DataSunrise Database Firewall for Amazon Aurora
DataSunrise is an Advanced Amazon APN Technology Partner in data and database security. On AWS Database Blog: Monitor Amazon Aurora database activities using DataSunrise Database Security. Amazon Aurora firewall by DataSunrise provides strong protection of business critical data from unauthorized access and malicious attacks. SQL injection protection, user privileges control, data leak prevention – corporate data remain secure both in production and non-production environments.
Amazon Aurora firewall by DataSunrise is database monitoring and protection tool. It is a perfect way to ensure 24/7 database security and maintain complete control over sensitive data in production and development/test environments. It ensures that organizations reach the required level of data security and successfully avoid compliance risks.
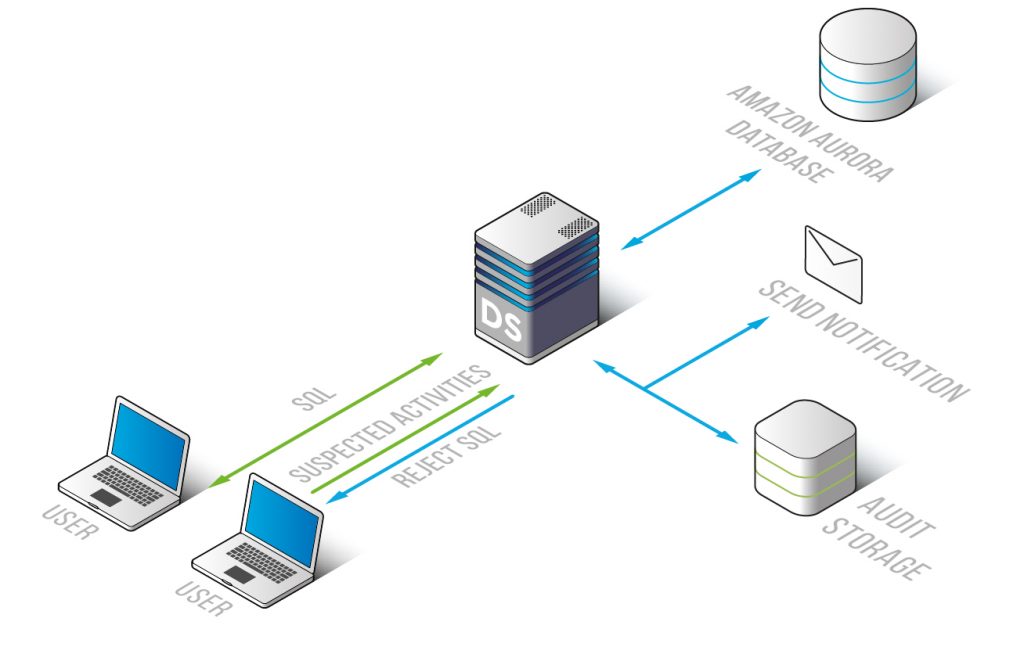
The firewall continuously monitors user activity and detects unusual and prohibited activity. With detailed logging, DataSunrise accurately tracks and keeps a record of user behavior and changes of data. Log information is then used to continuously monitor activity and prevent attacks, leaks, attempts of legitimate access rights abuse, etc.
Special algorithms detect and block database vulnerabilities that can be potentially exploited by negligent or malicious insiders. This helps to control data exposure to different groups of users and avoid the fundamental risk of privileged user abuse as database administrators are a source of potential danger to business data security as well.
The firewall operates as a proxy – it is placed between client and database and dramatically reduces a database’s attack surface, as DataSunrise database firewall detects SQL injections and a wide range of attack signatures.
The firewall recognizes and blocks SQL injections in real time. Among the recognized SQL injection techniques there are:
- Union Exploitation Technique
- Boolean Exploitation Technique
- Out of band Exploitation technique
- Time delay Exploitation technique
- Automated Exploitation
Rule conditions include the following parameters:
- type, instance and name of the target database;
- whether queries came from a certain client application;
- whether intercepted queries contain certain SQL statements;
- whether queries contain signs of SQL injection (OR and UNION statements, comments, double queries, constant expression, keyword in comments);
- whether queries are directed to certain database elements (schemas, tables, columns, stored procedures).
Amazon Aurora firewall by DataSunrise integrates seamlessly with third-party Security Information and Event Management solutions (SIEM). This helps to analyze database transactions and user behavior on a more advanced level. Integrated with a SIEM system DataSunrise becomes an essential part of enterprise-wide risk management security strategy and helps organizations meet regulatory and compliance requirements.