DataSunrise Masking for Hive
Data masking prevents accidental leakage or deliberate data breach by converting original data to fictive one. Hive data masking tool by DataSunrise performs masking dynamically, which doesn’t require additional hardware space to copy the database as in static masking. Entering user-friendly interface you can choose what part of information must be revealed. The feature enables third-party data requesters to access the database without compromising privacy of confidential data.
Real-Time Obfuscation
DataSunrise Masking for Hive is another line of information security system. It comes handy when companies hire third-party developers to install applications or conduct tests. Or in order to simplify the work of call centers without violating standards of regulators. During obfuscation original data is replaced by fictive data or random characters.
Masking can be static and dynamic. During static masking the copy of the database is created, then masking rules are applied and the access is provided for outsourced specialists. It demands extra hardware resources and might be time-consuming.
Dynamic obfuscation is performed on-the-fly, no stand-alone copy of database is required. Hive data masking tool by DataSunrise intercepts the queries from users as a proxy between users and a database, modifies them according to masking rules. It is also an effective tool for access privilege assignment for various business tasks.
How Data Masking Works
We have a table with the following information:
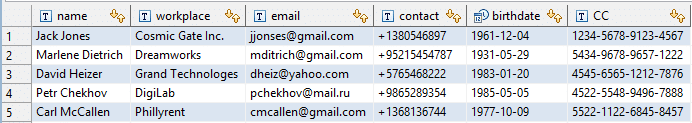
The table contains personal identifiable data that we need to hide from some users. First of all, we need to enter DataSunrise interface and customize masking rules. We will create a different masking rule for each column we want to obfuscate.
1. Add users (IP addresses or database login names) or applications. Data will be masked for selected users/apps. It will be hidden from everyone if you leave ‘Filter Sessions’ section empty.
2. Select table columns.
3. Select masking type. There is a variety of pre-defined patterns and the ability to set fixed mask value.
4. Set masking schedule if required.
5. Add your email address if you want to receive notifications of masking rule triggered.
After setting masking rules for all columns except the ones with names and contact numbers, we try to view our table again. Here is what we get:
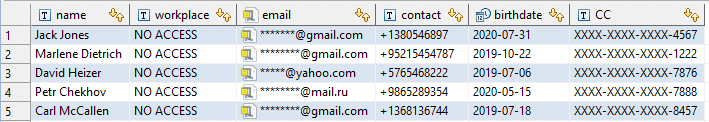
You can see the example of different masking types. Rule settings enable to customize parameters according to corporate needs and designate how much sensitive data must be revealed.
Deployment process is done in several simple steps. Convenient-to-use graphical interface simplifies the work with the system, making Hive data masking tool by DataSunrise a helpful addition to the security system of your Apache Hive database.
DataSunrise is a trusted provider of Apache Hive database protection solutions! Learn how DataSunrise can strengthen your data security. Book an online demo to explore our powerful features, including data masking, audit, and data discovery tools. Reach out to our sales team to schedule your customized demonstration today.