DataSunrise Database Activity Monitoring for Apache Cassandra
Cassandra Database Activity Monitoring from DataSunrise is a special tool intended for constant monitoring of all database traffic. This is a very convenient tool that database owners and admins can use to spot unwanted actions of users with a database. Cassandra Activity Monitoring also can help to prevent hacking attacks. Detailed logs on all database activities can serve an indispensable tool for cybercrime investigation.
Cassandra database activity monitoring by DataSunrise is a tool that can continuously monitor and track every database even in real time. To increase the safety of this information database monitoring logs can be stored outside the company network which doesn’t give a single chance of hiding a single transaction even for database admins. Furthermore, database activity monitoring tools give the opportunity to track every action of privileged users, for example, database admins. Such actions may include security policy update, alteration of user accounts, as well as system configuration changes. The logs contain all details of such activities.
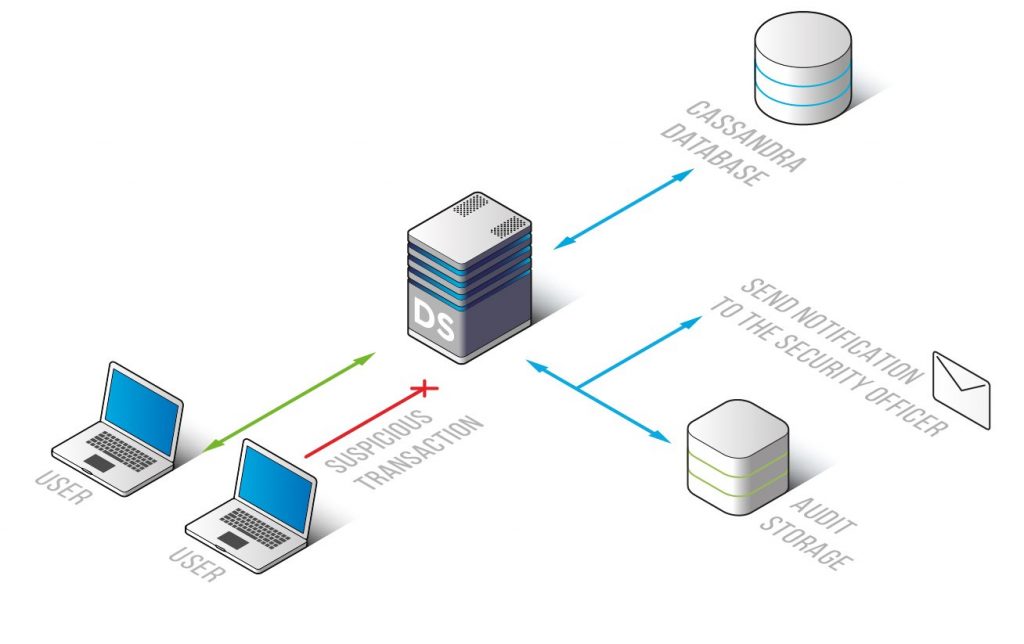
Cassandra activity monitoring solution from DataSunrise has a built-in self-learning mechanism that is able to analyze all database traffic and understand queries that are typical and safe for a given environment. If something unusual or dangerous is happening, for example, an SQL injection attempt, security personnel is immediately notified. This minimizes the risk of data theft and hacking threats.
Besides SQL injection Cassandra activity monitoring tool can detect password cracking, sharing database usernames, etc. The interface of the monitoring tool is very user-friendly and makes it possible to automate all database activity monitoring features.
Please note that database monitoring tool is very strong and effective, but at the same time it doesn’t cripple the database server performance. It can also support Syslog protocol and can be integrated with SIEM systems. Using DataSunrise is a prerequisite for being compliant with national, international industry-related sensitive data protection regulations such as GDPR, SOX, HIPAA, PCI, etc.)
Cassandra activity monitoring tool is the first step in your database protection tools that keep track of all users who have access to your Cassandra database. It helps to detect SQL injections, hacking attempts and fraudulent actions of your own employees. Use Cassandra monitoring tools to have your databases protected from cyber attacks and to control your database users.


