DataSunrise Database Activity Monitoring for Apache Hive
If you want to find a comprehensive Hive activity monitoring software, DataSunrise is what you are looking for. It continuously monitors and logs database traffic detecting any potentially dangerous operation, including actions of privileged users and database administrators. It also assists in compliance with requirements of SOX, HIPAA, PCI DSS and other regulations.
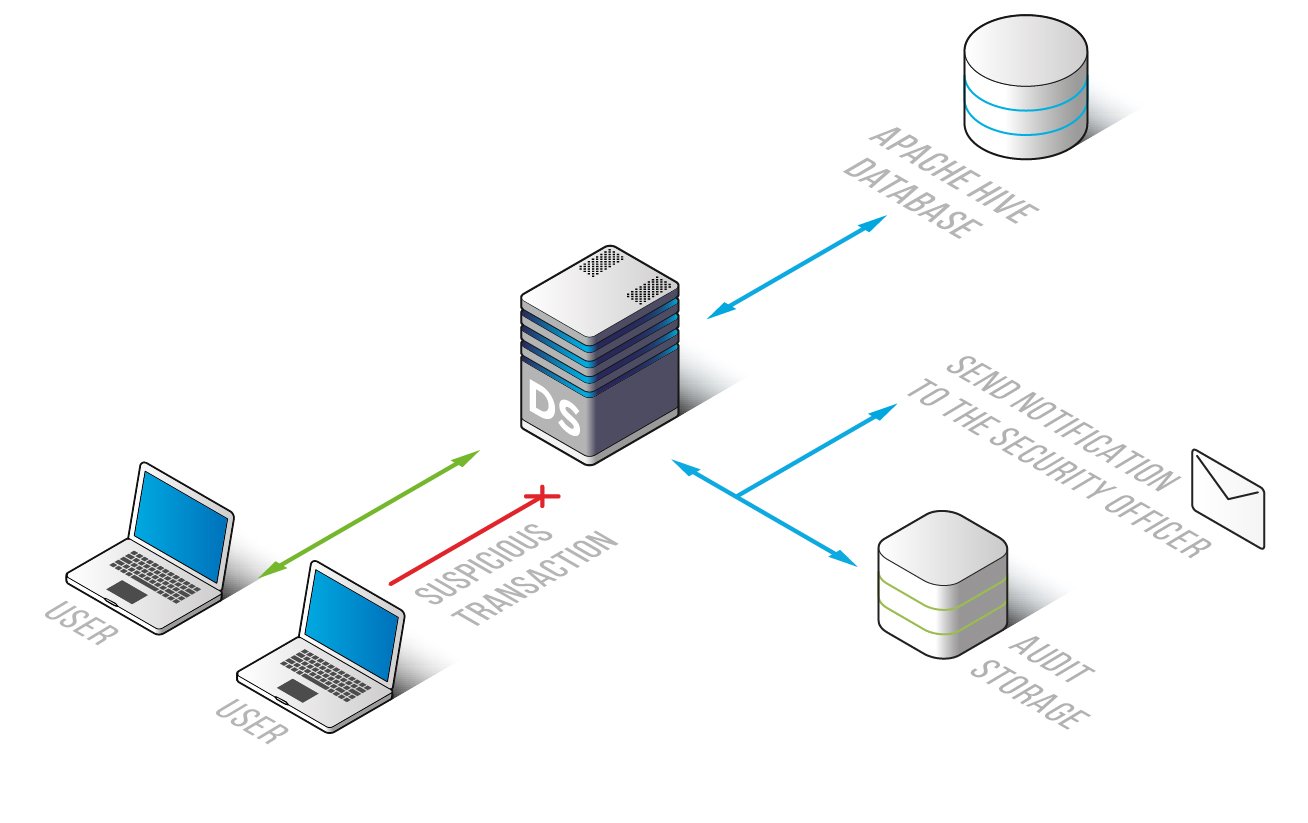
DataSunrise Database Activity Monitoring for Hive is designed to manage corporate activity traffic and reveal unauthorized and malevolent operations. All operations are logged and easy to retrieve.
There is no opportunity to delete logged information, because right after recording it goes to the outsourced database, so evildoers won’t be able to hide traces of their fraudulent activity. DataSunrise Database Activity Monitoring for Hive uses advanced technologies in order to analyze company network and generate a whitelist of SQL queries that helps in further customization of a firewall.
Advantages of using our product:
- Compliance with Sarbanes and Oxley Act (SOX), Health Insurance Portability and Accountability Act (HIPAA), Payment Card Industry Data Security Standard (PCI DSS);
- Convenient to work with, flexible settings
- SQL injection detection
- Self-learning mode that examines user queries and generates a group of SQL queries typical for certain environment
- Easy to deploy, no impact on database performance
- Ability of integration with SIEM systems (Splunk, IBM QRadar, HP ArcSight, McAfee and others)
- Managing multiple databases
- Alerts of unusual activity
Event section in GUI of Hive monitoring tool by DataSunrise will show you codes of executed queries, database responses, host names, IP addresses, used applications, error codes, user authentication information, security/audit rule updates. Any change in system settings will be recorded, including creation of new user profile and privilege assignment.
DataSunrise Database Activity Monitoring for Hive is an indispensable tool for a data breach investigation and a great measure of preventing data leaks by company members. It captures and records all changes that took place in the database.


