DataSunrise Masking for IBM DB2 Big SQL
Data Masking for IBM DB2 Big SQL enables you to prevent accidental data leaks by obfuscating the database output for specified users or client applications without affecting the underlying database content.
DataSunrise includes both dynamic and static data masking which guarantees the complete protection of your valuable data assets. Dynamic data masking changes client query execution results on-the-fly and static masking helps to create an environment for testing or reporting without exposing your original data.
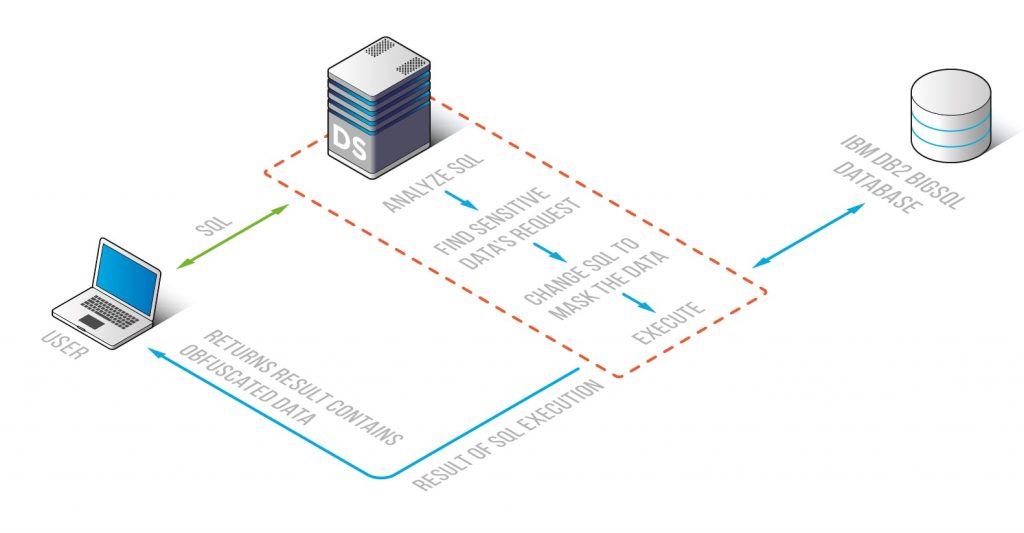
Dynamic masking for DB2 Big SQL comes in handy when you need to prevent accidental, insider-driven data leaks. Masking changes the query execution results for specified clients in the way depended on the masking algorithm used. The obfuscation is performed in real time, on-the-fly which means that no standalone copy of the masked table is created.
Static masking often used for creating a realistic testing or development environment for third-party specialists. Static masking for DB2 Big SQL includes creating of a standalone copy of your database table but with obfuscated data replacing the original sensitive data. This sterile environment enables third-party testers or developers to do their job without revealing your precious data to outsiders.
Let’s assume that we have some table with sensitive data inside that we need to hide from some database clients.
To do this, we go to the DataSunrise’s web console and create a masking rule.
- In the rule’s settings we specify database users or applications the masking should be applied for.
- Then we select the target database columns we want to obfuscate the contents of.
- Then we select a masking method to apply for the selected columns. DataSunrise proposes a variety of built-in masking algorithms to cover almost every type of data existing. You can also use your own dedicated custom functions for masking purposes.
- Data Masking settings also include schedules, thus you can run the rule at predefined time.
- You can also receive notifications on your email or instant messengers if the rule has been triggered.
As you can see, we’re using different masking methods for different types of sensitive data. And as the result we get all our sensitive data prevented from being exposed to outsiders.