DataSunrise Masking for Teradata
DataSunrise Masking for Teradata is based on converting real data values into fake ones in order to prevent accidental leakage or deliberate data breach. In response to an unauthorized query, the user gets values that actually look real and do not arouse suspicion or just represent unreadable signs of any kind in accordance with predetermined setting parameters.
Protect the database against sensitive data leaks with Teradata masking tools by DataSunrise. There are many occasions when a data masking solution is required. For example, when a company collaborates with third-party developers and testers or when the sales department has to get access to the database with the clients.
Static and dynamic masking for Teradata
When performing static masking, the data must be extracted from the Teradata database and duplicated in another directory. DataSunrise creates a proxy with temporary masking rules and makes a request for data extraction. The dynamic masking core is also used for static masking, so the rule configurations and patterns are the same. As a result, you get a duplicate of the database with masked sensitive data selected in rule settings. Static masking is the best practice when sharing data with outsourced companies. However, there are some drawbacks, such as threats during database extraction and possible need to frequently update the database, as it will be out-of-date.
Dynamic masking for Teradata is performed at the moment of request. Sensitive data doesn’t leave the database. Teradata masking tool performs proxying of inbound and outbound queries. In case the clients request the sensitive data signified in any of the masking rules, DataSunrise edits the request and ensures that the client gets masked data.
How Teradata masking tools function
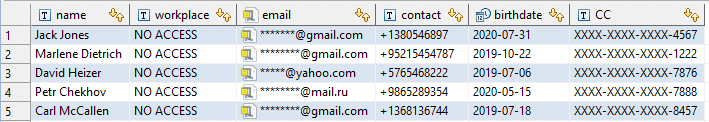
Below is the table with some confidential data that is required to be masked.
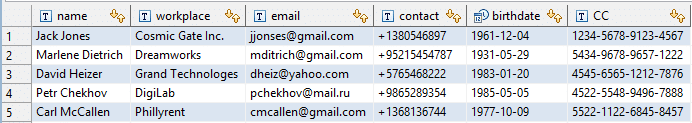
There are built-in patterns for masking and obfuscating different data types. You need to select required database elements, affected applications or users and masking patterns. After configuring rule settings we try to access the table and get the following:
For reliable protection of your critical data in an outsourced environment, use Teradata masking tools by DataSunrise. Static and dynamic masking for avoiding sensitive data breaches and unintentional leaks.