DataSunrise Database Activity Monitoring for Impala
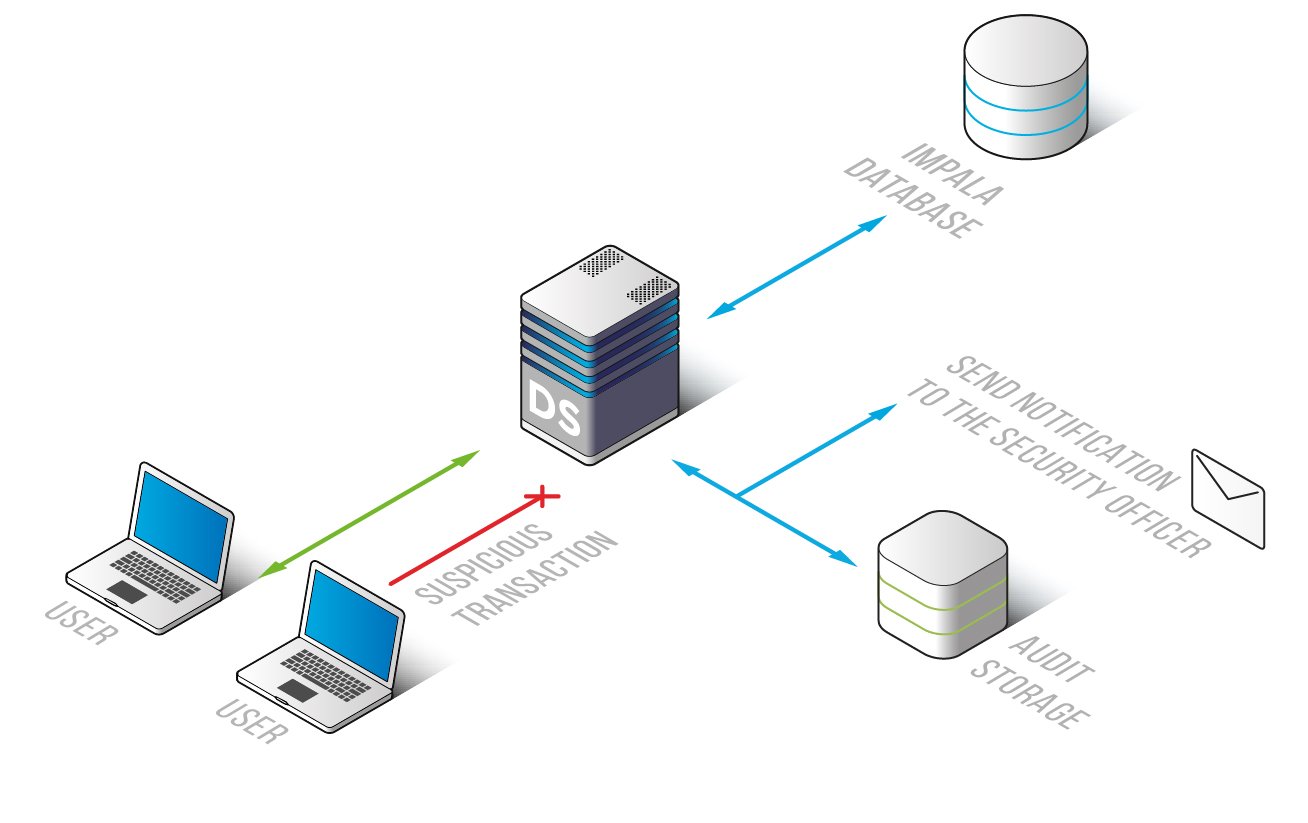
Impala Database Activity Monitoring included in DataSunrise Database Security Suite constantly monitors all database traffic and queries to the Impala database. Continuous monitoring helps to separate safe queries from queries that may pose some threat. Impala Activity Monitoring can help to timely detect SQL injections, suspicious access requests and non-typical operations of privileged users. The introduction of Impala Activity Monitoring ensures transparency of Impala database operations without hindering business processes and placing any additional load on servers.
By providing continuous tracking all database activity Impala Database Activity Monitoring gives a broad and detailed picture of all what’s happening in the database. Database owners and admins have updated information on who and how viewed or modified information. This approach helps to discover and ward off SQL injections, fraudulent insider activity and other suspicious operations.
In order to make Impala Database Activity Monitoring more effective you need to set up highly adjustable monitoring Rules. If case any of these rules is violated, alert notifications are immediately sent to the database security team with detailed information on what happened, when and where. This saves a lot of time, as the security team doesn’t have to look through all operation logs. All hacking attempts will be blocked.
Impala Database Activity Monitoring serves as an invaluable tool for investigating cyber crimes and frauds. The database monitoring information can’t be edited as it’s automatically sent to the outsourced database or SIEM system. The collected information contains the following:
- Codes of SQL queries, responds to queries;
- Session data on Impala database users;
- Applications used to query the database, IP addresses, host names;
- Configuration changes (security rule update, database errors, authorization attempts, etc.).
If your business needs to be compliant with national and international sensitive data protection regulations such as GDPR, PCI, SOX, HIPAA, etc. database activity monitoring is one of the pre-conditions. Use all the tools of DataSunrise Database Security Suite to be fully compliant with the requirements of GDPR, PCI, SOX, HIPAA, etc.
Impala Database Activity Monitoring from DataSunrise can easily detect all database vulnerabilities and identify malicious actions and stop them, if necessary eliminating all risks of data leakage. Database Activity Monitoring for Impala is one of the tool to prevent data theft, meet database security requirements and protect data integrity.


