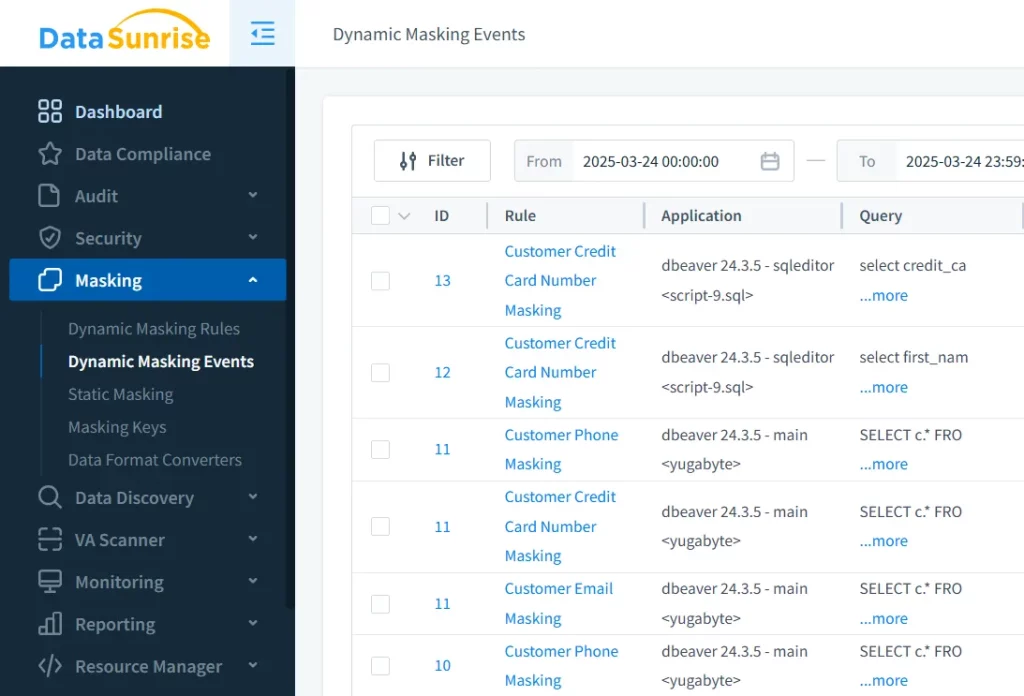
This ensures PCI-DSS and HIPAA controls are enforced consistently.
No-Code Policy Automation
Through a centralized interface, DataSunrise enables compliance management and deployment without scripting. Teams can define rules based on compliance frameworks and apply them across cloud and on-prem environments.
DataSunrise platform allows you to granularly adjust your compliance setup to follow strict regulations
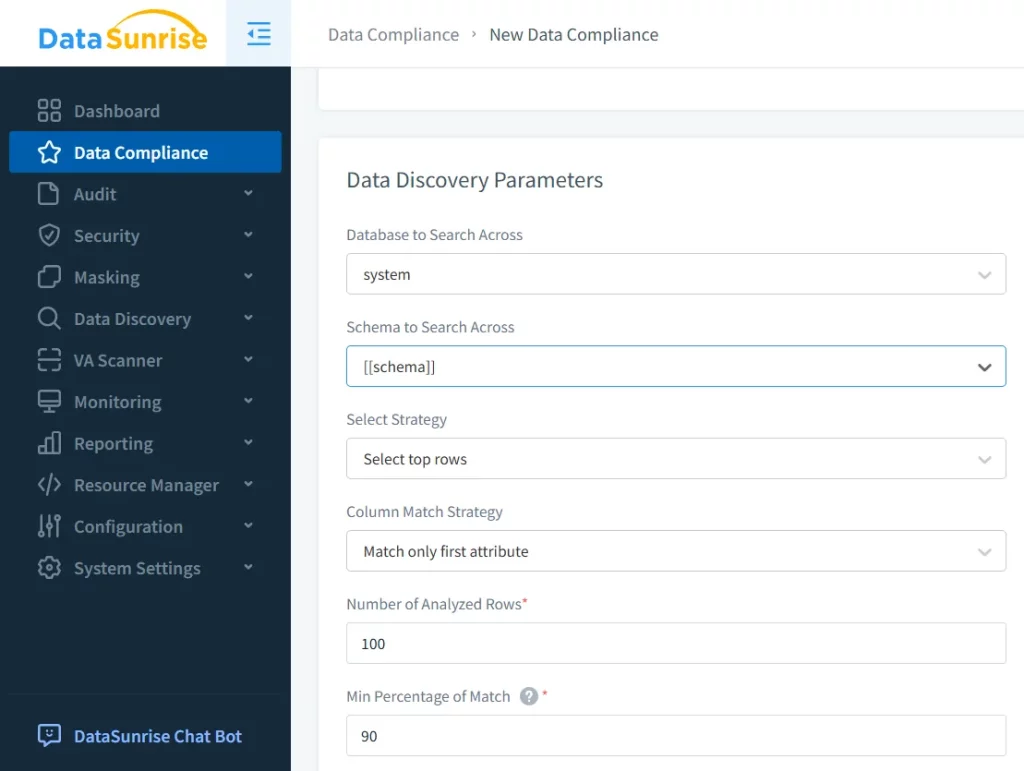
These policies can include masking, alert thresholds, and access controls tied to GDPR or SOX guidelines.
Real-Time Auditing and Anomaly Detection
In contrast to YugabyteDB’s passive logging, DataSunrise introduces:
- Compliance-driven audit rules
- Advanced User behavior analytics
- Alert forwarding to external tools via Notifications system
This enables proactive threat detection and risk remediation.
Implementation Considerations
DataSunrise integrates with YugabyteDB via:
- Proxy mode for inline query processing
- Sniffer mode for passive monitoring
- Log trailing for environments with restricted access
These flexible deployment options allow organizations to implement governance controls without changes to application code or architecture.
Conclusion
YugabyteDB provides foundational capabilities for data compliance through encryption, RBAC, and audit logging. However, to meet enterprise expectations for automation, masking, and real-time monitoring, a complementary platform like DataSunrise becomes essential.
With DataSunrise, teams gain centralized control over data access policies, dynamic data masking, and intelligent audit automation across YSQL and YCQL interfaces.
To explore how DataSunrise strengthens YugabyteDB compliance:
- Visit Data Compliance
- Learn more at the Regulatory Compliance Knowledge Center
