DataSunrise Sensitive Data Discovery for Greenplum
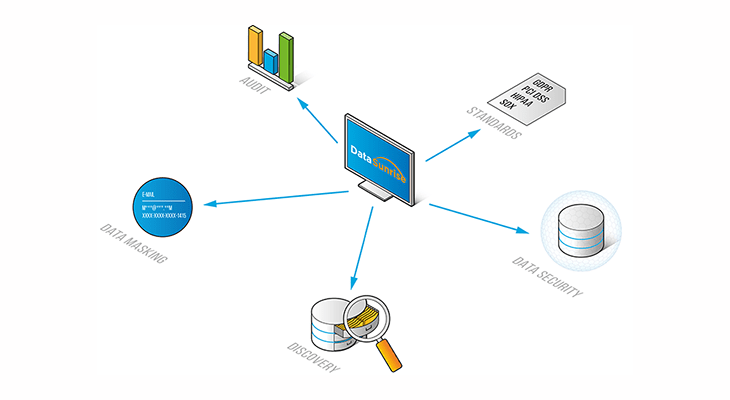
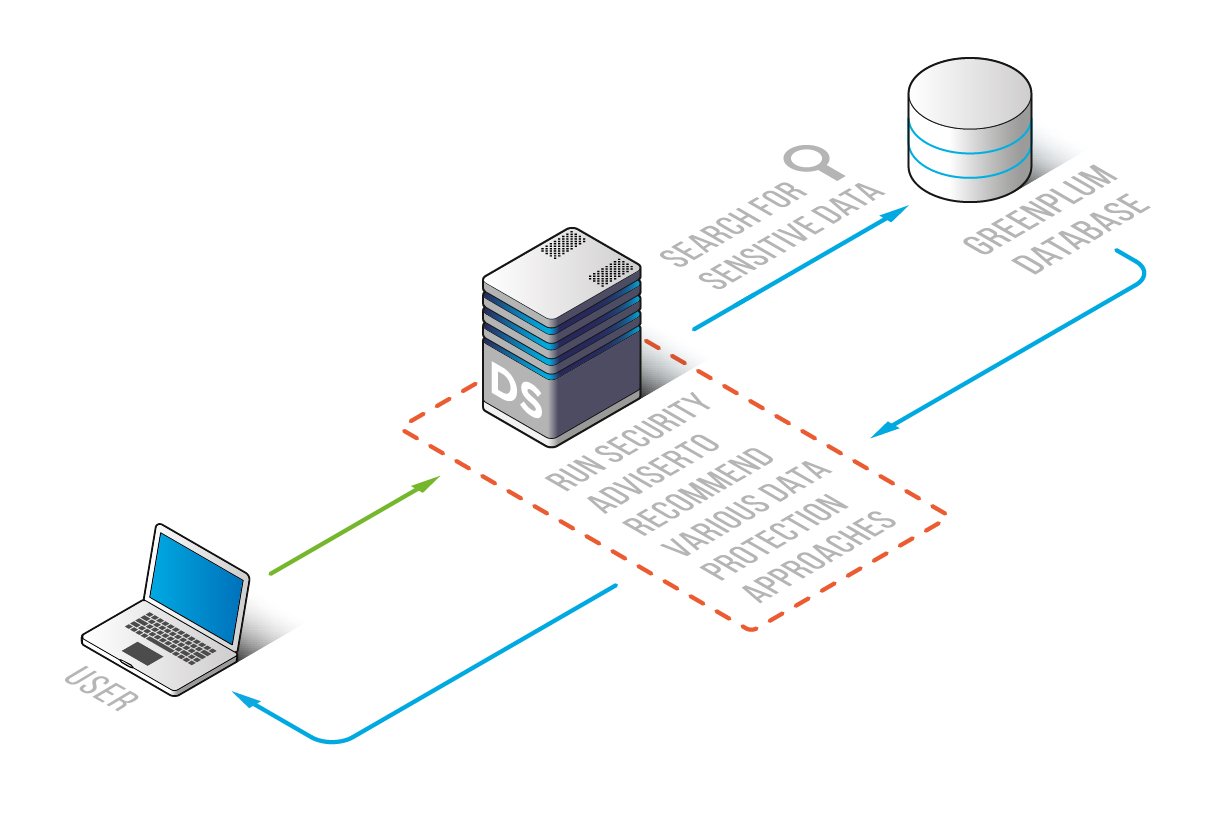
Sensitive Data Discovery feature from DataSunrise for Greenplum reduces the risk of confidential data mishandling and leak by searching and detecting sensitive information across Greenplum databases. This tool gives insight into the content of a database and helps to identify the sources of sensitive data. After that use the Security, Audit, and Masking tool from DataSunrise to guarantee your data security.
Sensitive data leaks and exposure pose a serious threat to the image of any company. And don’t forget that non-compliance with the requirements of national and international regulations such as GDPR, SOX, HIPAA, PCI DSS poses a serious financial risk too.
That is why Sensitive Data Discovery for Greenplum is a fundamental feature that ensures successful database protection. It’s also the first step to be compliant with such national and international regulations as GDPR, SOX, HIPAA, PCI DSS.
The search is conducted across all Greenplum databases using preset filters, however, these filters are customizable and you can retrieve any information you need.
You specify where you want to search for information. To do that you just need to specify a certain database, table, schema. Or you can conduct a reach throughout all available databases. The preset search filters are the following:
- Names
- Email addresses
- Financial (passwords, credit card numbers, salary, taxes)
- Geographical (address, city, country, post code, state, zip code)
- Medical information
- Driver License
- Social security numbers
- Phone numbers
- Web/network information (IP, URL addresses)
- Etc.
Once you have found and identified sensitive data you want to protect you can and must do the next step. Now apply security, audit and masking rules. That’s what these features from DataSunrise for Greenplum databases do.
- A Security rule. Blocks access to sensitive data for queries not meeting specific criteria.
- An Audit rule. Constant monitoring of all database-related activity.
- A Masking rule. Dynamic or static obfuscation of sensitive data.