DataSunrise Masking for Azure SQL
DataSunrise Data Masking for Azure SQL limits sensitive data exposure by masking it to non-privileged users. Instead of genuine information users get fictive, yet realistic looking data. Masking is performed dynamically at the moment of a request, so there is no need to create a copy of the database or use any additional resources. Use a set of pre-defined masking rules or create one adjusting your requirements via a graphical interface, selecting what part of data must be concealed and from which users.
Sometimes companies need to hire outsourced developers in order to deploy applications, conduct tests or build program extensions. Also, in some cases corporate data has to be represented outside of the corporate production system. DataSunrise Dynamic Data Masking for Azure SQL enables to conduct all these operations without compromising confidential information. Here are the advantages of using our product:
- Easy to deploy and to work with
- Customizable for various business needs (privilege access assignment)
- Compared to static masking, dynamic obfuscation is cost-effective, because real-time masking doesn’t require additional hardware resources to store another copy of your database
- No changes to the database or application layer
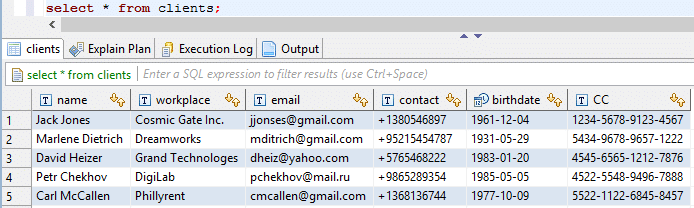
Let’s see how it works by the example of the following table.
First of all, masking rules have to be set:
1) Enter Masking section of DataSunrise GUI. Create a rule for each column you need to hide.
2) Add users you need to hide the data from.
3) Select the type of obfuscation (there are pre-defined patterns for email, credit card masking, etc.) or choose ‘Fixed String’ and set the mask value yourself.
4) There is an opportunity to customize the soft to send notifications via SMTP or SNMP whenever masking rule is triggered. Switch it on if required.
Our software is deployed as a proxy between a server and users. That’s why when a user queries the database, the query goes to DataSunrise, where it is analyzed and changed according to masking rules. Database answers the modified query and outputs masked data. We’ve set different masking rules for all columns except names and contacts. Fixed string for the column with workplaces, special masking patterns for credit card number and email addresses, random dates for birthdates. That’s what we’ve received:
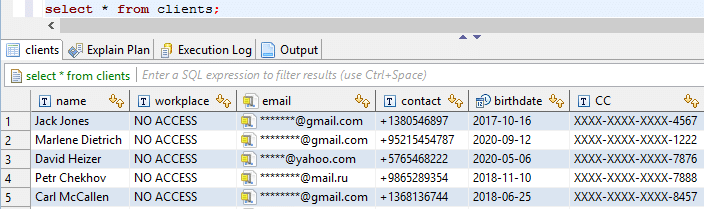
As you can see all selected columns are obfuscated, so that unauthorized users can’t see the real data. There is no need for data to be genuine, but it must be consistent enough to support proper functioning of the outsource party’s application. DataSunrise Dynamic Data Masking for Azure SQL is a great solution for access privilege assignment when a company has to protect the confidentiality of data from third-party specialists working with corporate database.