DataSunrise Database Activity Monitoring for MongoDB
MongoDB activity monitoring solution by DataSunrise provides complete visibility into user activity and changes applied to the database. Monitoring of MongoDB databases is helpful for detecting potentially unsafe operations and for reveling and investigating cybercrimes. The solution alerts database administrators in real time when suspicious activity is detected. DataSunrise is easy to deploy and has minimal impact on database throughput.
DataSunrise auditing solution is designed to monitor MongoDB database activity. Continuous monitoring and real-time alerts constitute an essential part of comprehensive approach to database security. DataSunrise accurately captures user behavior and stores information about who and when accessed the database records and details about performed actions and incoming and outgoing queries.
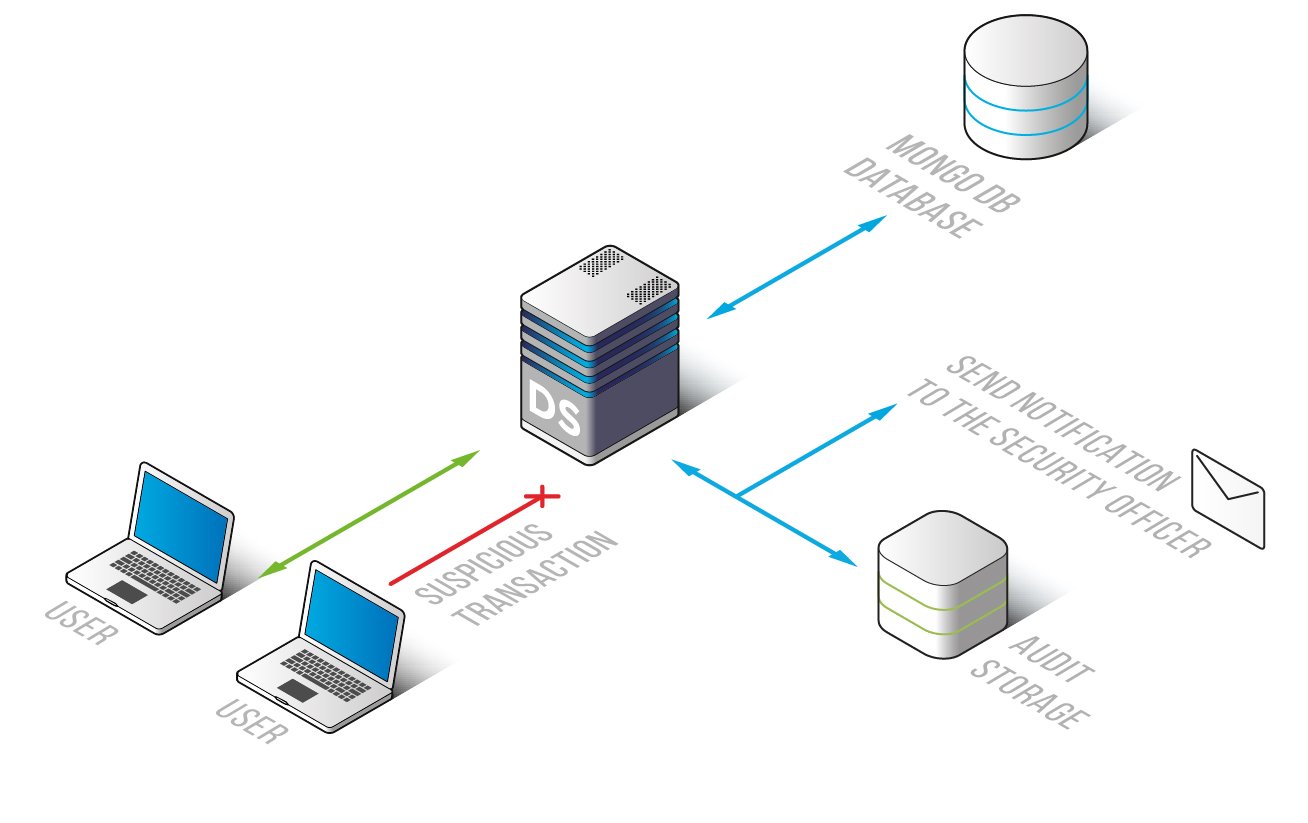
MongoDB activity monitoring solution by DataSunrise ensures that database administrators easily achieve complete visibility into database activity and get a full picture of what is happening with database and data it contains. DataSunrise monitors database traffic and analyzes it to stop potentially dangerous queries in real time.
DataSunrise tracks and logs all events performed on the database. When setting up audit rules database administrators could enable sending real-time notifications via SMTP or SNMP every time a rule is triggered.
DataSunrise ensures that database administrators reach a profound level of insight into database actvity. The tool collects information required for compliance purposes (by PCI DSS, SOX, HIPAA and other regulations) and investigating the cases of cyber crime. Logs cannot be changed or tampered with, and they are automatically sent to an external application, such as SIEM. The information imported contains code of queries and responses, session data on MongoDB database users, information about applications used to query the database, IP addresses, host names, configuration changes, including rule updates, database errors, authorization attempts, etc.


