DataSunrise Database Activity Monitoring for Vertica
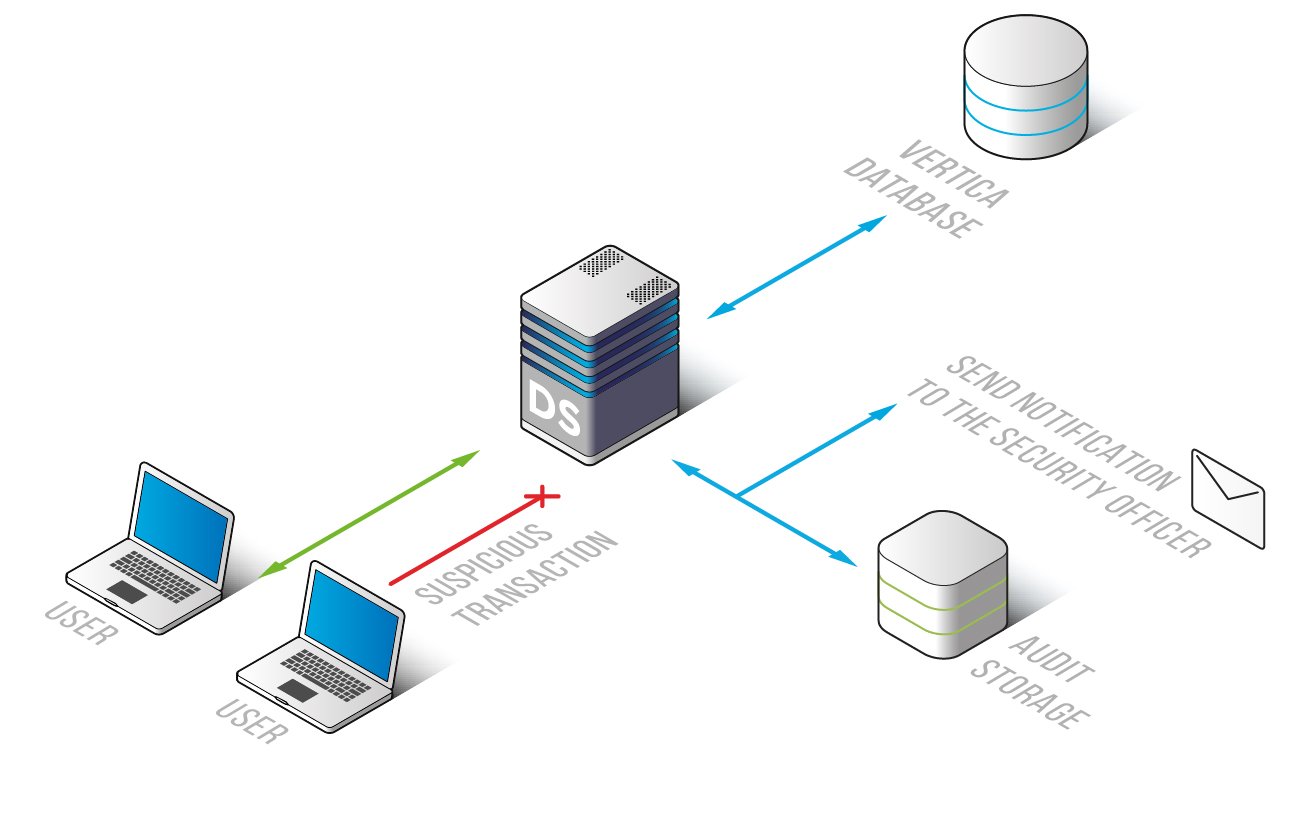
DataSunrise Database Activity Monitoring for Vertica brings to surface who accessed your database, why and when. Generating statistics allows you to keep a Vertica database under constant control. Information collected can be easily adapted for use in detecting suspicious user activity, revealing and investigating data leak thus ensuring reliable data security.
Meeting the pressing security challenges will require right information at hand to be studied and analyzed to always keep your sensitive data protected.
Vertica monitoring tool by DataSunrise finds, extracts and logs the following information:
- Database user information (user name, host name);
- SQL query code;
- Session start and end time, its duration;
- Number of rows affected or updated;
- Query result with indication of database errors, if any;
- Client application (application name, host name).
Learning mode memorizes typical database events and enables to generate alerts in case of unusual Vertica activity.
Database Activity Monitoring for Vertica
By default activity monitoring results are saved in SQLite database integrated into DataSunrise. The information may also be optionally kept in other external databases provided by the software product.
To get a more detailed analysis of deviations from standards and in order to obtain a more comprehensive understanding of Vertica activity, information generated by the monitoring tools can be exported to SIEM systems.
Generally speaking, with Vertica monitoring solution by DataSunrise you will be able:
- To analyze events and generate immediate alerts if any anomaly is detected: network traffic abnormality, unexpected user activity, unknown devices, etc;
- To meet government and industry standards that require to employ data auditing and database activity monitoring;
- To make reports;
- To have evidence, in case of incidents;
- To underline vulnerabilities and validate IT department needs to timely eliminate them;
- etc.


