DataSunrise Database Activity Monitoring for IBM Netezza
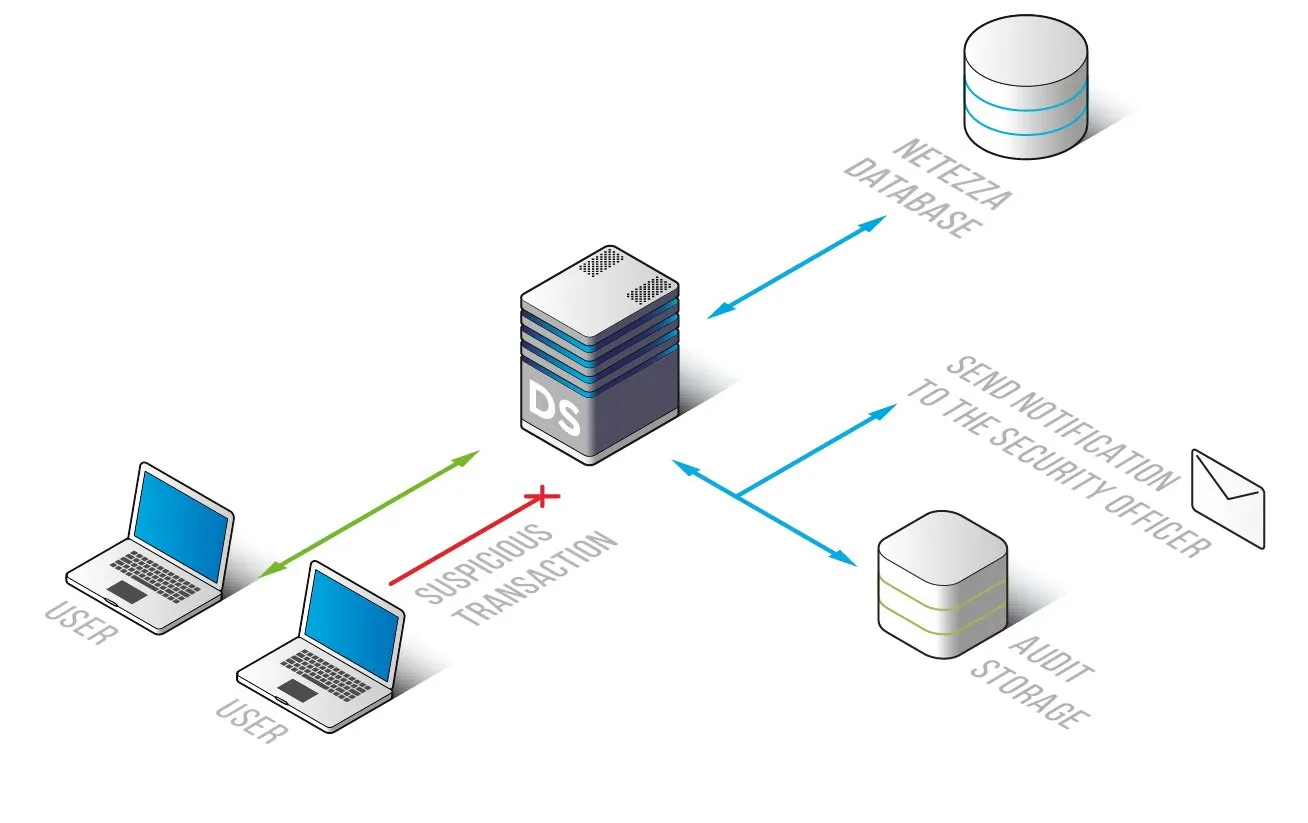
The IBM Netezza activity monitoring solution by DataSunrise analyses user transactions across multiple databases, detecting SQL injections, hack attacks and unauthorized operations of privileged users. Advanced filtration algorithms allow to differentiate between attacks and normal activity. Detailed logs help to investigate cybercrimes and prevent data breaches by revealing signs of imminent danger.
IBM Netezza activity monitoring solution by DataSunrise is a valuable tool for regulatory compliance and information security. It provides full visibility of database activities including common user transactions, changes made to the data and changes in configuration and security policy.
DataSunrise Activity Monitoring for IBM Netezza improves database security by detecting SQL injections, brute force cracking and other types of hacking attempts. According to recent researches, most cases of data leakage are caused by insiders. Thus, monitoring privileged user actions is even more important than detecting attacks. With DataSunrise privileged users cannot hide their malicious operations, as logs are stored in the outsourced database.
DAM helps to enable compliance controls: Health Insurance Portability and Accountability Act (HIPAA), Payment Card Industry Data Security Standard (PCI DSS), Sarbanes-Oxley Act (SOX).
The support of Syslog protocol gives the ability to integrate with SIEM systems and get real-time analysis of security threats according to logged information.
DataSunrise Activity Monitoring carefully inspects database transactions and records detailed information on user and system events, which can be used for Logs contain:
- Configuration changes, security/audit rule update;
- Session data: user, host names, IP addresses, list of executed queries and their results, applications used to query the database;
- SQL codes of the queries;
- Database errors, authentication data.
DataSunrise Activity Monitoring for IBM Netezza inspects and logs database activity and alerts administrators if there is a case of a security policy violation. Customizable features enable to adjust the solution to various corporate needs. It helps to protect confidentiality and integrity of your sensitive data without slowing down the database.


