DataSunrise Masking for SAP HANA
The SAP HANA data masking solution by DataSunrise is an effective and reliable measure to hide sensitive information from unwanted users. Outsourced specialists would still be able to use obfuscated data for purposes of application development, conducting tests. Real data is replaced with fictive info or characters set by the administrator. Masking rule settings can be justified to various corporate needs of access privilege assignment.
Protecting Confidentiality on SAP HANA database
The main purpose of using data obfuscation is to protect personal identifiable or commercially sensitive data when a company has to provide database access to outsourced application developers or testers. After obfuscation third-party workers get fictive or random information instead of original data, so that it doesn’t contain anything exploitable for malicious purposes. With our masking technologies data can’t be retrieved by any means of reverse-engineering.
Regulatory acts in the sphere of information security, such as SOX, HIPAA, PCI-DSS, GLBA require affected parties apply obfuscation on sensitive personal information while testing, quality assurance, application development.
SAP HANA Dynamic Data Masking
DataSunrise performs dynamic obfuscation, which has significant advantages compared to static masking. It doesn’t require any additional hardware resources as masking happens during the process of transferring data from one environment to another, so there is no need to create another copy of a database.
Operating Principle of Data Masking
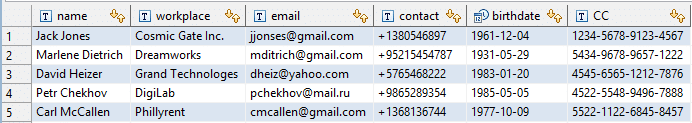
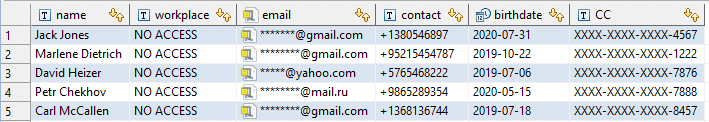
Let’s assume that we must share the following table with partners of our organization.
- Entering DataSunrise GUI we create masking rules for columns with personal identifiable data.
- Then we add users from whom we want to hide the data, creating a group for third-party workers by IP addresses, host names or login names.
- Choose masking type. We select ready patterns for emails, credit card numbers, fixed string for workplaces and random dates for birthdates.
Functioning as a proxy, DataSunrise intercepts all incoming queries to the database and modifies them according to security or masking rule. Now when our partner’s employees try to see the table, the database executes the modified query and outputs the following:
SAP HANA data masking solution by DataSunrise provides the opportunity to represent data outside of a corporate production system without violating privacy and security mandates and policies. It performs obfuscation on-demand at runtime saving your time and resources.
DataSunrise is a reliable supplier of SAP HANA database protection solutions! Discover how DataSunrise can enhance your data security. Schedule an online demo to explore our robust features, including data masking, audit, and data discovery tools. Contact our sales team to book your personalized demonstration today.