DataSunrise Database Firewall for SAP HANA
SAP HANA security solution by DataSunrise is a comprehensive enterprise-class tool designed to protect the integrity and confidentiality of sensitive data. Intercepting each incoming database query firewall analyzes using sophisticated self-learning algorithms and blocks it if the query violates any security policy. It provides prevention of privilege abuse, SQL injections, and other hacking attempts. Convenient settings allow to adjust firewall for different corporate needs.
DataSunrise provides SAP HANA security tools to protect databases against inside and outside threats, helping to comply with security and privacy mandates, such as HIPAA, SOX, PCI-DSS. Firewall is easy to deploy and to work with. It functions as an intermediary between a server and its users, so that all commands go through the firewall. SAP HANA firewall by DataSunrise compares attributes of the query with parameters of security policies and allows its execution in case the command doesn’t contain any malicious code, otherwise the query is blocked.
The main threat of data breach comes from company employees. It is very important to use relevant security tools for access privilege assignment. Rule settings allow to restrict access according to IP address, host name, used application or access to certain elements of the database (tables, columns). There is also an opportunity to set a schedule of policy operation.
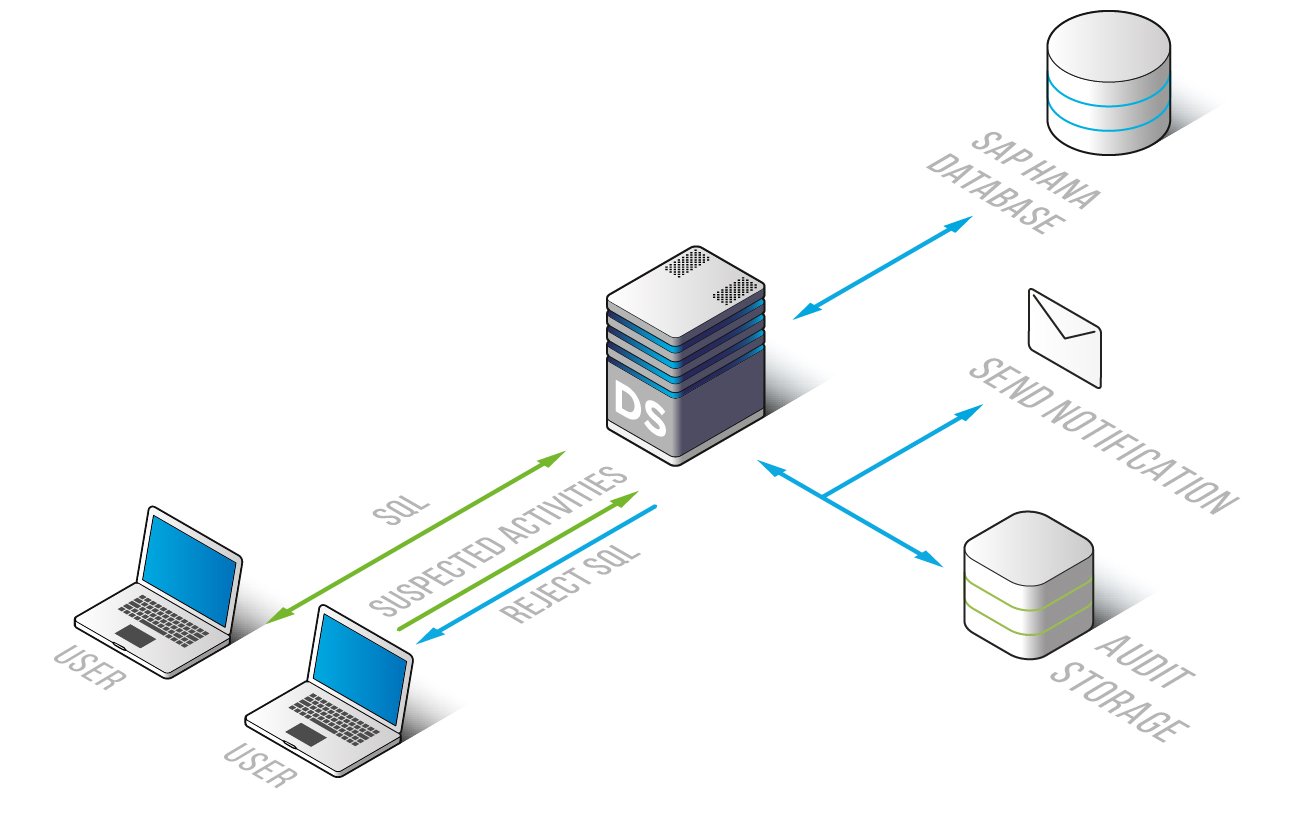
Detailed information about all queries and results of their execution is documented, including operations of privileged users. With DataSunrise you get full visibility of what’s going on in the database. It is helpful to investigate cybercrimes and detect vulnerabilities. Support of Syslog protocol allows SAP HANA firewall to integrate with SIEM-systems that provide real-time analysis of security alerts.
Learning mode simplifies the customization process of the firewall and prevents false triggering. DataSunrise analyzes the database traffic and creates a whitelist of common SQL queries. Further on, the firewall blocks the queries that are not on the whitelist and notifies administrators of a certain triggered security rule.
Firewall effectively protects against SQL injections (automated, out of band, time delay, Boolean, Union exploitation techniques) and other types of hacker attacks. In case of a certain rule violation, blocking scenario includes user session ending or disconnection from the database.
SAP HANA firewall by DataSunrise runs transparently and provides scale-out performance, it doesn’t require any changes to your applications. Advanced algorithms automatically create a user-specific list of pre-approved SQL commands and enable to build a secure network on SAP HANA database.