DataSunrise Audit for IBM Netezza
IBM Netezza Database Audit tool by DataSunrise is aimed at continuous monitoring of all database activity. The tool reacts to both external and internal attacks and immediately notifies the administrator about suspicious activity. Real-time traffic analysis enables to detect any attempt of abusing access rights and thus prevents data leakage due to employee’s fault or deliberate intention.
IBM Netezza audit tool by DataSunrise is responsible for the process of monitoring access to the database, modification of selected objects and resources within operational databases. IBM Netezza Audit retains a detailed record of the access which can be retrieved and analyzed as needed. Regular log inspections help to minimize risks by preventing potential security vulnerabilities.
Government and industry standards such as SOX, HIPAA, PCI-DSS require their subjects to perform database activity audition, because, when it comes to cybercrime investigation, database audit becomes an irreplaceable instrument to find the culprit and evaluate the value of the data breach. It is especially important nowadays due to the continuous increase of cyber attacks, performed not only by outside hackers but also by company members who have access to sensitive data. With IBM Netezza Audit you always know who did what to your data and when exactly it happened.
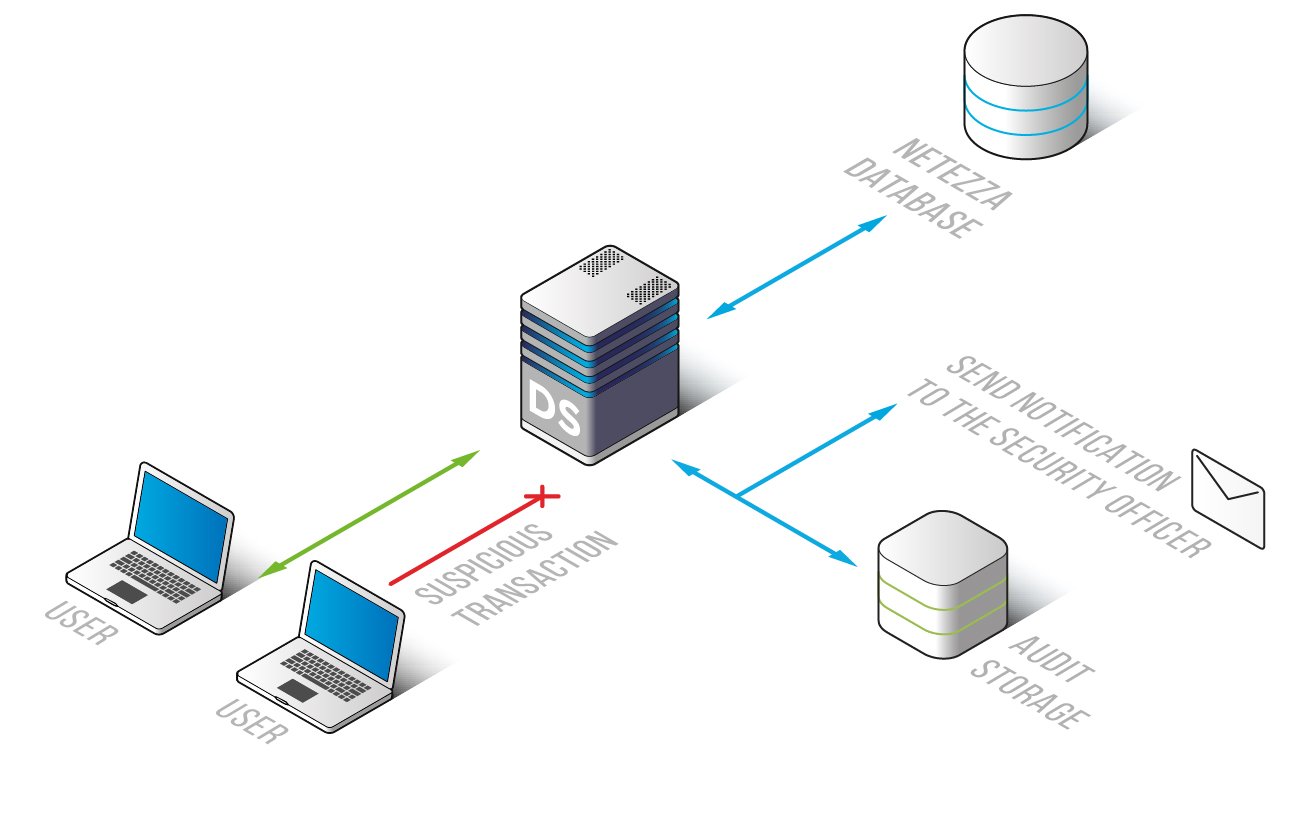
IBM Netezza Database Audit tool by DataSunrise is controlled via a user-friendly and simple interface and it doesn’t cause any downtimes. It has a self-learning system that identifies SQL queries typical for a given database, which helps to pay more attention to potentially dangerous queries. There is also an opportunity to customize the program to notify of certain activities so that administrators can timely react to suspicious behavior. Due to supporting of the Syslog protocol, it is compatible with any SIEM system. More detailed information on monitoring feature is available here.
Data Audit collects the following information:
- SQL code of overridden queries;
- Session information: client applications, usernames, session duration time, hostname queries came from, etc;
- Database errors;
- The database instance that received user queries and number of database entries that were affected by the query.
IBM Netezza data audit tool by DataSunrise is a powerful and yet easy-to-use audit tool which you can customize for corporate needs, it will provide you with detailed information about database activity and help you improve your database security system. Enhance your data governance with DataSunrise Audit. Schedule an online demo to see how our solutions can transform your operations.


