DataSunrise Sensitive Data Discovery for Vertica
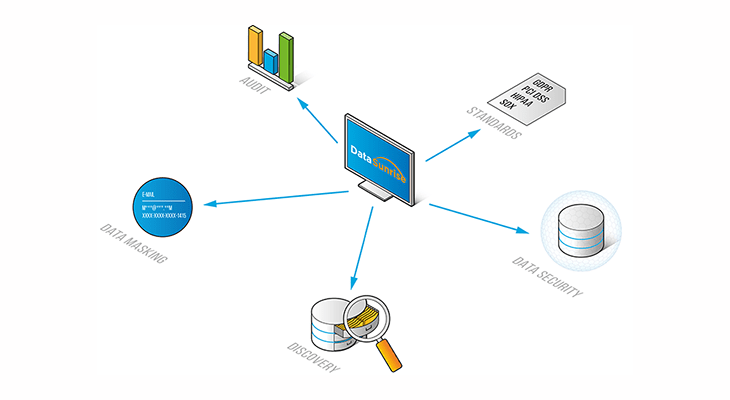
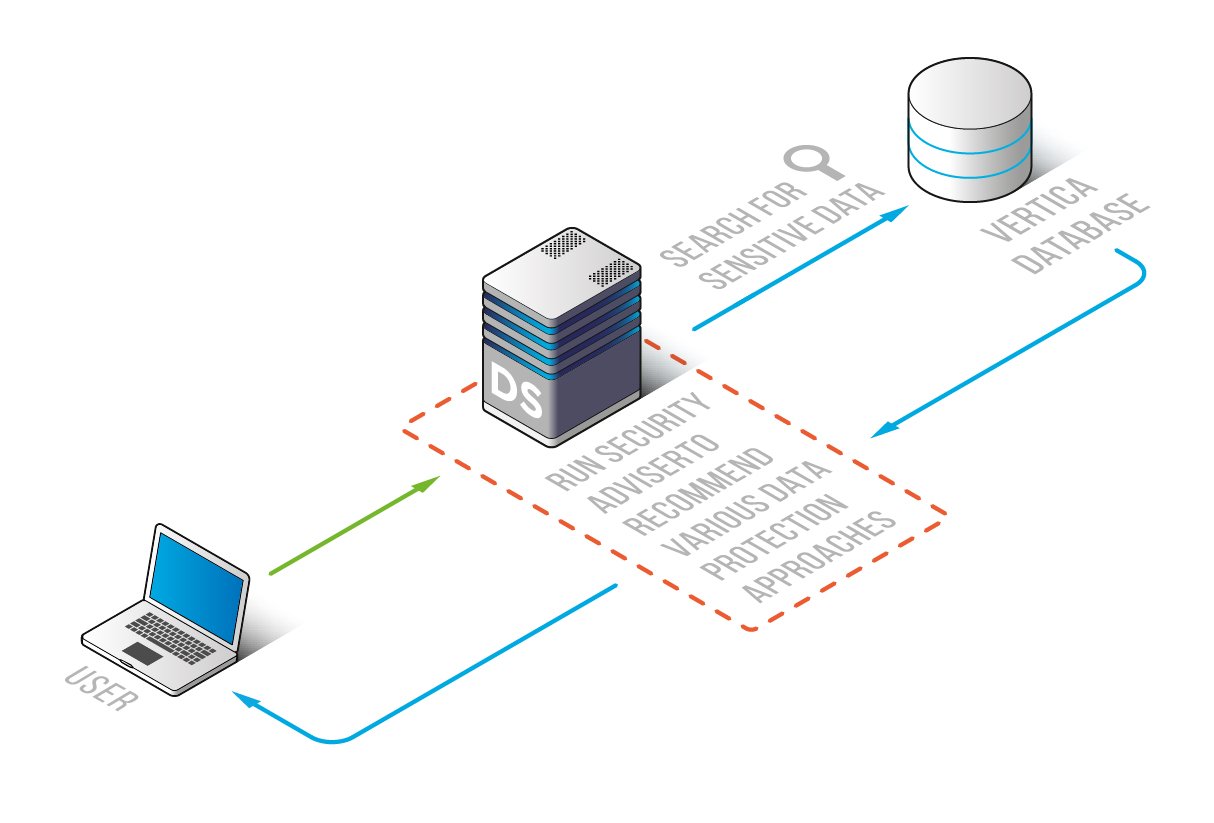
DataSunrise Data Discovery for Vertica enables security teams to locate sensitive enterprise information to effectively protect it. It also helps companies to demonstrate compliance with industry and government regulations. Users can apply either built-in search filters or create their own filters to trace various types of sensitive and regulated data.
Prevention of data loss, data leaks and data breaches starts with identifying and locating sensitive information across an organization. This makes Data Discovery one of the most critical features of any data security solution. Sensitive Data Discovery ensures that a company maintains a firm grasp on the organization’s security requirements and remains compliant with industry regulations.
DataSunrise Data Discovery for Vertica enables enterprises to continuously assess the full picture of the data they process and implement appropriate security strategy to keep it protected. The feature enables to perform search and analysis of data in all databases across the company. Database objects can contain confidential or proprietary data as well as protected data such as personally identifiable information (PII), electronic protected health information (ePHI), etc.
By default, the tool includes search for the following categories of data:
- Dates
- Financial (codes, credit card numbers, PIN codes, etc.)
- Geographic (names of cities, countries, ZIP codes, etc.)
- Medical (search for medical records)
- Names
- Numbers (account numbers, certificates, license plates, etc.)
- Social Security Number
- Telephone/Fax
Users can also create and edit their own search filters.
Search of sensitive and regulated data is performed across all available database elements or it can be applied to a particular database or table. After identifying the columns containing the specified data types, data masking and security rules are created. Security and masking rules allow users to make sensitive data available for a limited group of employees and reduce exposure of production databases to unauthorized personnel.